2019-05-02 - TRAFFIC ANALYSIS EXERCISE - BEGUILESOFT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
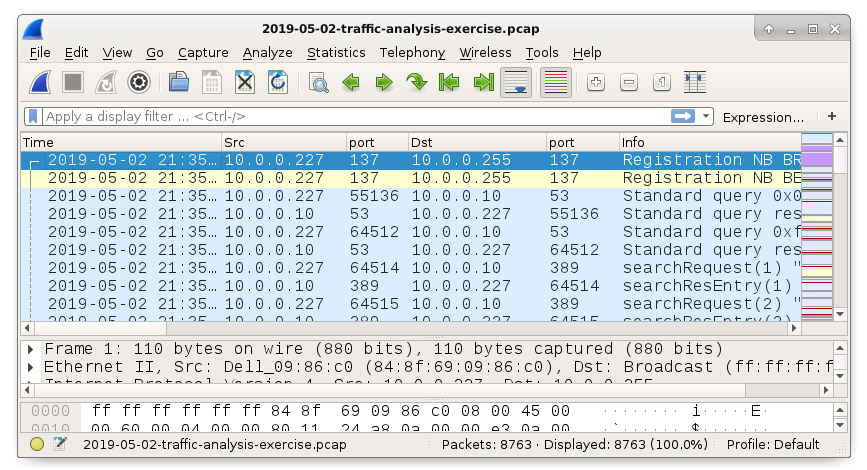
- Zip archive of the pcap: 2019-05-02-traffic-analysis-exercise.pcap.zip 5.3 MB (5,328,558 bytes)
- 2019-05-02-traffic-analysis-exercise.pcap (5,835,639 bytes)
- Zip archive of the alerts: 2019-05-02-traffic-analysis-exercise-alerts.zip 437 kB (162,193 bytes)
- 2019-05-02-traffic-analysis-exercise-alerts.jpg (202,610 bytes)
- 2019-05-02-traffic-analysis-exercise-alerts.txt (1,916 bytes)
- 2019-05-02-traffic-analysis-exercise-alerts-expanded.txt (14,997 bytes)
SCENARIO
LAN segment data:
- LAN segment range: 10.0.0[.]0/24 (10.0.0[.]0 through 10.0.0[.]255)
- Domain: beguilesoft[.]com
- Domain controller: 10.0.0[.]10 - BeguileSoft-DC
- LAN segment gateway: 10.0.0[.]1
- LAN segment broadcast address: 10.0.0[.]255
YOUR TASK
Review the pcap and alerts, then write an incident report for this infected Windows host. See below for a suggested template of an incident report.
Executive summary:
On 2019-05-02 at ??:?? UTC, a Windows host used by ????????? was infected with ???????Details of the infected Windows host:
IP address:
MAC address:
Host name:
Windows user account name:Indicators of Compromise:
[List of URLs, domains, IP addresses, and SHA256 hashes related to the infection should appear in this section]
ANSWERS
- Click here for the answers.
Click here to return to the main page.