2016-12-12 - "OSIRIS" VARIANT LOCKY RANSOMWARE FROM .JSE FILES
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-12-12-Locky-ransomware-email-tracker.csv.zip 3.7 kB (3,660 bytes)
- 2016-12-12-Locky-ransomware-infection-traffic.pcap.zip 284.7 kB (284,699 bytes)
- 2016-12-12-Locky-ransomware-emails-20-examples.zip 186.0 kB (185,979 bytes)
- 2016-12-12-email-attachments-for-Locky-ransomware-20-examples.zip 166.6 kB (166,608 bytes)
- 2016-12-12-extracted-jse-files-for-Locky-ransomware-20-examples.zip 131.4 kB (131,403 bytes)
- 2016-12-12-malware-from-a-Locky-ransomware-infection.zip 241.4 kB (241,351 bytes)
NOTES:
- The entry point for today's Locky ransomware DLL is sample get_str in case anyone wants to run it with rundll32.exe in a controlled environment.
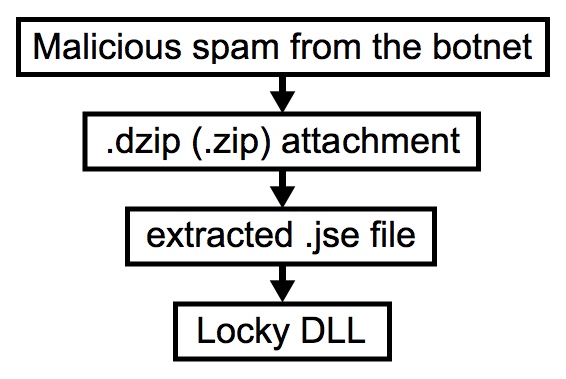
Shown above: Chain of events for an infection from this malspam.
EMAILS
SUBJECT LINES:
- Order Confirmation 001612 Hexstone Ltd
- Order Confirmation 028621 Hexstone Ltd
- Order Confirmation 03522791 Hexstone Ltd
- Order Confirmation 24138317 Hexstone Ltd
- Order Confirmation 297654 Hexstone Ltd
- Order Confirmation 329029761 Hexstone Ltd
- Order Confirmation 3842026 Hexstone Ltd
- Order Confirmation 3910005641 Hexstone Ltd
- Order Confirmation 435889 Hexstone Ltd
- Order Confirmation 4984764 Hexstone Ltd
- Order Confirmation 588883091 Hexstone Ltd
- Order Confirmation 625925256 Hexstone Ltd
- Order Confirmation 6923803141 Hexstone Ltd
- Order Confirmation 7186641643 Hexstone Ltd
- Order Confirmation 7308828900 Hexstone Ltd
- Order Confirmation 792066140 Hexstone Ltd
- Order Confirmation 892163 Hexstone Ltd
- Order Confirmation 9211029700 Hexstone Ltd
- Order Confirmation 943917502 Hexstone Ltd
- Order Confirmation 951095429 Hexstone Ltd
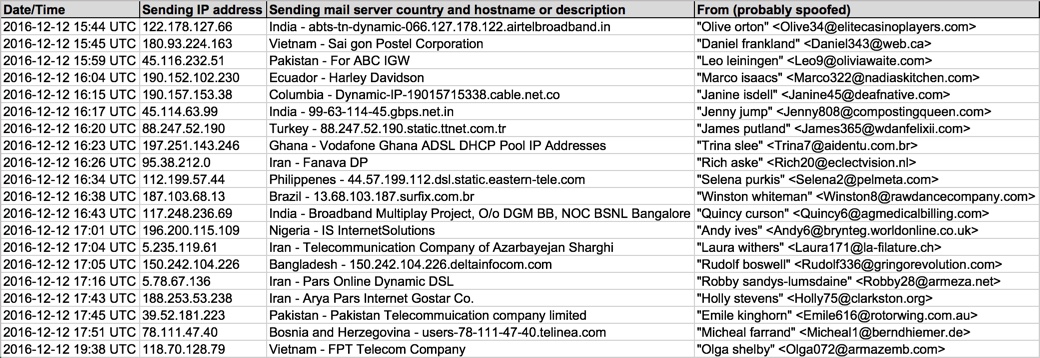
Shown above: Data from 20 emails pushing Locky ransomware (part 1 of 2).
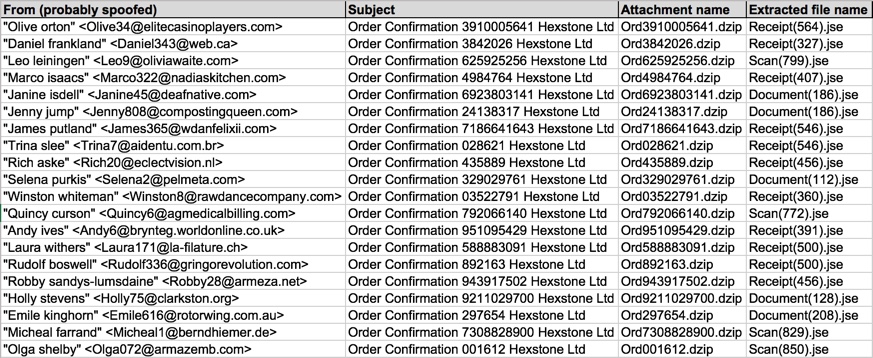
Shown above: Data from 20 emails pushing Locky ransomware (part 2 of 2).
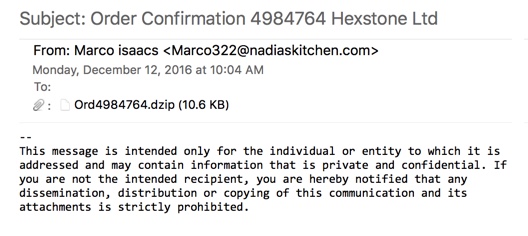
Shown above: An example from these emails.
TRAFFIC
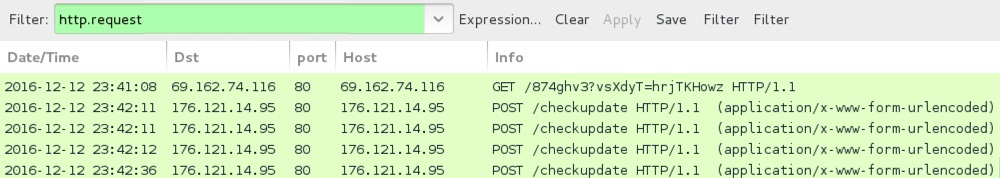
Shown above: An example of infection traffic by the Excel sheets from one of the emails.
EXAMPLES OF TRAFFIC GENERATED BY THE .JSE FILES RETRIEVING THE LOCKY RANSOMWARE BINARY:
- 23.229.166[.]185 - www.refereccu[.]com - GET /874ghv3?nMLywcbnOTX=qSItmcUxmhh
- 23.229.244[.]196 - autorijschoolpedro[.]nl - GET /874ghv3?hycFjlX=oGiPAd
- 27.254.55[.]25 - ratchadaphoto[.]com - GET /874ghv3?hnkOIEBk=tSKqWJ
- 27.254.96[.]195 - 3ainstrument[.]com - GET /874ghv3?JzaRmsLJ=jmdcFfxw
- 50.87.147[.]76 - cardbuilderplus[.]com - GET /874ghv3?sqfGdkvGc=kKVrJrzDTHa
- 64.34.68[.]80 - zasm[.]info - GET /874ghv3?nlyJYnQkWaY=uIqfjj
- 64.34.68[.]80 - zasm[.]info - GET /874ghv3?qVAILL=SgKgbROPT
- 66.147.240[.]172 - indiaclubdayton[.]org - GET /874ghv3?nlyJYnQkWaY=uIqfjj
- 66.96.149[.]19 - omnibusiness-solutions[.]com - GET /874ghv3?hycFjlX=oGiPAd
- 67.20.110[.]214 - sunwayautoparts[.]com - GET /874ghv3?bWRIatzeL=KrrBMXyVxD
- 69.162.74[.]116 - 69.162.74[.]116 - GET /874ghv3?vsXdyT=hrjTKHowz
- 69.89.31[.]111 - mer-pro[.]com - GET /874ghv3?nMLywcbnOTX=qSItmcUxmhh
- 70.33.246[.]100 - waterplusmaroc[.]com - GET /874ghv3?vsXdyT=hrjTKHowz
- 77.104.129[.]124 - ibfnetwork[.]com - GET /874ghv3?Iwvele=cffkCir
- 96.0.115[.]240 - olpharm[.]com - GET /874ghv3?yOtmOBXXQK=TqFJdur
- 103.27.52[.]92 - 103.27.52[.]92 - GET /874ghv3?feWkug=wOopBPy
- 103.27.52[.]92 - 103.27.52[.]92 - GET /874ghv3?qSzzdCEa=EIWRey
- 103.27.52[.]92 - 103.27.52[.]92 - GET /874ghv3?sqfGdkvGc=kKVrJrzDTHa
- 103.27.72[.]10 - www.pspmrsmag[.]com - GET /874ghv3?nMLywcbnOTX=qSItmcUxmhh
- 104.152.168[.]25 - muhammadmafazine[.]com - GET /874ghv3?feWkug=wOopBPy
- 104.152.168[.]25 - muhammadmafazine[.]com - GET /874ghv3?hnkOIEBk=tSKqWJ
- 104.152.168[.]25 - muhammadmafazine[.]com - GET /874ghv3?sqfGdkvGc=kKVrJrzDTHa
- 107.180.23[.]49 - icclicks[.]com - GET /874ghv3?vsXdyT=hrjTKHowz
- 107.180.4[.]37 - mynamepixs[.]com - GET /874ghv3?aXDVMP=wdpYzilI
- 107.180.4[.]37 - mynamepixs[.]com - GET /874ghv3?BEzJvyaiMCH=PlXEsFDdzY
- 107.180.4[.]37 - mynamepixs[.]com - GET /874ghv3?FbqqWm=vprrenIO
- 107.180.4[.]37 - mynamepixs[.]com - GET /874ghv3?nlyJYnQkWaY=uIqfjj
- 107.180.47[.]13 - megapowercash[.]com - GET /874ghv3?JzaRmsLJ=jmdcFfxw
- 108.168.206[.]100 - naacllc[.]com - GET /874ghv3?bWRIatzeL=KrrBMXyVxD
- 108.178.13[.]98 - www.kroyme[.]com - GET /874ghv3?aXDVMP=wdpYzilI
- 108.178.13[.]98 - www.kroyme[.]com - GET /874ghv3?BEzJvyaiMCH=PlXEsFDdzY
- 108.178.13[.]98 - www.kroyme[.]com - GET /874ghv3?FbqqWm=vprrenIO
- 108.178.13[.]98 - www.kroyme[.]com - GET /874ghv3?nlyJYnQkWaY=uIqfjj
- 108.178.13[.]98 - www.kroyme[.]com - GET /874ghv3?qVAILL=SgKgbROPT
- 111.67.22[.]192 - indigenouspromotions[.]com[.]au - GET /874ghv3?qSzzdCEa=EIWRey
- 117.239.70[.]228 - 117.239.70[.]228 - GET /874ghv3?qVAILL=SgKgbROPT
- 131.153.38[.]170 - www.russwat[.]org - GET /874ghv3?hnkOIEBk=tSKqWJ
- 150.107.31[.]57 - tifa-awards[.]net - GET /874ghv3?Iwvele=cffkCir
- 160.153.75[.]66 - tvctraffic[.]com - GET /874ghv3?hycFjlX=oGiPAd
- 160.153.75[.]66 - tvctraffic[.]com - GET /874ghv3?Iwvele=cffkCir
- 162.251.83[.]254 - w3care[.]com - GET /874ghv3?vsXdyT=hrjTKHowz
- 166.62.10[.]143 - onedotm[.]com - GET /874ghv3?yOtmOBXXQK=TqFJdur
- 166.62.10[.]29 - mebdco[.]com - GET /874ghv3?feWkug=wOopBPy
- 166.62.10[.]29 - mebdco[.]com - GET /874ghv3?hnkOIEBk=tSKqWJ
- 174.136.13[.]97 - thetravelbug[.]org - GET /874ghv3?qSzzdCEa=EIWRey
- 192.185.189[.]96 - soulanimtech[.]com - GET /874ghv3?yOtmOBXXQK=TqFJdur
- 192.185.225[.]231 - gudangg[.]com - GET /874ghv3?feWkug=wOopBPy
- 192.185.232[.]11 - filesdiamond[.]com - GET /874ghv3?JzaRmsLJ=jmdcFfxw
- 193.33.186[.]185 - mstest2[.]co[.]uk - GET /874ghv3?bWRIatzeL=KrrBMXyVxD
- 198.154.213[.]13 - therapymarketinginstitute[.]com - GET /874ghv3?JzaRmsLJ=jmdcFfxw
- 198.252.64[.]188 - envisorusa[.]com - GET /874ghv3?qVAILL=SgKgbROPT
- 198.54.120[.]18 - www.bfsa[.]gov[.]bd - GET /874ghv3?nMLywcbnOTX=qSItmcUxmhh
- 198.54.120[.]18 - www.ifs-b[.]org - GET /874ghv3?bWRIatzeL=KrrBMXyVxD
- 203.223.135[.]38 - www.pspmrsmtumpat[.]com - GET /874ghv3?qSzzdCEa=EIWRey
- 203.223.135[.]38 - www.pspmrsmtumpat[.]com - GET /874ghv3?sqfGdkvGc=kKVrJrzDTHa
- 206.72.192[.]15 - galtechprojects[.]com - GET /874ghv3?hycFjlX=oGiPAd
- 206.72.192[.]15 - galtechprojects[.]com - GET /874ghv3?yOtmOBXXQK=TqFJdur
- 208.113.172[.]228 - workandplaytherapy[.]com - GET /874ghv3?aXDVMP=wdpYzilI
- 208.113.172[.]228 - workandplaytherapy[.]com - GET /874ghv3?BEzJvyaiMCH=PlXEsFDdzY
- 208.113.172[.]228 - workandplaytherapy[.]com - GET /874ghv3?FbqqWm=vprrenIO
POST-INFECTION CALLBACK FROM THE LOCKY RANSOMWARE SAMPLE:
- 176.121.14[.]95 port 80 - 176.121.14[.]95 - POST /checkupdate
TOR DOMAIN FROM THE DECRYPTION INSTRUCTIONS:
- g46mbrrzpfszonuk[.]onion
FILE HASHES
LOCKY RANSOMWARE DLL FILE:
- SHA256 hash: 77be68d55cc051d234dd24b9305e832ebc49bc8160ddc415919946f39fc0b265 (225,280 bytes)
- File name: C:\Users\[username]\AppData\Local\Temp\[various names].dll
- DLL entry point: get_str
ZIP ATTACHMENTS FROM THE EMAILS (SHA256 HASH - FILE NAME):
- 0beadadb56e845af97faab552f7b0ea98105a6d9a421f257873ff72b5a790818 - Ord3910005641.dzip
- 0e8f3e2e54fe388f9ac1c24dc8ad75ececb12e2b60d804fa340d7b5ec0c79fdc - Ord001612.dzip
- 3cab212819b335bc7b77180af8a50ee9cccb9872ee23bd7bc7030f19e66d658a - Ord329029761.dzip
- 4da2e1e4b728858433d7e01cdac6e1bce9f9d6d1ad9e9e1cda242afe60c071c4 - Ord7308828900.dzip
- 57682af268ef423438ec1fb44875224fc492a3a32b98ae8821f47e6d5581d11d - Ord9211029700.dzip
- 587c52a0f3aa8fd0a76a85d61a1808abccfd02a25678876e91acba2f80255955 - Ord435889.dzip , Ord943917502.dzip
- 659c3845cd756a968858f1c0395ef1b95aefb55924b905ff22928e3d2852a047 - Ord625925256.dzip
- 65e2482927dd452282e4139cd7cc588886ec8009feace9ca00617b15287c9eab - Ord4984764.dzip
- 675fc86cdf53ccbdec9ba9823f70b4cc84a844e362a5e0a35f81bd5b0b6eef46 - Ord588883091.dzip , Ord892163.dzip
- 897c662976a773815b25e39141d55246ea8d9cd1501b92700f9823da4fff5613 - Ord297654.dzip
- 983999dee418fcc733fa0231b30d164744e0453e5b0ddc7b0819e61aaa18b553 - Ord792066140.dzip
- a7f60cdf194759b44b7a992a9485caf3d5b3d1a1b5bbd76a40d49b8dc7cc2ea3 - Ord951095429.dzip
- b7463bdf6affb2d85c71384545130ebaaf86f5ceaa32ac98148cc30aa3d93f6f - Ord24138317.dzip , Ord6923803141.dzip
- ba0f6b1e187613647bb973070f6aafba6dcf4d637533498938710a605cb09acf - Ord3842026.dzip
- d45f9362e02c8234662f56125c577863cbf5463465936c7b44a37bffca5bfd24 - Ord028621.dzip , Ord7186641643.dzip
- f212e63b85644550a0196c11904704ba9a21cad80afe2a4a9df09e3a806aed3c - Ord03522791.dzip
.JSE FILES EXTRACTED FROM THE ZIP ATTACHMENTS (SHA256 HASH - FILE NAME):
- 0a1b051fa7a5154cdc0cad64b54969822e84620940f81ba011b29298f2984149 - Scan(829).jse
- 16940b20d1aa1eea7d17233f9330819ae87919cabd2ec636a15cb9e62cb04521 - Receipt(456).jse
- 215619cf44ee770bf3bc57a16cdb9fe8f656b7bb40f572fd43d71b36a6bd5135 - Document(186).jse
- 2a86c0068a71ebb186ec70fea38d9127c3210e3c67cc93178796a0e877ea35a1 - Receipt(546).jse
- 355fd9ff898fe5c74fa9135375b196345680b732805eaefd5fffb57cdf3c0138 - Receipt(391).jse
- 500b3c02fdb3a7140a8e5a8ac6ce757d40239641ee0ad0a90bc374006d9920e3 - Scan(772).jse
- 702a7dca681c9e6a8018b74c48a04f1fc34ca0129298b8645f522cf9dfc54610 - Receipt(500).jse
- 76b5aaef307fb29be3e0c57b0805eaf0e07014b320de14a5d148229cc82201ad - Receipt(564).jse
- 822a35bccb502bfdf7b87a6a8f446a6e1852e803c9f23f33beed55b291ff4ad9 - Document(112).jse
- 922c1a649ed8791b477faf6e6136f76dbfcdf390aef55a0e7a06ddf8d7400849 - Document(128).jse
- 9901714ca289db876d180d435888b8e8f19c596ba3162181c3a53ff319098250 - Receipt(360).jse
- 9a52c869a25cc75aa592515a9cfc106d7918de92dd1749c9ab63aa2d2e275a8f - Document(208).jse
- b5413c921d7457b6870a84ef97b07fab6fbf1a3954dd6e69236aa632c1dfcfb7 - Scan(850).jse
- d54cbe5fce186d50d8af0351838d1a7d5238ccddf101a9a1b8cffa9533896ce9 - Receipt(327).jse
- d7244801a18f3d5b7f9869a557d44f8ddbd862df38e09489dcab0b6a6c560f74 - Scan(799).jse
- de20216783c60d5806ca74886e5a9f6bfb16d1305c1e9dbf946de947ddd77773 - Receipt(407).jse
IMAGES
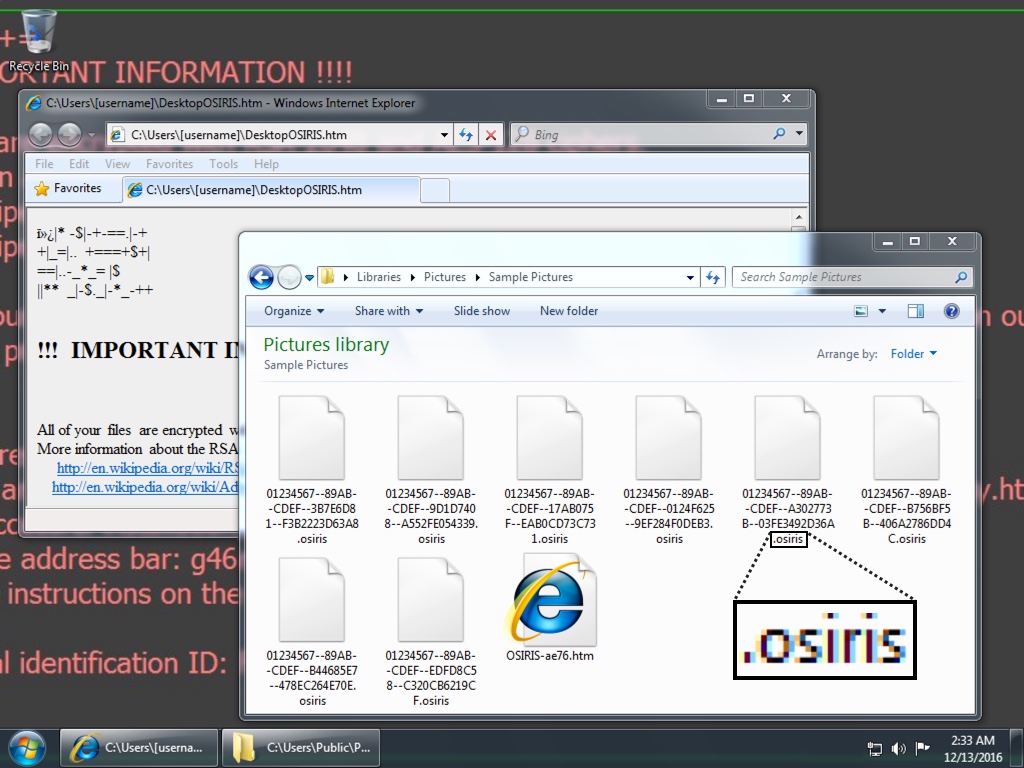
Shown above: Screen shot from an infected Windows desktop. Note the .osiris file extension.
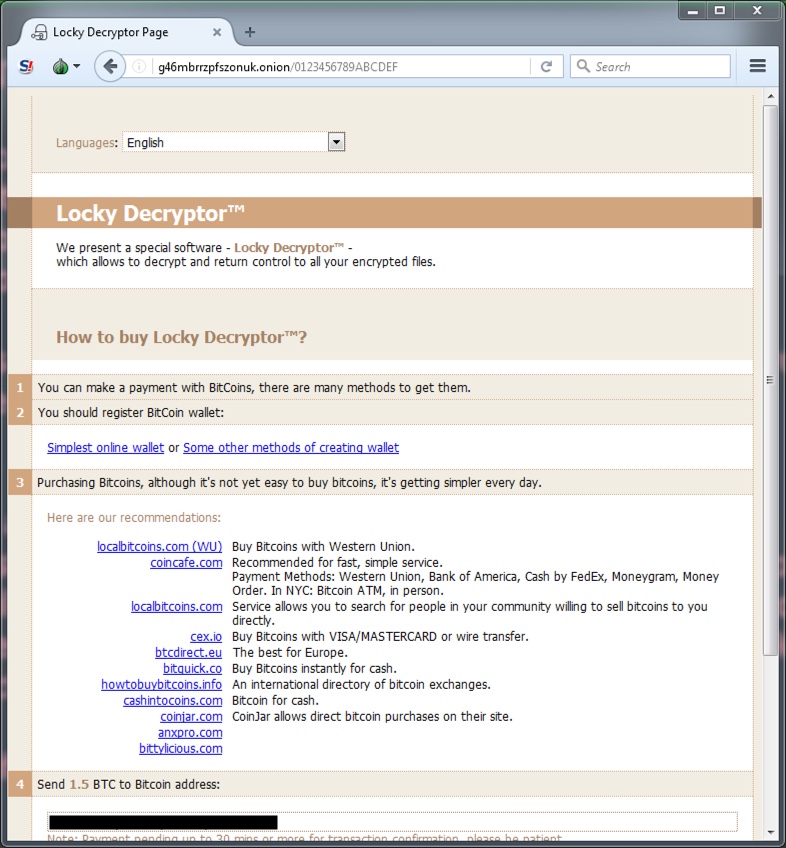
Shown above: Ransom payment was 1.5 bitcoin for the infections I generated.
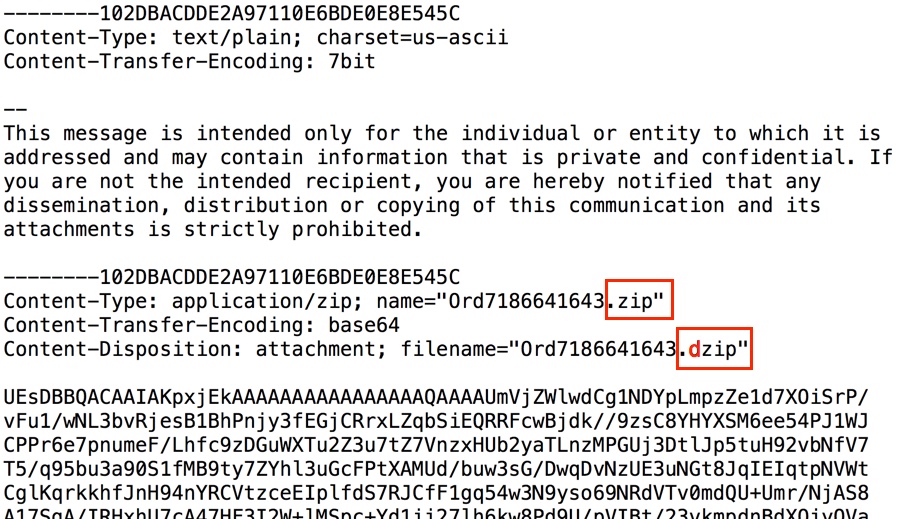
Shown above: There was an error in emails from this wave of emails, causing files extensions for .dzip attachments instead of .zip attachments.
Click here to return to the main page.