2015-07-11 - TRAFFIC ANALYSIS EXERCISE - AN INCIDENT AT PYNDRINE INDUSTRIES
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
TRAFFIC:
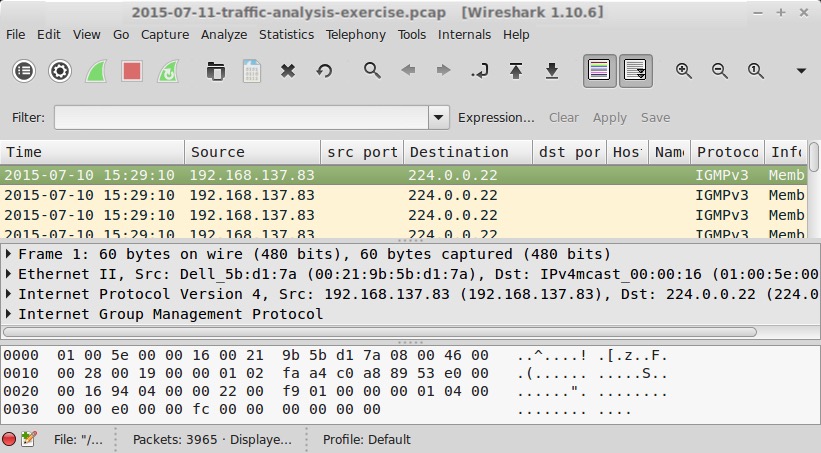
- 2015-07-11-traffic-analysis-exercise.pcap.zip 3.2 MB (3,154,798 bytes)
Note: Pyndrine Industries is a fictional company I made up for this exercise.
SCENARIO
You are working as an analyst at the Security Operations Center (SOC) for a company named Pyndrine Industries.
Friday afternoon on July 10th 2015, one of the company directors called the SOC. His name is Marcus Pyndrine. He said his Windows desktop started acting strange, so it was wiped and reimaged. Marcus wants to know if the SOC saw anything unusual.
Your shift manager asked you if there were any related network alerts. Too bad most of the SOC tools suffered an outage that morning! But everything was back on line by that afternoon, so you searched the SOC's intrusion detection system (IDS). You found no alerts associated with Marcus Pyndrine's computer.
Fortunately, the company's network activity was recorded the entire time, and a sample of the traffic was retrieved. A coworker filtered the traffic to focus on Marcus Pyndrine's computer and saved it to a pcap. After a quick review, the analysts on shift all agreed something malicious happened.
QUESTIONS
You've been tasked with determining what happened and drafting a report. You'll need to include the following information:
- IP address of the director's computer
- MAC address of the director's computer
- Host name of the director's computer
- An overall description of the activity
- Any Indicators of compromise (IOCs) from the traffic to include IP addresses, domain names, etc.
ANSWERS
- Click here for the answers.