2019-09-13 - WSHRAT INFECTION FROM MALSPAM
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2019-09-13-malspam-pushing-WSHRAT.eml.zip 41.9 kB (41,876 bytes)
- 2019-09-13-WSHRAT-infection-traffic.pcap.zip 19.3 MB (19,320,697 bytes)
- 2019-09-13-WSHRAT-malware-and-artifacts.zip 79.5 kB (79,509 bytes)
IMAGES
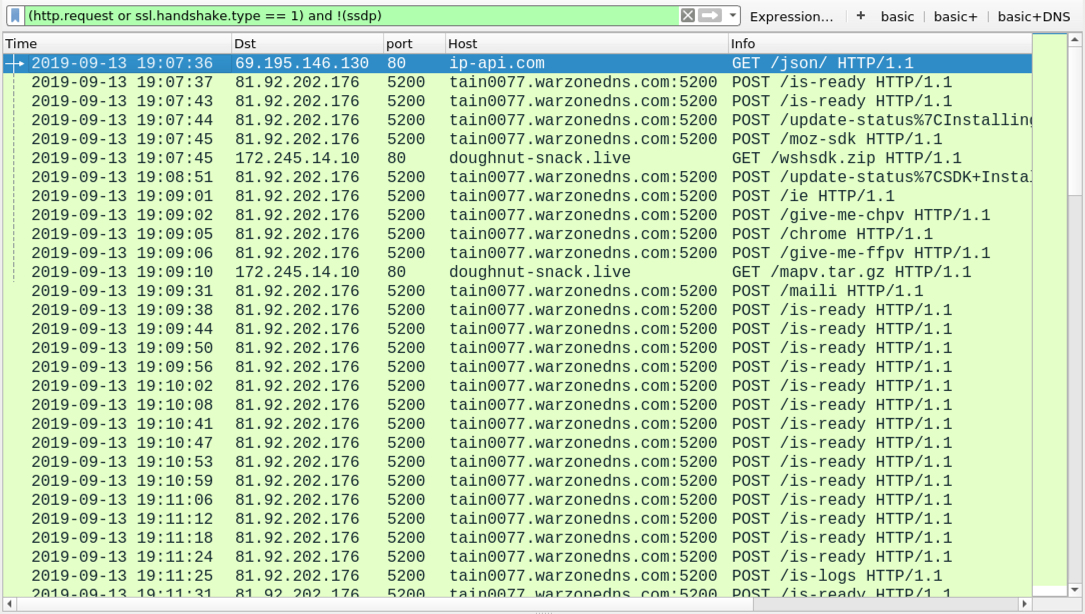
Shown above: Traffic from the infection filtered in Wireshark.
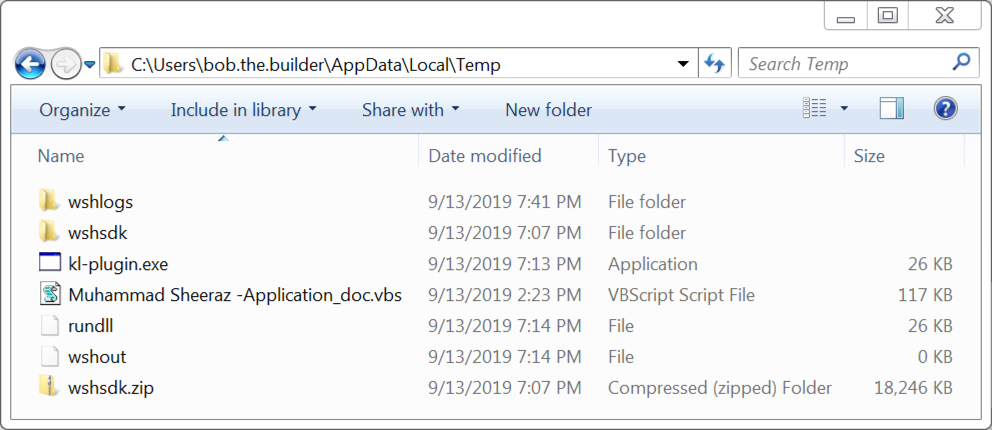
Shown above: Artifacts noted in the infected user's AppData\Local\Temp directory.
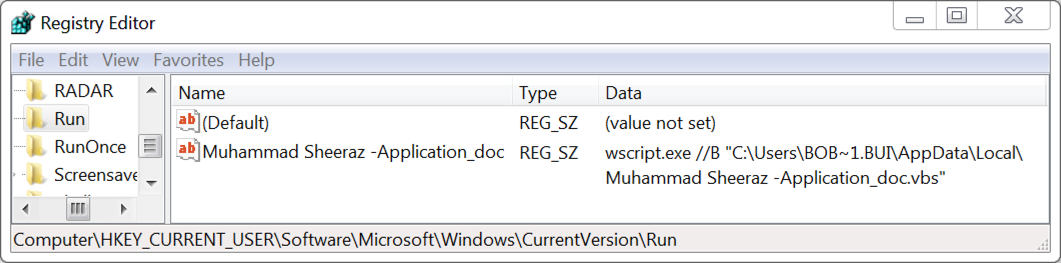
Shown above: WSHRAT persistent on the infected Windows host through the registry.
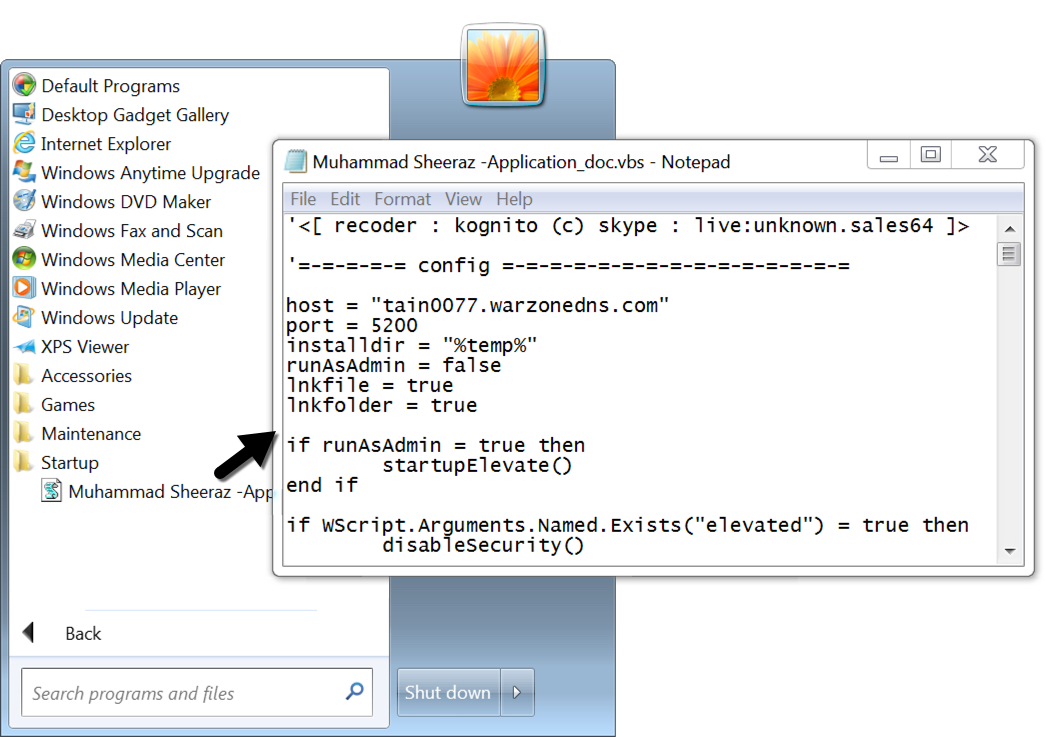
Shown above: WSHRAT persistent on the infected Windows host through the Startup directory.
Click here to return to the main page.
