2015-05-08 - TRAFFIC ANALYSIS EXERCISE - FINAL ANALYSIS
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
TRAFFIC:
- 2015-05-08-traffic-analysis-exercise.pcap.zip 317.5 kB (317,528 bytes)
FINAL ANALYSIS
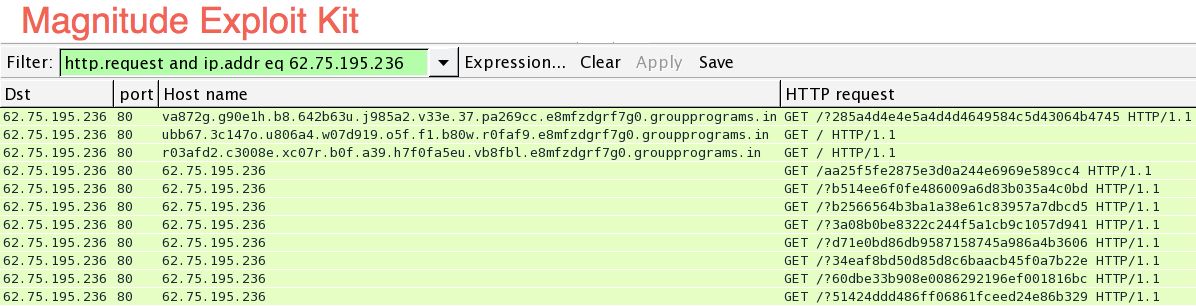
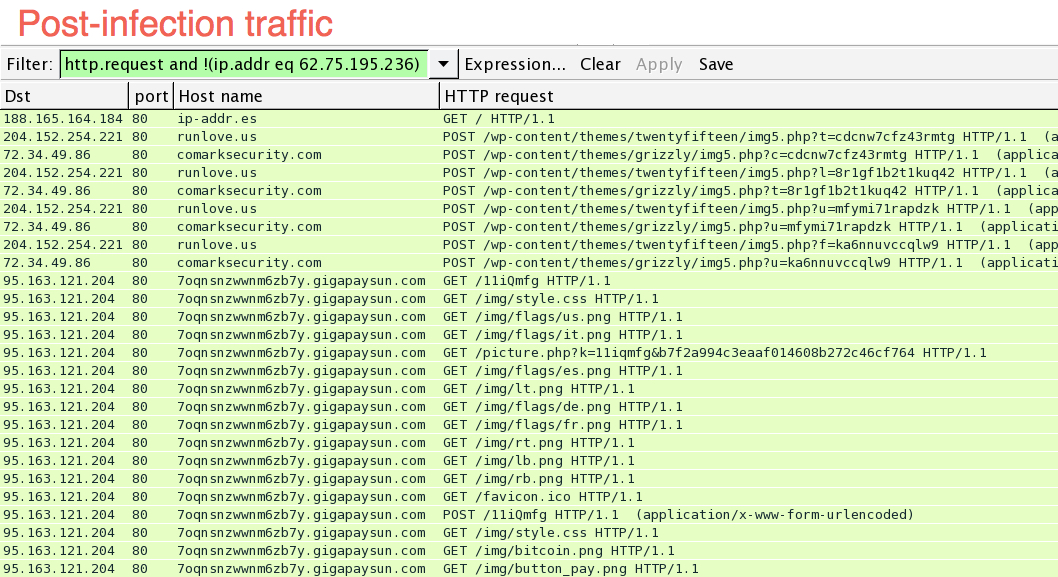
You can separate the traffic into exploit kit activity (the first part) and post-infection traffic (the second part).
Here's the first part:
Here's the second part:
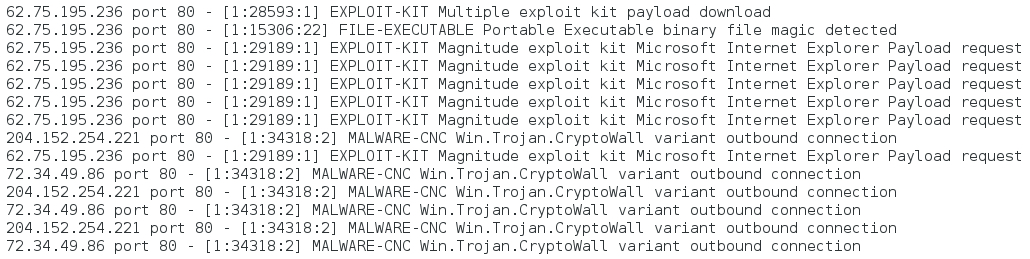
Read the pcap with Snort 2.9.7.2 and the Talos (VRT) signature set, you'll find the following alerts:
Playback the pcap in Security Onion using the Emerging Threats and ETPRO rulesets, and you'll find the following:
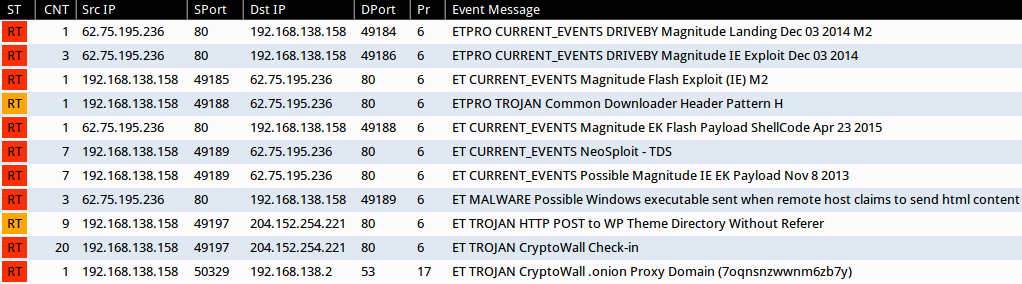
Shown above: Screenshot from Sguil RealTimeEvents tab in Security Onion.
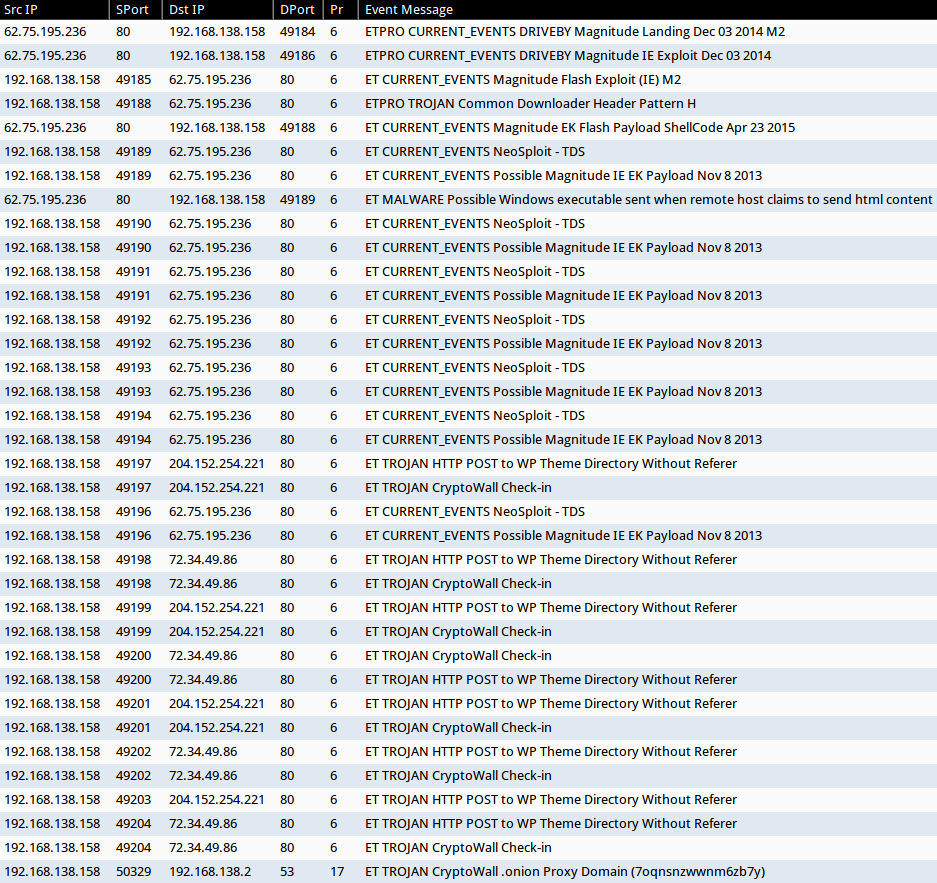
Shown above: Sguil alerts all escalated, so you can see the indivdual events.
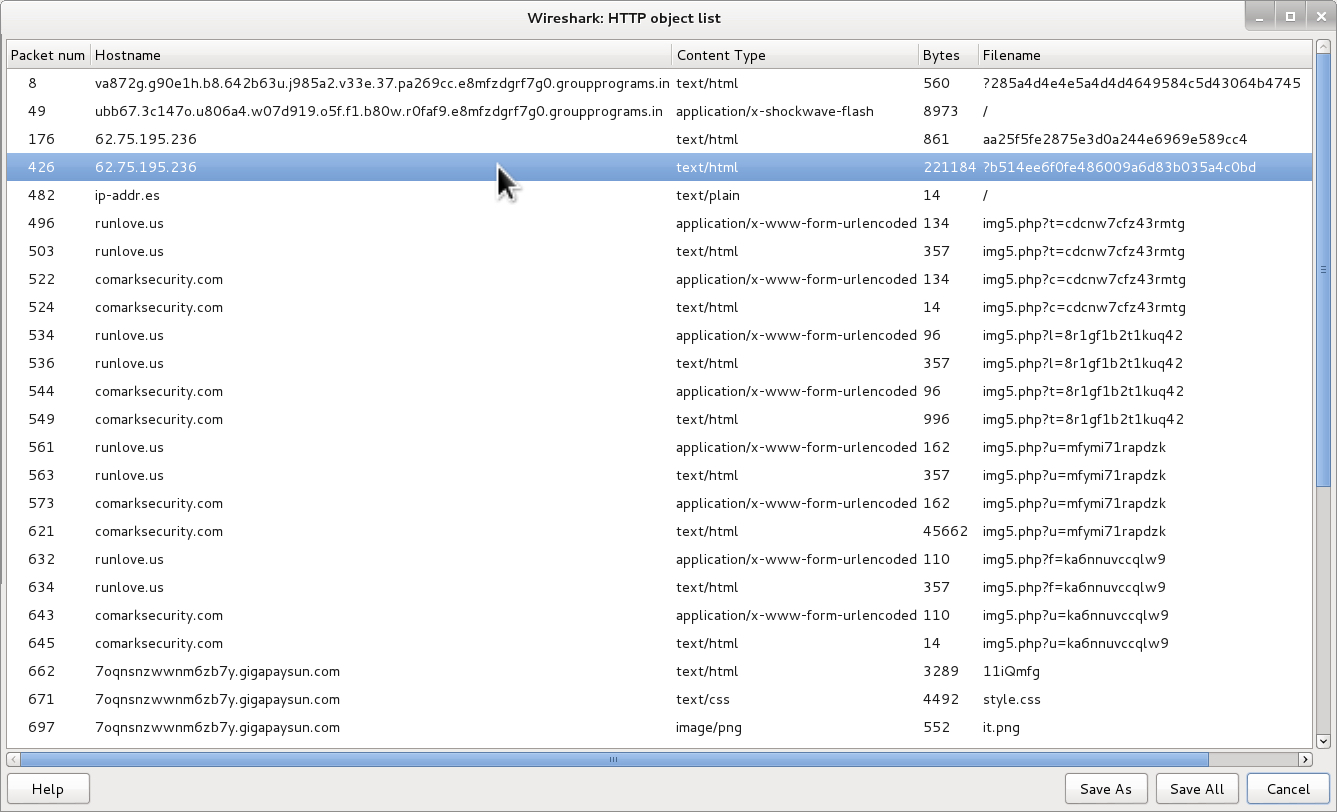
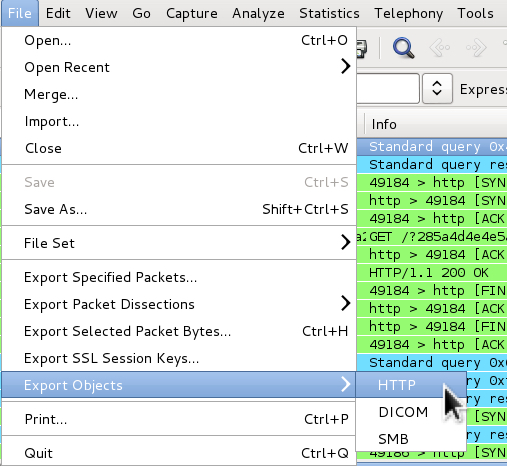
This exploit kit can send multiple payloads, but only one was sent in this pcap. To export the payload from the pcap, use File --> Export Object --> HTTP
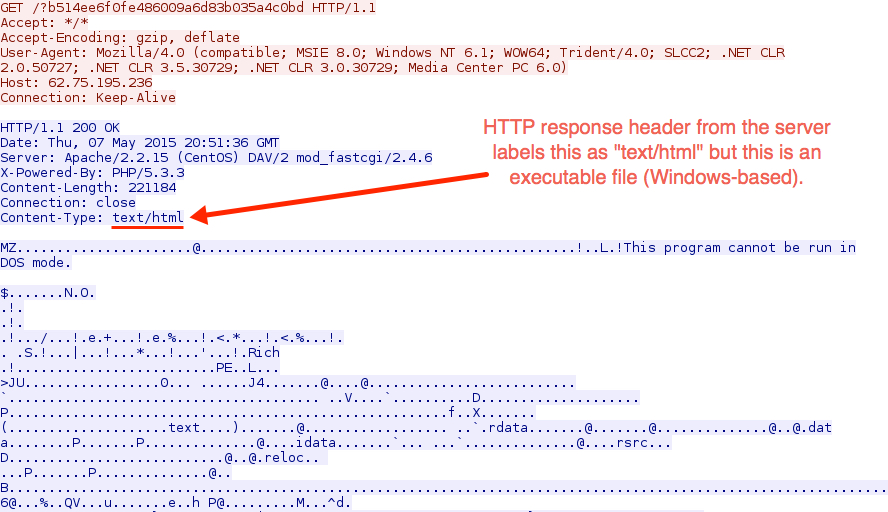
The image below shows the 221,184 bytes of malware payload, which was falsely labled as text/html in the HTTP response headers sent by the server:
Follow the associated TCP stream, and you'll see this is a Windows-based executable file:
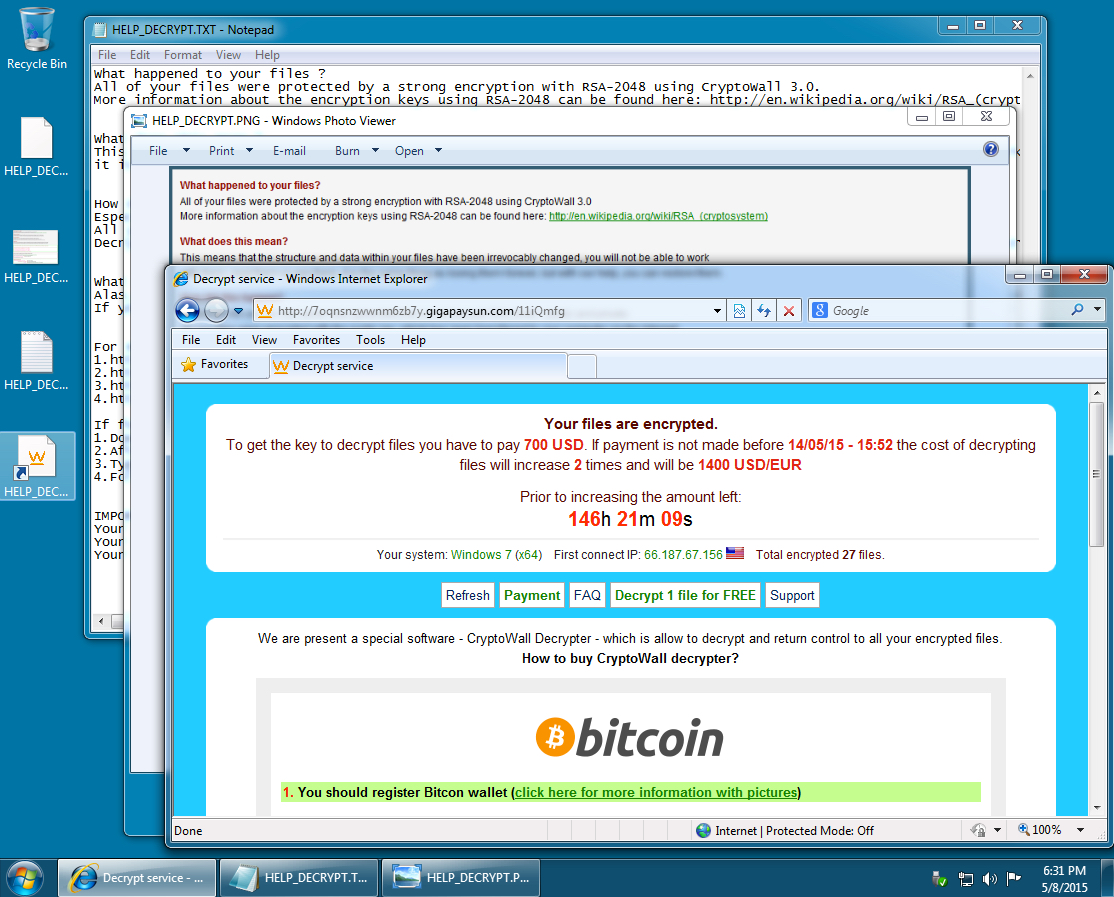
I ran the file on a Windows host to confirm the malware:
FINAL WORDS
If you need to confirm you extracted the malware correctly, you can grab a copy here at malwr.com. You'll need to be a registered user to download the sample.
Hope you found this useful. Thanks for reading!
Click here to return to the main page.