2017-05-15 - MY TAKE ON WANNACRY RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
==========
2017-05-23 UPDATE - I received some helpful information from @sec_panda:
SHA256 hash b9318a66fa7f50f2f3ecaca02a96268ad2c63db7554ea3acbde43bf517328d06, the binary with a killswitch, is a worm component.
SHA256 hash ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa is an encryptor sample. It has no worm or propagation behavior, and it doesn't check any for any killswitch domain. This sample will not work to simulate the propagation.
That explains why I wasn't able to generate any propagation traffic for this blog post.
==========
Here's an email from one of the Korean readers who follows this blog:
Sent: Monday, May 15, 2017 06:45 UTC
To: brad@malware-traffic-analysis[.]net
Subject: Please...
Can you do some research about the Wannacry ransomware? It's
targeting our country now, it's on the front news (Korea).
So here are my personal thoughts on the recent outbreak of WannaCry ransomware...
Whenever I hear about a ransomware outbreak, my very first thought is, "What was the initial vector for the first infection?"
Some sources state the infection vector is EternalBlue, an exploit leaked by the Shadow Brokers group last month in April 2017 based on CVE-2017-0144 for Microsoft's SMB protocol. So far, I've been under the impression that EternalBlue is how the ransomware propagates itself after an initial infection. Once a Windows host is infected, it uses EternalBlue to spread throughout that organization's network, assuming the organization's Windows servers are not properly patched or up-to-date.
So how did that organization's first Windows host get infected?
Other sources state the initial infection vector might be a phishing email or malicious spam (malspam). I doubt it's malspam, or someone would've posted an example by now. WannaCry certainly isn't in any of the malspam campaigns I've been tracking.
UPDATE: According to this Proofpoint article, a different attack using the EternalBlue exploit was launched from several virtual private servers which have been massively scanning the Internet on TCP port 445 for potential targets. So it looks like Windows servers vulnerable to EternalBlue are probably an initial infection vector after all.
FINDING SAMPLES
Even without knowing the initial infection vector, it's easy to find WannaCry samples through VirusTotal. I searched on the #wcry tag and found 44 comments on 43 files in the past 3 days or so. 41 of those files are executable binaries. Those results are from Monday afternoon in the US central timezone.
Shown above: Searching VirusTotal for #wcry.
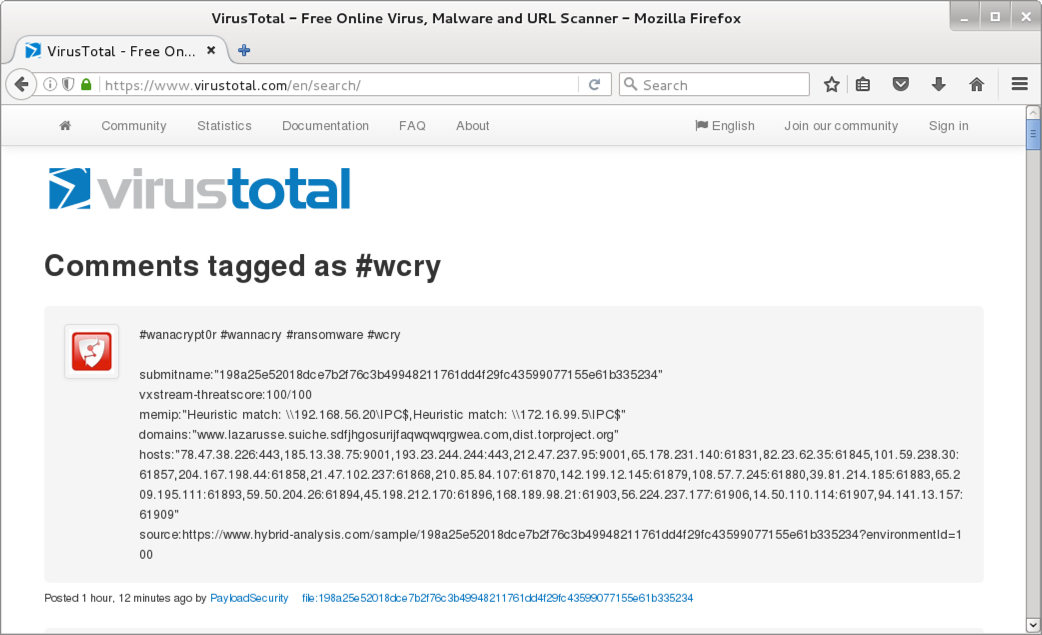
Shown above: #wcry search results in VirusTotal.
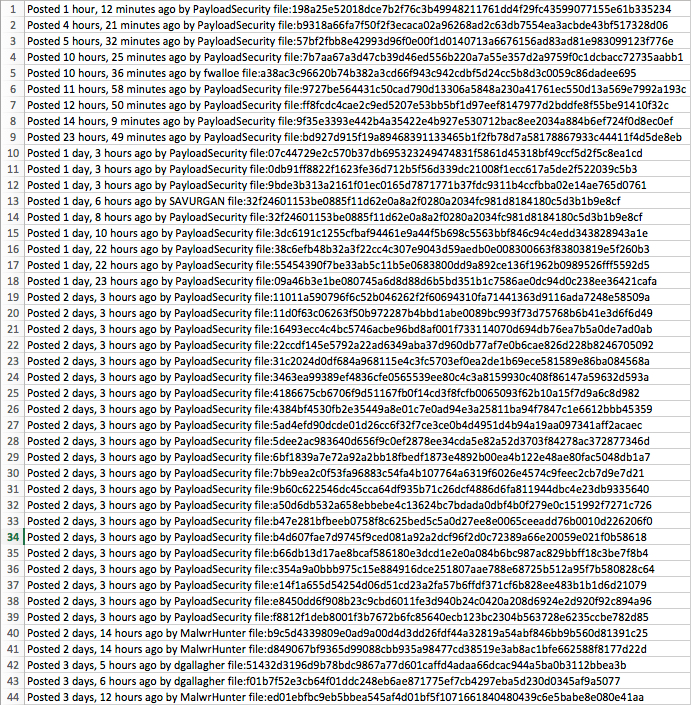
Shown above: 44 comments tagged #wcry when I checked.
Below are the SHA256 hashes for the WannaCry executables I found on Virus Total. Most (maybe all) have also been submitted to Hybrid Analysis. You can obtain these WannaCry samples from hybrid-analysis.com by registering for a free account.
- 07c44729e2c570b37db695323249474831f5861d45318bf49ccf5d2f5c8ea1cd
- 09a46b3e1be080745a6d8d88d6b5bd351b1c7586ae0dc94d0c238ee36421cafa
- 0db91ff8822f1623fe36d712b5f56d339dc21008f1ecc617a5de2f522039c5b3
- 11011a590796f6c52b046262f2f60694310fa71441363d9116ada7248e58509a
- 11d0f63c06263f50b972287b4bbd1abe0089bc993f73d75768b6b41e3d6f6d49
- 16493ecc4c4bc5746acbe96bd8af001f733114070d694db76ea7b5a0de7ad0ab
- 198a25e52018dce7b2f76c3b49948211761dd4f29fc43599077155e61b335234
- 22ccdf145e5792a22ad6349aba37d960db77af7e0b6cae826d228b8246705092
- 31c2024d0df684a968115e4c3fc5703ef0ea2de1b69ece581589e86ba084568a
- 32f24601153be0885f11d62e0a8a2f0280a2034fc981d8184180c5d3b1b9e8cf
- 3463ea99389ef4836cfe0565539ee80c4c3a8159930c408f86147a59632d593a
- 38c6efb48b32a3f22cc4c307e9043d59aedb0e008300663f83803819e5f260b3
- 3dc6191c1255cfbaf94461e9a44f5b698c5563bbf846c94c4edd343828943a1e
- 4186675cb6706f9d51167fb0f14cd3f8fcfb0065093f62b10a15f7d9a6c8d982
- 4384bf4530fb2e35449a8e01c7e0ad94e3a25811ba94f7847c1e6612bbb45359
- 55454390f7be33ab5c11b5e0683800dd9a892ce136f1962b0989526fff5592d5
- 57bf2fbb8e42993d96f0e00f1d0140713a6676156ad83ad81e983099123f776e
- 5ad4efd90dcde01d26cc6f32f7ce3ce0b4d4951d4b94a19aa097341aff2acaec
- 5dee2ac983640d656f9c0ef2878ee34cda5e82a52d3703f84278ac372877346d
- 6bf1839a7e72a92a2bb18fbedf1873e4892b00ea4b122e48ae80fac5048db1a7
- 7b7aa67a3d47cb39d46ed556b220a7a55e357d2a9759f0c1dcbacc72735aabb1
- 7bb9ea2c0f53fa96883c54fa4b107764a6319f6026e4574c9feec2cb7d9e7d21
- 9727be564431c50cad790d13306a5848a230a41761ec550d13a569e7992a193c
- 9b60c622546dc45cca64df935b71c26dcf4886d6fa811944dbc4e23db9335640
- 9bde3b313a2161f01ec0165d7871771b37fdc9311b4ccfbba02e14ae765d0761
- 9f35e3393e442b4a35422e4b927e530712bac8ee2034a884b6ef724f0d8ec0ef
- a38ac3c96620b74b382a3cd66f943c942cdbf5d24cc5b8d3c0059c86dadee695
- a50d6db532a658ebbebe4c13624bc7bdada0dbf4b0f279e0c151992f7271c726
- b47e281bfbeeb0758f8c625bed5c5a0d27ee8e0065ceeadd76b0010d226206f0
- b4d607fae7d9745f9ced081a92a2dcf96f2d0c72389a66e20059e021f0b58618
- b66db13d17ae8bcaf586180e3dcd1e2e0a084b6bc987ac829bbff18c3be7f8b4
- b9318a66fa7f50f2f3ecaca02a96268ad2c63db7554ea3acbde43bf517328d06
- b9c5d4339809e0ad9a00d4d3dd26fdf44a32819a54abf846bb9b560d81391c25
- bd927d915f19a89468391133465b1f2fb78d7a58178867933c44411f4d5de8eb
- c354a9a0bbb975c15e884916dce251807aae788e68725b512a95f7b580828c64
- d849067bf9365d99088cbb935a98477cd38519e3ab8ac1bfe662588f8177d22d
- e14f1a655d54254d06d51cd23a2fa57b6ffdf371cf6b828ee483b1b1d6d21079
- e8450dd6f908b23c9cbd6011fe3d940b24c0420a208d6924e2d920f92c894a96
- ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa
- f8812f1deb8001f3b7672b6fc85640ecb123bc2304b563728e6235ccbe782d85
- ff8fcdc4cae2c9ed5207e53bb5bf1d97eef8147977d2bddfe8f55be91410f32c
TRAFFIC
I tried one of the samples from Monday May 15th, 2017: SHA256 hash: b9318a66fa7f50f2f3ecaca02a96268ad2c63db7554ea3acbde43bf517328d06. Unfortunately (for me), it didn't work because the "kill switch" domain was active. A good write-up on those kill switch domains is here. To summarize that article, if the kill switch domain for a particular WannaCry sample is active, and the infected Windows host can contact the domain, that WannaCry sample shuts down before it encrypts any files.
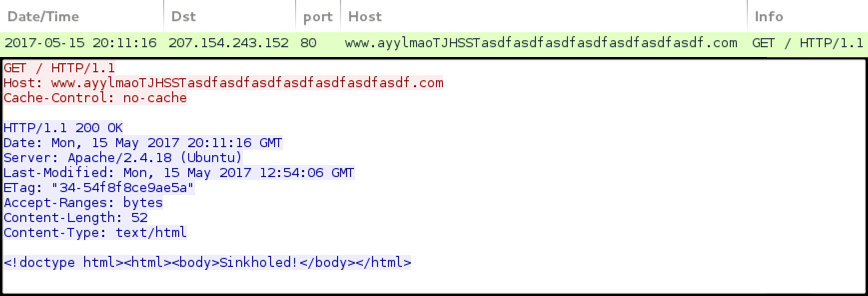
Shown above: The only activity I saw from the above sample.
After my first unsuccessful attempt, I tried a different sample from Friday May 12th, SHA256 hash: ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa. That particular WannaCry sample did not call out to a kill switch domain, and it did infect a host in my home lab.

Shown above: Desktop of an infected host running an unpatched installation of Windows 7 Home Edition.
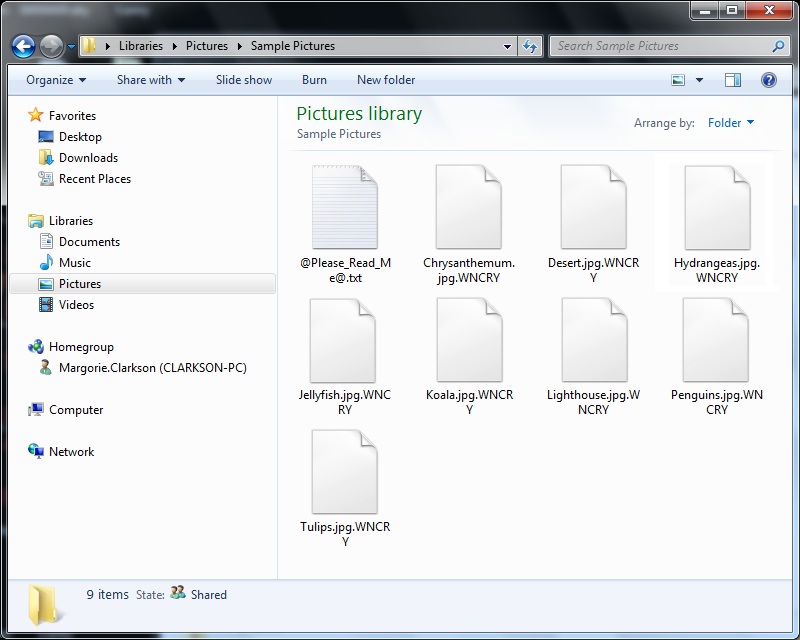
Shown above: Encrypted files on an infected Windows host.
MY FAILED ATTEMPT AT SOMETHING INTERESTING
The media has hyped the worm-style SMB propagation of WannaCry ransomware. Several posts on Twitter have even used the hashtag #ransomworm to describe WannaCry. I tried to replicate WannaCry's propagation in my home lab. Unfortunately, my attempt did not work.
I've never been a Windows administrator, so I only set up two Windows 7 clients in my home lab, and I used the quickest method to share files between them. These physical hosts were connected through a physical switch, so they were effectively an isolated LAN consisting of two Windows computers with a gateway to the Internet. [2025 note: This was before I was able to test malware with an Active Directory environment with a domain controller]
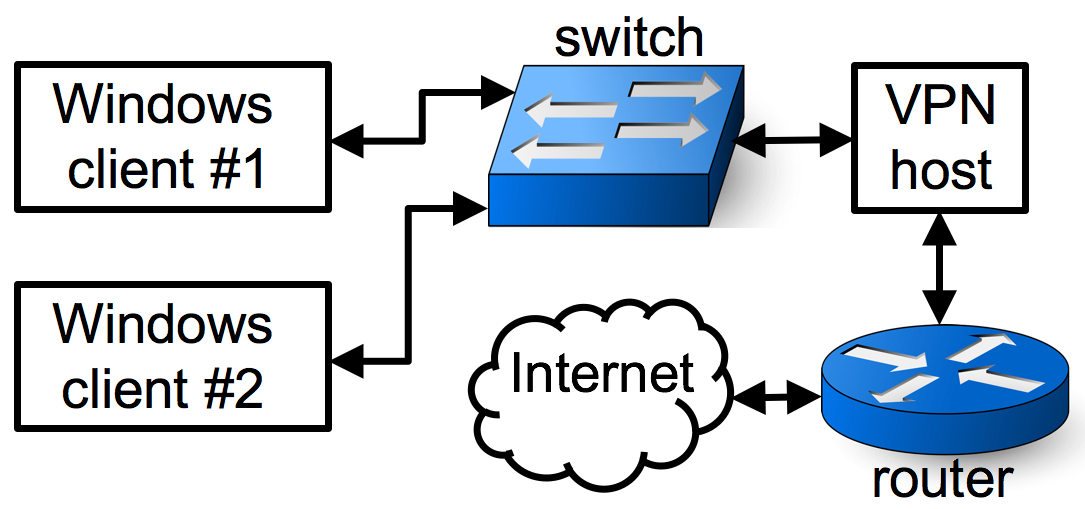
Shown above: My physical setup used to investigate those two WannaCry samples.
One PC was host name Simspon-PC with an admin account named Gregory.Simpson. The other was was host name Clarkson-PC with an admin account named Margorie.Clarkson.
I used homegroup to share files between the two Windows computers. There wasn't a server in this environment, and there was no SMB traffic. I only saw Tor traffic along with the associated tor files dropped somewhere under the same Desktop directory I executed the WannaCry in.
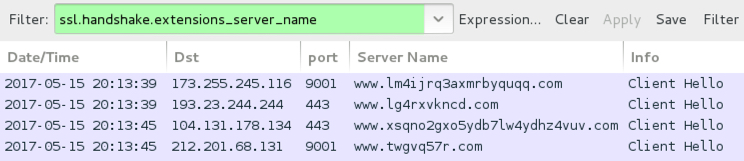
Shown above: Tor traffic noted from the infected Windows host.
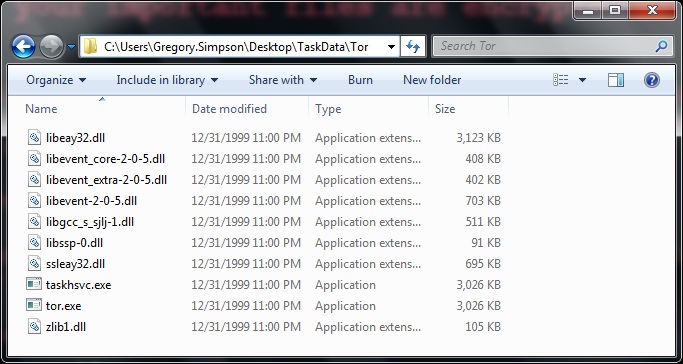
Shown above: Associated Tor files on the infected Windows host.
So yes, I infected Simspon-PC with WannaCry. And files on Clarkson-PC were easily accessible from the infected Simspon-PC. However, nothing happened to Clarkson-PC. It was never infected.
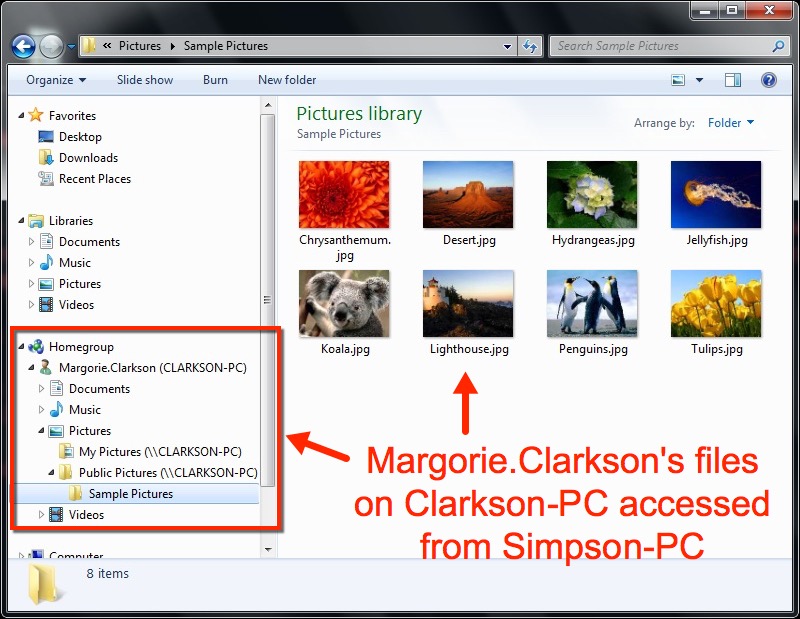
Shown above: Unencrypted files on Clarkson-PC easily accessed from the infected Simspon-PC.
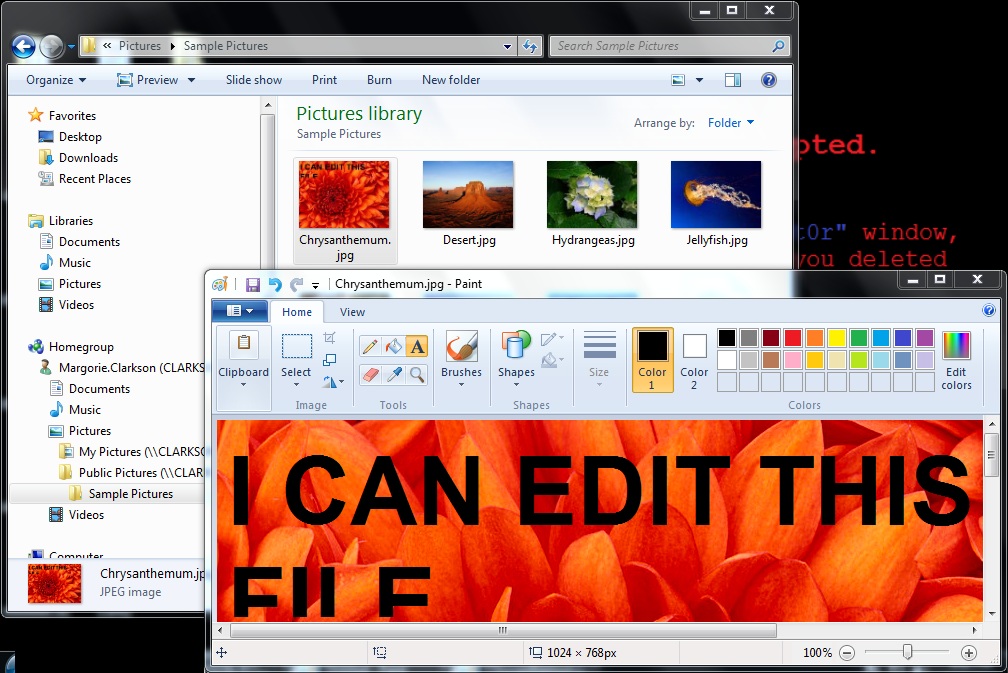
Shown above: Even though I could alter the files on Clarkson-PC from the infected Simspon-PC, they were not encrypted by WannaCry.
So WannaCry's method of propagation doesn't work through homegroup sharing. That's good news, I guess, for home users that don't connect to any Windows servers through SMB. WannaCry seems like a business-oriented ransomware anyway.
Click here to return to the main page.
