2022-03-21 (MONDAY) - HANCITOR (CHANITOR/MAN1/MOSKALVZAPOE/TA511) WITH COBALT STRIKE & MARS STEALER
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2022-03-21-Hancitor-infection-IOCs.txt.zip 1.8 kB (1,773 bytes)
- 2022-03-21-Hancitor-with-Cobalt-Strike-and-Mars-Stealer.pcap.zip 2.3 MB (2,342,008 bytes)
- 2022-03-21-Hancitor-and-Mars-Stealer-malware.zip 3.6 MB (3,590,358 bytes)
NOTES:
- The initial Hancitor Word doc was likely downloaded from a link distributed through eFax-themed Hancitor malspam.
- Hancitor malspam is not as widespread as it was previously, so I don't have any copies of emails from this wave of infection activity.
IMAGES
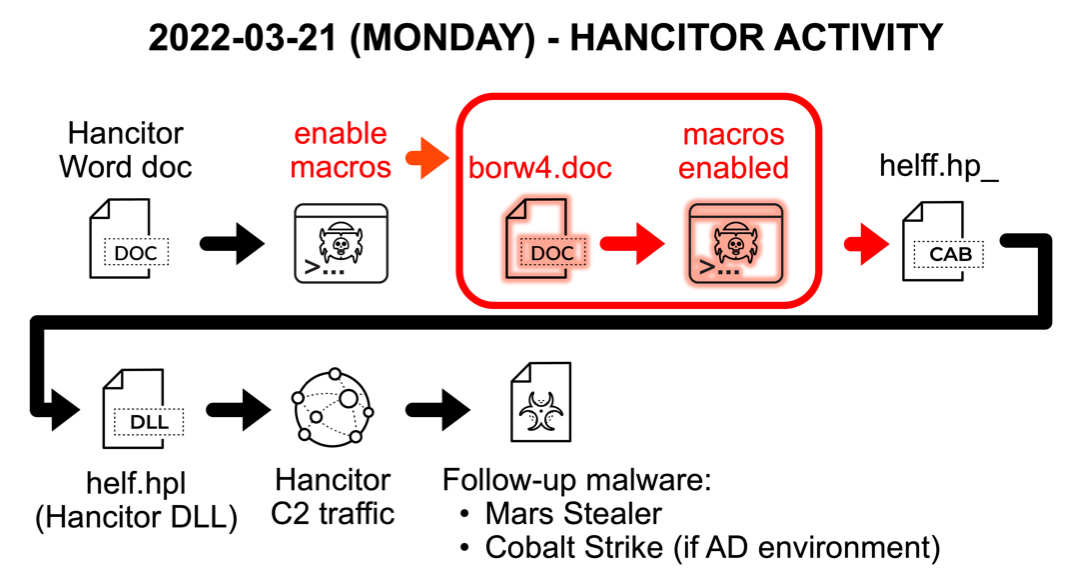
Shown above: Flow chart for this infection.
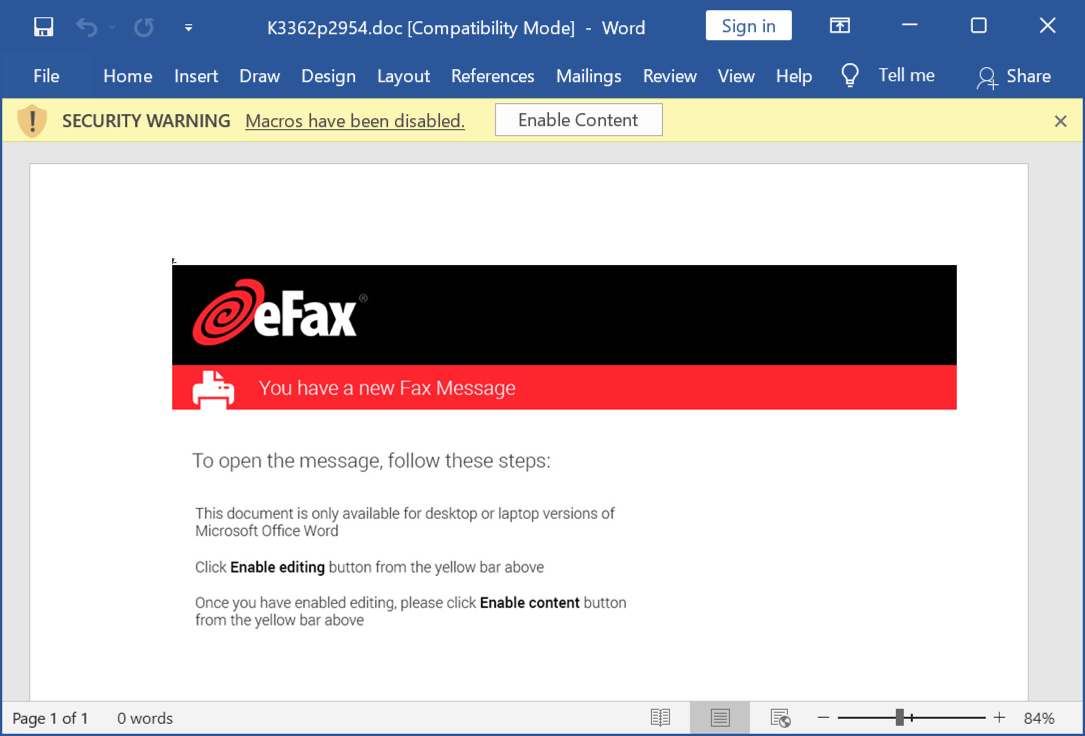
Shown above: Screen shot of the downloaded Hancitor Word document.
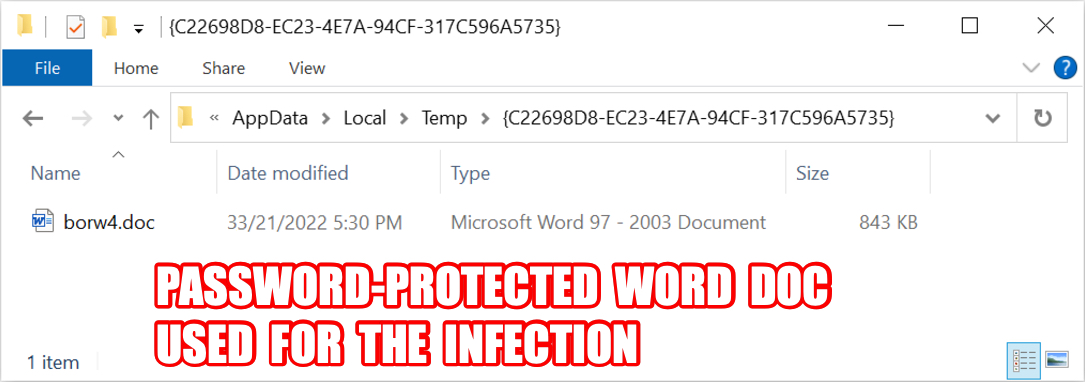
Shown above: Password-protected Word doc dropped after enabling macros on Hancitor Word doc.
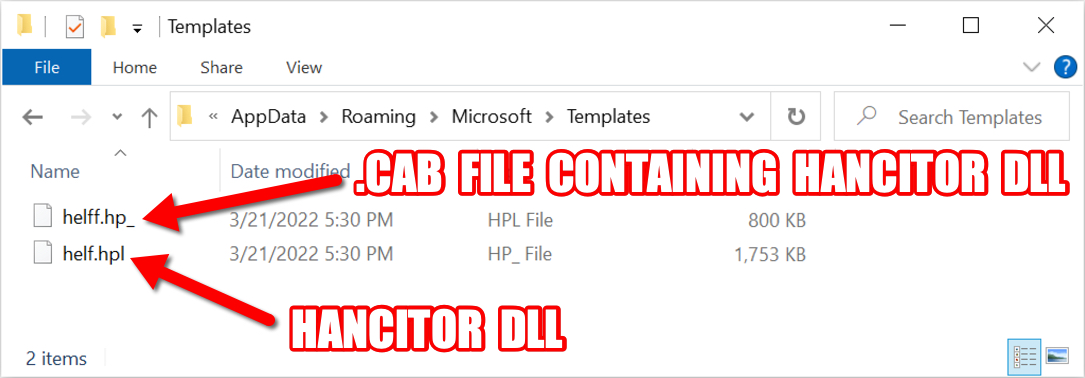
Shown above: .cab file created by password-protected Word doc and extracted Hancitor DLL.
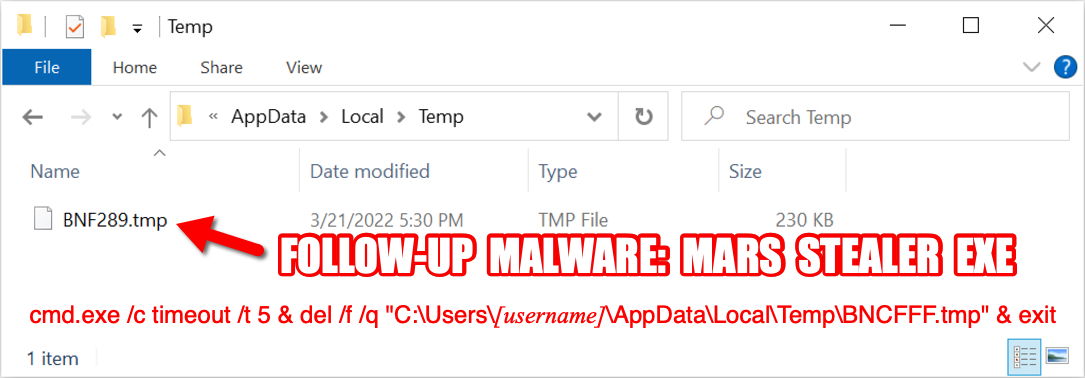
Shown above: Follow-up malware Mars Stealer temporarily saved to the infected Windows host.
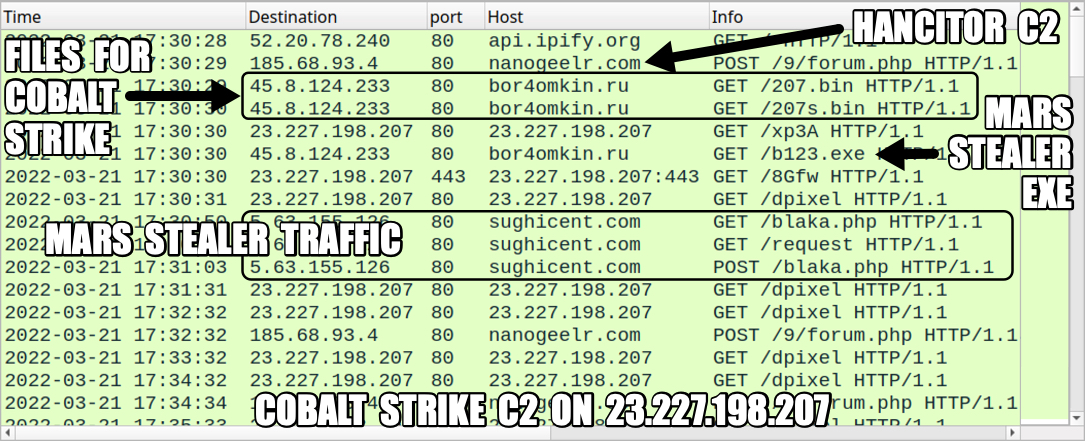
Shown above: Traffic from the infection filtered in Wireshark.
Click here to return to the main page.
