2018-07-18 - QUICK POST: TRICKBOT INFECTION WITH TOR TRAFFIC AND NEW MODULE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2018-07-18-Trickbot-malspam-1409-UTC.eml.zip 38 kB (38,214 bytes)
- 2018-07-18-Trickbot-infection-in-AD-environment.pcap.zip 15.3 MB (15,310,423 bytes)
- 2018-07-18-malware-and-artifacts-from-Trickbot-infection.zip 679 kB (679,351 bytes)
NOTES:
- Thanks to @benkow_, @VK_Intel, @K_N1kolenko, @peterkruse, @MalwareTechBlog and others for their tweets today that clarified things for me.
- This traffic is also another example of Trickbot moving from an infected client (172.16.1.205) to an AD domain controller (172.16.1.8).
- Timeline for recent changes:
- 2018-07-11 - @VK_Intel reported an .onion domain in config data from a Trickbot sample (link to tweet).
- Others on Twitter notice these .onion domains in Trickbot configs.
- 2018-07-16 - @VK_Intel posts "Let's Learn: Decoding Latest "TrickBot" Loader String Template & New Tor Plugin Server Communication" (link).
- 2018-07-18 - I've generated Trickbot infections this past week, but today is the first time I've noticed Tor traffic during the infection.
- 2018-07-18 - Today is also the first time I've noticed the NewBCtestDll64 module in my Trickbot-infected Windows hosts.
IMAGES
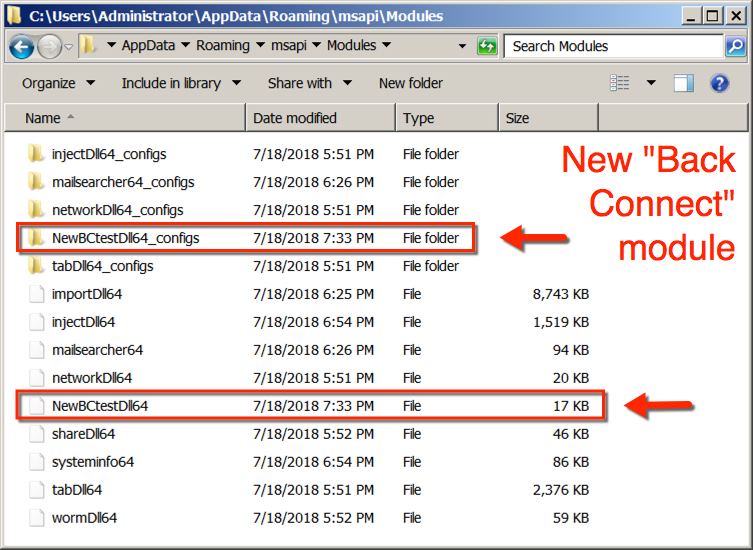
Shown above: I saw a new "BackConnect" module in Trickbot today.
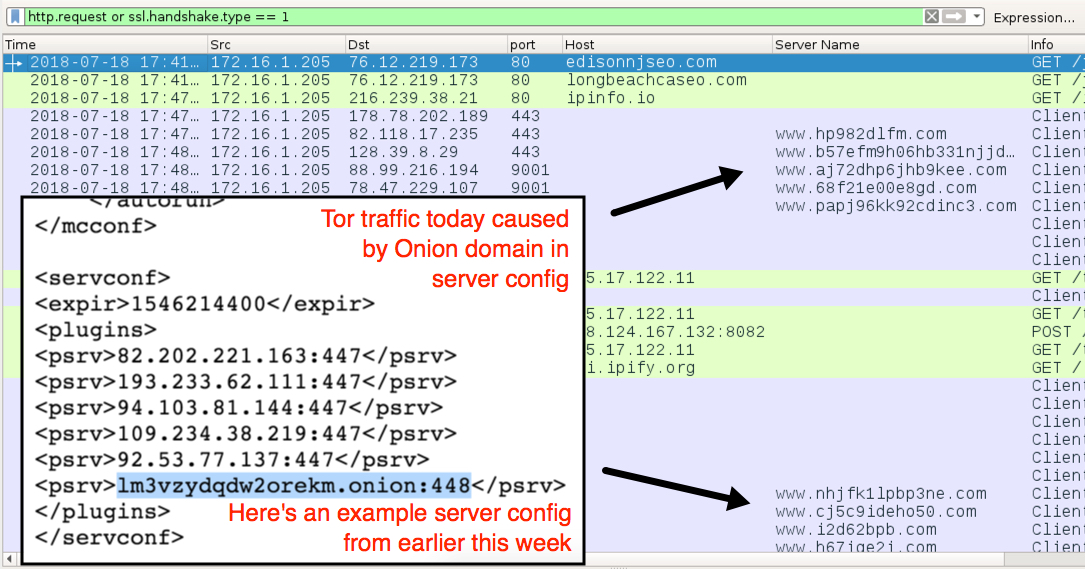
Shown above: I also saw some Tor traffic in today's infection.
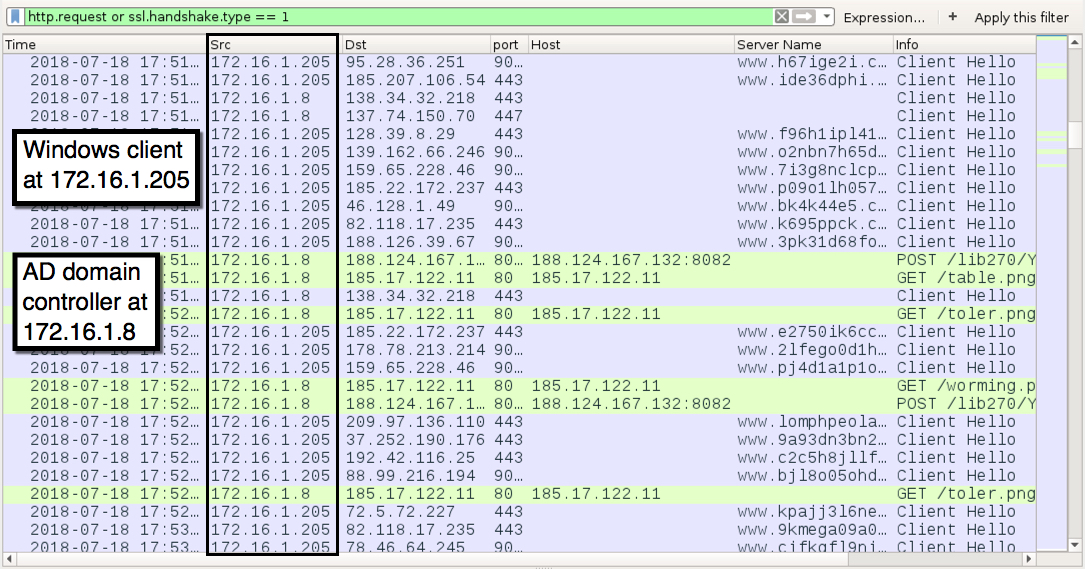
Shown above: Trickbot also infected the domain controller in this AD environment.
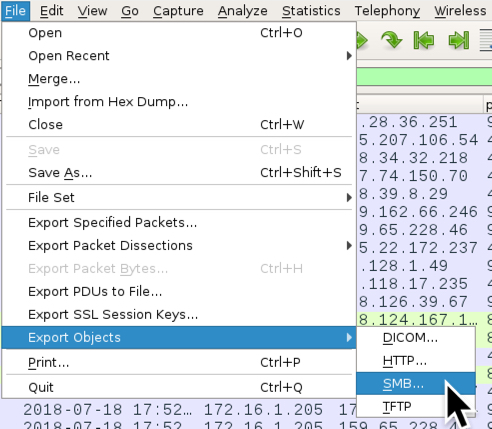
Shown above: Export SMB objects from this pcap...
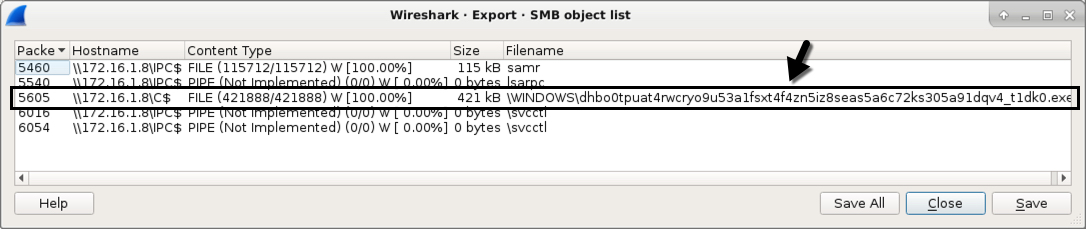
Shown above: And you'll find a Trickbot binary sent over SMB.
Click here to return to the main page.
