2016-10-14 - AFRAIDGATE RIG EK FROM 194.87.237[.]217 SENDS LOCKY RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-14-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap.zip 313.3 kB (313,279 bytes)
- 2016-10-14-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap (335,459 bytes)
- 2016-10-14-Afraidgate-Rig-EK-and-Locky-ransomware-files.zip 314.4 kB (314,402 bytes)
- 2016-10-14-Afraidgate-Rig-EK-flash-exploit.swf (50,368 bytes)
- 2016-10-14-Afraidgate-Rig-EK-landing-page.txt (30,237 bytes)
- 2016-10-14-Afraidgate-Rig-EK-payload-Locky-ransomware-downloader.exe (58,368 bytes)
- 2016-10-14-followup-malware-Locky-ransomware.exe (190,976 bytes)
- 2016-10-14-page-from-investmentpropertiesmexico_com-with-injected-script.txt (100,478 bytes)
- 2016-10-14-round.luc-hariamn_com-scripts-imagesloaded.min.js.txt (393 bytes)
- _HOWDO_text.bmp (3,721,466 bytes)
- _HOWDO_text.html (9,363 bytes)
NOTES:
- My most recent report on the Afraidgate campaign can be found here.
- Thanks to Jeremy Glass for discovering this particular infection chain and sharing the info.
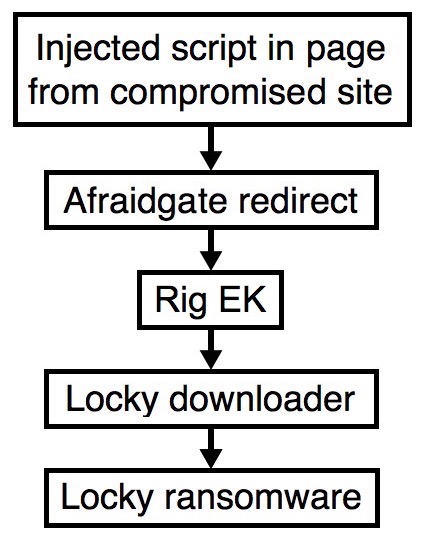
Shown above: Flowchart for this infection traffic.
TRAFFIC
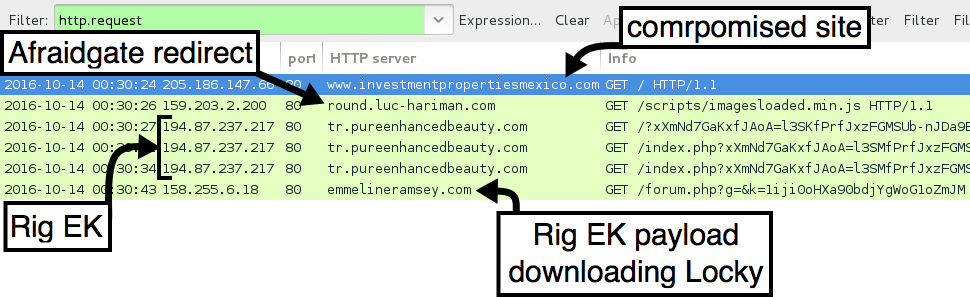
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- www.investmentpropertiesmexico[.]com - Compromised website
- 159.203.2[.]200 port 80 - round.luc-hariman[.]com - GET /scripts/imagesloaded.min.js - Afraidgate gate/redirect
- 194.87.237[.]217 port 80 - tr.pureenhancedbeauty[.]com - Rig EK
- 158.255.6[.]18 port 80 - emmelineramsey[.]com - GET /forum.php?g=&k=1iji0oHXa90bdjYgWoG1oZmJM - Rig EK payload (downloader retrieving Locky ransomware)
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- jhomitevd2abj3fk.tor2web[.]org
- jhomitevd2abj3fk[.]onion[.]to
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: b95fa5beddf64653bf88456ed521a0b7226d4fb4f5e8983b85ca5d03d8621be5
File name: 2016-10-14-Afraidgate-Rig-EK-flash-exploit.swf (50,368 bytes)
RIG EK PAYLOAD (DOWNLOADER FOR LOCKY RANSOMWARE):
- SHA256 hash: dd142090d4813db5243a151aca1fdf51c05e015691e4f3e2dd818adf6aba5b5b
File name: C:\Users\[username]\AppData\Local\Temp\rad22D03.tmp.exe (58,368 bytes)
FOLLOW-UP MALWARE (LOCKY RANSOMWARE):
- SHA256 hash: e3adeecd5dd55ab25fb738e3ba994135e35c00874c49075b3cff0d946ed80755
File name: C:\Users\[username]\AppData\Local\Temp\l8eEl9pAt7h3j9xYCU6kC25vQ.exe (190,976 bytes)
Click here to return to the main page.