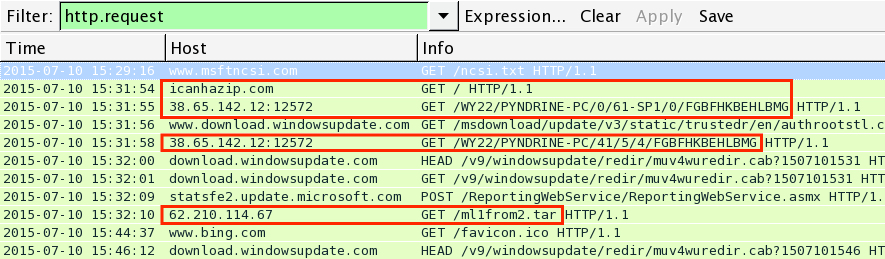
2015-07-11 - TRAFFIC ANALYSIS EXERCISE - ANSWERS
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
TRAFFIC AND MALWARE:
- 2015-07-11-traffic-analysis-exercise.pcap.zip 3.2 MB (3,154,798 bytes)
- 2015-07-11-traffic-analysis-exercise-malware-samples.zip 2.3 MB (2,318,552 bytes)
ANSWERS
NOTE: I've included malware extracted from the infected host. These would be samples of Upatre and Dyre extracted from the infected host by your forensics team. Information on the malware won't be included in this incident report.
Below is an example of a writeup for this incident report. It doesn't include any snort alerts, but you could include those as well, assuming you can generate alerts in your own lab environment.
DETAILS
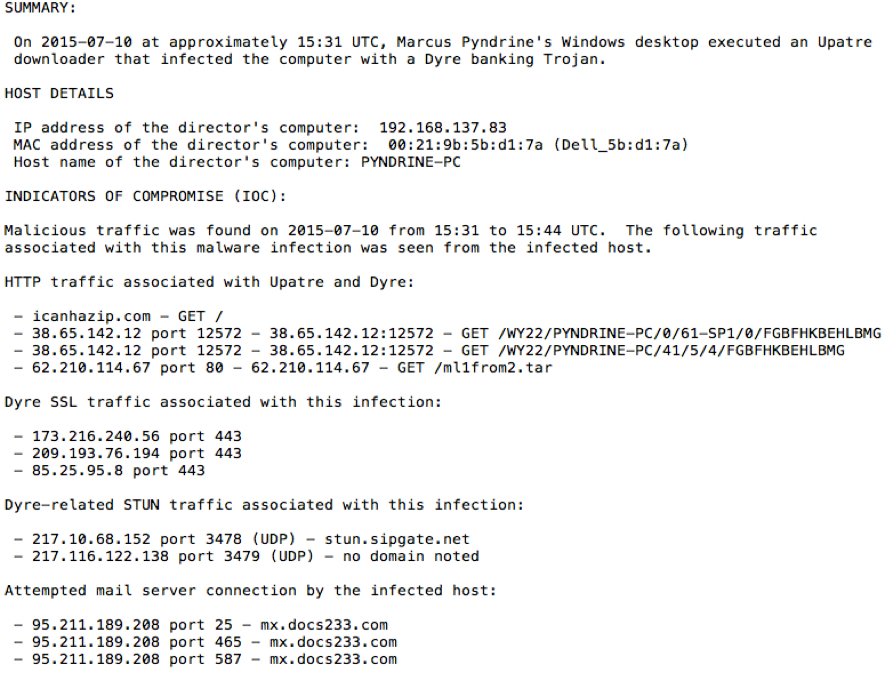
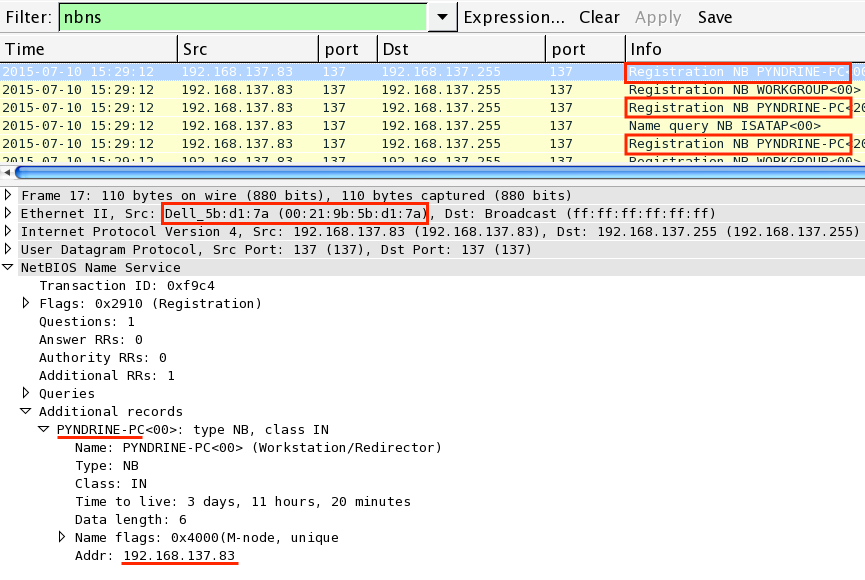
The host name and mac address are easy enough to figure out if you filter on the NBNS traffic:
You can also find this same information in the DHCP traffic.
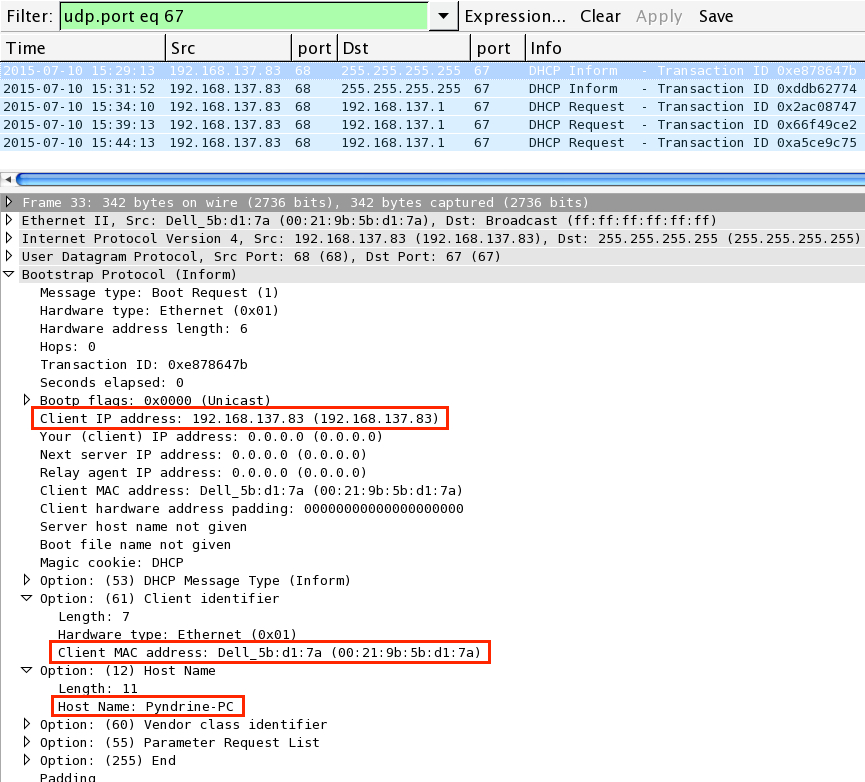
Filter on http.request in Wireshark, and you'll find some HTTP traffic on non-standard ports, and some other unusual GET requests. I've highlighted the important ones below.
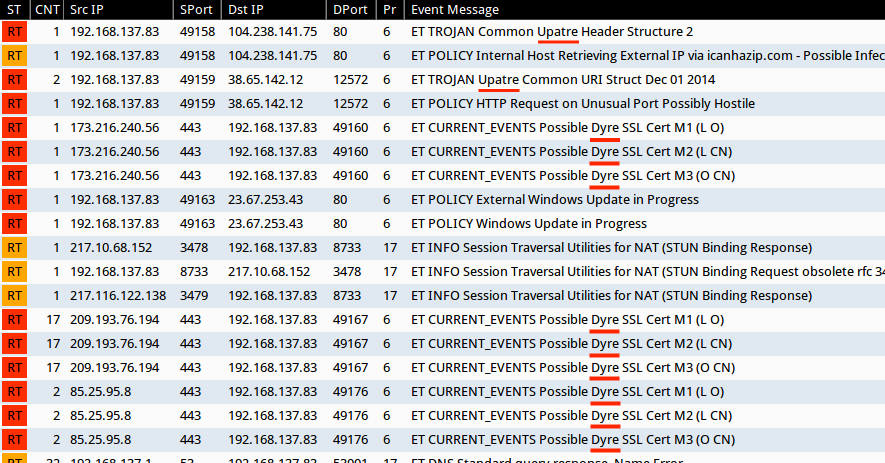
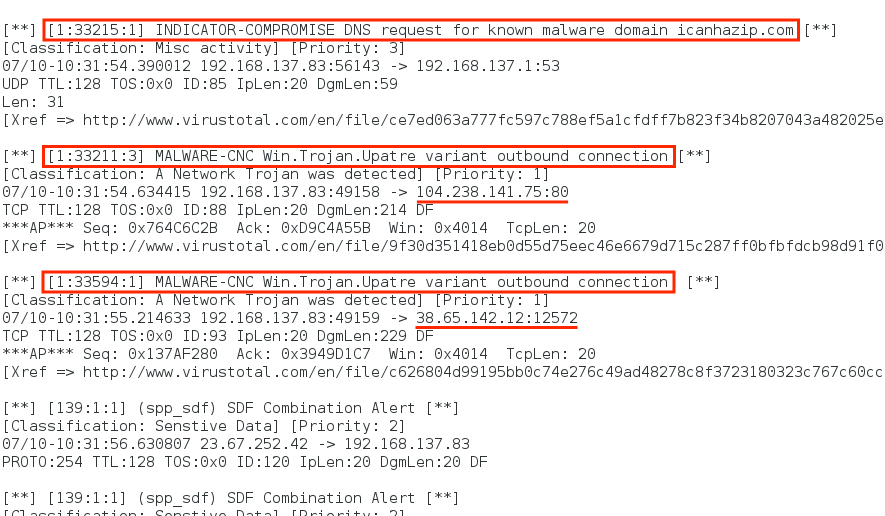
If you don't recongize the traffic, you can use Suricata or Snort to read or playback the pcap. I prefer using Suricata on Security Onion. Using the Emerging Threats signature set (the free version), I found events for Upatre and Dyre after replaying the pcap on Security Onion.
Running Snort 2.9.7.3 using the free Snort subscriber set, I found alerts for Upatre.
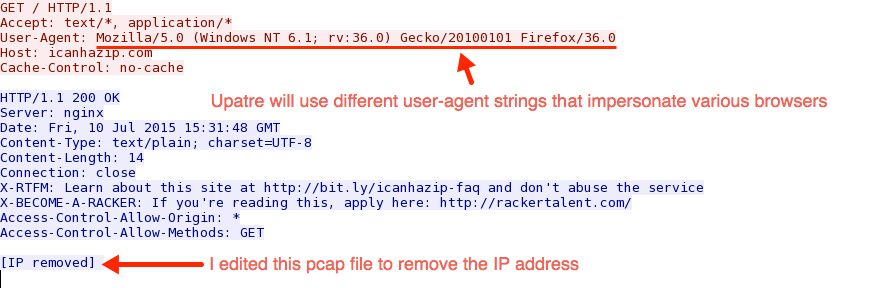
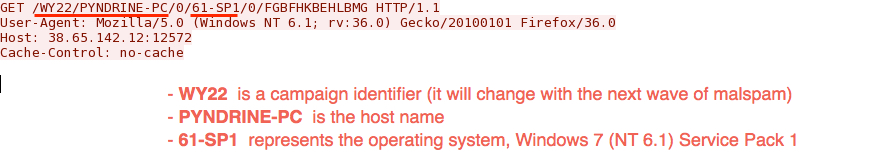
The HTTP GET requests by Upatre have the same user agent, which is fake and often changes. In this case, it's impersonating Firefox 36.0.
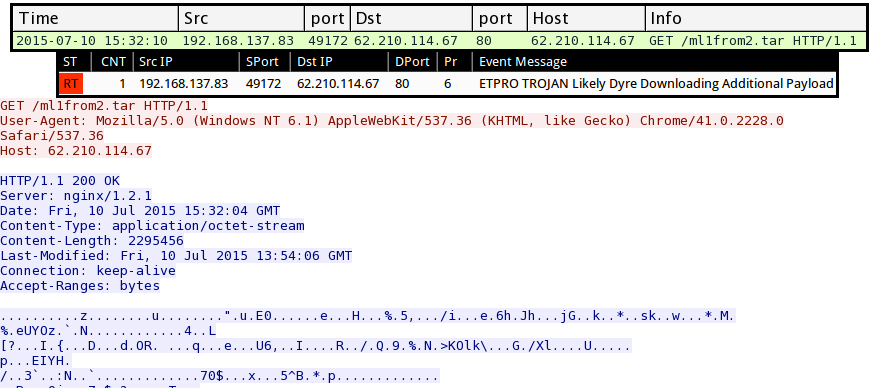
The HTTP GET request shown below is likely Dyre downloading an additional payload.
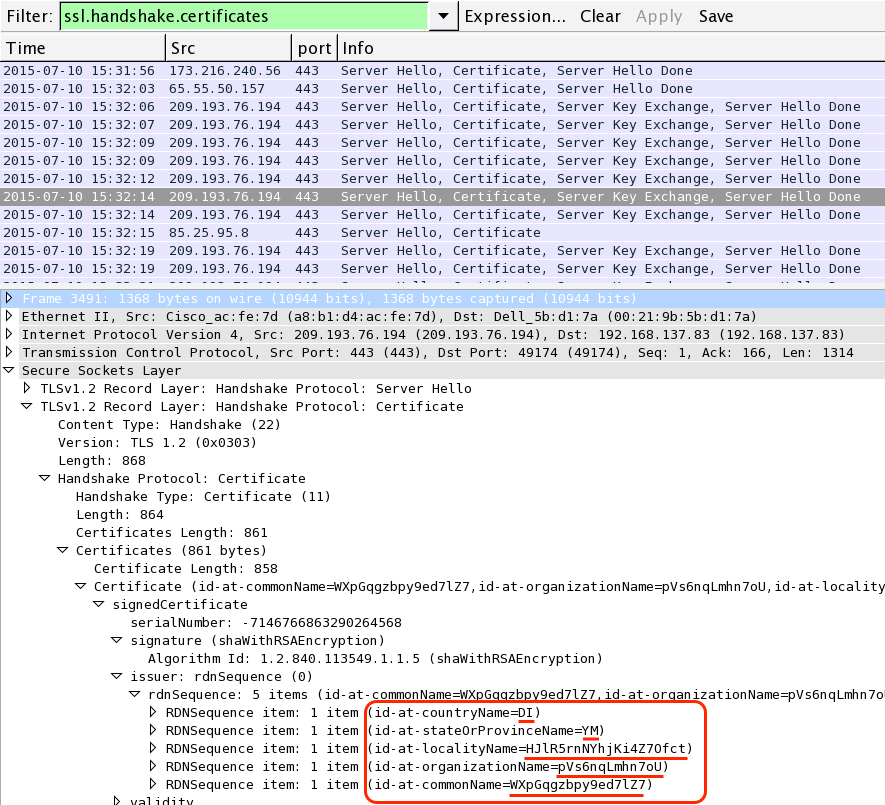
If you filter on ssl.handshake.certificates, you can find certifcates typical for Dyre infection traffic. Notice the random characters used in the country, state, locality, and organization names shown below.
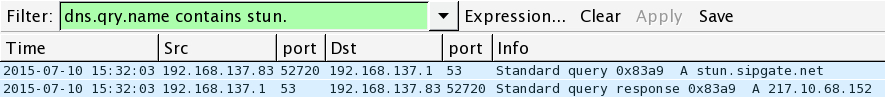
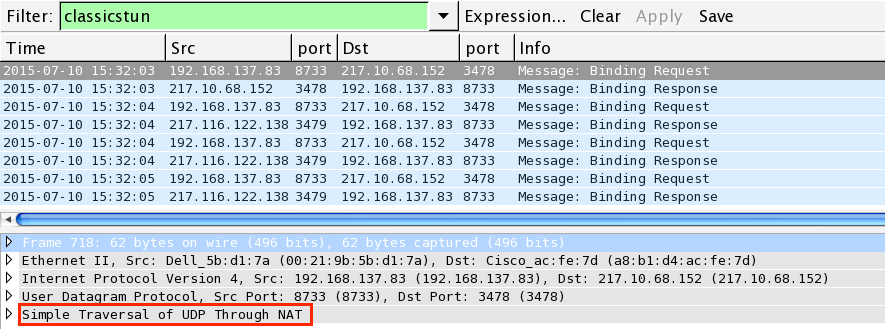
There's usually STUN traffic associated with Dyre (STUN = Simple Traversal of UDP Through NAT). The pcap contains a DNS query for a STUN server and some UDP STUN traffic with 2 public hosts.
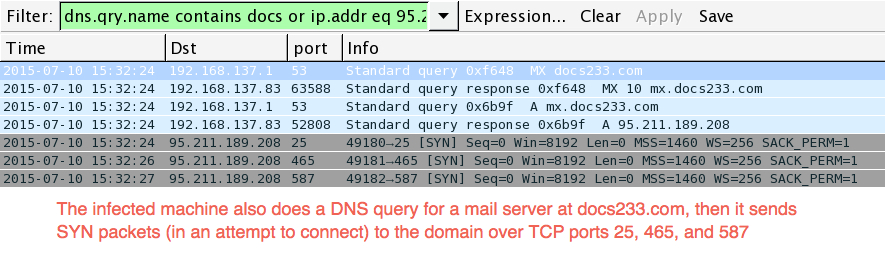
There's also some mail server traffic associated with this infection. Below, you'll find a DNS request for a mail server followed by some SYN packets sent in an attempt to connect with it.
Click here to return to the main page, but remember Pyndrine Industries' official slogan: