2016-10-12 - PSEUDO-DARKLEECH RIG EK FROM 109.234.36[.]39 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-12-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware.pcap.zip 428.8 kB (428,780 bytes)
- 2016-10-12-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware.pcap (550,739 bytes)
- 2016-10-12-pseudoDarkleech-Rig-EK-and-Cerber-ransomware-files.zip 752.2 kB (752,195 bytes)
- 2016-10-12-Cerber-ransomware-decryption-instructions-README.hta (63,059 bytes)
- 2016-10-12-Cerber-ransomware-decryption-instructions.bmp (1,920,054 bytes)
- 2016-10-12-page-from-joellipman_com-with-injected-script.txt (136,590 bytes)
- 2016-10-12-pseudoDarkleech-Rig-EK-flash-exploit.swf (25,457 bytes)
- 2016-10-12-pseudoDarkleech-Rig-EK-landing-page.txt (30,234 bytes)
- 2016-10-12-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware.exe (490,497 bytes)
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-22 - PaloAlto Networks Unit 42 blog: Campaign Evolution: Darkleech to Pseudo-Darkleech and Beyond
- 2016-07-02 - SANS ISC diary: Change in patterns for the pseudoDarkleech campaign
- 2016-09-14 - Malware-traffic-analysis.net: The pseudoDarkleech campaign starts using Rig EK instead of Neutrino EK
- 2016-10-03 - Malware-traffic-analysis.net: The pseudoDarkleech campaign stops sending CryptXXX, starts sending Cerber ransomware
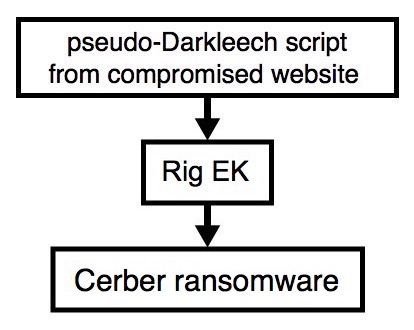
Shown above: Flowchart for this infection traffic.
TRAFFIC
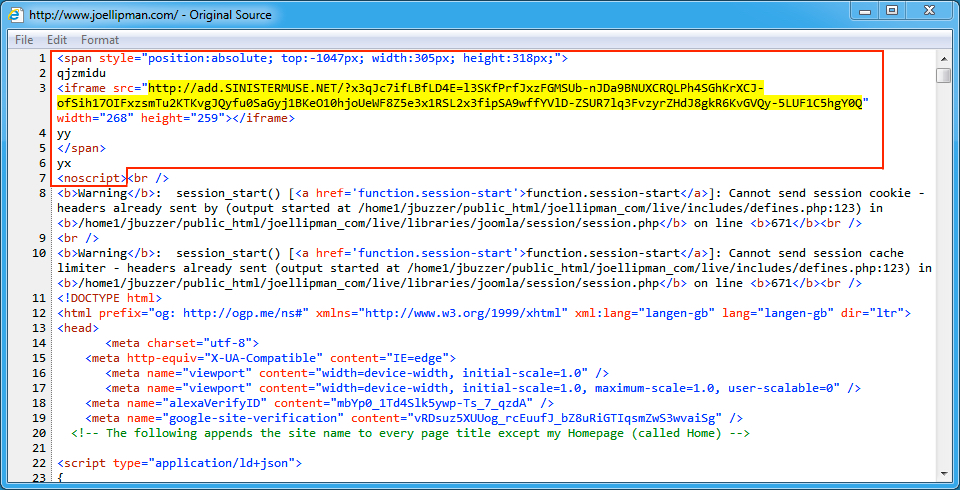
Shown above: Injected script from the pseudoDarkleech campaign in a page from the compromised site.
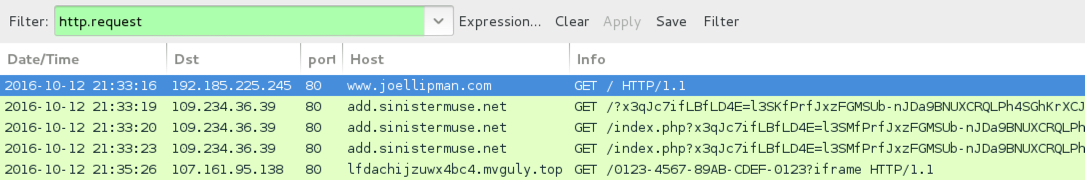
Shown above: Traffic from the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- www.joellipman[.]com - Compromised site
- 109.234.36[.]39 port 80 - add.sinistermuse[.]net - Rig EK
- 31.184.234[.]0 - 31.184.235[.]255 port 6892 (UDP) - UDP traffic caused by Cerber ransomware
- 107.161.95[.]138 port 80 - lfdachijzuwx4bc4.mvguly[.]top - HTTP traffic caused by Cerber ransomware
OTHER DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- lfdachijzuwx4bc4.rbrkng[.]bid
- lfdachijzuwx4bc4[.]onion[.]to
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 9a4bd98a72ea8b547027943e9876a3d90e86314b1a95dff65e7f9455e423e0cb
File name: 2016-10-12-pseudoDarkleech-Rig-EK-flash-exploit.swf (25,457 bytes)
PAYLOAD:
- SHA256 hash: ef1c5cf88a746167647638c3809576366cac31bd6f099f60e55c537af602a050
File name: 2016-10-12-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware.exe (490,497 bytes)
IMAGES
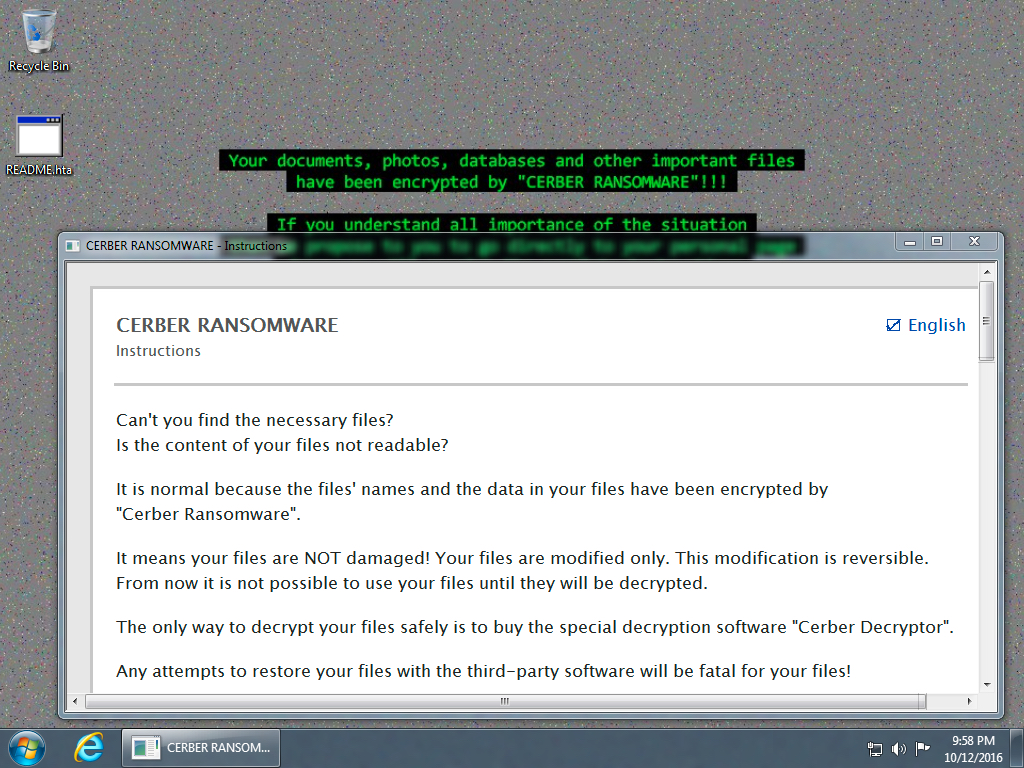
Shown above: Desktop of an infected Windows host after rebooting.
Click here to return to the main page.