2015-09-23 - TRAFFIC ANALYSIS EXERCISE - ANSWERS
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive containing the pcap: 2015-09-23-traffic-analysis-exercise.pcap.zip 1,257,973 bytes (1.3 MB)
NOTES:
- @MalwareKiwi posted answers to this exercise on a blog at: http://malware.kiwi/2015-09-23-traffic-analysis-exercise-results/
- My answers are below...
ANSWERS
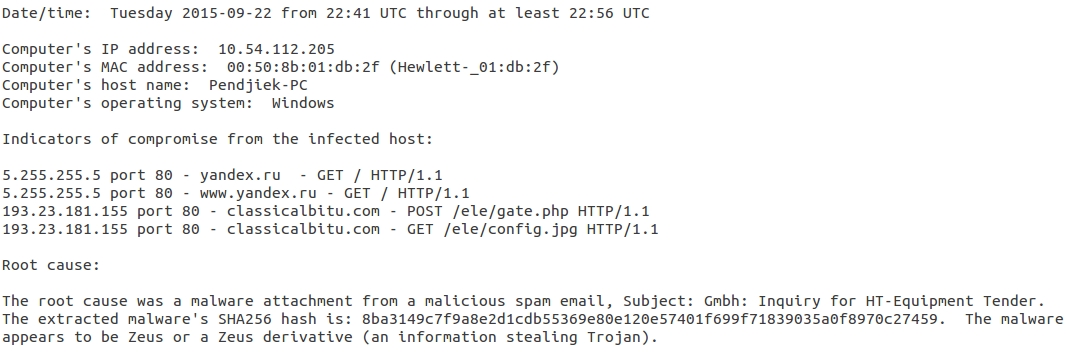
Below is an example of the documentation for this investigation:
TRAFFIC REVIEW
Make sure when you downloaded the pcap that you recieved the full 1.5 MB of data. As always, I suggest you change your column display in Wireshark as shown here.
First things first. Let's filter on http.request and see what we have.
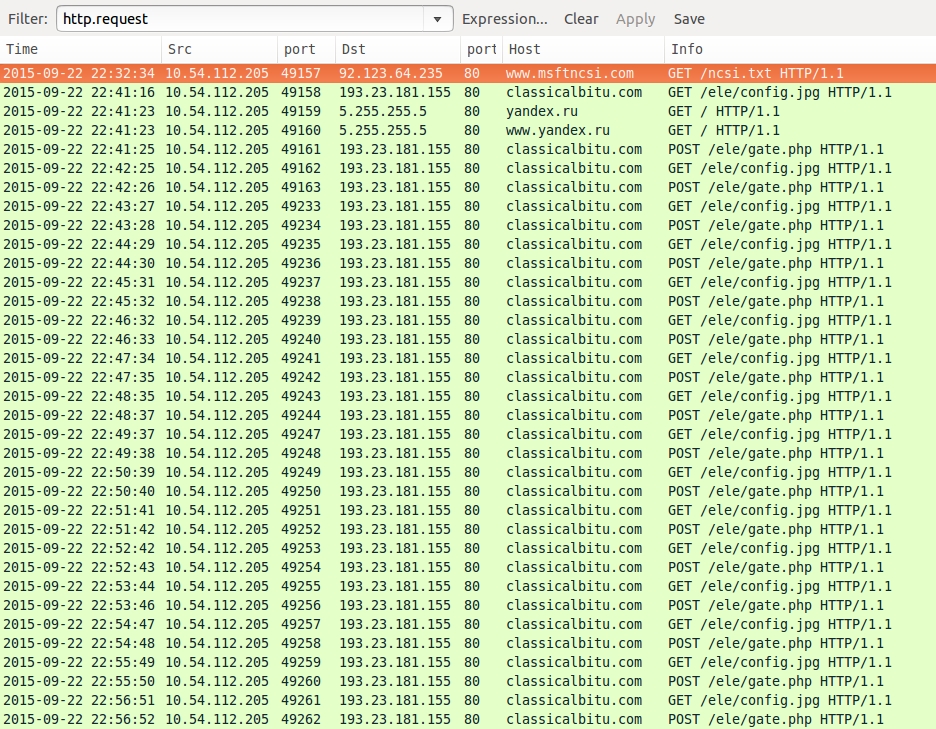
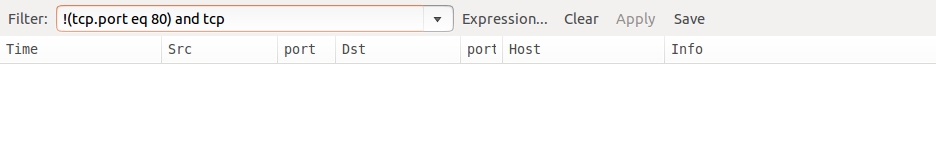
We have some HTTP GET and POST requests with nothing else in the pcap. A quick check shows no other TCP traffic.
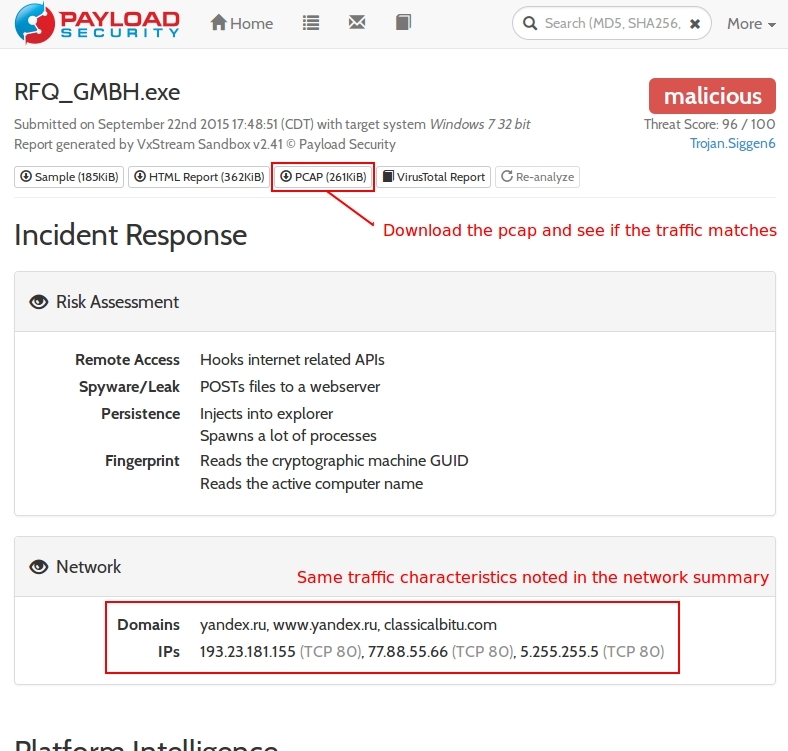
So what's the cause? We won't find anything more from the pcap. For now, we'll have to search Google for the IP addresses and domain names. Try them individually or all together. Eventually, you should find the results of a malware analysis at hybrid-analysis.com (see the top search result in the image below).
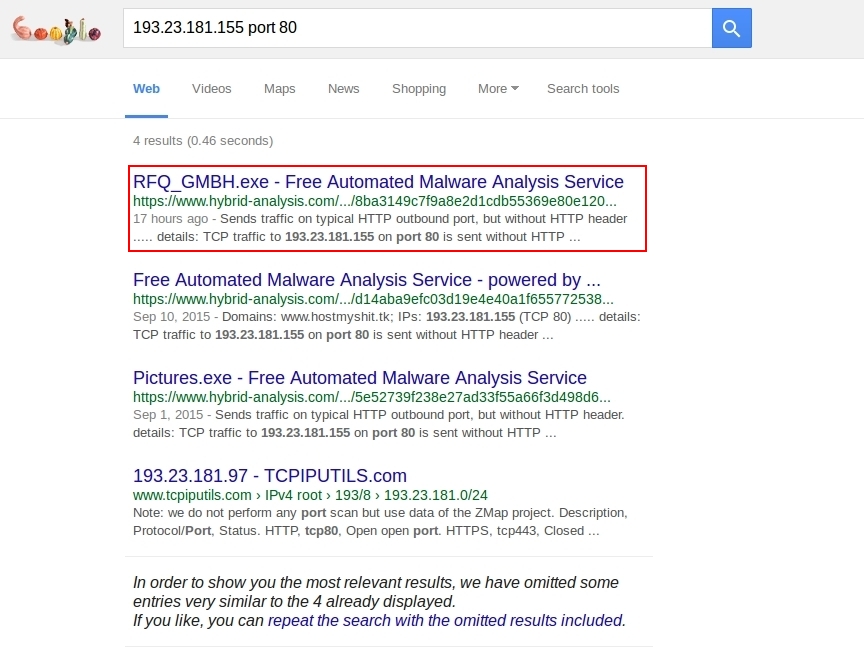
Looking through the hybrid-analysis.com results, you'll find the same traffic characteristics as seen in our pcap. Download and examine hybrid-analysis.com's pcap to confirm it has the same traffic patterns.
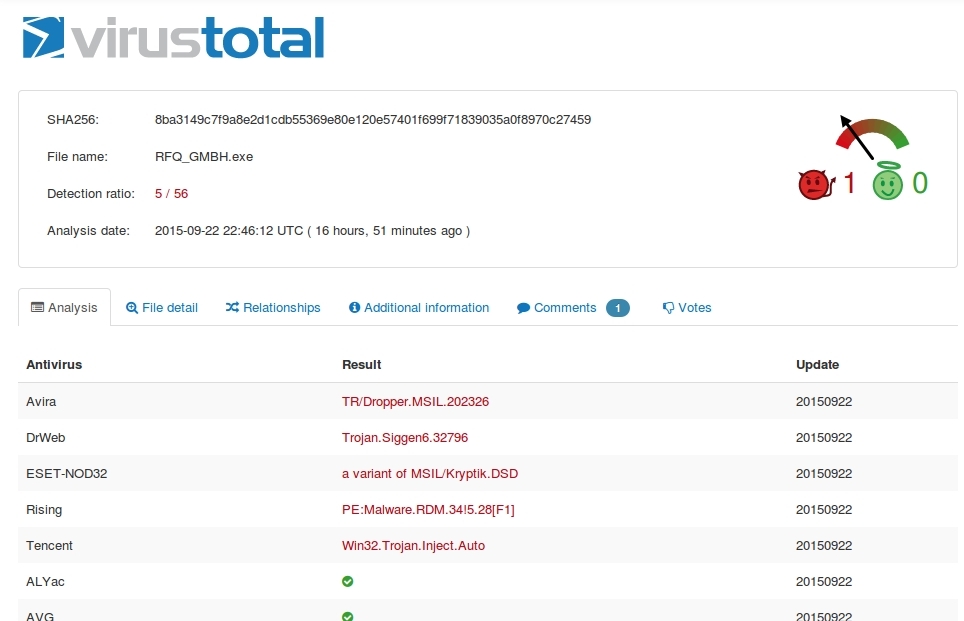
Go to the VirusTotal results for this malware. You can get to it using the "VirusTotal Report" button from the hybrid-analysis.com report.
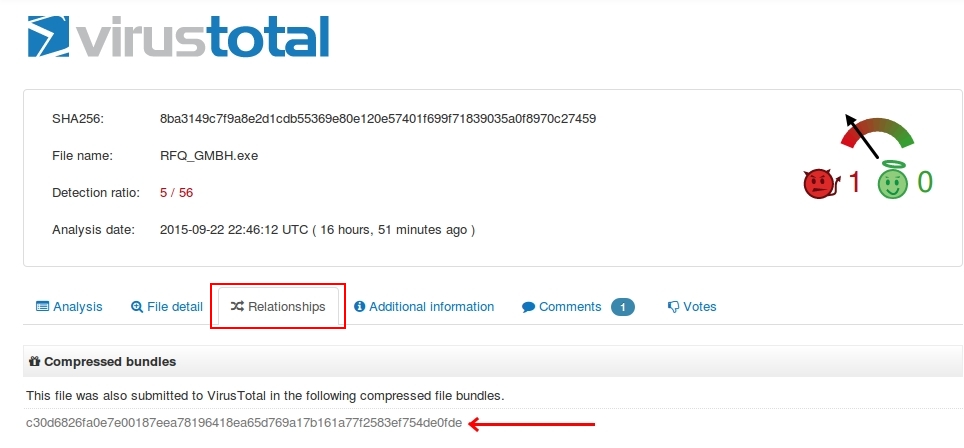
The "Relationships" tab will let you know if the .exe file was taken from a .zip archive. At least it will if someone has submitted the .zip archive to VirusTotal. Fortunately, someone has. Just click on that file hash to see VirusTotal's report on the .zip archive.
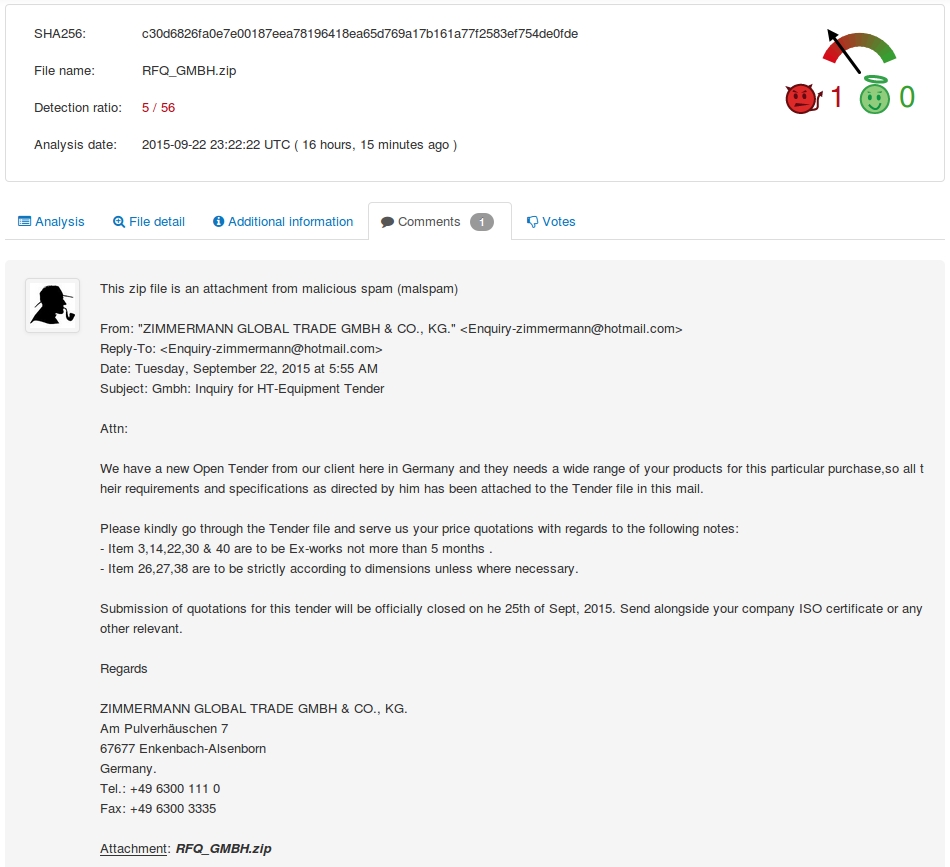
And here's the report. You'll note it has comments.
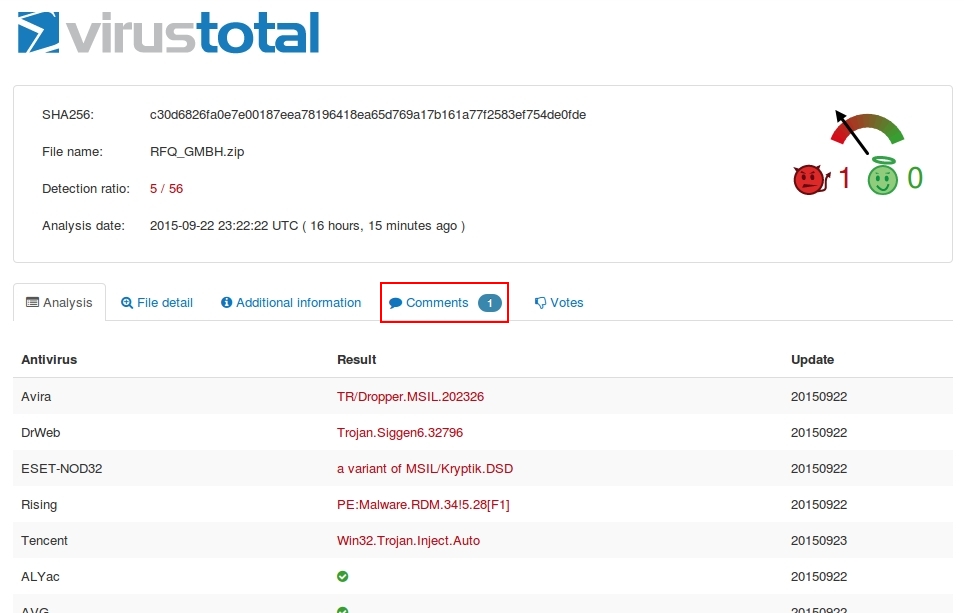
The majority of people submit malware to VirusTotal without inlcuding any comments. In this case, some helpful person posted a comment indicating the .zip archive came from an email. I encourage anyone submitting malware to VirusTotal to leave a comment, if possible. You'll be doing the community a favor.
What, exactly, is this malware? You can also submit the pcap to VirusTotal and see what alerts were triggered. Traffic in the pcap triggered alerts for Zeus or some sort of Zeus variant. Zeus is a password stealer.
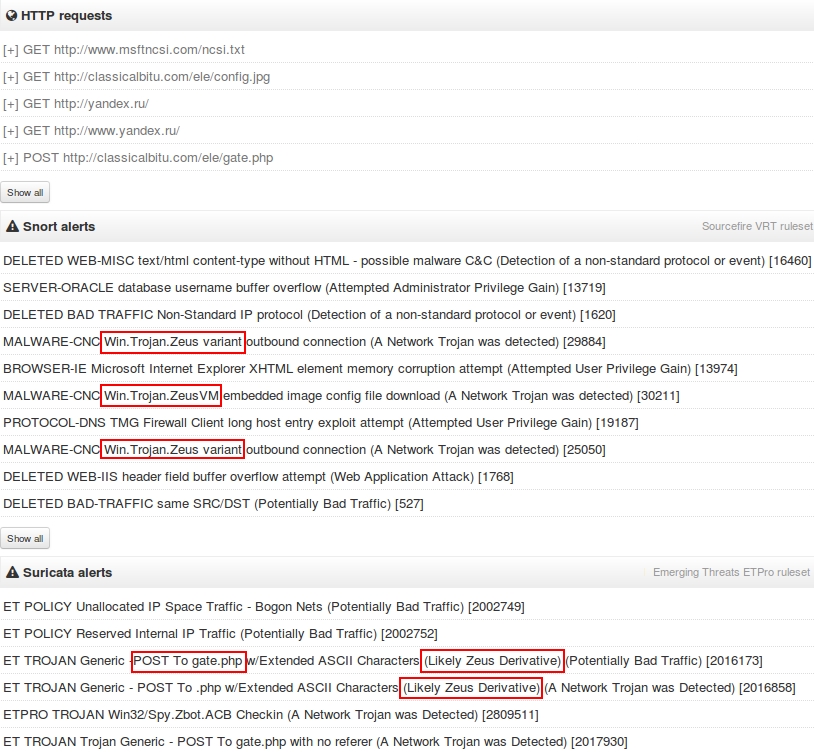
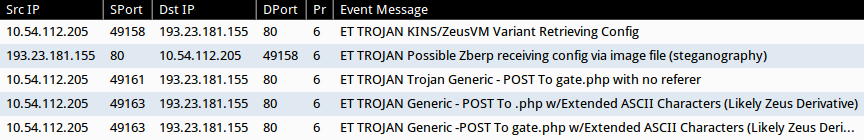
I also used tcpreplay on Security Onion set up with Suricata and the EmergingThreats signature set. I got mostly the same results as VirusTotal found.
FINAL WORDS
Hopefully, this exercise has helped improve your traffic analysis skills. Thanks for following along!
I crack myself up...
Click here to return to the main page.
