2018-09-21 - MALSPAM WITH PASSWORD-PROTECTED WORD DOCS STILL PUSHING NYMAIM
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2018-09-21-malspam-with-password-protected-Word-doc-4-email-examples.zip 130 kB (129,760 bytes)
- 2018-09-21-Nymaim-infection-traffic.pcap.zip 6.2 MB (6,240,157 bytes)
- 2018-09-21-malware-and-artifacts-Nymaim-activity.zip 6.2 MB (6,166,386 bytes)
NOTES:
- I've blogged about this malspam several times before. Feel free to review these previous posts to see how this campaign has evolved.
- 2018-09-19 - Part of Data dump (Hancitor, Nymaim, Trickbot)
- 2018-09-17 - Quick post: Malspam with password-protected Word doc pushes Nymaim
- 2018-09-06 - malspam with password-protected Word doc pushes AZORult then Neutrino
- 2018-08-21 - more malspam with password-protected Word docs, now pushing Neutrino malware
- 2018-08-15 - More malspam pushing password-protected Word docs for AZORult and Hermes Ransomware
- 2018-07-27 - Malspam with password-protected Word docs pushes Hermes ransomware
- 2018-07-23 - Malspam using password-protected Word docs continues to push ransomware
- 2018-06-04 - More malspam pushing password-protected Word docs
- 2018-05-09 - Malspam using password-protected Word docs still active
- 2018-04-20 - Malspam pushing ransomware using two layers of password protection to avoid detection
- 2018-03-14 - Malspam pushing Sigma ransomware
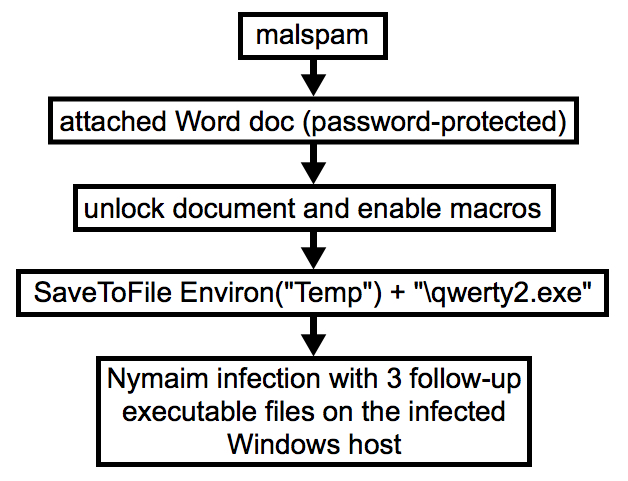
Shown above: My attempt at a flow chart for today's infection.
WEB TRAFFIC BLOCK LIST
Indicators are not a block list. If you feel the need to block web traffic, I suggest the following URLs and domain:
- hxxp[:]//209.141.59[.]124/521.exe
- hxxp[:]//209.141.60[.]230/521.exe
- fesishineds[.]com
EMAILS
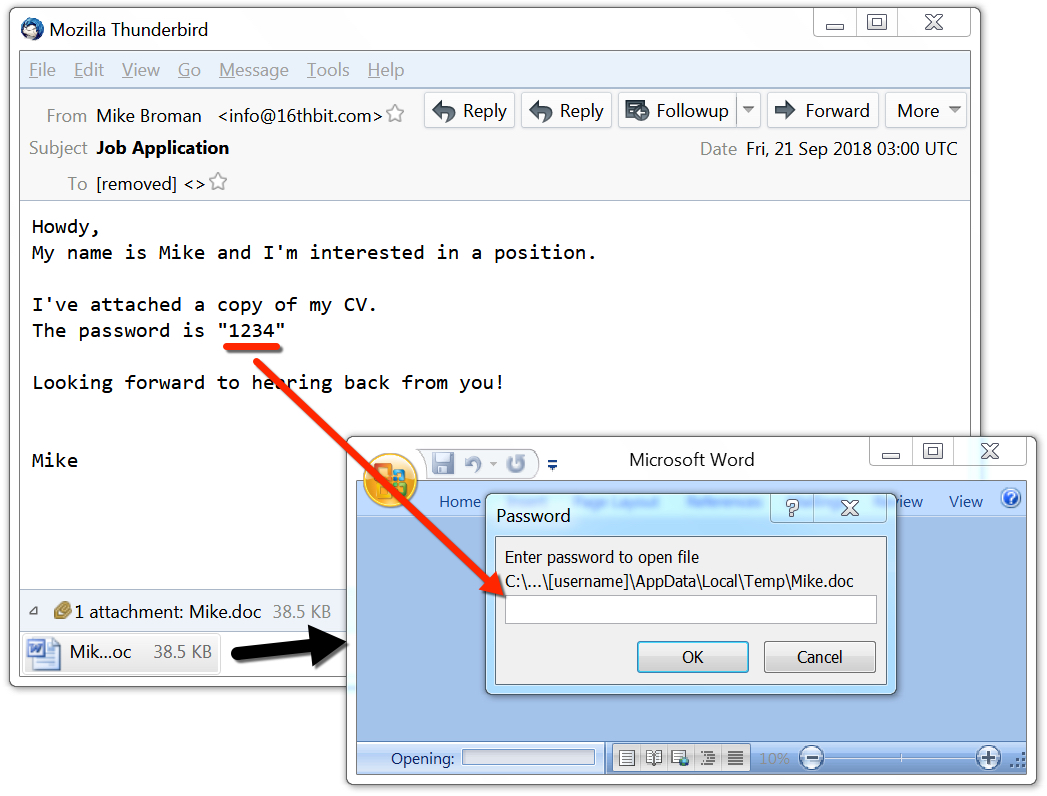
Shown above: Screenshot from an email for today's infection.
- Date: Thu, 20 Sep 2018 at 08:26 UTC
- Received: from 0937[.]org (0937[.]org [46.161.42[.]3])
- From: Clementina Liebig =?UTF-8?B?wqA=?= <info@0937[.]org>
- Subject: Invoice Attached - FINAL NOTICE
- Attachment name: invoice.doc
- Attachment password: 1234
- Date: Thu, 20 Sep 2018 at 18:03 UTC
- Received: from simplexhealthcare[.]info (simplexhealthcare[.]info [46.161.42[.]2])
- From: Dennis Cadet =?UTF-8?B?wqA=?= <sale@simplexhealthcare[.]info>
- Subject: Job Application
- Attachment name: Dennis.doc
- Attachment password: 1234
- Date: Thu, 20 Sep 2018 at 18:24 UTC
- Received: from managedprintservices-online[.]com (managedprintservices-online[.]com [46.161.42[.]5])
- From: Hien Thome =?UTF-8?B?wqA=?= <noreply@managedprintservices-online[.]com>
- Subject: Job Application
- Attachment name: Hien.doc
- Attachment password: 1234
- Date: Fri, 21 Sep 2018 at 03:00 UTC
- Received: from 16thbit[.]com (16thbit[.]com [46.161.42[.]22])
- From: Mike Broman =?UTF-8?B?wqA=?= <info@16thbit[.]com>
- Subject: Job Application
- Attachment name: Mike.doc
- Attachment password: 1234
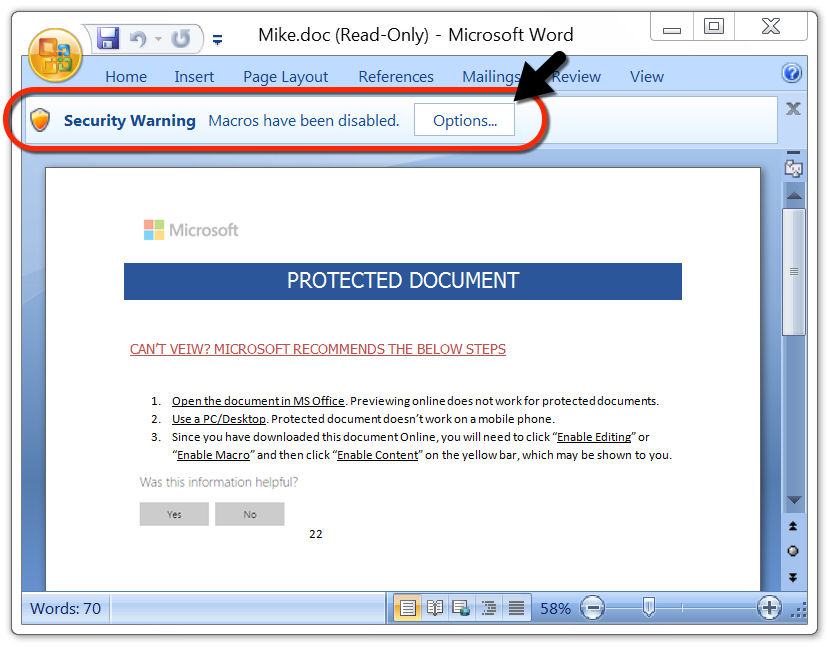
Shown above: The attached Word document after it's unlocked with the password.
TRAFFIC
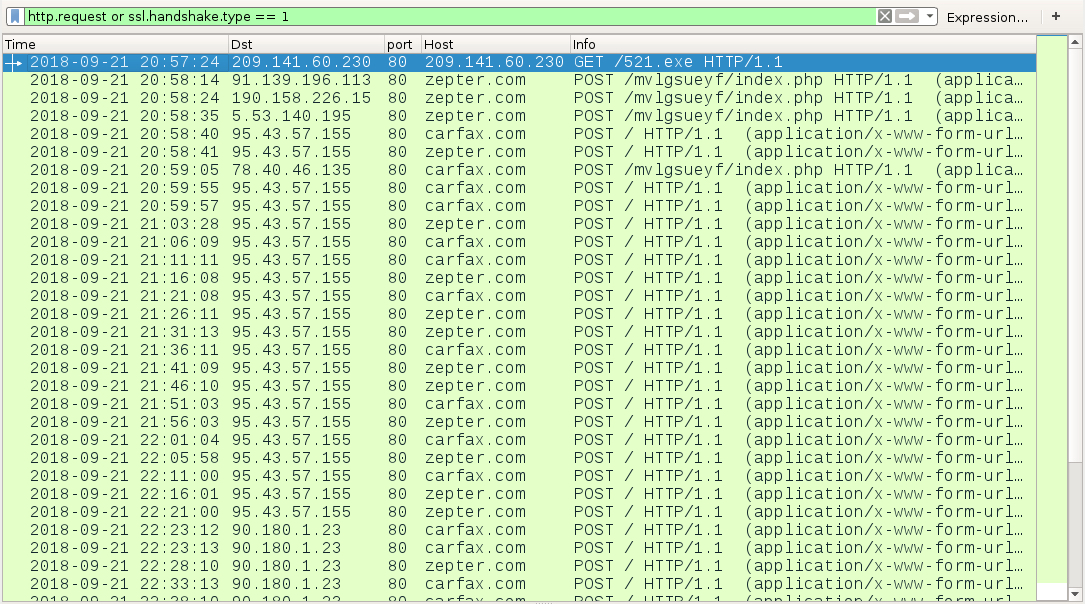
Shown above: Traffic from the infection filtered in Wireshark.
TRAFFIC FROM AN INFECTED WINDOWS HOST:
- 209.141.60[.]230 port 80 - 209.141.60[.]230 - GET /521.exe
- 91.139.196[.]113 port 80 - zepter[.]com - POST /mvlgsueyf/index.php
- 190.158.226[.]15 port 80 - zepter[.]com - POST /mvlgsueyf/index.php
- 5.53.140[.]195 port 80 - zepter[.]com - POST /mvlgsueyf/index.php
- 95.43.57[.]155 port 80 - carfax[.]com - POST /
- 95.43.57[.]155 port 80 - zepter[.]com - POST /
- 78.40.46[.]135 port 80 - carfax[.]com - POST /mvlgsueyf/index.php
- 90.180.1[.]23 port 80 - carfax[.]com - POST /
- 90.180.1[.]23 port 80 - zepter[.]com - POST /
- DNS queries for fesishineds[.]com using Google DNS (8.8.8[.]8 or 8.8.4[.]4)
- DNS queries for microsoft[.]com using Google DNS (8.8.8[.]8 or 8.8.4[.]4)
- DNS query for google[.]com using Google DNS (8.8.8[.]8 or 8.8.4[.]4)
NOTE:
- IP addresses used in the post-infection HTTP traffic are not actually used by legitimate domains zepter.com and carfax.com.
- At first, I thought the IP addresses came from DNS queries to fesishineds[.]com, but they don't match up.
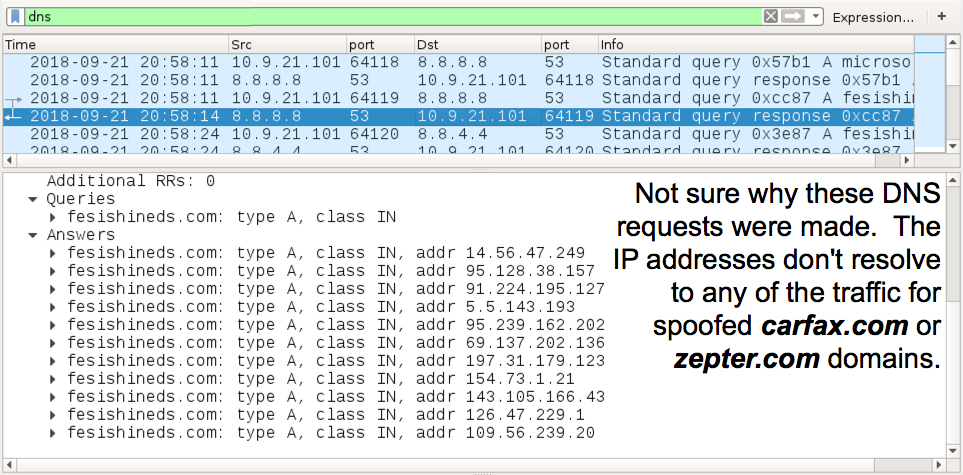
Shown above: DNS traffic to Google DNS from the infected Windows host.
MALWARE
EXECUTABLES FOUND ON THE INFECTED WINDOWS HOST:
- C:\Users\[username]\AppData\Local\Temp\qwerty2.exe
- C:\ProgramData\ddram-3\ddram-0.exe
- C:\ProgramData\vmebus-0\vmebus-4.exe
- C:\Users\[username]\AppData\Roaming\valence-42\valence-59.exe
NOTE:
- Random file names/paths are used for the follow-up Nymaim executables after qwerty2.exe is retrieved by the Word macro.
- File paths I've seen for the follow-up malware fall somewhere under the ProgramData directory or the user's AppData directory.
- Follow-up executables for Nymaim all have command line arguments as shown in the persistence mechanisms section. So far, I've seen these as either 1- or 2-characters.
PERSISTENCE MECHANISMS:
- Registry Key: HKCU\Software\Microsoft\Windows\Windows NT\CurrentVersion\Winlogon
Value Name: shell
Value Type: REG_SZ
Value Data: C:\ProgramData\ddram-3\ddram-0.exe -y, explorer.exe
- Registry Key: HKCU\Software\Microsoft\Windows\CurrentVersion\Run
Value Name: blvds-4
Value Type: REG_SZ
Value Data: C:\Users\[username]\AppData\Roaming\valence-42\valence-59.exe -3
- Shortcut file: C:\Users\[username]\AppData\Roaming\Windows\Start Menu\Programs\Startup\vmebus-60.lnk
Shortcut Target: C:\ProgramData\vmebus-0\vmebus-4.exe -0
FILE HASHES:
PASSWORD-PROTECTED (ENCRYPTED) WORD DOCS ATTACHED TO THE EMAILS:
- 073afacaaec9faa399462051830c9ca37a18c53b44c861da8cb75b80f458791f - Dennis.doc
- be24f9c0d9f0789b5dbfac1102f21a0fe4deb06b1f18e0112ad120083fc96948 - Hien.doc
- c194ce90a3803d8b904632efa8fe72510d00132dc7f15cdff751ad15b9639953 - Mike.doc
- 1b09051784ce95e010e2d4b0d6e69eb511b4e6e0892bd47a03e152397c64a6ac - invoice.doc
FILES FROM AN INFECTED WINDOWS HOST (ALL NYMAIM OR NYMAIN-RELATED):
- a3195d54888f4d0057e5fdbc893b8acd412c73f3ea77da629ed120b3f63f846d - qwerty2.exe
- 2e3f9dc50efef6ec1b055e700415db2578bbba38b0e5c7ec6091e99238126b17 - ddram-0.exe
- e40ca101df83d388495cb4846930925f75b45193cf6f5688264911c18ca61e0b - valence-59.exe
- c8da98b11734e02ae2b9ae3e39c5bb4189845b1b65c4e1c85fb86033b2f2ed73 - vmebus-4.exe
FILES FROM AN EARLIER INFECTION THAT I LOST THE TRAFFIC FOR (ALL NYMAIM OR NYMAIN-RELATED):
- aabc133327f0881b95c92daf41e993b6759a8ffb71ea9472acdf01931c892bcc - qwerty2.exe
- 0cbb807e616d2f25fbaddb40e3958192b40dfbe48c46cdbd3d2bc3564a153255 - baryon-48.exe
- 068babac5b4aa202742c78ade8d04c24cb755301f9443576f2c64cc96521653e - debounce-6.exe
- 84e48f5f7a727ac502b88270ba7659a150d15105b48d6cdbbf3866622cd398fc - molecule-52.exe
IMAGES
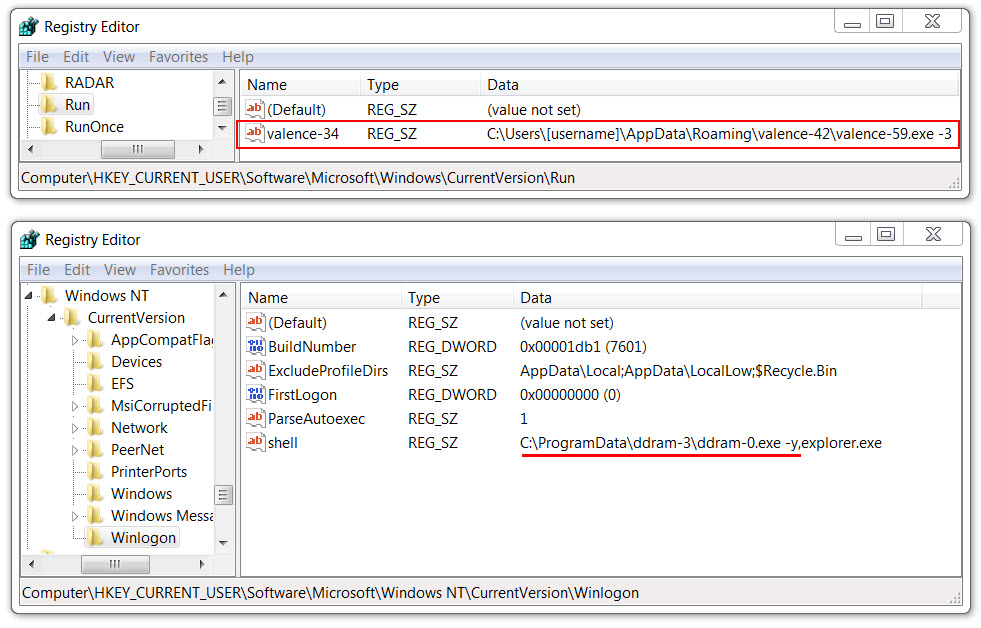
Shown above: Windows registry entries for 2 of the 3 follow-up Nymaim executables on the infected Windows host.
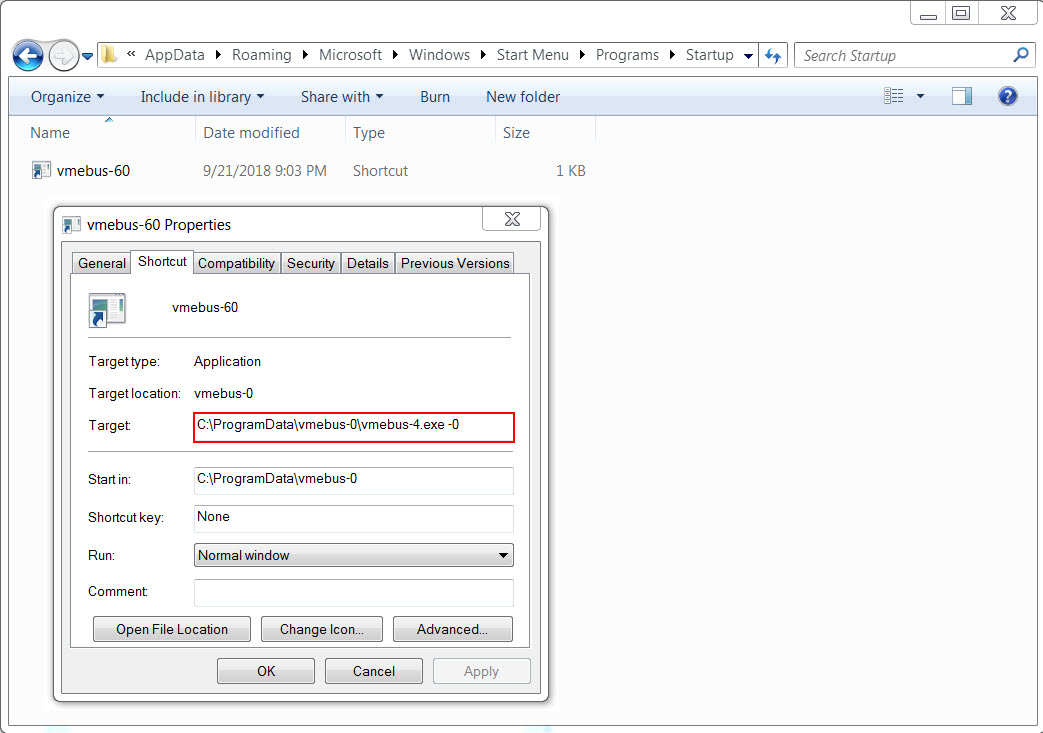
Shown above: 1 of the 3 follow-up Nymaim executables is persistent through a shortcut in the Startup folder from the Windows Start Menu.
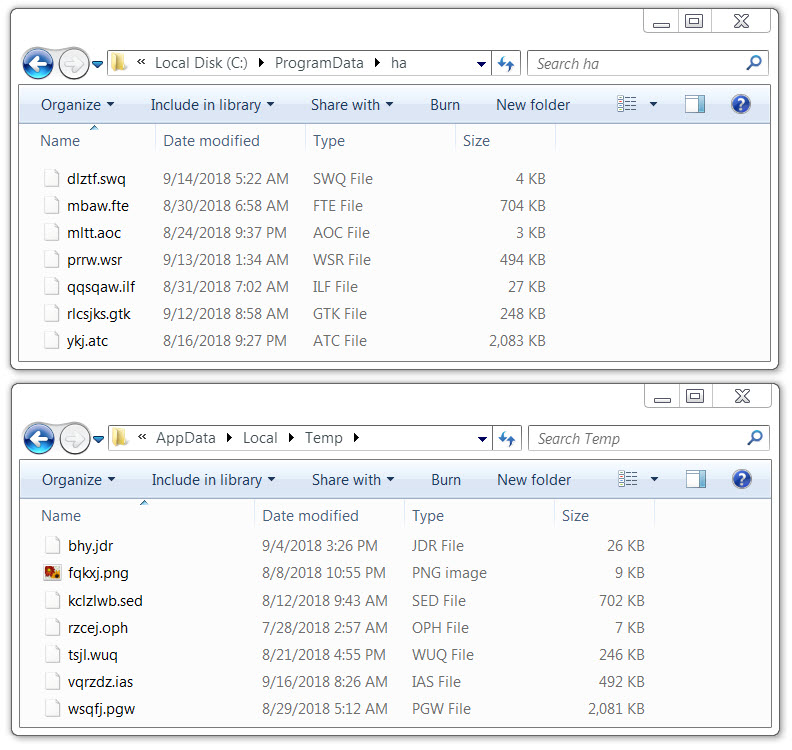
Shown above: Some randomly-named data files were also seen on the infected Windows host.
Click here to return to the main page.