2016-07-07 - "PIZZACRYPTS" (BANDARCHOR) RANSOMWARE (REALLY? PIZZACRYPTS?)
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-07-07-Neutrino-EK-sends-PizzaCrypts-ransomware.pcap.zip 254.5 kB (254,456 bytes)
- 2016-07-07-Neutrino-EK-sends-PizzaCrypts-ransomware.pcap (273,028 bytes)
- Z2016-07-07-Neutrino-EK-and-PizzaCrypts-ransomware-files.zip 195.2 kB (195,213 bytes)
- 2016-07-07-Neutrino-EK-flash-exploit.swf (79,659 bytes)
- 2016-07-07-Neutrino-EK-landing-page.txt (3,199 bytes)
- 2016-07-07-Neutrino-EK-payload-PizzaCrypts-ransomware.exe (172,034 bytes)
- Pizzacrypts Info.txt (772 bytes)
NOTES:
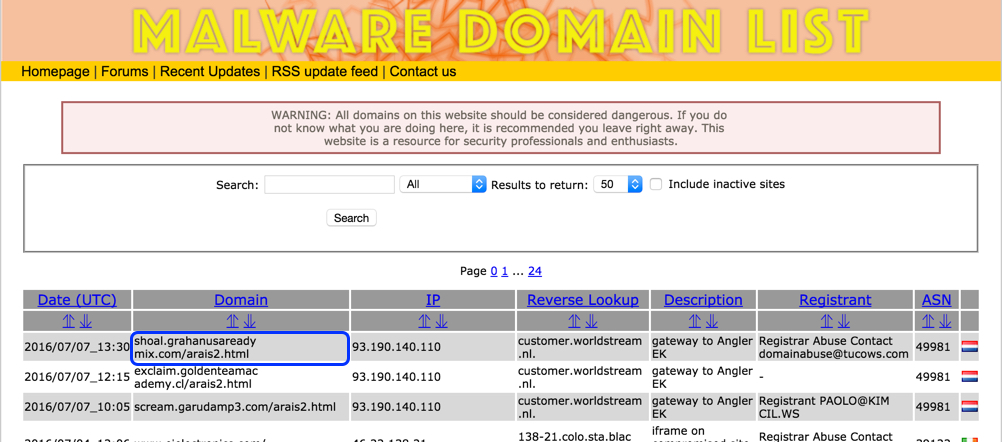
- Saw a campaign noted on MalwareDomainList that used Neutrino EK to send ransomware. This ransomware prominently used the term "pizzacrypts."
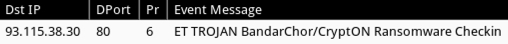
- Follow-up note that this is actually Bandarchor ransomware.
Shown above: My initial tipper for today's traffic.
- This ransomware might be associated with the term "pizzacrypts," but the Proofpoint ET rule I saw on the post-infection traffic was created in early- to mid-June 2016 for Bandarchor ransomware.
Shown above: EmergningThreats rule hit on the post-infection traffic.
TRAFFIC
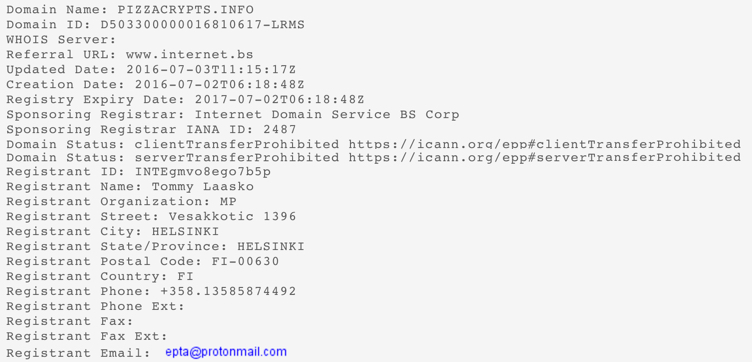
Shown above: Traffic from today's infection filtered in Wireshark.
ASSOCIATED DOMAINS:
- 93.190.140[.]110 port 80 - shoal.grahanusareadymix[.]com - GET /arais2.html - [initial URL]
- 68.233.35[.]11 port 80 - xczc.b2gmffy[.]eu - GET /vmh.cgi?4 - [redirect]
- 185.141.25[.]158 port 80 - j63d.lbhlp52[.]top - [Neutrino EK]
- 93.115.38[.]30 port 80 - avtoship[.]com - POST /123/index.php - [Post-infection traffic from the ransomware]
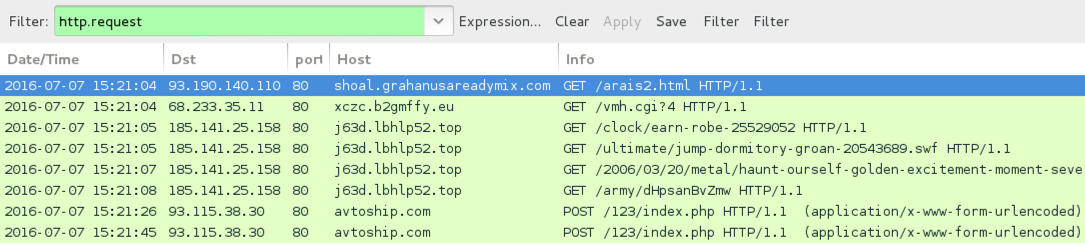
ADDRESSES FROM THE DECRYPT INSTRUCTIONS:
- Primary email: maestro@pizzacrypts[.]info
- Secondary email: pizzacrypts@protonmail[.]com
- Bitmessage: BM-NBRCUPTenKgYbLVCAfeVUHVsHFK6Ue2F
Shown above: Whois data on pizzacrypts[.]info, registered 5 days ago.
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: ba6a5230dbf6f0c016976a1be77796088e028899cd0e2bdf131fa452763b75d4
File name: 2016-07-07-Neutrino-EK-flash-exploit.swf
MALWARE PAYLOAD:
- SHA256 hash: d6818864dc9e10b15c88aca4d1e8fd971eff43572beba3001fd6c96028afd9f3
File name: 2016-07-07-Neutrino-EK-payload-PizzaCrypts-ransomware.exe
OTHER IMAGES
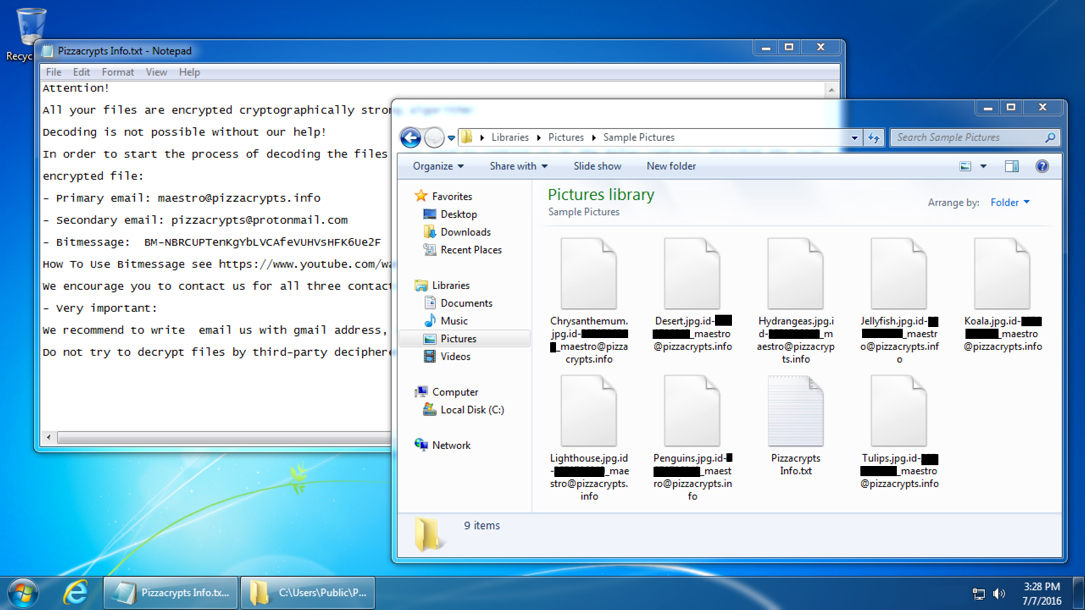
Shown above: Desktop of the infected Windows host.
Click here to return to the main page.