2019-01-04 - HOOKADS CAMPAIGN RIG EK PUSHES SMOKELOADER
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive of the infection traffic: 2019-01-04-HookAds-campaign-Rig-EK-sends-SmokeLoader.pcap.zip 747 kB (746,662 bytes)
- 2019-01-04-HookAds-campaign-Rig-EK-sends-SmokeLoader.pcap (800,333 bytes)
- 2019-01-04-HookAds-campaign-Rig-EK-payload.exe (291,328 bytes)
- 2019-01-04-Rig-EK-artifact-a.e.txt (1,149 bytes)
- 2019-01-04-Rig-EK-flash-exploit.swf (32,313 bytes)
- 2019-01-04-Rig-EK-landing-page.txt (136,345 bytes)
- 2019-01-04-Scheduled-task-Opera_scheduled_Autoupdate_3830086449.xml.txt (3,504 bytes)
- 2019-01-04-SmokeLoader-artifact-fcifrjgj.bin (321,738 bytes)
NOTES:
- I don't post much about exploit kits (EKs) anymore, because I rarely find them.
- But every once in a while I see a tweet about EK activity from @nao_sec, and I can replicate the infection traffic.
- I kicked off today's infection chain with datitngforllives[.]com, a decoy dating site used by the HookAds campaign. It appears in ad traffic and redirects to Rig EK.
- For a historic look at the HookAds campaign, see this 2016 blog post by Malwarebytes.
- traffic.moe has some examples of the HookAds campaign using Fallout EK or Rig EK to distribute different types of malware.
WEB TRAFFIC BLOCK LIST
Indicators are not a block list. If you feel the need to block web traffic, I suggest the following domains:
- datitngforllives[.]info
- freebitc[.]pro
- letitbit[.]su
TRAFFIC
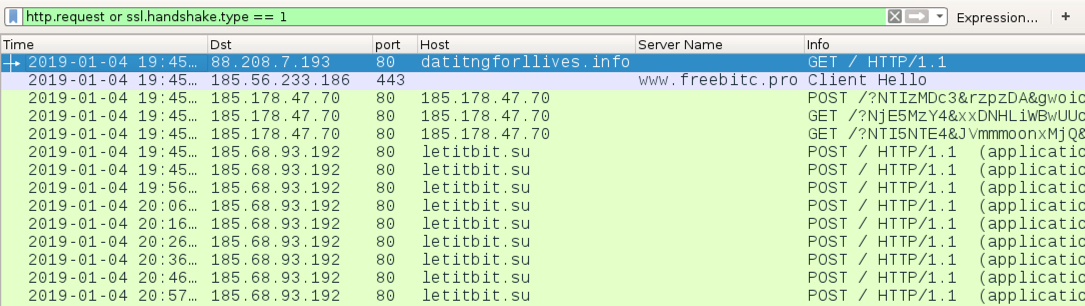
Shown above: Infection traffic filtered in Wireshark.
TRAFFIC TO DECOY DATING SITE USED BY HOOKADS AND REDIRECT LEADING TO RIG EK:
- 88.208.7[.]193 port 80 - datitngforllives[.]info - GET /
- 185.56.233[.]186 port 443 - www.freebitc[.]pro - GET /unlimited/howareyou (HTTPS traffic)
RIG EK:
- 185.178.47[.]70 port 80 - 185.178.47[.]70 - Rig EK
SMOKELOADER POST-INFECTION TRAFFIC:
- 185.68.93[.]192 port 80 - letitbit[.]su - POST /
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: d7bb1f853e55fa7f80f04bf1cd4b20129843a6821881dff0bf860dbcfbf33bac
File size: 32313 bytes
File description: Rig EK flash exploit, exploiting CVE-2018-4878, seen on 2019-01-04
HOOKADS CAMPAIGN PAYLOAD FROM RIG EK:
- SHA256 hash: 6432d90a7ffbbdd41b0da8443d2d1c4f377dabb6ffde4f6e28a8bd88d41732fb
File size: 291,328 bytes
File location: C:\Users\[username]\AppData\Roaming\Temp\rad95C6B.exe (random hex digits after "rad" and before ".exe")
File location: C:\Users\[username]\AppData\Roaming\Microsoft\Windows\fcifjgj\rrtirtbs.exe (random file and directory names under the "Windows" folder)
File description: Smokeloader EXE distributed by the HookAds campaign through Rig EK on 2019-01-04
IMAGES
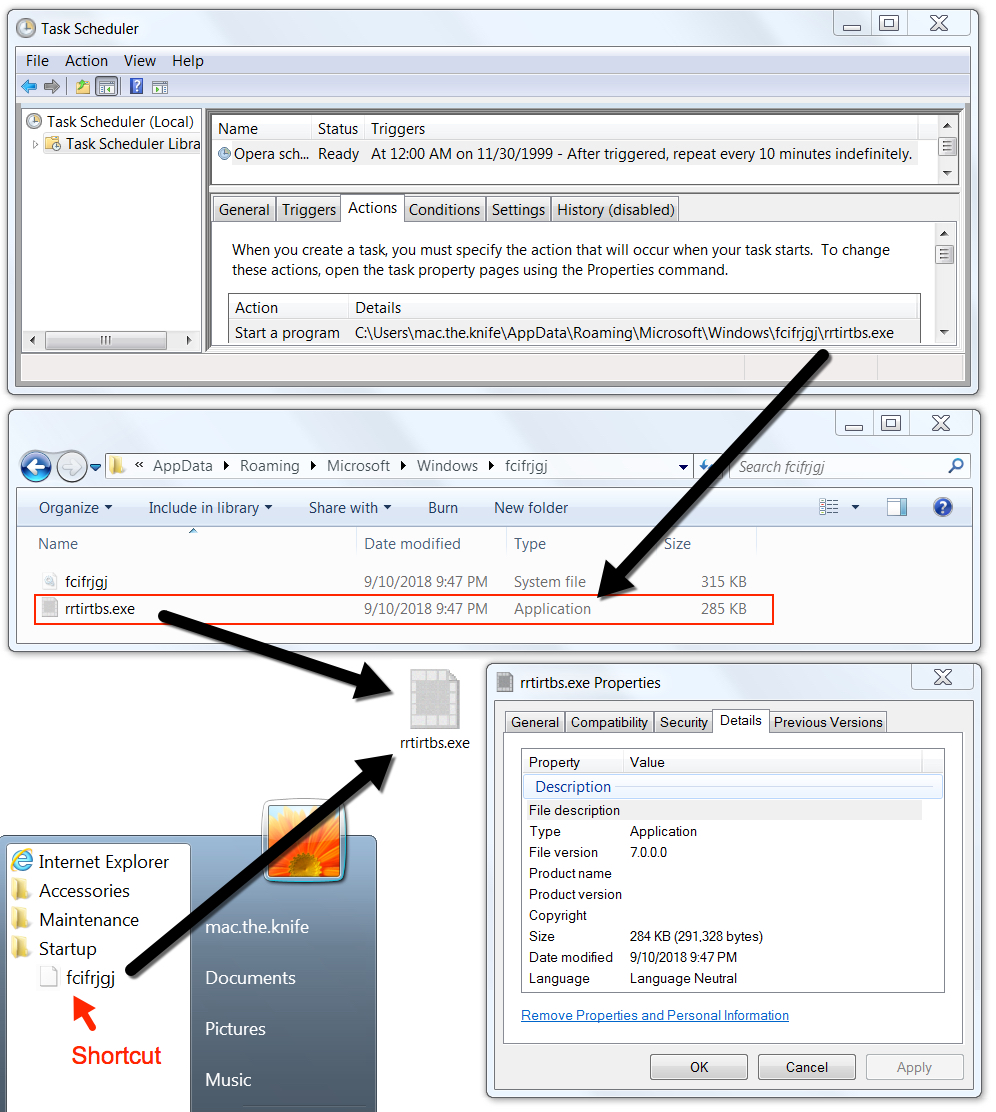
Shown above: SmokeLoader persistent on the infected Windows host.
Click here to return to the main page.
