2016-08-08 - LOCKY RANSOMWARE INFECTION FROM EMAIL ATTACHMENT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-08-08-Locky-ransomware-infection-traffic.pcap.zip 705.8 kB (705,774 bytes)
- 2016-08-08-Locky-ransomware-infection-traffic.pcap (873,563 bytes)
- 2016-08-08-Locky-ransomware-files.zip 250.5 kB (250,529 bytes)
- 2016-08-08-Locky-ransomware-email-0939-UTC.eml (12,356 bytes)
- 2016-08-08-Locky-ransomware-instructions.bmp (3,721,466 bytes)
- 2016-08-08-Locky-ransomware-instructions.html (100,07 bytes)
- 2016-08-08-Locky-ransomware.exe (281,600 bytes)
- IMG(6,559).zip (7,041 bytes)
- Photo195.wsf (32,253 bytes)
NOTES:
- Waves of emails pushing Locky ransomware (the ".zepto" variant) continue on a near-daily basis.
- This post has only one sample. It documents a recent pattern change in .zepto variant Locky ransomware's post-infection traffic.
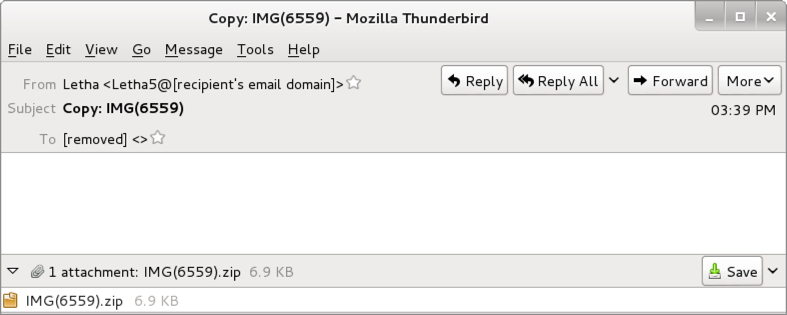
Shown above: An example from this wave of emails.
Shown above: Email headers.
ATTACHMENT
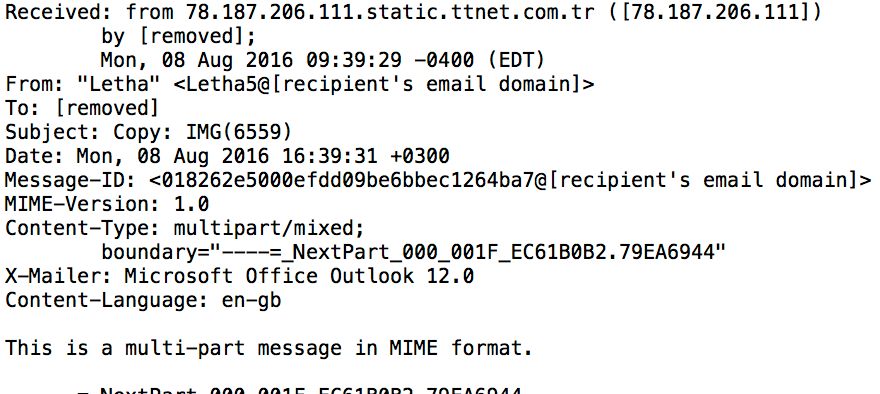
Shown above: Attachment and extracted .wsf file.
TRAFFIC
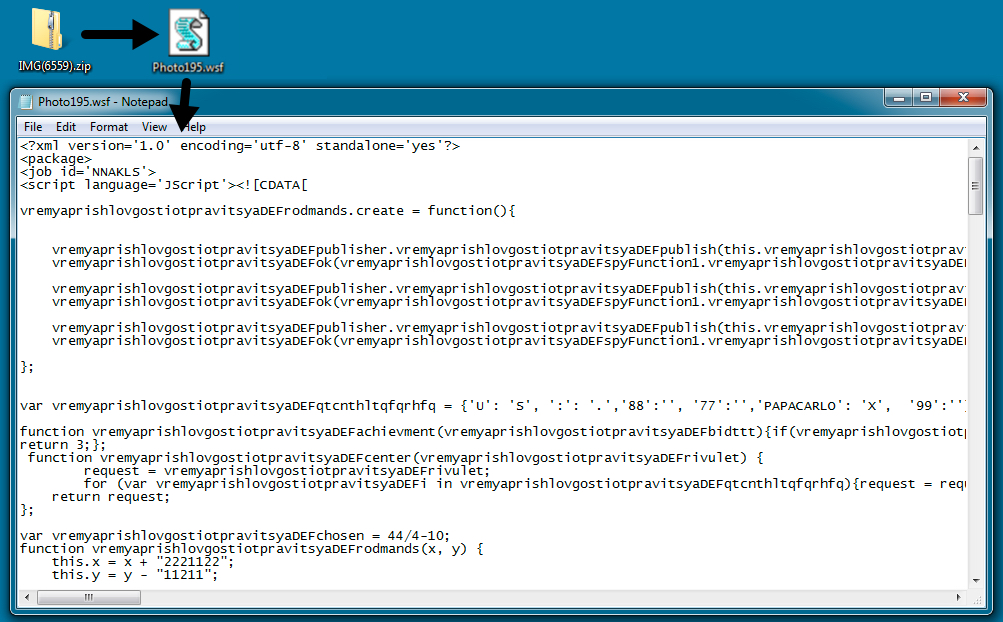
Shown above: Traffic generated from the extracted .wsf file.
ASSOCIATED DOMAINS:
- 108.60.15[.]36 port 80 - nflfootballpool[.]ca - GET /988g765f?kyudVHTd=LetXYvHUJDE [initial download of .exe]
- 185.129.148[.]19 port 80 - 185.129.148[.]19 - POST /php/upload.php [callback]
- 213.205.40[.]169 port 80 - www.azetapiemonte[.]it - GET /988g765f?BzWfzNh=nSQAkwir [follow-up download of the same .exe]
- 208.71.106[.]35 port 80 - keramago.web.fc2[.]com - GET /988g765f?SEhkUhewzxB=VvmKzoiC [follow-up download of the same .exe]
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- zjfq4lnfbs7pncr5[.]tor2web[.]org
- zjfq4lnfbs7pncr5[.]onion[.]to
FILE HASHES
LOCKY RANSOMWARE SAMPLE FROM THE INFECTED HOST:
- SHA256 hash: 21d92fa81d5748c9981f4aa2ade97c1b04e264457bb2c610263476000036ade1
File name: 2016-08-08-Locky-ransomware.exe
IMAGES
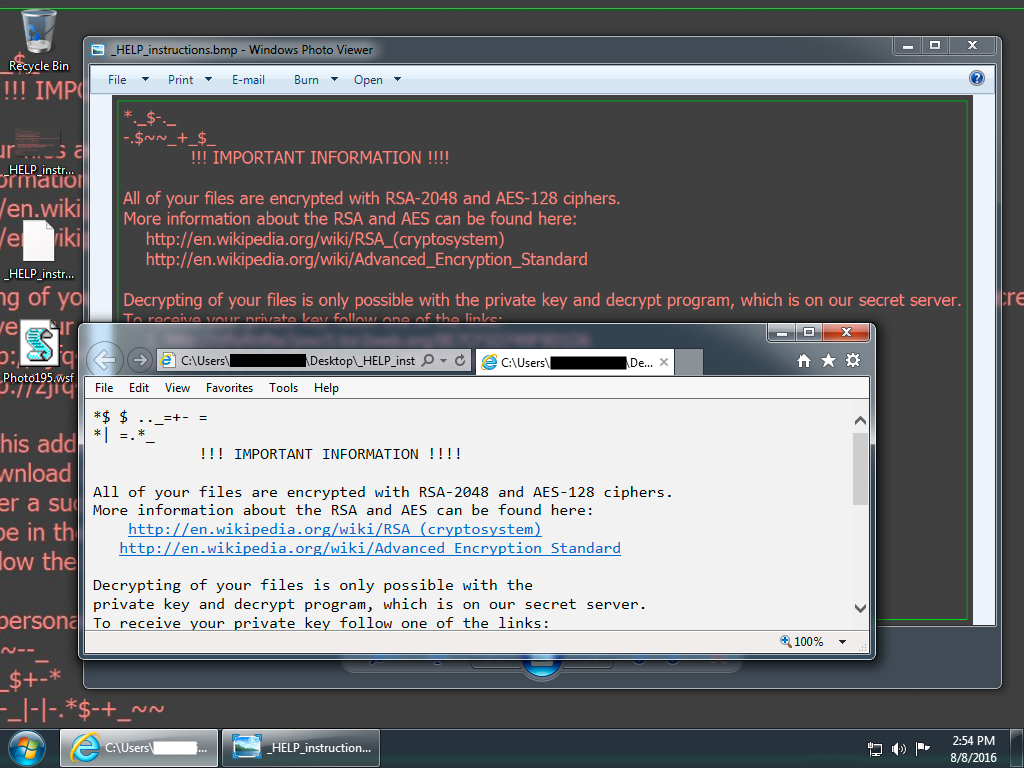
Shown above: Infected Windows desktop after double-clicking the .wsf file.
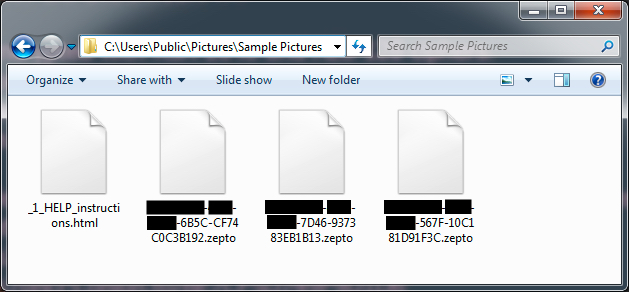
Shown above: Re-named encrypted files showing this is the .zepto variant of Locky ransomware.
Click here to return to the main page.
