2014-02-02 - NEUTRINO EK USES CVE-2013-0074 (SILVERLIGHT EXPLOIT)
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
NOTES:
I found Neutrino EK using a Silveright exploit today. Included are pcaps for two different infections--one for infection by the Silverlight exploit, and another by the same domain using a Java exploit.
DETAILS
ALERTS FOR SILVERLIGHT EXPLOIT ON 2014-02-02 (FROM SECURITY ONION)
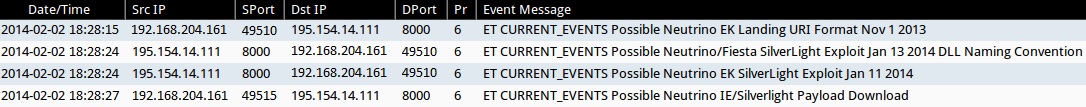
- 18:28:15 UTC - 195.154.14[.]111:8000 - ET CURRENT_EVENTS Possible Neutrino EK Landing URI Format Nov 1 2013 (2017652)
- 18:28:24 UTC - 195.154.14[.]111:8000 - ET CURRENT_EVENTS Possible Neutrino/Fiesta SilverLight Exploit Jan 13 2014 DLL Naming Convention (2017963)
- 18:28:24 UTC - 195.154.14[.]111:8000 - ET CURRENT_EVENTS Possible Neutrino EK SilverLight Exploit Jan 11 2014 (2017958)
- 18:28:27 UTC - 195.154.14[.]111:8000 - ET CURRENT_EVENTS Possible Neutrino IE/Silverlight Payload Download (2017971)
ASSOCIATED DOMAINS
- 162.144.12[.]195 - www.bloggingwithdogs[.]com - Compromised website
- 188.40.79[.]151 - 38hartrobertsroad[.]com - Redirect from the compromised website
- 77.55.4[.]14 - pracowniahistoryczna[.]pl - Another redirect from the compromised website
- 62.76.177[.]211 - no domain name - Redirect from 38hartrobertsroad[.]com
- 92.53.105[.]34 - no domain name - Redirect from pracowniahistoryczna[.]pl
- 31.22.4[.]108 - 30oct2007[.]com - Final redirect from both redirect chains
- 195.154.14[.]111 - oojahphi.brittmany[.]com - Neutrino exploit domain on TCP port 8000
INFECTION CHAIN OF EVENTS FOR SILVERLIGHT EXPLOIT
- 18:28:09 UTC - 162.144.12[.]195 - www.bloggingwithdogs[.]com - GET /
- 18:28:10 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr
- 18:28:11 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/
- 18:28:11 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - GET /wp-content/themes/zenith/rotr
- 18:28:11 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - GET /wp-content/themes/zenith/rotr/
- 18:28:11 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - HEAD /wp-content/plugins/rotr/load.swf?sid=98590
- 18:28:12 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/
- 18:28:12 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - GET /wp-content/themes/zenith/rotr/
- 18:28:12 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/load.swf?sid=98590
- 18:28:12 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl- HEAD /wp-content/themes/zenith/rotr/load.swf?sid=58925
- 18:28:12 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/load.swf?sid=98590&ref=hxxp[:]//www.bloggingwithdogs[.]com/
- 18:28:12 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - GET /wp-content/themes/zenith/rotr/load.swf?sid=58925
- 18:28:13 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - HEAD /wp-content/plugins/rotr/load.swf?sid=52489
- 18:28:13 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - HEAD /wp-content/themes/zenith/rotr/load.swf?sid=91371
- 18:28:13 UTC - 77.55.4[.]14 - pracowniahistoryczna[.]pl - GET /wp-content/themes/zenith/rotr/load.swf?sid=91371
- 18:28:13 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/load.swf?sid=52489
- 18:28:13 UTC - 62.76.177[.]211 - no domain name - GET /sleev/?10
- 18:28:13 UTC - 92.53.105[.]34 - no domain name - GET /speedup/?id=3
- 18:28:13 UTC - 188.40.79[.]151 - 38hartrobertsroad[.]com - GET /wp-content/plugins/rotr/load.swf?sid=52489&ref=hxxp[:]//www.bloggingwithdogs[.]com/
- 18:28:14 UTC - 62.76.177[.]211 - no domain name - GET /sleev/?10
- 18:28:14 UTC - 92.53.105[.]34 - no domain name - GET /speedup/?id=3
- 18:28:14 UTC - 31.22.4[.]108 - 30oct2007[.]com - GET /wp-content/rotr/
- 18:28:14 UTC - 31.22.4[.]108 - 30oct2007[.]com - GET /wp-content/rotr/
- 18:28:15 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /djgdkxwov?ehyvgiqpkwqy=2404448
- 18:28:15 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /djgdkxwov?ehyvgiqpkwqy=2404448
- 18:28:16 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /dobqfqrwli.js
- 18:28:18 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /rqngyeai
- 18:28:24 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - POST /bhrkyufjx
- 18:28:24 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /somdlbrm?nlzjovudzehl=qvimchxspm (Silverlight exploit)
- 18:28:27 UTC - 195.154.14[.]111 - oojahphi.brittmany[.]com:8000 - GET /hyfwodhmsdx?nskee=qvimchxspm (EXE payload)
CHAIN OF EVENTS FOR SAME MALWARE PAYLOAD USING A JAVA EXPLOIT
NOTE: The chain of events from the compromised web site to the Neutrino EK domain is the same as shown above. The EXE payload is also the same.
- 17:54:23 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /dfhvswiprgpspq?abwbkv=2404448
- 17:54:23 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /owlikhdeduc.js
- 17:54:24 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /hsmhjkpzjuegnwl
- 17:54:25 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /dfhvswiprgpspq?abwbkv=2404448
- 17:54:29 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - POST /yorfewhulnrx
- 17:54:45 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /erelwascrltb?bkhotdy=zoetkpsjmv (Java exploit)
- 17:54:46 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /META-INF/services/javax.xml.datatype.DatatypeFactory
- 17:54:46 UTC - 195.154.14[.]111 - weilaeni.brittmany[.]com:8000 - GET /fvalvitqspp?bjguudvnf=zoetkpsjmv (EXE payload)
PRELIMINARY MALWARE ANALYSIS
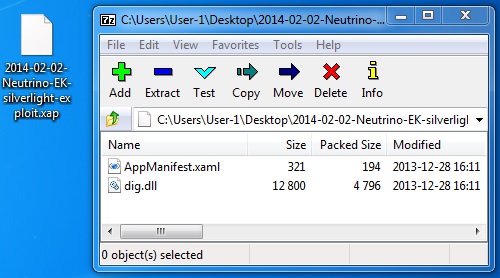
File name: 2014-02-02-Neutrino-EK-silverlight-exploit.xap
File size: 5,210 bytes
MD5 hash: ce056895e07d2a9d04c5e8db844013ea
Virus Total link: https://www.virustotal.com/en/file/8bd2cd6a40ad378a974b20e6b0ae49ba4715cd81b96c667c2627f14eab08bc50/analysis/
Detection ratio: 4 / 50
First submitted: 2014-02-02 18:44:37 UTC
- https://www.cve.org/CVERecord?id=CVE-2013-0074
- https://malware.dontneedcoffee.com/2013/11/cve-2013-0074-silverlight-integrates.html
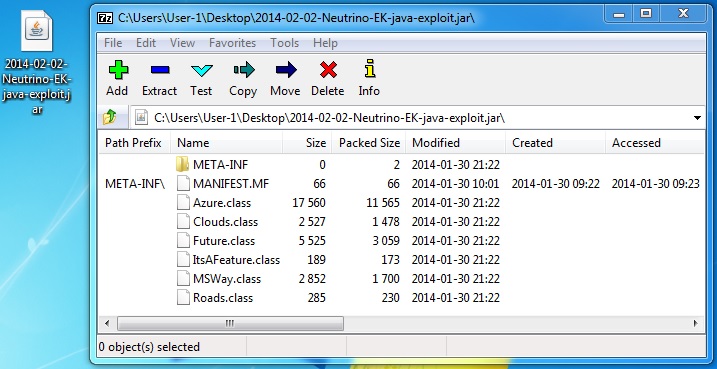
File name: 2014-02-02-Neutrino-EK-java-exploit.jar
File size: 556b926e4fb68e255993696691f8e48b
MD5 hash: 19,265 bytes
Virus Total link: https://www.virustotal.com/en/file/dca6b3d8e2ae52d5994bc052b2d2b566c711b53fc8acbab5856115e022bf4411/analysis/
Detection ratio: 0 / 50
First submitted: 2014-02-01 00:30:13 UTC
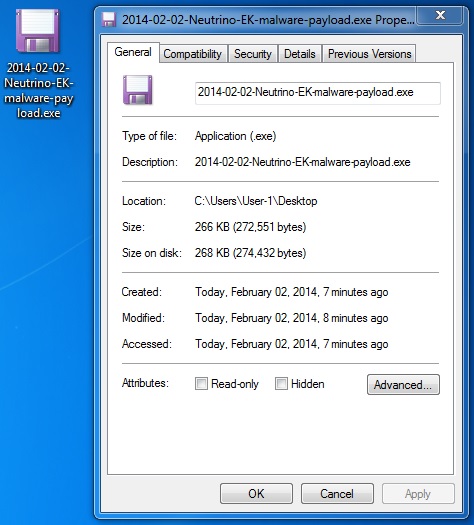
File name: 2014-02-02-Neutrino-EK-malware-payload.exe
File size: 272,551 bytes
MD5 hash: bec79bed374f4853fbd70209ddeab8d6
Virus Total link: https://www.virustotal.com/en/file/267630f17f204141cf9e1fd4768414e8f738c0e84122692c5b677d9d7cffe68c/analysis/
Detection ratio: 8 / 49
First submitted: 2014-02-02 18:45:02 UTC
POST INFECTION CALLBACK TRAFFIC
The malware gave an error while running from the VM, so I set up a physical host to see what the callback traffic looks like. On the physical host, the malware copied itself to C:\Users\User-1\AppData\Roaming\Deylro\aqum.exe and updated the following registry key:
Registry key: HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Value name: Uxwaol
Value data: C:\Users\User-1\AppData\Roaming\Deylro\aqum.exe
Here are the snort events generated from the infected physical host:
- 2014-02-03 01:03:44 UTC - 89.191.150[.]230:80 - ET CNC Zeus Tracker Reported CnC Server TCP group 19
- 2014-02-03 01:03:44 UTC - 89.191.150[.]230:80 - ET TROJAN Generic -POST To file.php w/Extended ASCII Characters
- 2014-02-03 01:03:44 UTC - 89.191.150[.]230:80 - ET TROJAN Generic - POST To .php w/Extended ASCII Characters
- 2014-02-03 01:04:13 UTC - 74.125.227[.]243:80 - ET TROJAN Zeus Bot GET to Google checking Internet connectivity
- 2014-02-03 01:04:14 UTC - 118.69.206[.]95:80 - ET CNC Zeus Tracker Reported CnC Server TCP group 3
- 2014-02-03 01:04:14 UTC - 118.69.206[.]95:80 - ET CNC Zeus Tracker Reported CnC Server TCP group 2
Some of the callback traffic seen from the infected physical host:
- 89.191.150[.]230 - www.gminalubiewo[.]pl - POST /images/files/file.php
- 74.125.227[.]243 - www.google[.]com - GET /webhp
- 69.16.143[.]110 - www.h8adioigud[.]su - POST /files/file.php
- 118.69.206[.]95 - www.kimsa[.]vn - POST /images/redir/redir.php
- 69.16.143[.]110 - www.gaieiuu4877g[.]su - POST /files/file.php
Click here to return to the main page.