2026-01-01 (THURSDAY): LUMMA STEALER INFECTION WITH FOLLOW-UP MALWARE
NOTICE:
- Zip files are password-protected. Of note, this site has a new password scheme. For the password, see the "about" page of this website.
ASSOCIATED FILES:
- 2026-01-01-IOCs-for-Lumma-Stealer-and-follow-up-malware.txt.zip 1.1 kB (1,054 bytes)
- 2026-01-01-Lumma-Stealer-infection-with-follow-up-malware.pcap.zip 4.5 MB (4,501,606 bytes)
- 2026-01-01-files-from-the-infection.zip 19.4 MB (19,373,875 bytes)
2026-01-01 (THURSDAY): LUMMA STEALER INFECTION WITH FOLLOW UP MALWARE EXAMPLE OF LUMMA STEALER EXE: - SHA256 hash: 07b8e705a0017ab1df5ffabc1fc7fb0a4d0738e98235b5725e47bb9d5229c5c4 - File size: 31,720,900 bytes - File type: PE32 executable (GUI) Intel 80386, for MS Windows - File name: application .exe - File desecription: Installer EXE for Lumma Stealer - Note: Original file was 900 MB with null byte padding; this has most of the padding removed. FILES TEMPORARILY SAVED TO AN INFECTED WINDOWS HOST BY THE INSTALLER: - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\645429\Treat.exe <-- copy of AutoIt3.exe - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Auction - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Mono - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Portraits - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Uniform - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Finish.accde <-- script to build Lumma Stealer .a3x file - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Lifetime.accde - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Omega.accde - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Refugees.accde - C:\Users\[username]\AppData\Local\Temp\IXP000.TMP\Tries.accde AUTOIT3 SCRIPT (.A3X) FOR LUMMA STEALER CREATED BY THE INSTALLER: - SHA256 hash: 477bb335e2512e4a6b24b9b4ba6811e3d318bfa77d7665fec93e8d13a7bd820b - File size: 762,960 bytes - File type: data LUMMA STEALER C2 TRAFFIC: - offenms[.]cyou - HTTP and HTTPS traffic TRAFFIC FOR FOLLOW-UP MALWARE: - hxxps[:]//pastebin[.]com/raw/pr8gCLAA - memory-scanner[.]cc - HTTPS traffic - communicationfirewall-security[.]cc - HTTPS traffic
IMAGES
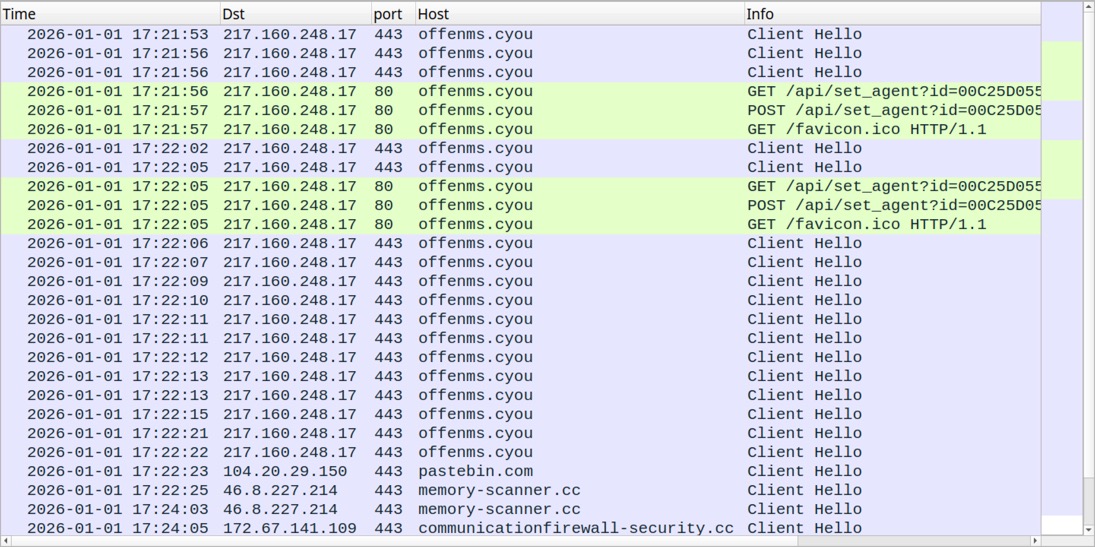
Shown above: Traffic from an infection filtered in Wireshark.
Click here to return to the main page.
