2018-08-07 - HOOKADS RIG EK PUSHES AZORULT, AZORULT PUSHES SMOKELOADER
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive of the infection traffic: 2018-08-07-Rig-EK-traffic-both-pcaps.zip 6.9 MB (6,904,359 bytes)
- 2018-08-07-Rig-EK-infection-traffic-1st-run.pcap (5,193,718 bytes)
- 2018-08-07-Rig-EK-infection-traffic-2nd-run.pcap (6,102,865 bytes)
- 2018-08-07-Rig-EK-landing-page-1st-run.txt (140,787 bytes)
- 2018-08-07-Rig-EK-landing-page-2nd-run.txt (140,863 bytes)
- 2018-08-07-Rig-EK-artifact-sp.txt (1,151 bytes)
- 2018-08-07-Rig-EK-flash-exploit.swf (34,325 bytes)
- 2018-08-07-Rig-EK-payload-1st-run-AZORult.exe (134,656 bytes)
- 2018-08-07-Rig-EK-payload-2nd-run-AZORult.exe (285,968 bytes)
- 2018-08-07-Rig-EK-AZORult-infection-follow-up-malware-1-of-2-possibly-SmokeLoader.exe (54,784 bytes)
- 2018-08-07-Rig-EK-AZORult-infection-follow-up-malware-2-of-2-possibly-SmokeLoader.exe (204,560 bytes)
NOTES:
- This appears to be the Hookads campaign.
- It's very similar to what I saw last year in 2017 with an HTTP request for popunder.php from a decoy domain (example from last year).
- Last year, the Hookads campaign used mostly decoy porn-themed domains. This time, it was a decoy dating domain.
WEB TRAFFIC BLOCK LIST
Indicators are not a block list. If you feel the need to block web traffic, I suggest the following domains and URL:
- freedatingvideo[.]info
- actsconduit[.]icu
- ascribesanniversaries[.]bid
- hxxp[:]//85.143.171[.]2/fazu.exe
TRAFFIC
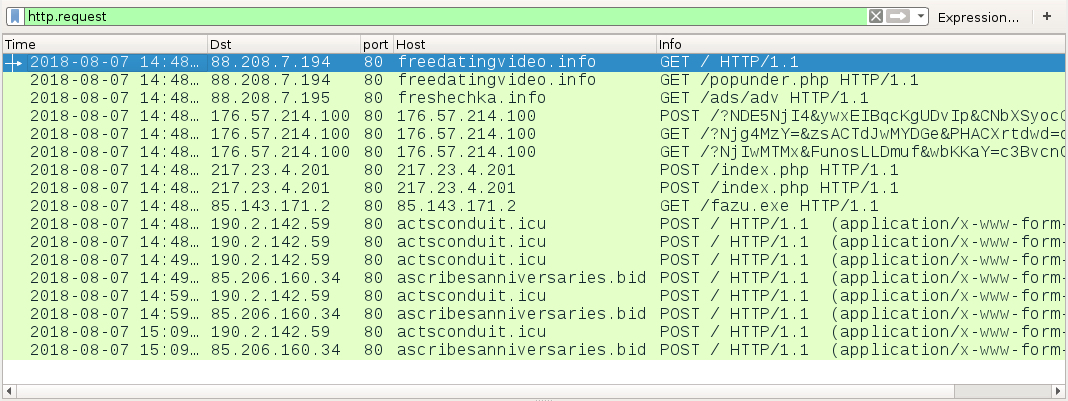
Shown above: Infection traffic from the 2nd run filtered in Wireshark.
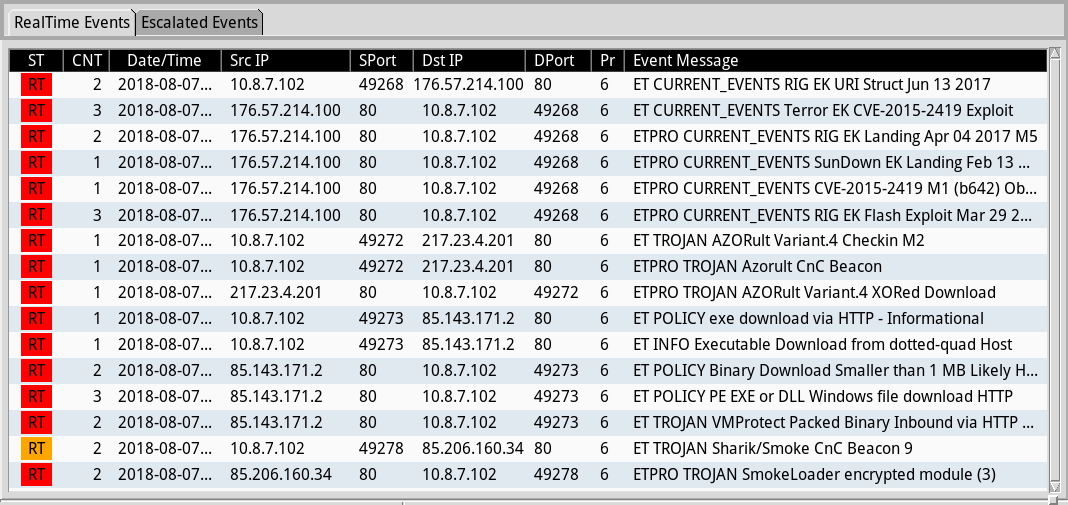
Shown above: Alerts from Sguil in Security Onion using Suricata and the EmergingThreats Pro (ETPRO) ruleset.
TRAFFIC TO DECOY DATING DOMAIN AND REDIRECT LEADING TO RIG EK:
- 88.208.7[.]194 port 80 - freedatingvideo[.]info - GET /
- 88.208.7[.]194 port 80 - freedatingvideo[.]info - GET /popunder.php
- 88.208.7[.]195 port 80 - freshechka[.]info - GET /ads/adv
RIG EK:
- 176.57.214[.]100 port 80 - 176.57.214[.]100 - Rig EK
POST-INFECTION TRAFFIC:
- 92.63.197[.]99 port 80 - 92.63.197[.]99 - POST /index.php - AZORult callback, 1st run
- 217.23.4[.]201 port 80 - 217.23.4[.]201 - POST /index.php - AZORult callback, 2nd run
- 85.143.171[.]2 port 80 - 85.143.171[.]2 - GET /fazu.exe - Additional malware, 2nd run, possible SmokeLoader
- 190.2.142[.]59 port 80 - actsconduit[.]icu - POST / - SmokeLoader callback, 2nd run
- 85.206.160[.]34 port 80 - ascribesanniversaries[.]bid - POST / - SmokeLoader callback, 2nd run
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: 3ee3fbb5555fb250061101b55e31c8859fcd10c873f9275e087f938057efaf43
File size: 34,325 bytes
File description: Rig EK flash exploit seen on 2018-08-07
RIG EK PAYLOADS:
- SHA256 hash: ef30a9611553f396b7d391760523fca54f0618f03d442278e034dc149f39e227
File size: 134,656 bytes
File description: Rig EK payload seen on 2018-08-07 (1st run) AZORult
- SHA256 hash: 688cfd1a6c5fa652bbeef8ea27f0daaa8e4213b6976022367599ded243403607
File size: 285,968 bytes
File description: Rig EK payload seen on 2018-08-07 (2nd run) AZORult
FOLLOW-UP MALWARE SEEN DURING THE SECOND RUN:
- SHA256 hash: f1523c4a8c9bd6b2344763f4b3df912830991dd4dc3d4220534f14574bbc34a2
File size: 54,784 bytes
File location: C:\Users\[username]\AppData\Roaming\Microsoft\Windows\taduuavf\wgggdsuu.exe
File note: Kept persisent through shortcut in Startup folder in Windows Start Menu
File description: Possible Smokeloader malware seen after AZORult infection in 2nd run
- SHA256 hash: 6e0d982f83f01cda505b54ea476531b7d391051be8cb6a7185205f74e7ac4222
File size: 204,560 bytes
File location: C:\Users\[username]\AppData\Roaming\Microsoft\Windows\cbbbacsw\wgggdsuu.exe
File note: Kept persisent through shortcut in Startup folder in Windows Start Menu
File description: Possible Smokeloader malware seen after AZORult infection in 2nd run
Click here to return to the main page.
