2022-06-08 (WEDNESDAY) - MONSTER LIBRA (TA551) SVCREADY INFECTION
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
NOTES:
- Sometime in April 2022, Monster Libra (TA551) began distributing a new malware family named SVCready.
- Today's infection used a Word document with an Italian language template.
- More information on SVCready can be found here.
- Some data on Monster Libra can be found here.
ASSOCIATED FILES:
- 2022-06-08-IOCs-for-SVCready-infection.txt.zip 1.8 kB (1,846 bytes)
- 2022-06-08-SVCready-infection.pcap.zip 4.8 MB (4,818,874 bytes)
- 2022-06-08-SVCready-malware-and-artifacts.zip 5.0 MB (4,995,727 bytes)
INDICATORS
MALWARE:
SHA256 hash: d74c9ebf3a09df2fccd47265ddab693862b09a4d1cfea336675baff32bc83c93
- File size: 1,986,318 bytes
- File name: coreinsrl.document.08.06.2022.doc
- File description: Example of Italian language template Word document with macros for SVCready
SHA256 hash: 6cbe0e1f046b13b29bfa26f8b368281d2dda7eb9b718651d5856f22cc3e02910
- File size: 61,440 bytes
- File location: C:\Users\[username]\AppData\Local\Temp\r78AD.tmp.exe
- File description: Copy of rundll32.exe (not inherently malicious)
SHA256 hash: d1fd5c38787affe3b1a09039baff4f4be3a8a7045927fd32536db3310a886b0c
- File size: 835,584 bytes
- File location: hxxp[:]//marinesss[.]su/xd/DE8dTPMvW1_oSwAuyl6sWTbkxj7zUB0TbQ~~/XXIuljLT2yw6c132eukG9J3jqz470HZ8jw~~/
- Initial saved location: C:\Users\[username]\AppData\Local\Temp\y7021.tmp.dll
- Persistent saved location:
- C:\Users\[username]\AppData\Roaming\Microsoft\03111A6F-4EE9-4DD1-B29C-98A365C3A188.mLT
- C:\Users\[username]\AppData\Roaming\Microsoft\A7618B65-1624-4887-901E-B5C83235DE38.GD8
- C:\Users\[username]\AppData\Roaming\Microsoft\E63A728C-39AA-4C37-8760-C11049F7B898.XcT
- C:\Users\[username]\AppData\Roaming\Microsoft\F0610BAA-2BD0-494E-A3C9-EA29C25A8FFB.88B
- File description: SVCready DLL
- Run method: rundll32.exe [filename], DllRegisterServer
- Note 1: The persistent SVCready DLL is copied to a new name approximately every 30 to 45 minutes.
- Note 2: The scheduled task is updated to relfect the new name of the SVCready DLL
- Note 3: Old copies of the SVCready DLL remain under C:\Users\[username]\AppData\Roaming\Microsoft\
INFECTION TRAFFIC DOMAINS/IP ADDRESSES:
- 5.188.90[.]154 port 80 - marinesss[.]su
- 5.188.90[.]154 port 80 - galmerts[.]art
INFECTION TRAFFIC URLS:
- marinesss[.]su - GET /xd/DE8dTPMvW1_oSwAuyl6sWTbkxj7zUB0TbQ~~/XXIuljLT2yw6c132eukG9J3jqz470HZ8jw~~/ HTTP/1.1
- marinesss[.]su - POST /xl/gate/check HTTP/1.1
- marinesss[.]su - POST /xl/gate HTTP/1.1 (text/plain)
- marinesss[.]su - POST /xl/gate HTTP/1.1
- marinesss[.]su - POST /xl/gate/task HTTP/1.1
- galmerts[.]art - POST /xl/gate/check HTTP/1.1
- galmerts[.]art - POST /xl/gate HTTP/1.1 (text/plain)
- galmerts[.]art - POST /xl/gate HTTP/1.1
- galmerts[.]art - POST /xl/gate/task HTTP/1.1
IMAGES
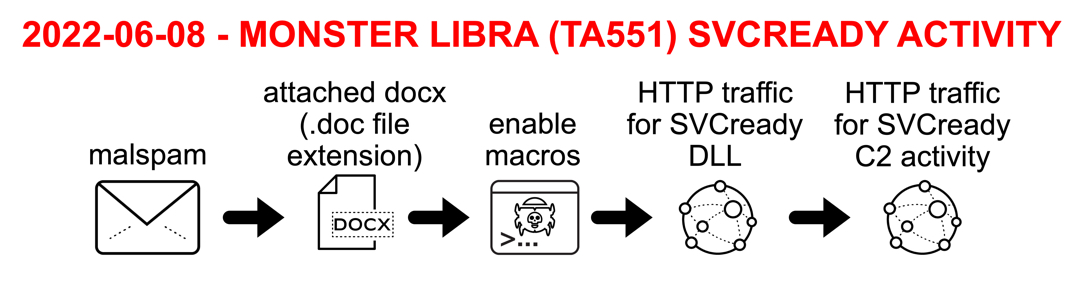
Shown above: Chain of events for this SVCready infection.
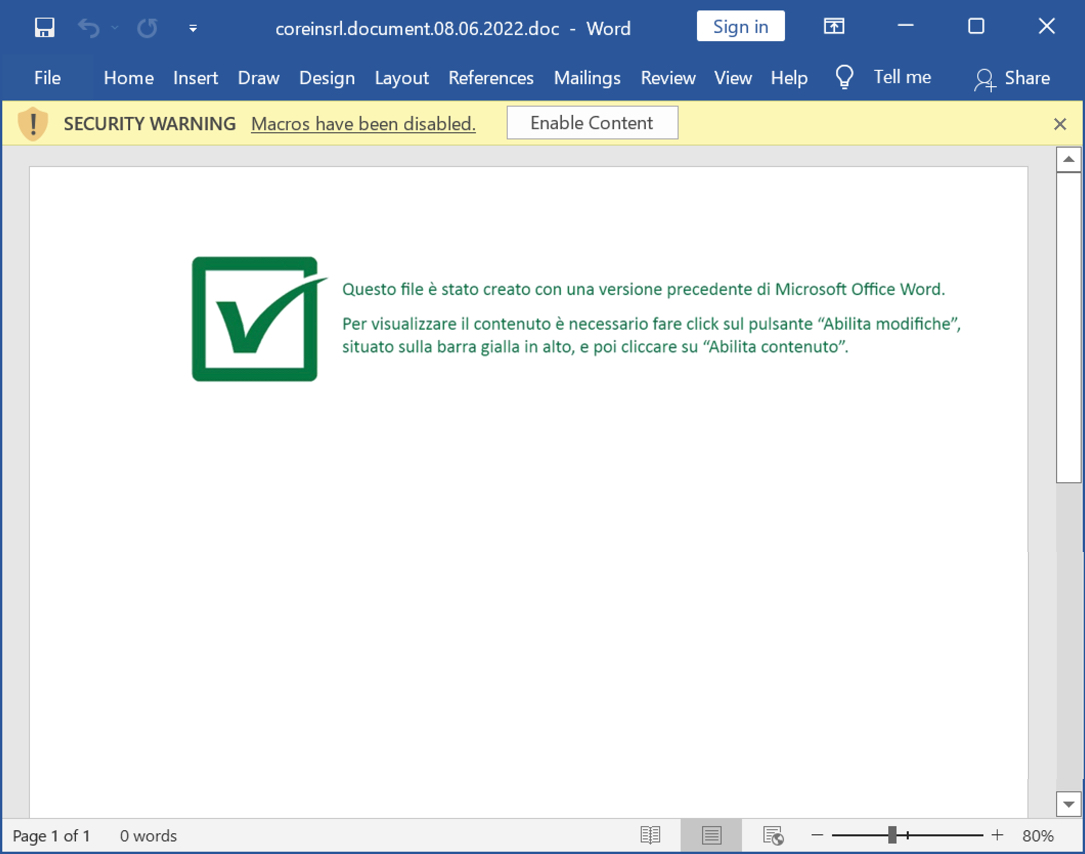
Shown above: Word document with macros for SVCready.
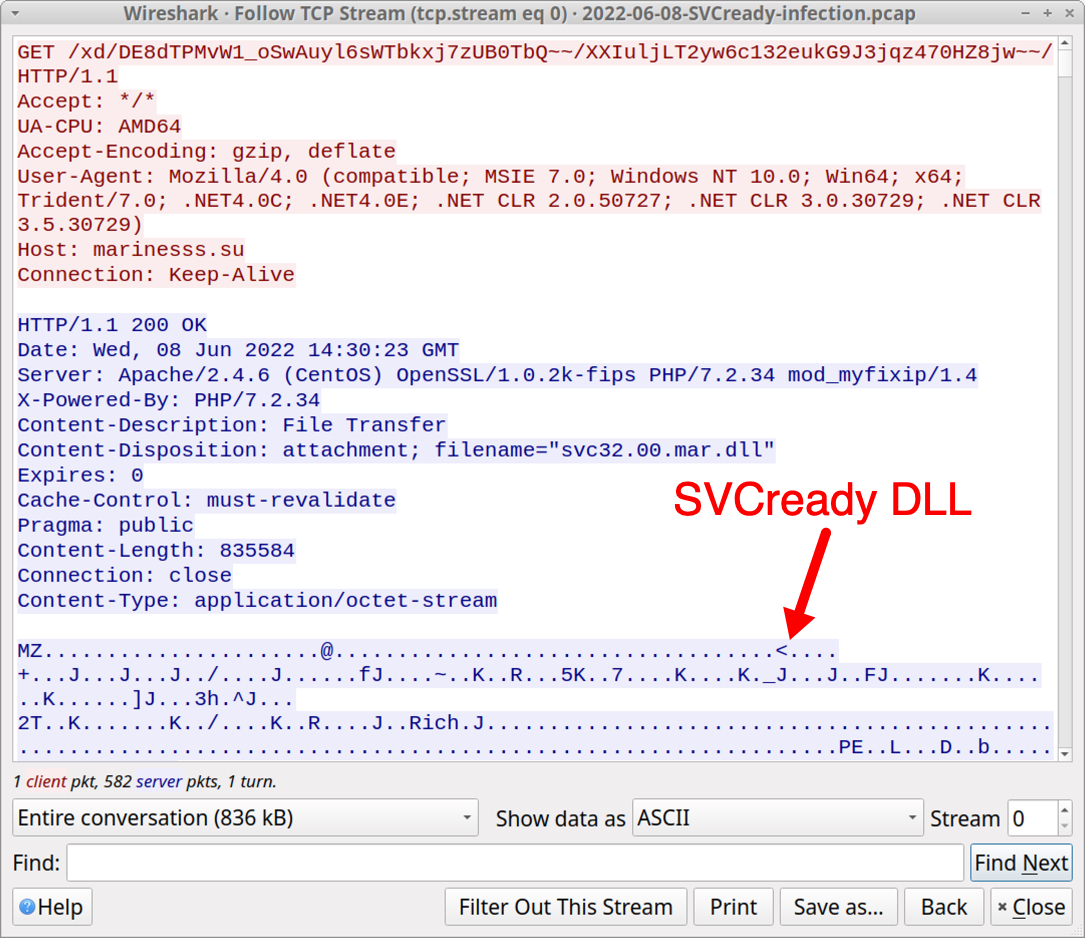
Shown above: TCP stream of SVCready DLL retrieved in network traffic.
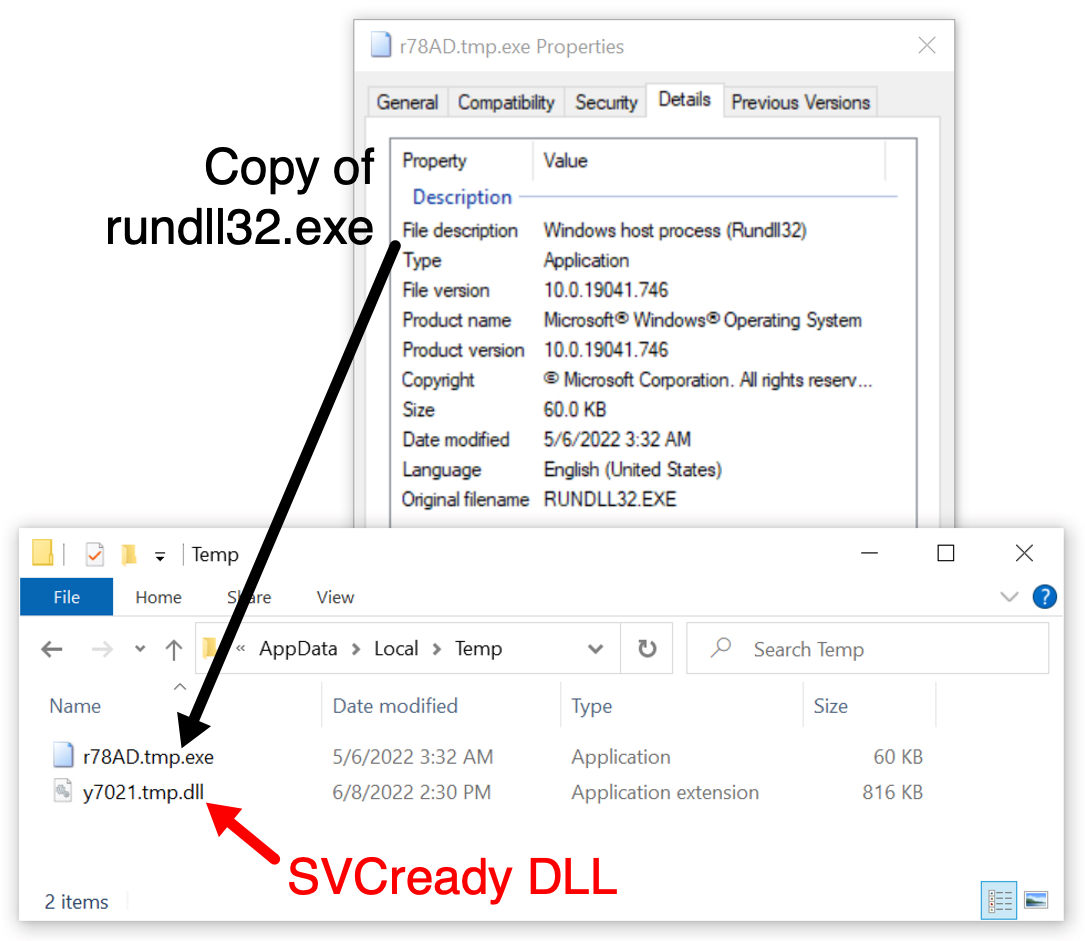
Shown above: SVCready DLL saved to the local host, run with a copy of rundll32.exe in teh same directory.
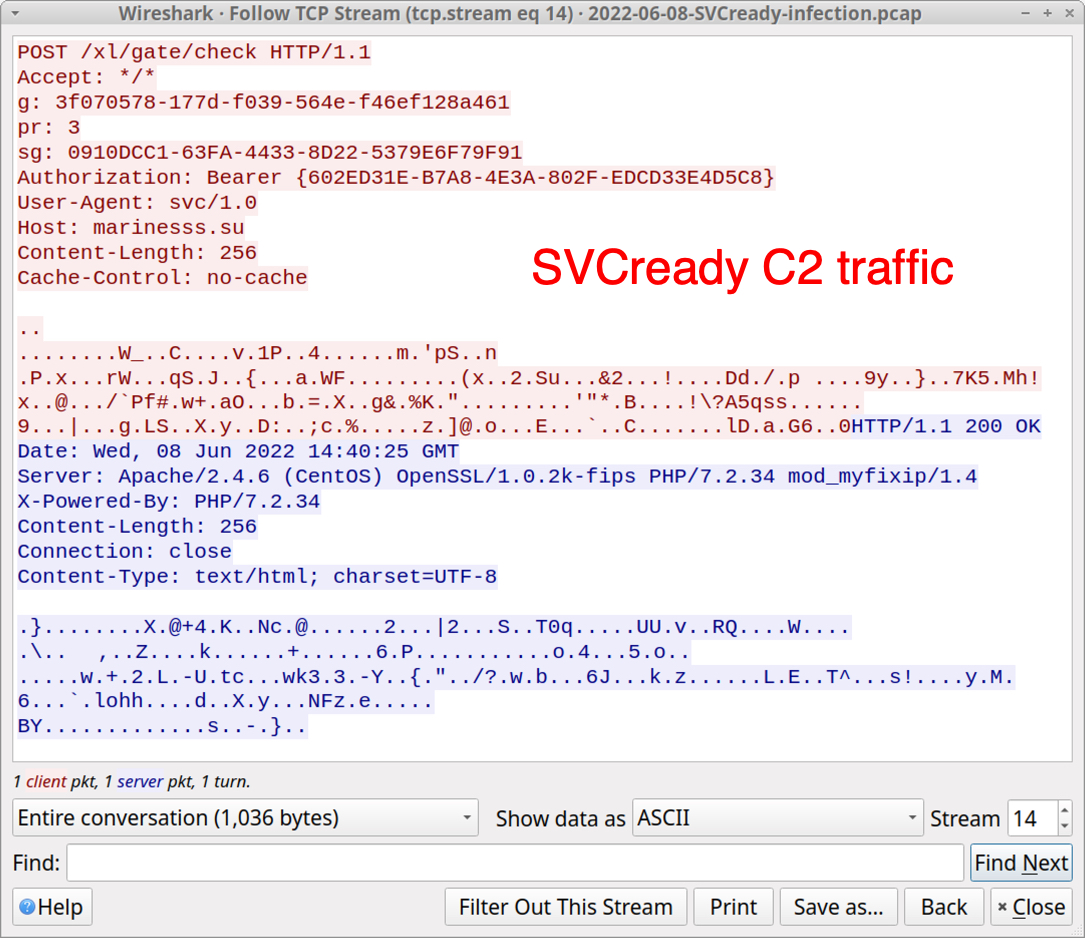
Shown above: TCP stream of SVCready C2 traffic.
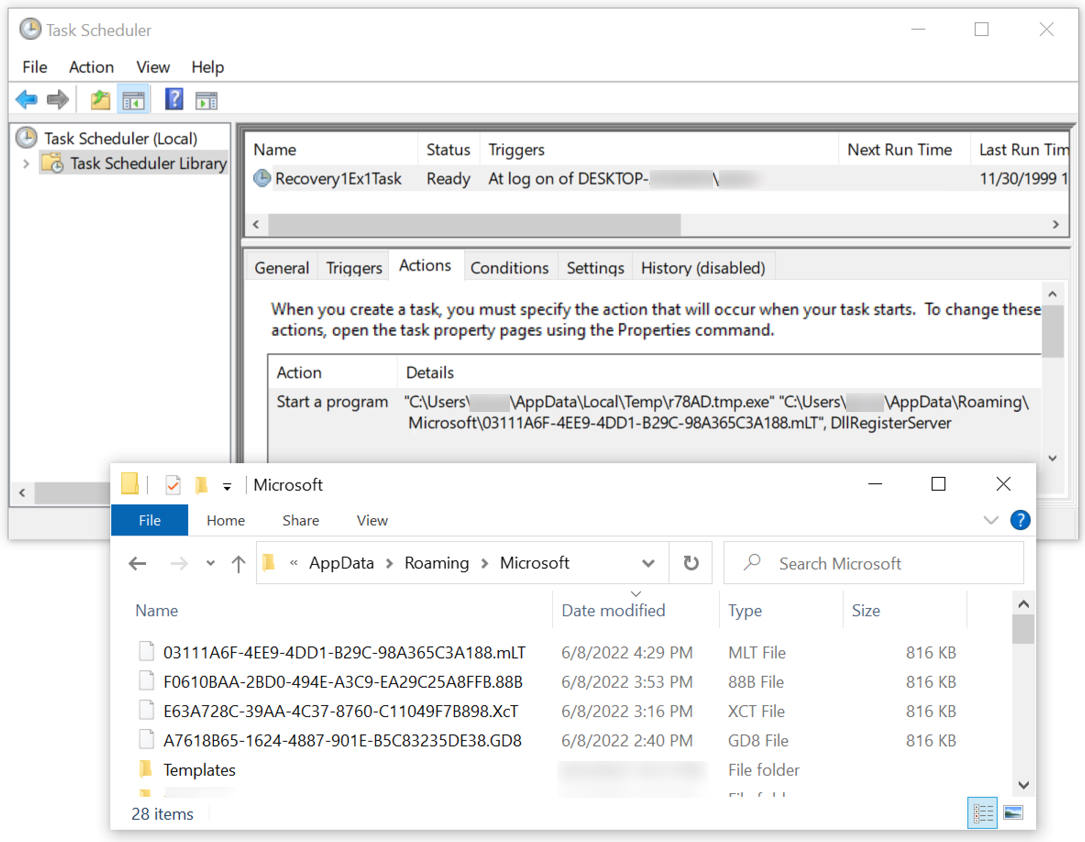
Shown above: Scheduled task to keep SVCready persistent on the infected Windows host.
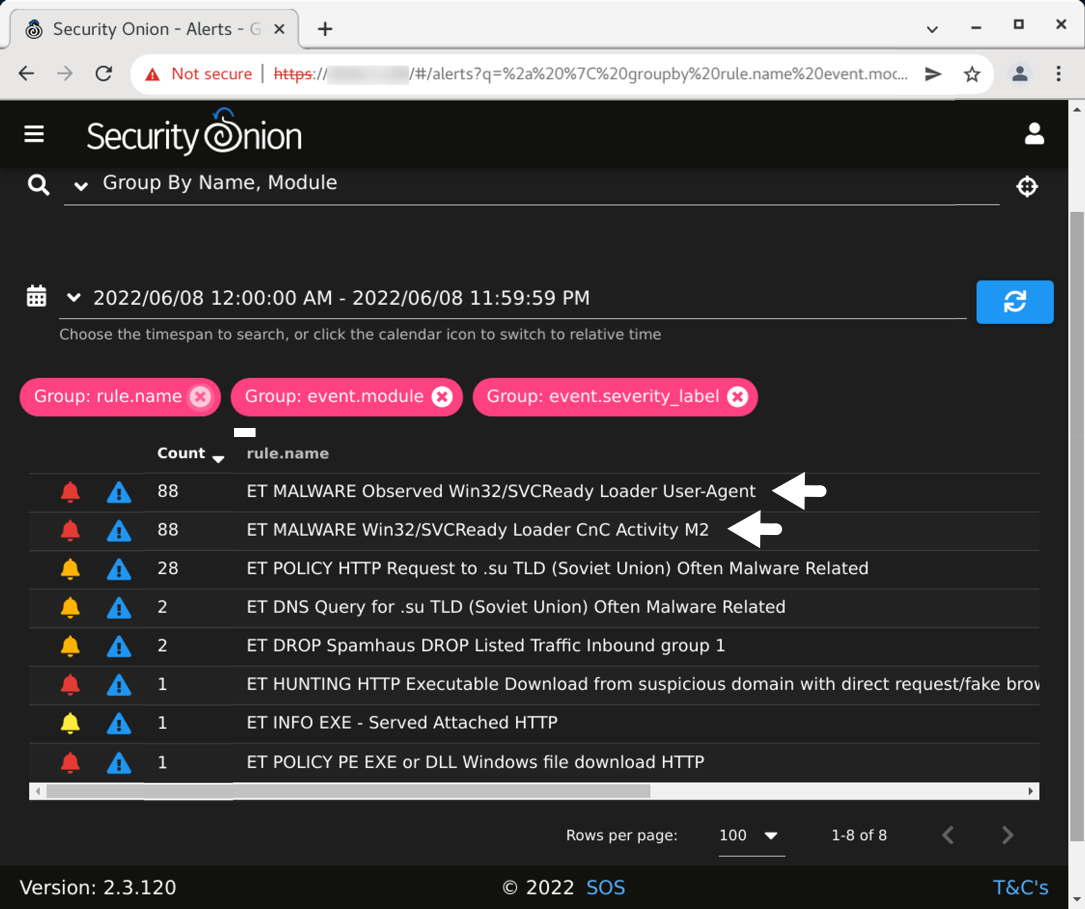
Shown above: Alerts on the traffic from Security Onion using the EmergingThreats open ruleset.
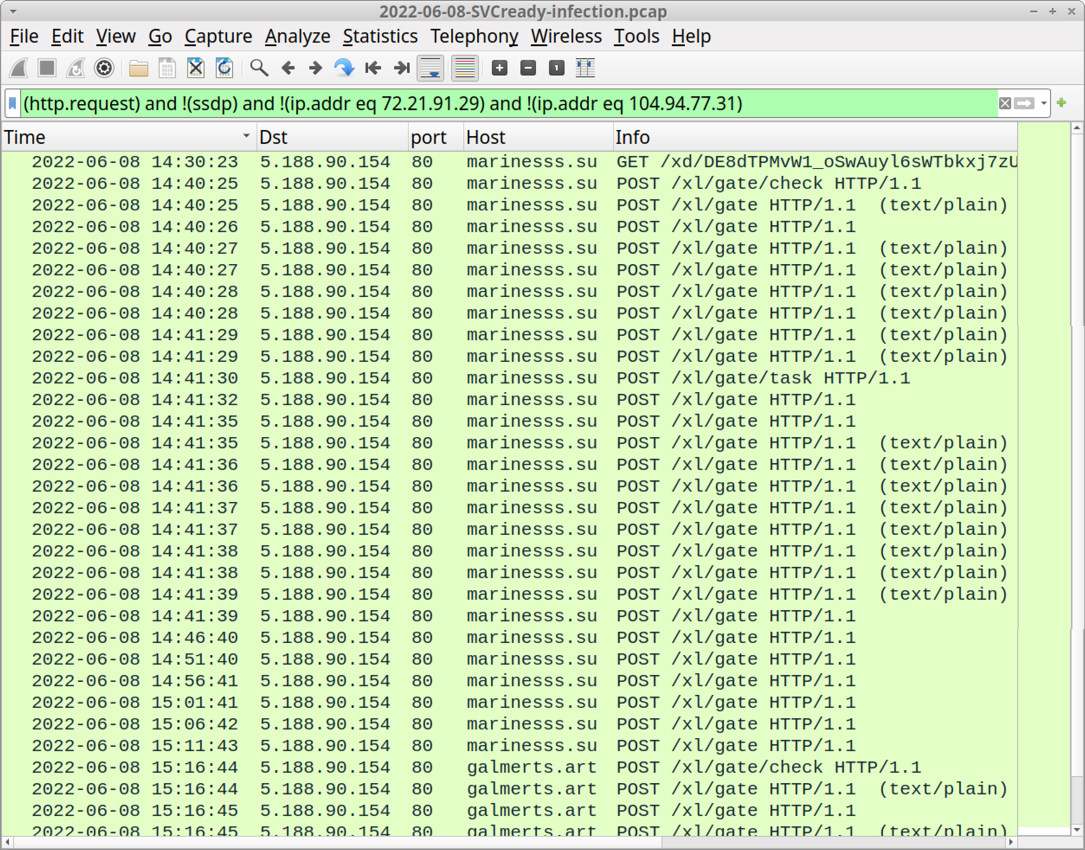
Shown above: Traffic from the infection filtered in Wireshark.
Click here to return to the main page.
