2015-07-24 - TRAFFIC ANALYSIS EXERCISE - WHERE'D THE CRYPTOWALL COME FROM?
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
TRAFFIC:
- 2015-07-24-traffic-analysis-exercise.pcap.zip 52.1 MB (52,090,873 bytes)
SCENARIO
You've been hired as an analyst for a small company with approximately 200 employees in an office building. So far, intrusion and malware detection is host-based through a commercial anti-virus product. At this point, network security monitoring consists of a Snort setup using registered Snort rules. You have access to the last 12 hours of network traffic through a SAN server.
On Friday 2015-07-24 at starting at 14:59 UTC, you notice at least a dozen Snort events with the following characteristics:
- Source IP address: 192.168.137[.]85
- Source port: various
- Destination IP address: various
- Destination port: 80
- Signature name: [1:34318:2] MALWARE-CNC Win.Trojan.CryptoWall variant outbound connection
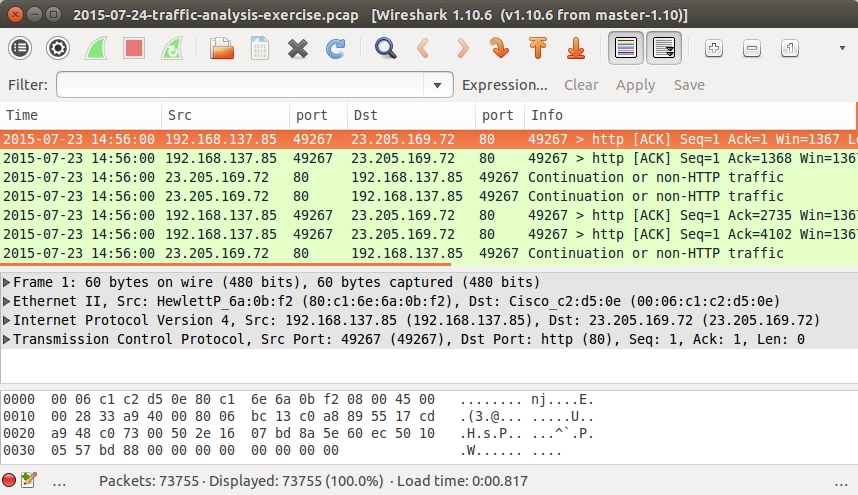
This is post-infecion traffic for CryptoWall ransomware, so it's time to investigate! You retrieve a pcap from the SAN server. The pcap has all network traffic by 192.168.137[.]85 from 14:56 to 15:04 UTC.
Due to a synchronization issue when the traffic was recorded, your pcap has the wrong date. It reads 2015-07-23, but it should be 2015-07-24. All times in the pcap appear to be correct.
You know CryptoWall 3.0 has been making the rounds. This malware has been seen from malicious spam and different exploit kits. Your gut feeling? This CryptoWall infection was probably caused by an exploit kit. You'll need to prove it, though.
YOUR TASK
Investigate the pcap and document your findings. Your report should include:
- The infected computer's host name
- The infected computer's MAC address
- The infected computer's operating system and browser
- Exploit kit (Angler, Magnitude, or Nuclear?)
- IP address and domain name used by the exploit kit
- Compromised website that caused the exploit kit traffic
- Domains and IP addresses from the CryptoWall 3.0 post-infection traffic
- What was vulnerable one the user's computer (the browser, Flash, Java, Silverlight, etc.)?
ANSWERS
- Click here for the answers.