2016-05-05 - THURSDAY MALWARE HUNT - LOCKY RANSOMWARE AND DRIDEX
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-05-05-malware-data.zip 957.4 kB (957,368 bytes)
NOTES:
The Palo Alto Networks Unit 42 blog about Locky ransomware can be found here, and Proofpoint's blog about Dridex actors sending Locky ransomware is available here.
Zip attachments sent by "Jaypee" (a spoofed sender) contain text files, but the files names have no extentions. I ran them after appending .js to the file names.
EMAILS AND ATTACHMENTS
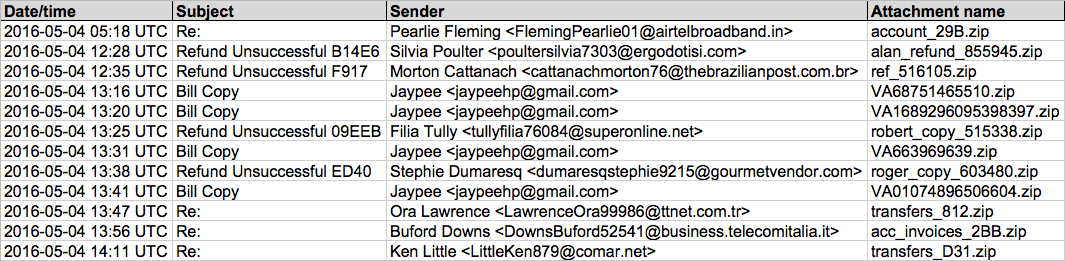
Shown above: Data from the .csv spreadsheet on 12 examples from today's emails.
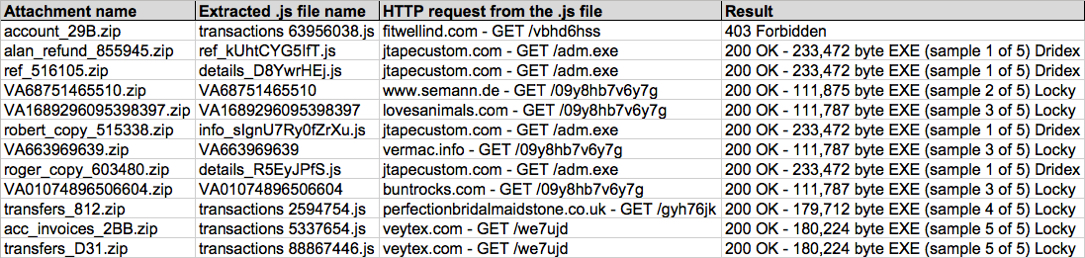
Shown above: Data from the .csv spreadsheet on 12 attachments from today's emails.
TRAFFIC
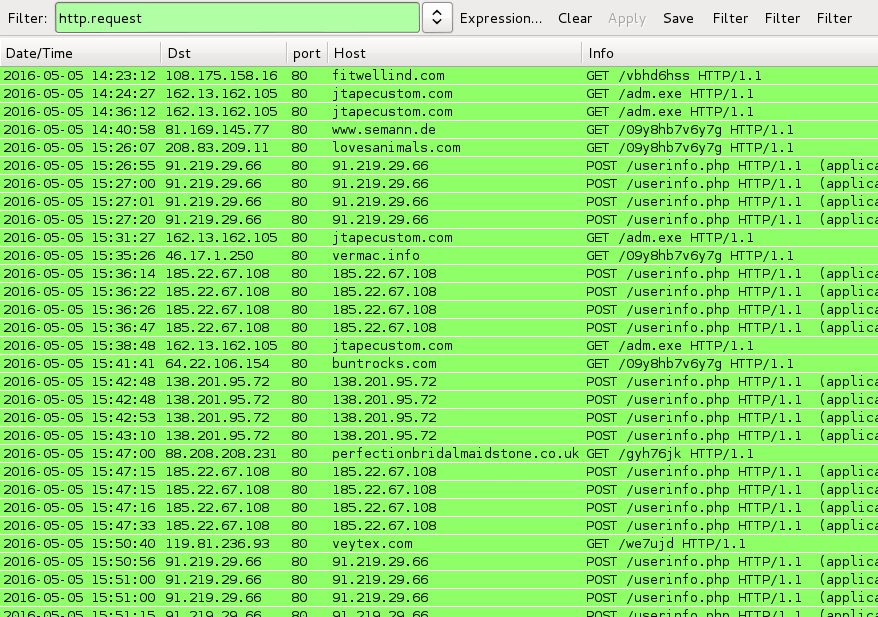
Shown above: Traffic from executing the extracted .js files, filtered in Wireshark.
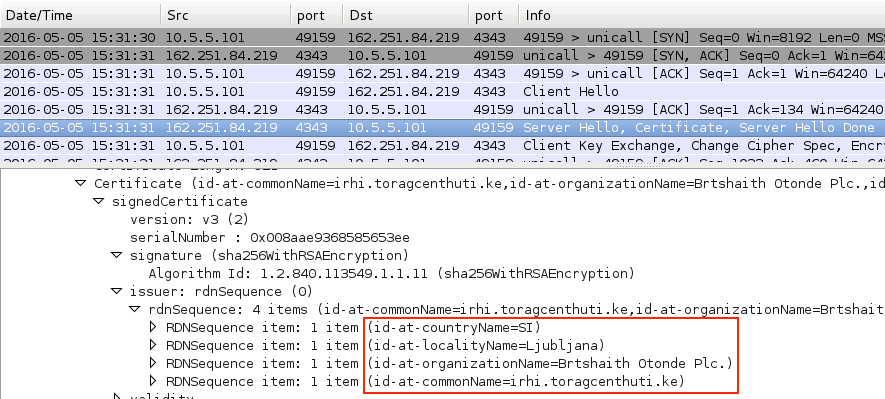
Shown above: Post-infection traffic seen from the Dridex sample.
DRIDEX INFECTION TRAFFIC:
- 162.13.162[.]105 port 80 - jtapecustom[.]com - GET /adm.exe [HTTP request by .js files for Dridex]
- 162.251.84[.]219 port 4343 [Dridex post-infection TLS traffic]
HTTP REQUEST BY .JS FILES FOR LOCKY RANSOMWARE:
- 108.175.158[.]16 port 80 - fitwellind[.]com - GET /vbhd6hss
- 81.169.145[.]77 port 80 - www.semann[.]de - GET /09y8hb7v6y7g
- 208.83.209[.]11 port 80 - lovesanimals[.]com - GET /09y8hb7v6y7g
- 46.17.1[.]250 port 80 - vermac[.]info - GET /09y8hb7v6y7g
- 64.22.106[.]154 port 80 - buntrocks[.]com - GET /09y8hb7v6y7g
- 88.208.208[.]231 port 80 - perfectionbridalmaidstone[.]co[.]uk - GET /gyh76jk
- 119.81.236[.]93 port 80 - veytex[.]com - GET /we7ujd
LOCKY RANSOMWARE POST-INFECTION TRAFFIC:
- 91.219.29[.]66 port 80 - 91.219.29[.]66 - POST /userinfo.php
- 138.201.95[.]72 port 80 - 138.201.95[.]72 - POST /userinfo.php
- 185.22.67[.]108 port 80 - 185.22.67[.]108 - POST /userinfo.php
ZIP ARCHIVE CONTENTS
- 2016-05-05-email-tracker.csv (2,476 bytes)
- attachments\VA01074896506604.zip (6,411 bytes)
- attachments\VA1689296095398397.zip (6,410 bytes)
- attachments\VA663969639.zip (6,381 bytes)
- attachments\VA68751465510.zip (6,393 bytes)
- attachments\acc_invoices_2BB.zip (13,090 bytes)
- attachments\account_29B.zip (13,519 bytes)
- attachments\alan_refund_855945.zip (10,038 bytes)
- attachments\ref_516105.zip (9,686 bytes)
- attachments\robert_copy_515338.zip (10,121 bytes)
- attachments\roger_copy_603480.zip (10,064 bytes)
- attachments\transfers_812.zip (13,177 bytes)
- attachments\transfers_D31.zip (13,087 bytes)
- extracted-files\VA01074896506604 (13,354 bytes)
- extracted-files\VA1689296095398397 (13,362 bytes)
- extracted-files\VA663969639 (13,312 bytes)
- extracted-files\VA68751465510 (13,336 bytes)
- extracted-files\details_D8YwrHEj.js (26,453 bytes)
- extracted-files\details_R5EyJPfS.js (27,491 bytes)
- extracted-files\info_sIgnU7Ry0fZrXu.js (27,419 bytes)
- extracted-files\ref_kUhtCYG5IfT.js (27,741 bytes)
- extracted-files\transactions 2594754.js (533,236 bytes)
- extracted-files\transactions 5337654.js (533,212 bytes)
- extracted-files\transactions 63956038.js (536,491 bytes)
- extracted-files\transactions 88867446.js (533,179 bytes)
- malspam\2016-05-05-0518-UTC.eml (19,801 bytes)
- malspam\2016-05-05-1228-UTC.eml (15,411 bytes)
- malspam\2016-05-05-1235-UTC.eml (14,933 bytes)
- malspam\2016-05-05-1316-UTC.eml (12,012 bytes)
- malspam\2016-05-05-1320-UTC.eml (12,026 bytes)
- malspam\2016-05-05-1325-UTC.eml (15,542 bytes)
- malspam\2016-05-05-1331-UTC.eml (11,958 bytes)
- malspam\2016-05-05-1338-UTC.eml (15,484 bytes)
- malspam\2016-05-05-1341-UTC.eml (12,031 bytes)
- malspam\2016-05-05-1347-UTC.eml (19,317 bytes)
- malspam\2016-05-05-1356-UTC.eml (19,286 bytes)
- malspam\2016-05-05-1411-UTC.eml (19,188 bytes)
- malware-from-the-infected-host\2016-05-05-Locky_HELP_instructions.bmp (4,006,594 bytes)
- malware-from-the-infected-host\2016-05-05-Locky_HELP_instructions.html (2,086 bytes)
- malware-from-the-infected-host\2016-05-05-malware-from-js-malspam-sample-1-of-5-Dridex.exe (233,472 bytes)
- malware-from-the-infected-host\2016-05-05-malware-from-js-malspam-sample-2-of-5-Locky.exe (111,875 bytes)
- malware-from-the-infected-host\2016-05-05-malware-from-js-malspam-sample-3-of-5-Locky.exe (111,787 bytes)
- malware-from-the-infected-host\2016-05-05-malware-from-js-malspam-sample-4-of-5-Locky.exe (179,712 bytes)
- malware-from-the-infected-host\2016-05-05-malware-from-js-malspam-sample-5-of-5-Locky.exe (180,224 bytes)
Click here to return to the main page.
