2017-09-19 - TRAFFIC ANALYSIS EXERCISE - MISSION POSSIBLE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive of the pcap: 2017-09-19-traffic-analysis-exercise.pcap.zip 4.7 MB (4,711,481 bytes)
- Zip archive of the email and malware: 2017-09-19-traffic-analysis-exercise-email-and-malware.zip 294.2 kB (294,197 bytes)
INTRODUCTION
You're an analyst at a Security Operations Center (SOC). As you show up for work one morning, your manager approaches. He's wearing a trenchcoat with the collar turned up, and you can barely see his face under the fedora he's wearing.
Shown above: Your manager is acting a bit weird.
"Greg," you say. "Is that you?"
"Check your email," he replies. "You have a mission, should you choose to accept it."
You scractch your head. "It's warm outside. Why are you wearing a trenchcoat?"
Greg slowly walks to a shadowy corner of the SOC. "You never saw me," he whispers. "I was never here..."
"Of course you're here," you reply. "We're both scheduled to work today."
Minutes later, Greg hasn't moved since going to that dark corner. You inform him he is clearly visible.
YOUR MISSION
Your email includes a message from an unknown sender. The message contains a pcap of network traffic and instructions to write an incident report. This isn't the first time Greg has sent you a traffic analysis exercise, but he's never acted so weird about it.
You look over at Greg's desk where he's now sitting. He's no longer wearing the trenchcoat, and he looks normal.
"Uh, Greg," you say. "Did you send me this traffic analysis exercise?"
He glances over at you and looks very nervous. "I don't know what you're talking about."
"This email," you reply. "The one about my mission, should I choose to accept it?"
Greg gets up and quickly walks over to your desk. "That's top secret," he angrily whispers. "Just go see Lenny in the forensics lab. He's got more information for you."
You shake your head and wonder if Greg has stopped taking his meds. Nevertheless, you walk over to the forensics lab.
ADDITIONAL INFORMATION
You go to the forensics lab and find Larry working at his computer. However, he's suspended in the air. And he looks a lot more like Tom Cruise than usual.

Shown above: Larry in the forensics lab.
"Hey Larry," you say as you walk in. "Greg says you have something for me?"
He looks over and replies, "Ah yes. Your mission."
Larry hands you a USB stick and says, "The traffic you received is from an infected Windows host. I did some foresnics on the computer, and I found a malicious email sent to the victim." He taps the USB stick. "This contains the email and some malware I found on the infected host."
He taps at his computer screen and shows you where the malware was located. "Look," he says while pointing at the information. "Here's the malware and associated registry update to keep it persistent."
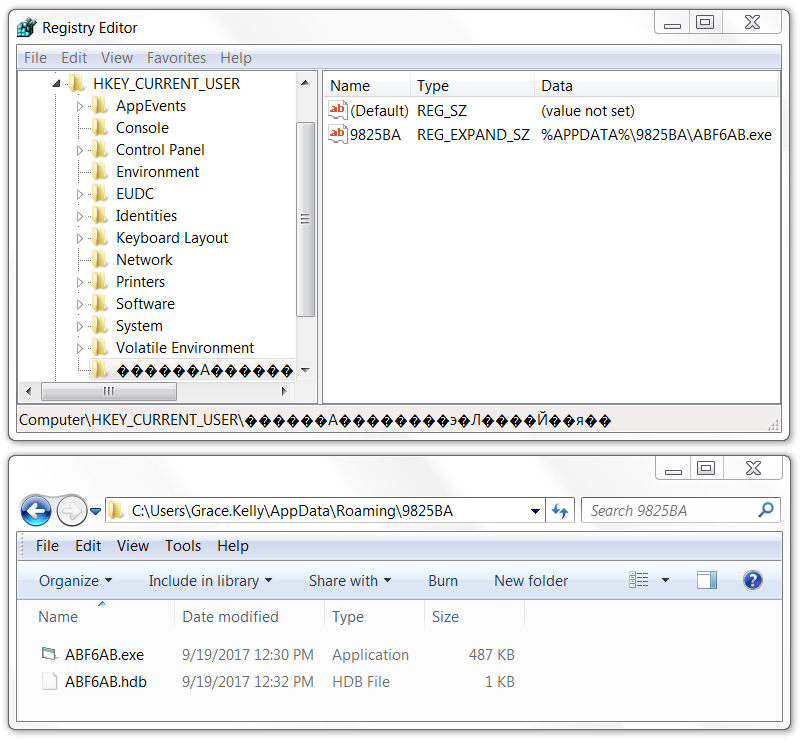
Shown above: The information Larry shows you.
You look at Larry and ask, "Is it comfortable? Being suspended in the air like that?"
"Not really," he replies. "But I have a crippling fear of cockroaches and mice. I saw one the other day, and now I refuse to stand on the floor or sit in this building."
"Okay," you say and slowly back out of the room. Larry is now on your list of possible escapees from the local insane asylum. Maybe it's time to switch jobs.
WHAT SHOULD YOUR INCIDENT REPORT LOOK LIKE?
Your report should contain:
- Date and time of the activity (in GMT or UTC)
- The account name or username from the infected Windows computer
- The host name of the infected Windows computer
- The MAC address of the infected Windows computer
- SHA256 file hashes from the associated files
- A summary of what happened
ANSWERS
- Click here for the answers.
Click here to return to the main page.
