2020-10-20 - HANCITOR WITH SOMETHING AND COBALT STRIKE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2020-10-20-Hancitor-IOCs.txt.zip 2.6 kB (2,574 bytes)
- 2020-10-20-Hancitor-malspam-9-examples.zip 19.9 kB (19,914 bytes)
- 2020-10-20-Hancitor-infection-traffic.pcap.zip 4.4 MB (4,444,385 bytes)
- 2020-10-20-Hancitor-and-follow-up-malware.zip 760 kB (760,319 bytes)
IMAGES
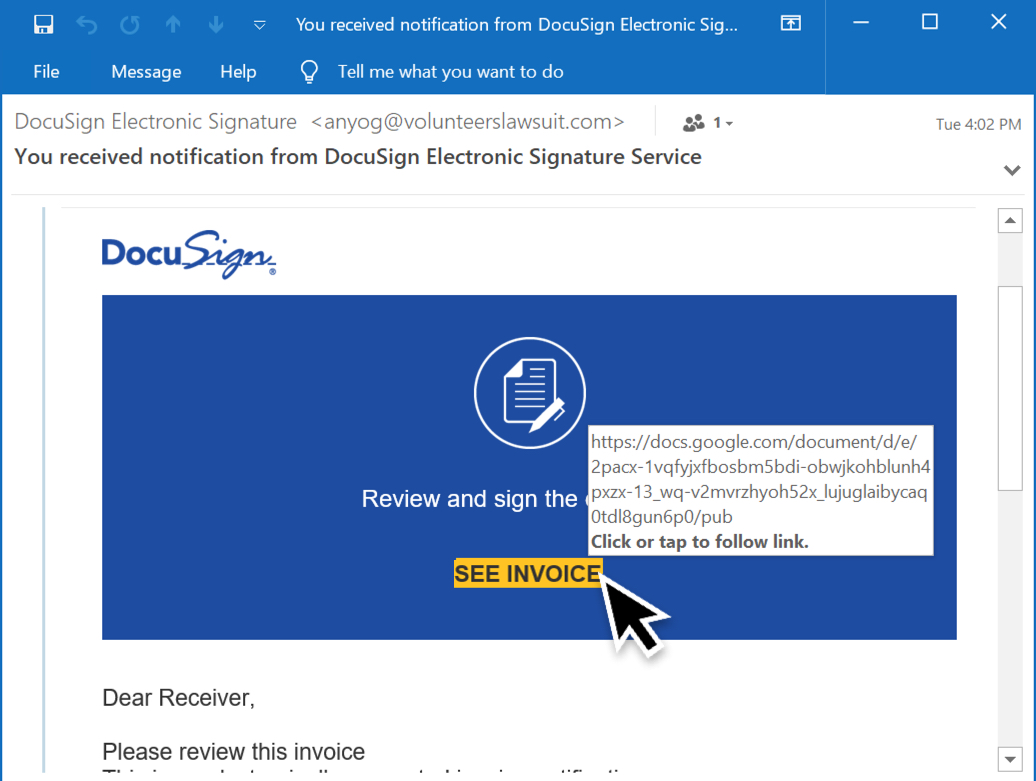
Shown above: Screen shot from an example of malspam pushing Hancitor.
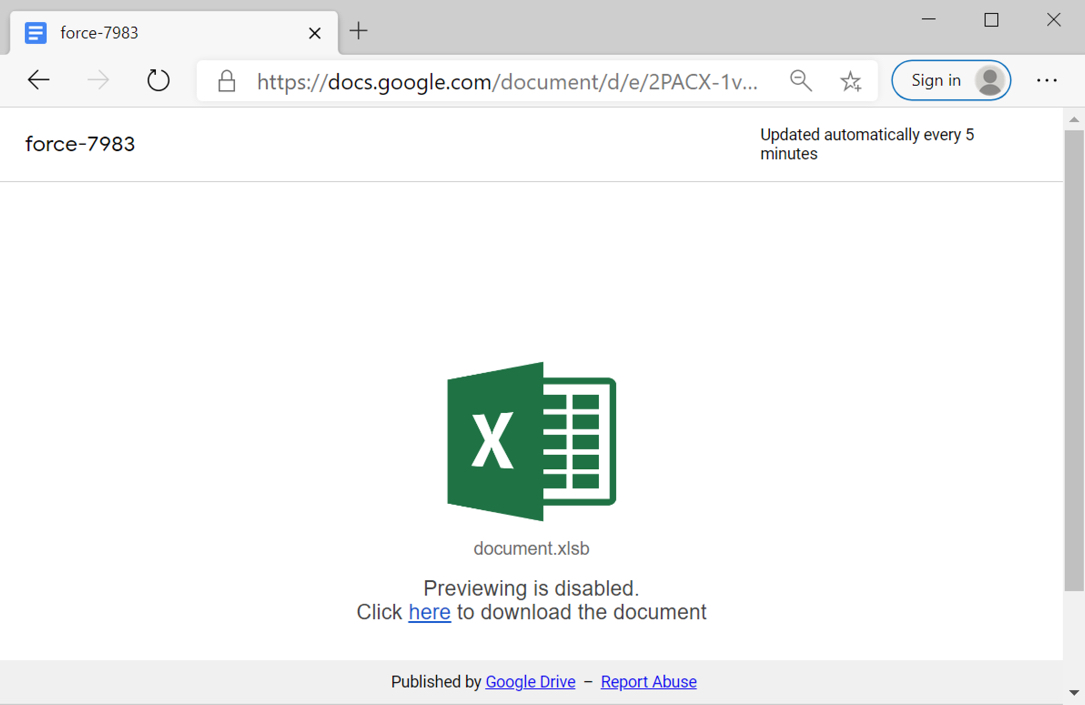
Shown above: Screenshot from one of the Google Docs pages leading to the spreadsheet.
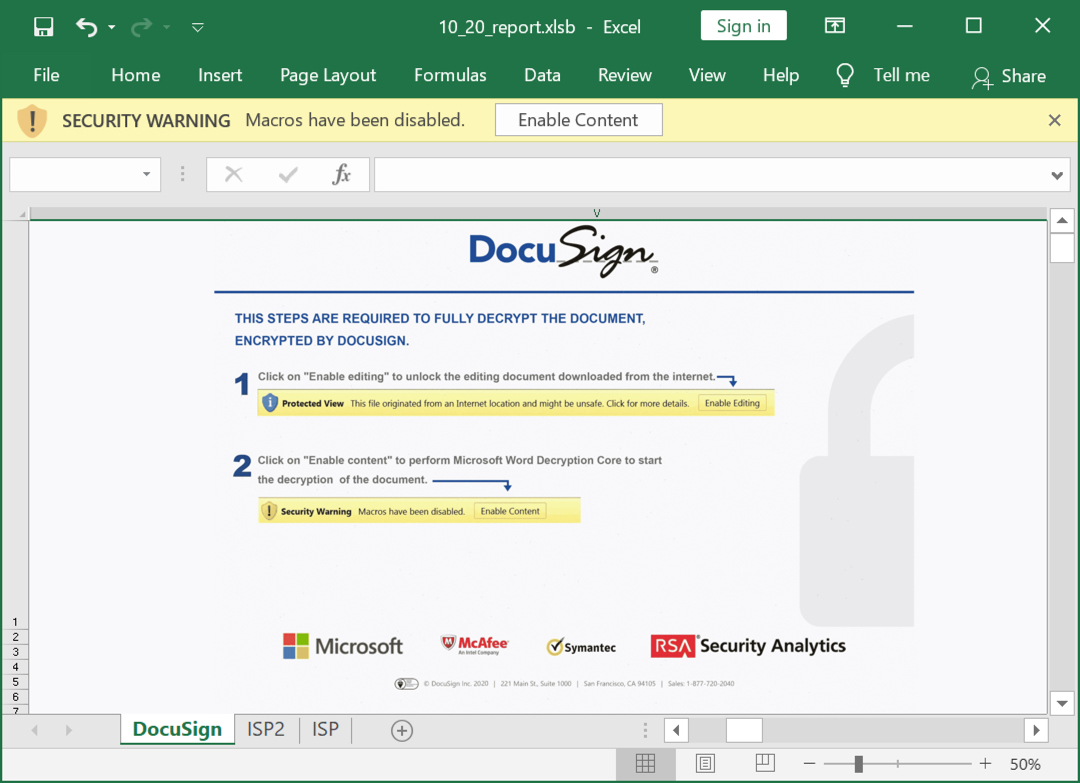
Shown above: Screenshot from one of the Excel files downloaded through the Google Docs pages.
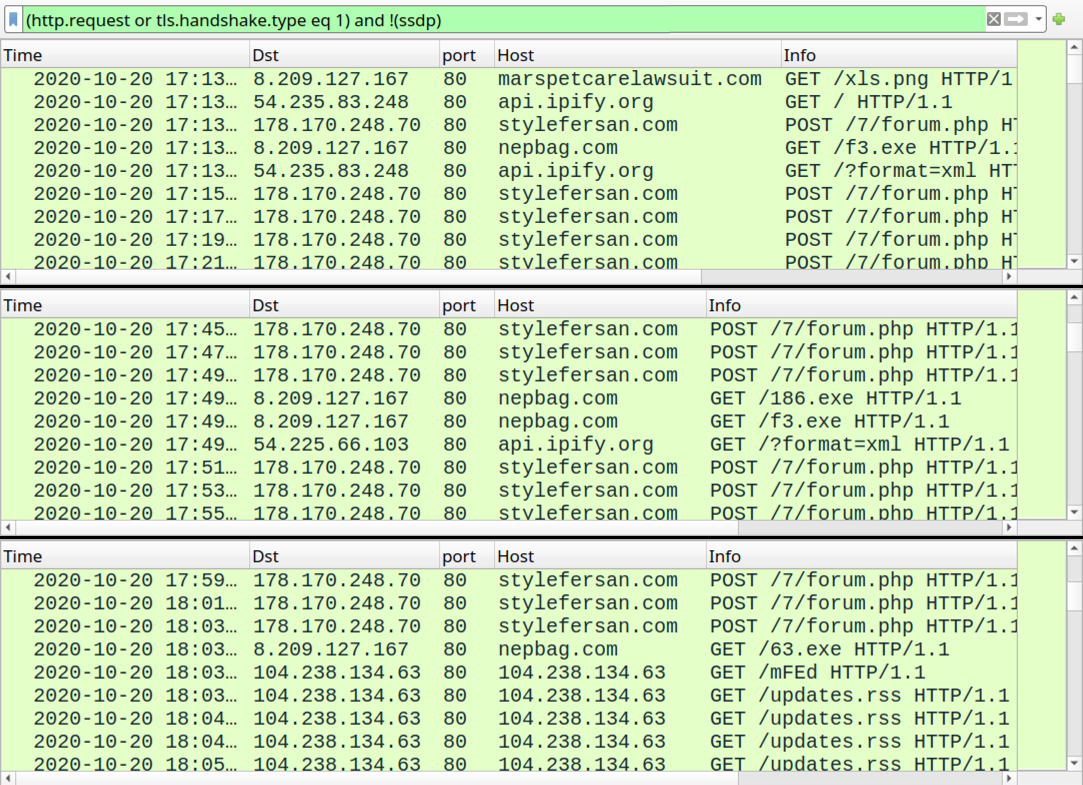
Shown above: Traffic from an infection filtered in Wireshark.
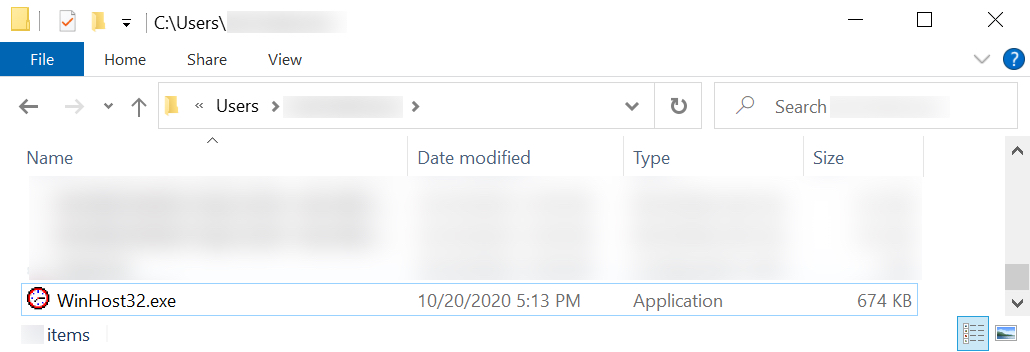
Shown above: The initial Hancitor EXE.
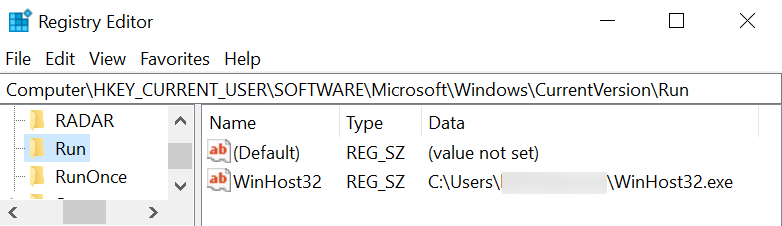
Shown above: Registry update to make the Hancitor EXE persistent.
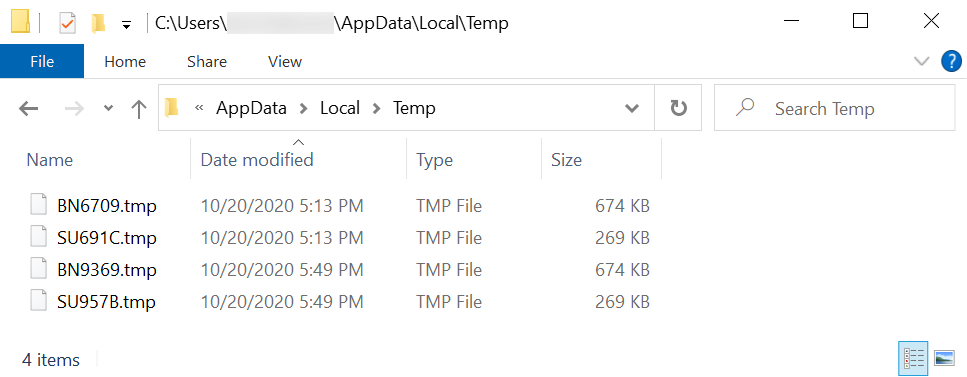
Shown above: Malware binaries in the infected user's AppData\Local\Temp directory.
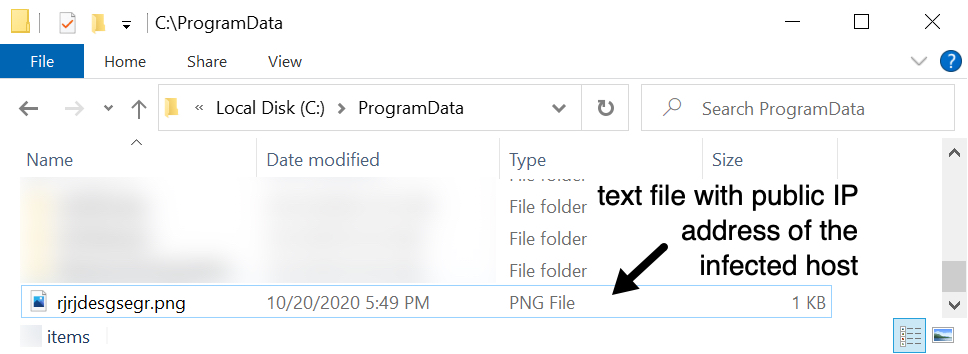
Shown above: This appeared after the Cobalt Strike activity started.
Click here to return to the main page.
